Welcome back, everyone. In the previous part of this rapid-fire miniseries, we built the attacker portion of the shell. In this article, we'll just be testing it to see if everything works correctly.

In my last post I introduced how to use ncat to connect to your Pi remotely, but what's the point to if you can't actually hack? This tutorial I'm gonna show you how to use very simple tools for a much bigger purpose. With that said, boot up our Pi and lets wreck havoc.

OTW's great Tutorial Hack Like a Pro: How to Save the World from Nuclear Annihilation gives me the inspiration to try this on Win7 sp1.

In order to access blocked videos and websites, you will need to set up a proxy service in the U.S., if you are trying to use Hulu. Go to a list site.

How to Use Your Mac as a Server: Turn your Mac Mini into a server! Yes, that's right, with a little know-how and a little spunk, you can turn an inexpensive Mac Mini computer into a server to provide services over you network. You won't even need the Mac OS X Server, just the Mac OS X Client, so there is no extra software to buy, just the Mac Mini and it's operating system.

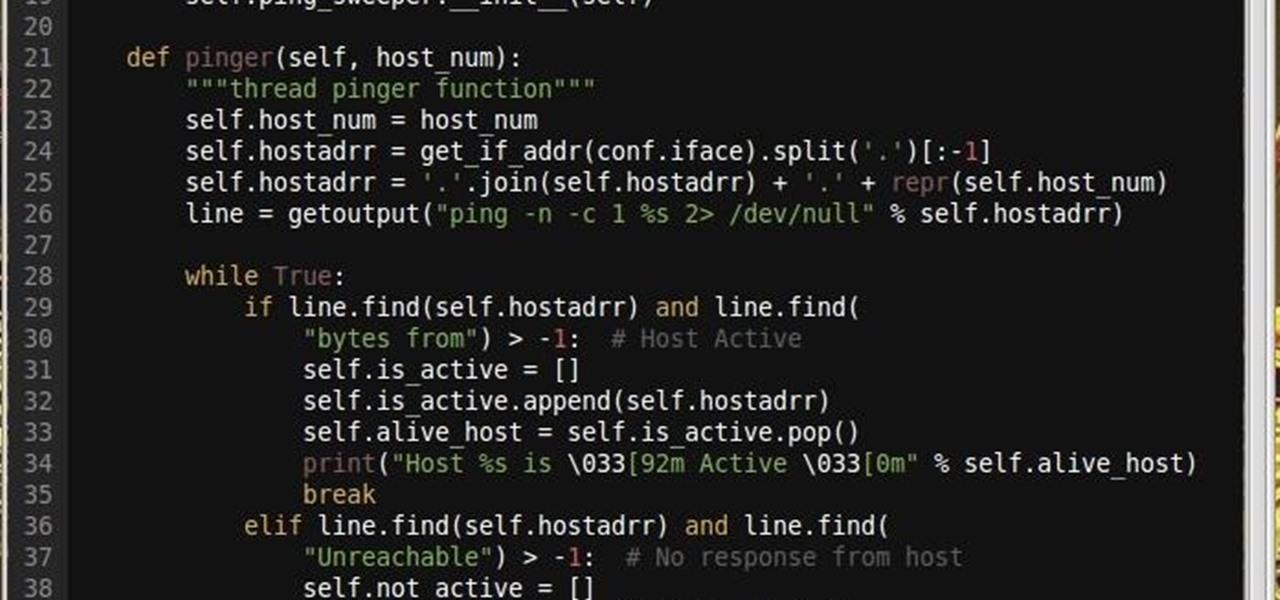
Welcome back, my novice hackers! Reconnaissance is one of the most important preparatory steps to hacking. As I have emphasized many times before here on Null Byte, you must know the operating system, the ports, the services, the applications, and sometimes even the language of the target to be effective. If you haven't taken the time to gather this info, then you are likely wasting your time.

Welcome back, my greenhorn hackers! Recently, I asked the Null Byte community what subject they would most like me to cover in future tutorials. Many of you cited scripting, and I decided it's best to cover this subject soon, so here goes.

Remote Desktop gives you access to your Windows 8 PC or device from wherever you are to run your applications and access your files remotely.

