In just a few months, Binance has experienced explosive growth, overtaking its rivals to rank among the top three cryptocurrency exchanges in the world by trading volume. Without a doubt, Binance is now among the best sites for trading alt-coins like Ripple (XRP), Stellar (XLM), and NEM (XEM) to name a few.
Welcome back Hackers\Newbies!
SCRABBLE. To some it's just a game, but to me it's life or death. Well, not really, but it feels that way anyway. On a normal weekend, a game becomes much like Jon Thomas' "friendly game of death Scrabble."
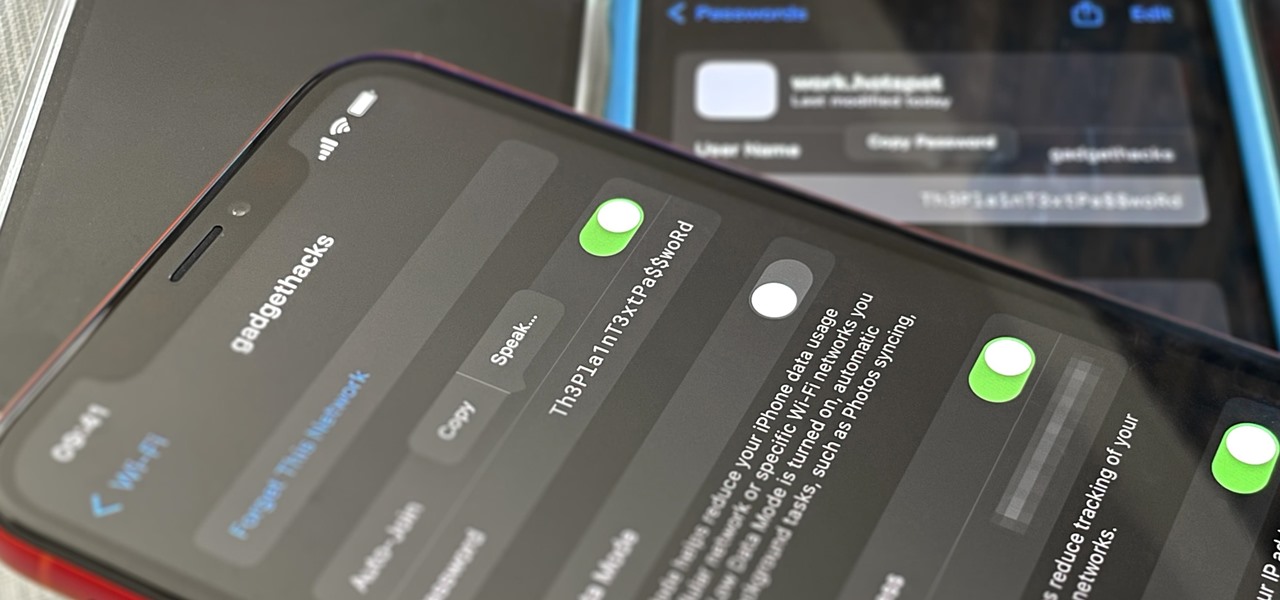
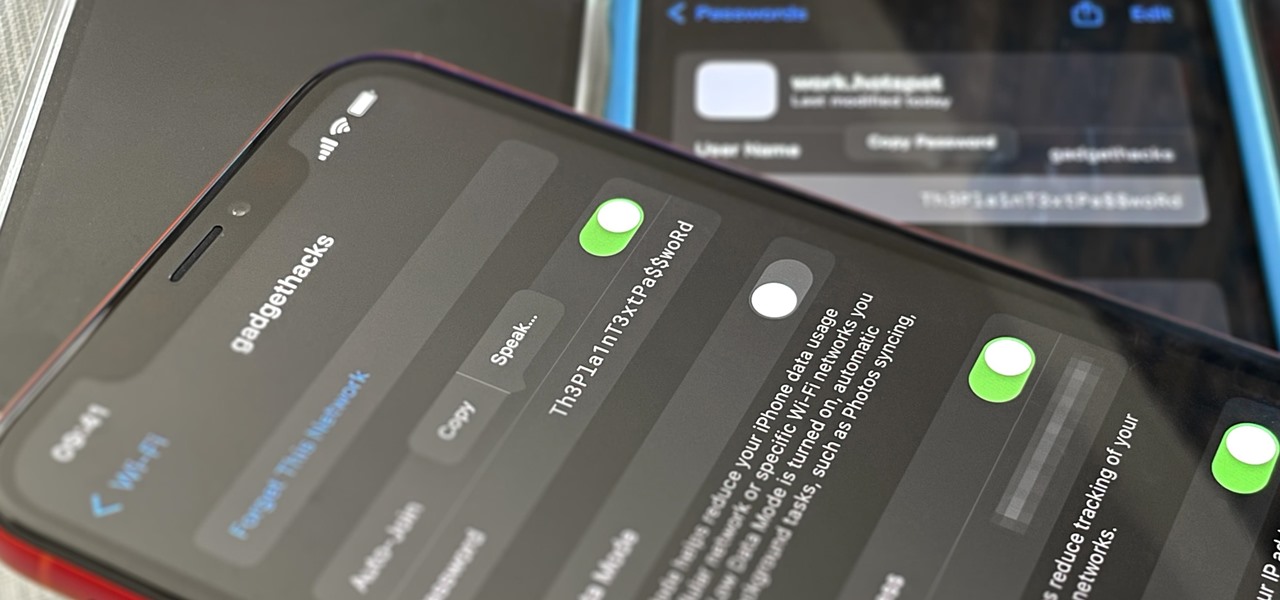
Your iPhone goes with you pretty much everywhere you go, and unless you have unlimited data on your cellular plan, you've probably connected to dozens of Wi-Fi hotspots over the years. Wi-Fi passwords are saved to your iPhone so you can auto-connect to the router or personal hotspot again, but finding the plain text password for a network hasn't always been easy.
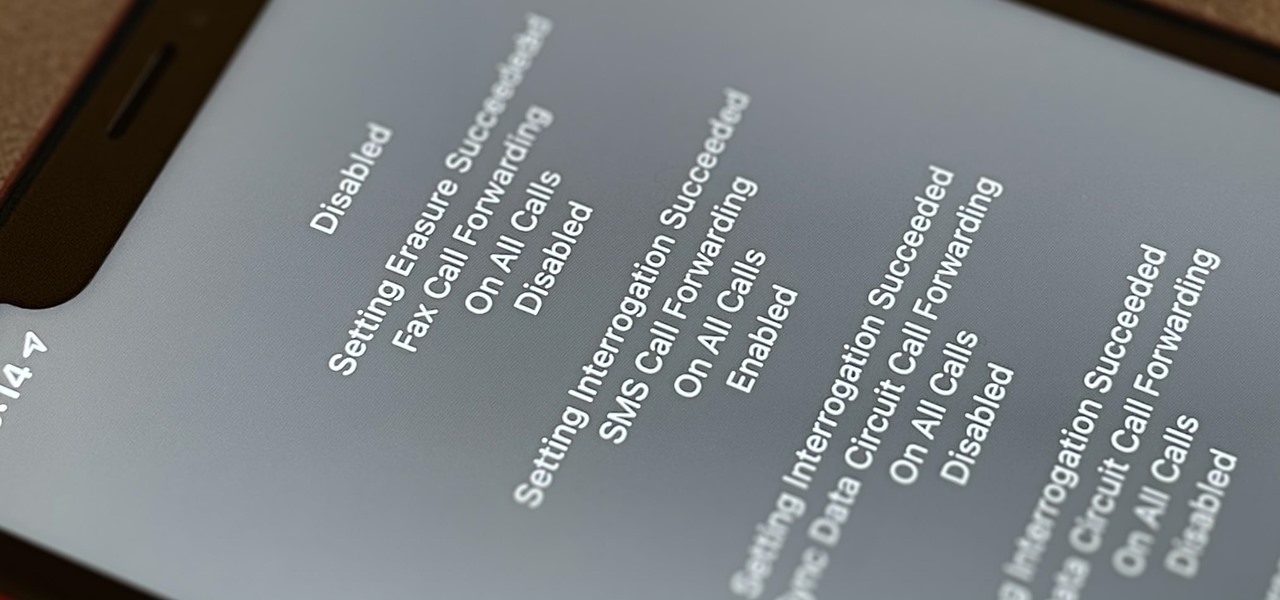
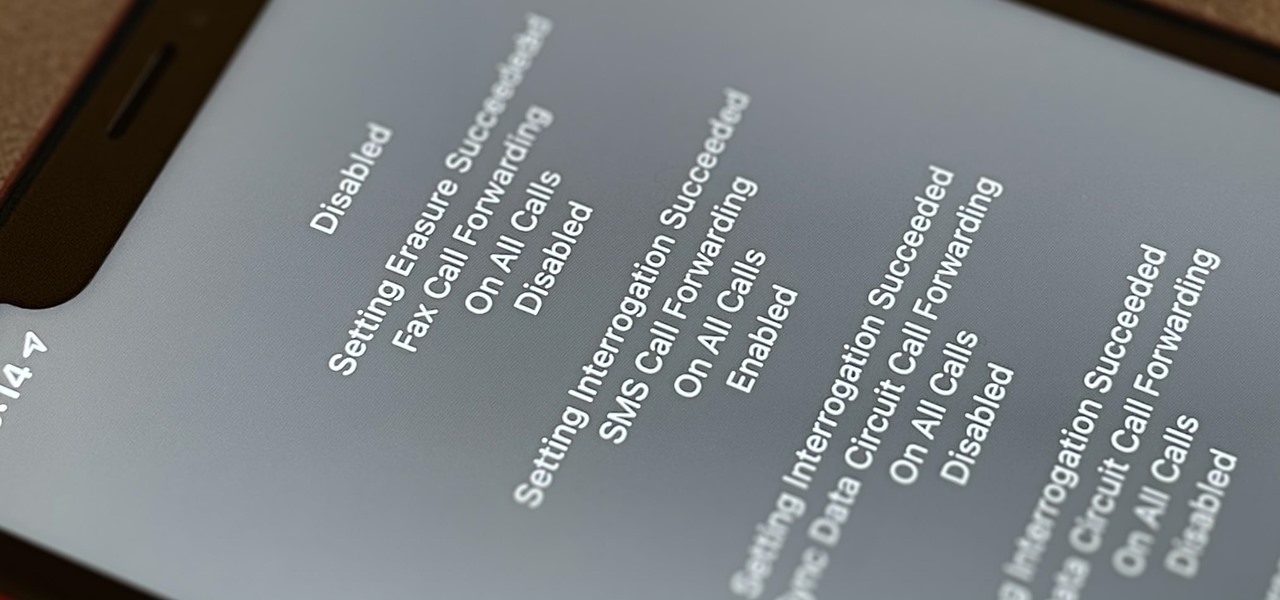
Malevolent hackers can divert your incoming calls and texts to any number they want, and they don't need to be a criminal mastermind to do it. Even friends and family members can reroute your incoming calls and messages so that they know exactly who's trying to reach you, and all it takes is seconds of access to your iPhone or wireless account. These secret codes can help uncover them.