Okay, so first things first: the con presented in this bar trick video is illegal since you're basically stealing money, so perform at your own risk!

Samsung's not one to make drastic changes to what already works. They've continued on with the IP68 rating under IEC 60529 first given to the Galaxy S8 all the way to the the Galaxy Note 10. If you're a little confused as to what this rating means, don't worry, it's actually pretty simple once you get to the meat and bones of it.

When it comes to attacking devices on a network, you can't hit what you can't see. Nmap gives you the ability to explore any devices connected to a network, finding information like the operating system a device is running and which applications are listening on open ports. This information lets a hacker design an attack that perfectly suits the target environment.

Welcome aboard my inquisitive comrades. I am starting a new series that nobody expected coming. It may not seem very exciting at first, but await the last few parts as many startling discoveries will be made. This is a series which I plan to continue after the completion of Nmap, unless you have major objections.

Social engineering is a pretty important item in a hacker's toolkit. In Mr robot there was a time, we saw Elliot using social engineering to gain access to his therapist's boyfriend's email and bank accounts by calling him and pretending to be someone from his bank, then Elliot asked him for some info that were really useful to gain access to his account, the target believed to be someone from the bank and gave him the info Elliot was looking for. But How Is It in the Real World?

Hello null_byters, after some time out here we are again with another tutorial, continuing our beautiful series, today we will write our first real world bash script.

Hello My Fellow Hackerzz.. This is my first How-to and i'll be updating the “Hacking Android Using Kali” to msfvenom and some FAQ about known problems from comments. So Here we GO!!

Welcome back, my novice hackers! The worst thing that can happen to any hacker is being detected by a security admin, the security technologies (IDS, firewall, etc.), or a forensic investigator.

The NSA's massive internet spying efforts will continue. In President Obama's latest press conference, he went public to (in so many words) say that the NSA's spying efforts will continue uninterrupted. This, coming just weeks after the Amash Amendment which would have defunded the program, was narrowly defeated in the House (you can check if your congressmen voted against it here).

All kinds of people pretend to be someone they're not on the internet, including scammers, people attempting to wind others up, hackers and web predators. Almost all of these people will leave bases uncovered and they're all easy to expose when you understand how to. Here are my favorite ways of finding out when somebody is lying quickly. Image Search

If you're trying to hack someone's wifi, a useful bit of software you may want to try is called Wireshark. Wireshark is a wifi packet sniffer, which is an essential step in actually breaking into someone's wireless system. Of course, this is illegal, so make sure you're only doing it to test a network's security, or for your own educational purposes. Check out the video, follow the steps and see how secure network is. Hack, hack, hack!

Looking to do a little Friendster account hacking? Well, this video will show you how to hack into anyone's Friendster account after getting their password. Friendster was Facebook before Facebook was around, and beleive it or not, people still use it! You'll need a little tool to do the work, which you can find here. After that, follow the steps and get into any Friendster account. Remember, hacking is illegal, so be responsible out there.

In this video Dave Spencer shows you how to make soda bottles explode using dry ice. You will need dry ice pellets plastic soda pop bottles , and gloves (dry ice can be held in your hands but should be kept moving and not held up too long as it can cause severe frost bite). The presenter asks you to note that this activity is illegal in the state of Utah. Crushed dry ice is inserted into the soda pop bottle. The soda pop bottle is then shaken up vigorously and placed into the ground. You shou...

The FN P90. Everybody wants one, but more than likely, you can't get your hands on one, especially if it's illegal in your area. Designed by FN Herstal back in the 80's, the P90 personal defense weapon is the cream of the crop. It's full name, Project 90, specifies a weapon system of the 1990's. If you want this firearm for a weapon prop or just to have, you can easily build one yourself with household materials, mostly cardboard. Watch this video tutorial to learn how to build a P-90 prop ca...

Just like the title says, learn how to crack a master lock. Not pick the lock (picking a master lock will not get you the combo). You don't need any special tools to crack this master lock- all you need is the right technique. Crack master locks for fun only - don't use this for illegal purposes. Great trick if you lose your combination to your master lock. All you need is a little math. Learn how to hack a master lock with this lock cracking tutorial.