Next to spam calls, few things are more annoying than being inundated with spam, scam, and smishing texts. Your iPhone's Messages app should be a place for your friends and family to stay in touch, not a minefield of phishing attacks, malicious links, and viruses. Luckily, there are quite a few methods to block and report your way to a more spam-free iPhone.

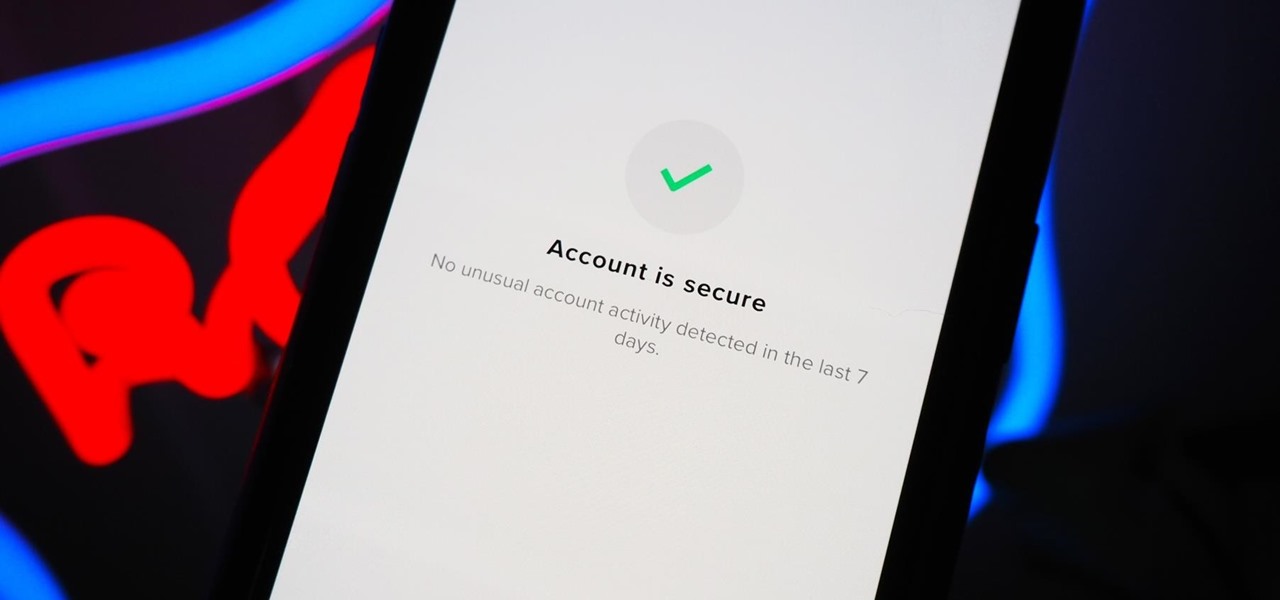
You should feel relatively safe to watch and post videos on TikTok, but like with any online service, you're always at the mercy of hackers.

Silence spreads over these mountains like nothing I've ever felt. If I didn't have Moby blasting in my earphones, there'd probably be no other sounds around. Well, except for someone, Phil probably, murmuring in a nearby tent just low enough to make his words indiscernible.

No more carrying around heavy laptops and thousands of Linux Live CDs and USBs to always be ready for pentesting on the fly!

Apple announced support for mobile driver's licenses and state identification cards in Apple Wallet back in 2021, and Arizona was the first state to jump on board in 2022. Fast forward to now, and only six states let you add a driver's license or state ID to Apple Wallet on your iPhone and Apple Watch. It has been a slow rollout, but more states are coming or are at least showing interest.

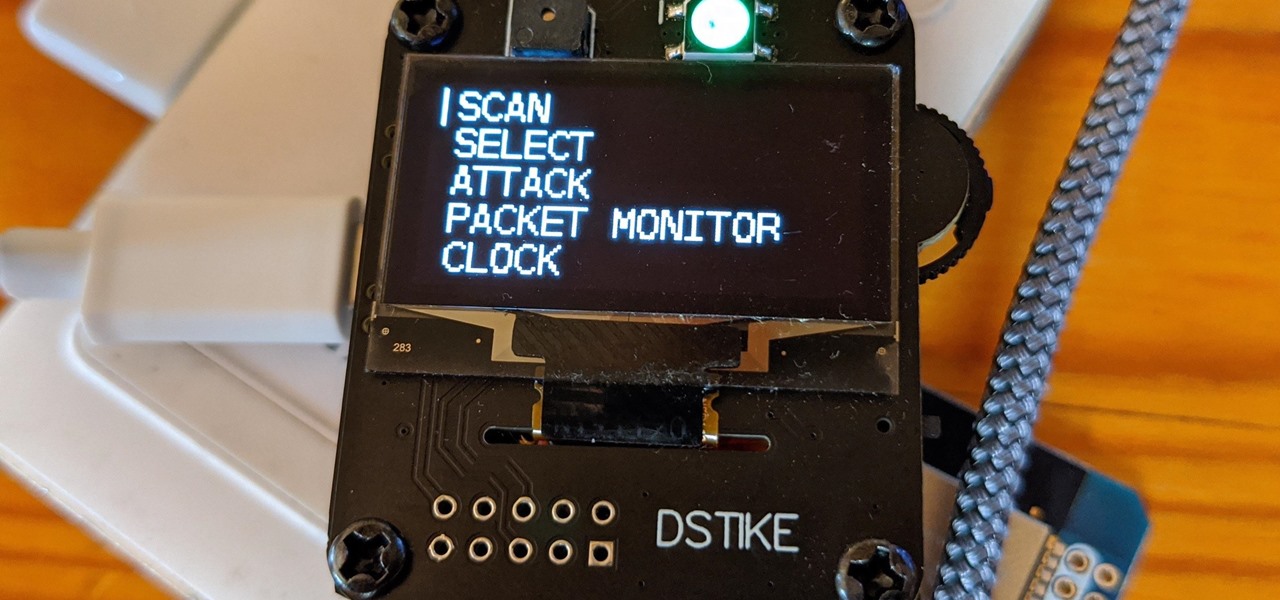
The Deauther Watch by Travis Lin is the physical manifestation of the Wi-Fi Deauther project by Spacehuhn, and it's designed to let you operate the Deauther project right from your wrist without needing a computer. That's pretty cool if you want to do all the interesting things that the Wi-Fi Deauther can do without plugging it into a device.