Here is a very in-depth description on how to make a silencer, but really a sound suppressor for your paintball gun. If you want to try to make a suppressor for a real firearm, the principles are basically the same. So, for ninja-like paintball action, watch this video tutorial to see how to make a silencer for a paintball gun, or sound suppressor, whichever you would like to call it.

No website will be inaccessible and no web filter will deny you content once you learn the skills presented in this internet hacking video.

This video illustrates the method to Set up a Remote Desktop connection on a Windows PC. This process is composed of the following steps: Step 1Install "TeamViwer" software on the PC's which would be involved in this process.Step 2Create a connection between the computer you want to access remotely and the one which would be used to gain remote access. To create a connection , you need to connect them through Wi-Fi, LAN or through the internet.Step 3Open the TeamViewer software from the compu...

In order to access your wireless router settings in a Windows PC you need to use a command called ipconfig. The purpose of this command is to find out what your IP is. Go into the command console and use ipconfig to find out what it is but instead of noting down the IP address, we actually have to note down the default gateway values for the task at hand. Now all you need to do is open your web browser and insert the default gateway values from before into the address bar. By doing so you wil...

FROMAN1115 teaches you how to change your NAT type to Open on your PlayStation 3. On the PlayStation 3, go to Settings-Network Settings-Settings and Connection Status List and write down your IP. Go to your PC and start your internet browser. Type in 192.168.1.1. This will bring up the router settings page. Go to Applications and games and then DMZ. Check the first box that says Enabled. Enter your IP address below and click ok. Your settings have been saved and you can enter a new internet m...

Hackers rely on good data to be able to pull off an attack, and reconnaissance is the stage of the hack in which they must learn as much as they can to devise a plan of action. Technical details are a critical component of this picture, and with OSINT tools like Maltego, a single domain name is everything you need to fingerprint the tech details of an organization from IP address to AS number.

CEO's of IT companies doesn't know this because they are not a hacker. Only a true hacker can become a successful Security head officer.

Man-in-the-Middle attacks can prove to be very useful, they allow us to do many things, such as monitoring, injection, and recon.

Why did I write this when they're tons of scanning tools available.

Recently, there have been some questions regarding networking popping up and we have decided to put together this series to try and cover this gap.

Fox hunting has become illegal is some parts of the world, but there are still places where fox hunting is an acceptable activity, where people ride on horseback, following foxhounds and other scent dogs on their hunt for foxes, most likely a red foxes.

In this tutorial, we learn how to use BitTorrent and burn a DVD on a Mac. First, download uTorrent from uTorrent. After this, go to The Pirate Bay and search for what you want to download. After you find something you want, download it through uTorrent and then double click on it to view it. If you want to burn this to a CD, go to the website Burn OS X and download this software. Now, you will be able to open up your download through the burn tool so you can watch the movie whenever you want....

Bluetooth is a great feature to have on your car for many reaons. One of the biggest being, that many states are now adopting laws that may it illegal to text or talk on a phone while dirivng. So, owning a car that has the bluetooth feature already in it, is great for drivers. So in this tutorial, you'll be finding out how to setup bluetooth on a 2010 Kia Sportage. Good luck and enjoy!

Setting up bluetooth in your vehicle is an easy task that anyone can complete. Bluetooth is a great and useful gadget that enables drivers to have conversations on their phone, without ever having to lift it from their dash. It's also a vital gadget to have in some states, since texting and calling while driving is becoming illegal. So in this tutorial, you'll be finding out how to setup bluetooth in a 2011 Hyundai Sonata. Good luck and enjoy!

Drawing graffiti is a tricky art form that requires patience and a little bit of imagination. With the right set of tools, or paint, you can turn a canvas into a bautiful piece of work. But before laying anything down, you'll need to know how to draw a graffiti outline. This tutorial, will teach you how to do just that. So good luck and please don't do anyhting illegal. Enjoy!

There are several ways you can remove window tinting. This video will show you how you can use a steamer and razor blade to peel and scrape of the tinting of a back window in a car. The steam heater will get the tint coat to separate from the glass. Depending on how old and the quality of the tint will determine how easy this process is. Hopefully you have a good tint job which will allow for easier removal. You can use Windex to finish removing any residue left when you are done. You may nee...