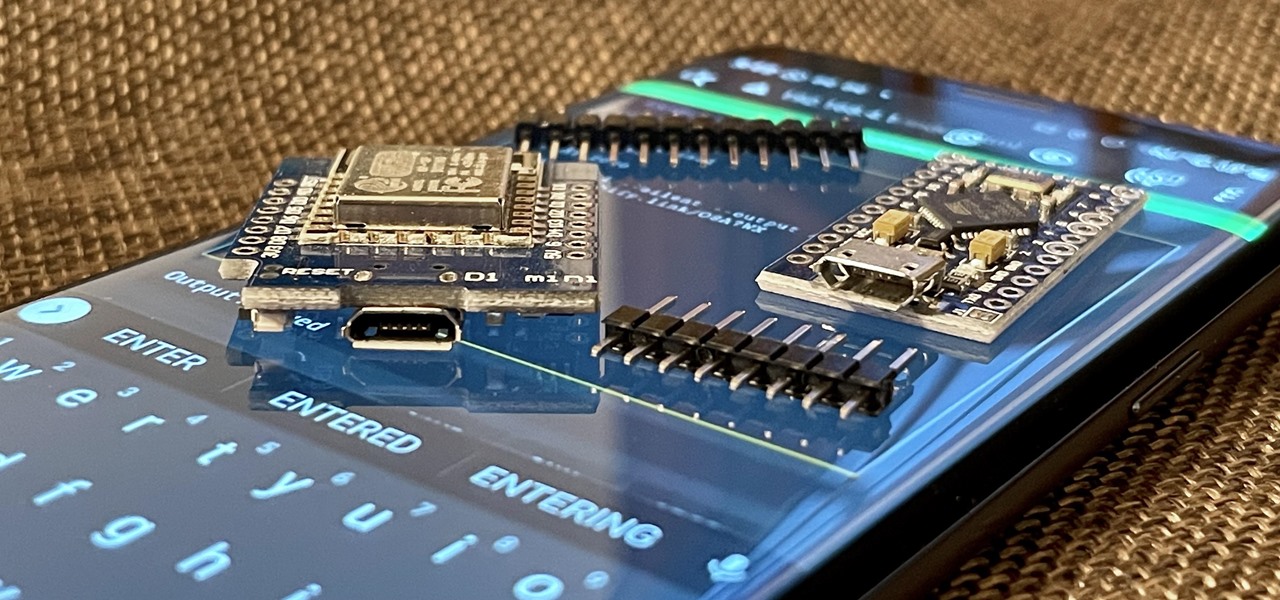
With just two microcontrollers soldered together, you can inject keystrokes into a computer from a smartphone. After building and programming the device, you plug it into a desktop or laptop, access it over a smartphone, and inject keystrokes as you would with a USB Rubber Ducky.

Rooting. As an Android user, I'm sure you've heard the word once or twice. According to Kaspersky, 7.6% of all Android users root — but for the 92.4% who don't, we wanted to talk to you.

A PirateBox creates a network that allows users to communicate wirelessly, connecting smartphones and laptops even when surrounding infrastructure has been disabled on purpose or destroyed in a disaster. Using a Raspberry Pi, we will make a wireless offline server that hosts files and a chat room as an educational database, a discreet local chat room, or a dead-drop file server.

Flight disruptions can cost billions of dollars, but most modern commercial flights rely on air traffic control systems that harbor serious vulnerabilities. The Federal Aviation Administration uses an infrastructure called NextGen, which relies on Automatic Dependent Surveillance – Broadcast, or ADS-B for short.

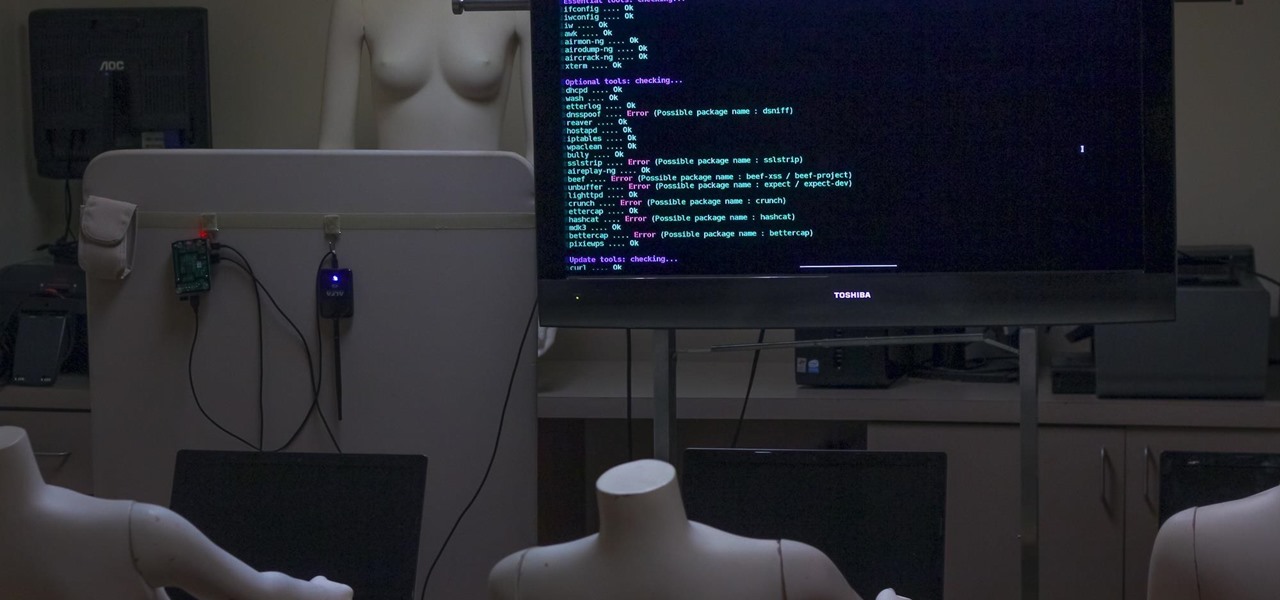
Airgeddon is a multi-Bash network auditor capable of Wi-Fi jamming. This capability lets you target and disconnect devices from a wireless network, all without joining it. It runs on Kali, and we'll cover installing, configuring, and using its jamming functionalities on a small, inexpensive Raspberry Pi. When done correctly, it will deny service to a wireless network for up to several blocks.

Apple's iOS 16.3 update for iPhone had impressive new features, but iOS 16.4 might impress you even more.

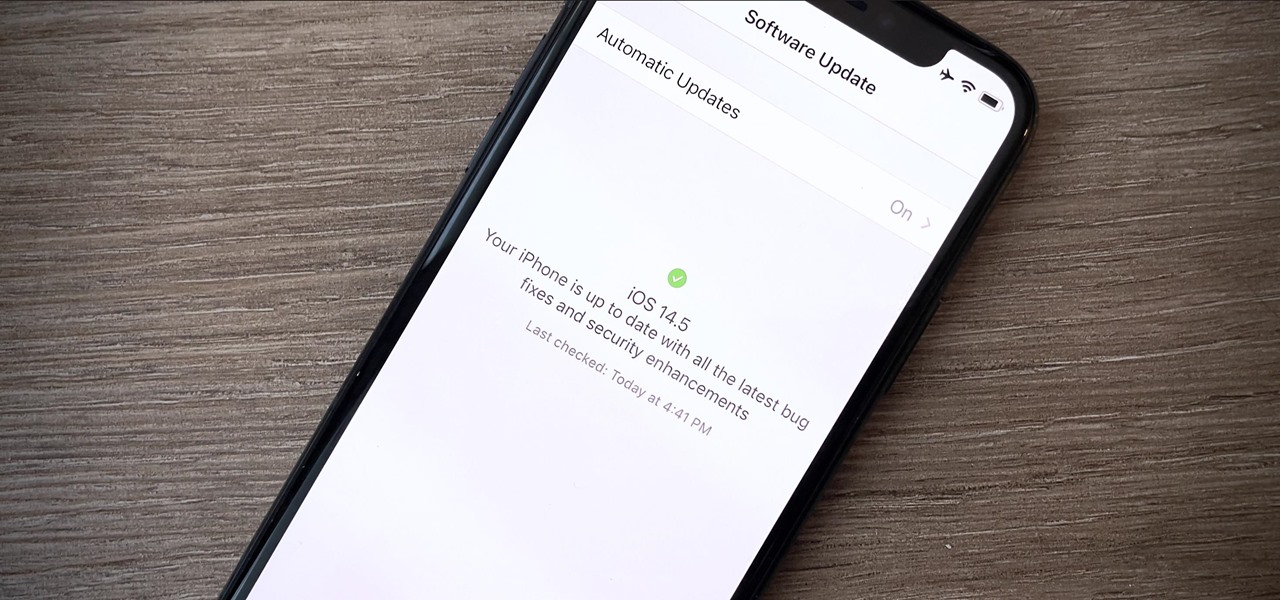
Your iPhone is full of features, many of which you might not even know about yet. Still, Apple keeps adding feature after feature with each new iOS update, and iOS 14.5 is no exception. The latest iOS version adds at least 69 features for your iPhone that you should be happy about.

The last two US Presidential elections were marred by reports of voter fraud. So Princeton University took it upon themselves to investigate how easy it could be to hack the election.Answer: easy.

s the Kony 2012 movement a fraud designed to justify another U.S. military invasion into another country? With oil reserves in Uganda speculated to be as large as those in Saudi Arabia, it wouldn't be a surprise. The Kony 2012 movement is VERY popular and seems to have a good intention. Let's just make sure we don't repeat history. QUESTION EVERYTHING, then you can support it!

This video is here to demonstrate that the TSA's insistence that the nude body scanner program is effective and necessary is nothing but a fraud, just like their claims that the program is safe and non-invasive .

Iraq war reconstruction: $6 billion to $8 billion wasted, US official says - Open Channel. The official in charge of monitoring America’s $51 billion effort to reconstruct Iraq has estimated that $6 billion to $8 billion of that amount was lost to waste, fraud and abuse.

For those of you behind on their international politics, Vladimir Putin has once again been elected as President of Russia. And right now, there are over 20,000 protesters in Moscow yelling about election fraud. Now, whether or not you think they're right, or whether or not you think Putin is a badass (he is, for the record), you have to admit he is an amazingly interesting cultural figure. And what do we do with amazing cultural figures? Why, we make fun of them with Impact-laden photos, of ...
On 2 October 2010 Univision held the first Spanish-English debate in the state, which was hosted by CSU Fresno.

Paparazzi are very annoying for the stars but with these sunglasses, paparazzi can't take you in picture .Why ? Because with this sunglasses your face will be invisible to the camera . Disclaimer: CAUTION! . Never use them for illegal act. Make anti paparazzi infrared invisibility sunglasses.

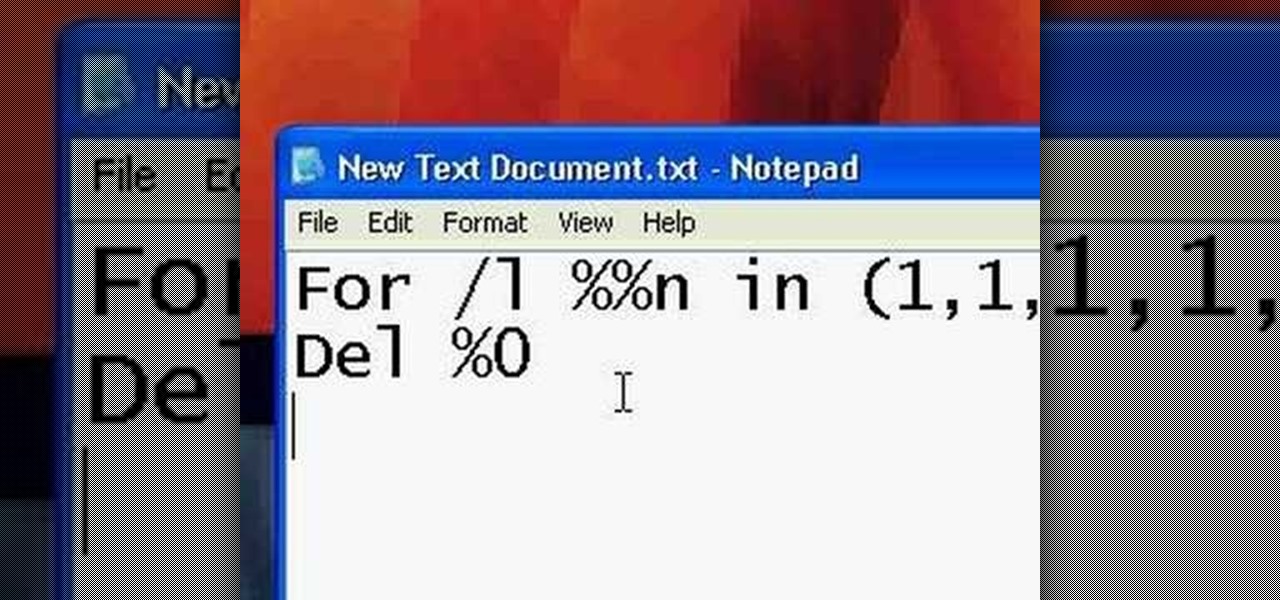
.bat files can be quite dangerous to any machine. Creating and opening these files should be done at your own risk. Sending malicious .bat files over the internet is illegal. This video will show you how to make and use a .bat file to prank your friends. Create an annoying batch file to fool your friends.

Immigration is a serious political issue in the United States, and those who oppose or support stricter immigration laws are often outspoken and candid about their beliefs, imposing their will on future legislation to not only politicians, but the general public—the voters. And what's the best way to reach the public? Entertainment.

It seems like the EU is currently in the works of making "the production or sale of devices such as computer programs designed for cyber-attacks" illegal. So, if you're a network admin that uses WireShark or Metasploit, you better watch out!
Many times throughout history companies have been hacked by so-called "grey-hatters": hackers who do ambiguously ethical things with their computer skills. Often enough, after being hacked the companies actually offer to hire the hacker, but not always (as you see in this case). Just a reminder that you need to watch what you are doing. Never do anything illegal unless you don't mind facing the consequences!

This shows how to collect rain water for future use from the roof of your house. Very cool setup, but be careful not to break the law while you're doing it. I know that here in Colorado, it is actually illegal to collect rain water without a permit. Scary, huh?

Do you think that this controversy surrounding GOP nominie Meg Whitman's illegal immigrant housekeeper goingo to affect her votes in her political campaign?

Here is the trailer for the movie "Import Export" If you want to see a really disturbing twisted movie about illegal workers and deviant behavior, check this film out, it will not disappoint.

Acclaimed Cinematographer Adam Kimmel Arrested:

She is kind of cute, in that fetching, illegal is-she-under-18 kind of way. A model from Paraguay. There is a 'green' undercurrent to the headline, in addition to an accomplished arts and crafts sensibility. It is a sweet domesticated how-to.

As hard as you try to protect your valuable information with strong passwords and anti-doxing measures, there's nothing you can really do when someone else gives up your goods. And that is the case with the recent Global Payments breach.

If you're a frequenter of Null Byte, I bet you have at least some interest in information security. Furthermore, you have a hobby that if applied in certain ways, will get you arrested. I've received quite a few messages from the community here about federal cybercrime law and how it applies to them, so I decided to get together with my lawyer to come up with some answers.

Have you been sharing your Netflix password with your friends? How about Rhapsody or Hulu Plus? If you get caught sharing your online subscription accounts, you could be slapped with a fine and even imprisoned.

From Boing Boing, a highly amusing photo gallery of illegal goods seized by airport customs officials in Australia. Some are fairly typical, but others really make you wonder... Yes, I'm most definitely talking about the tropical fish skirt lady.
Born in Sacramento, CA on January 1, 1958 and raised by two Mexican immigrant parents, Xavier Becerra was the only Hispanic on the House Ways and Means Committee. He was elected vice chair of the Democratic Caucus for 111th Congress and was a reprensentative from California's 31st district. From 1987-90, he was the California Deputy Attorney General. Xavier Becerra was part of the California State Assembly (1990-92) and has been a member of the U.S. State House since 1993.Xavier Becerra is a ...

.bat files can be quite dangerous to any machine. Creating and opening these files should be done at your own risk. Sending malicious .bat files over the internet is illegal. This video will show you how to make a virus that crashes your computer.