This tutorial will show you how to customize a Monster High doll using a My Little Pony Equestria Girls Mini. Watch this video to see how it is done. When you are done painting your custom doll, add a thin layer of Mod podge to seal the paint.

With the FBI getting access to iPhones, and apps like Waze being used to track people's locations, you've got to wonder just how safe and secure your smartphone is... or isn't. When you consider everything you do on your phone, from taking and sharing pictures to mobile banking, keeping your information safe is a crucial step that may seem out of your hands.

I'm a sucker for sushi, both in its traditional forms and its modern fusion creations. When the infamous sushi burritos surfaced, I'm not ashamed to admit that I waited in a ridiculously long line for what is essentially an uncut sushi roll. (As for whether it was worth it or not, well... that's another story.)
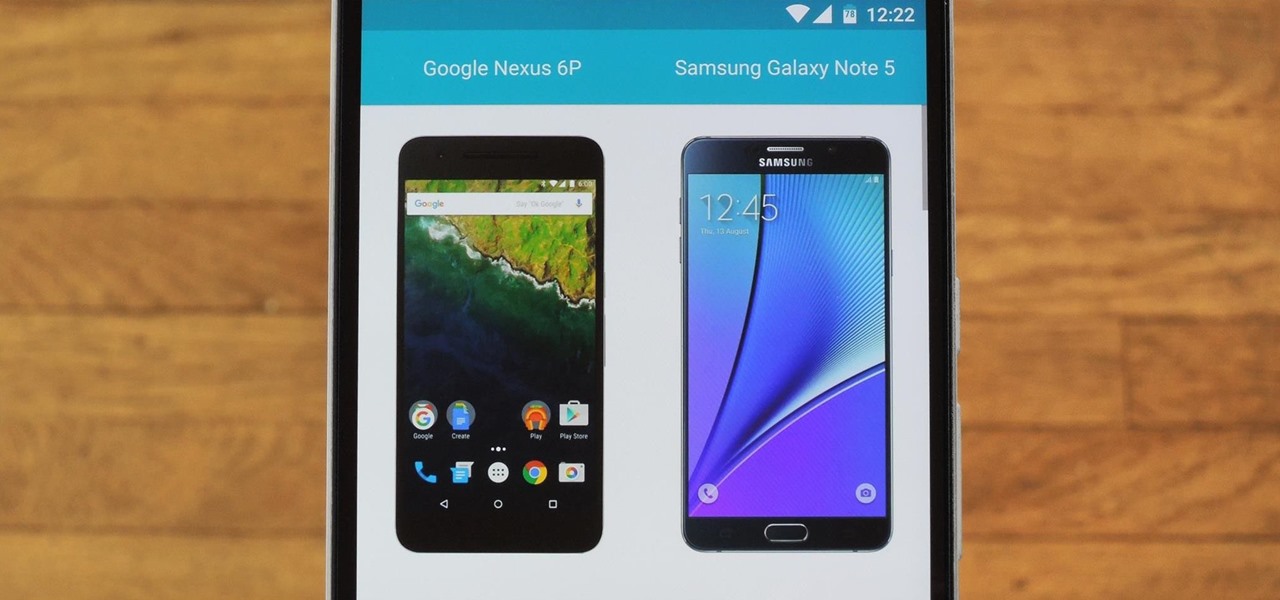
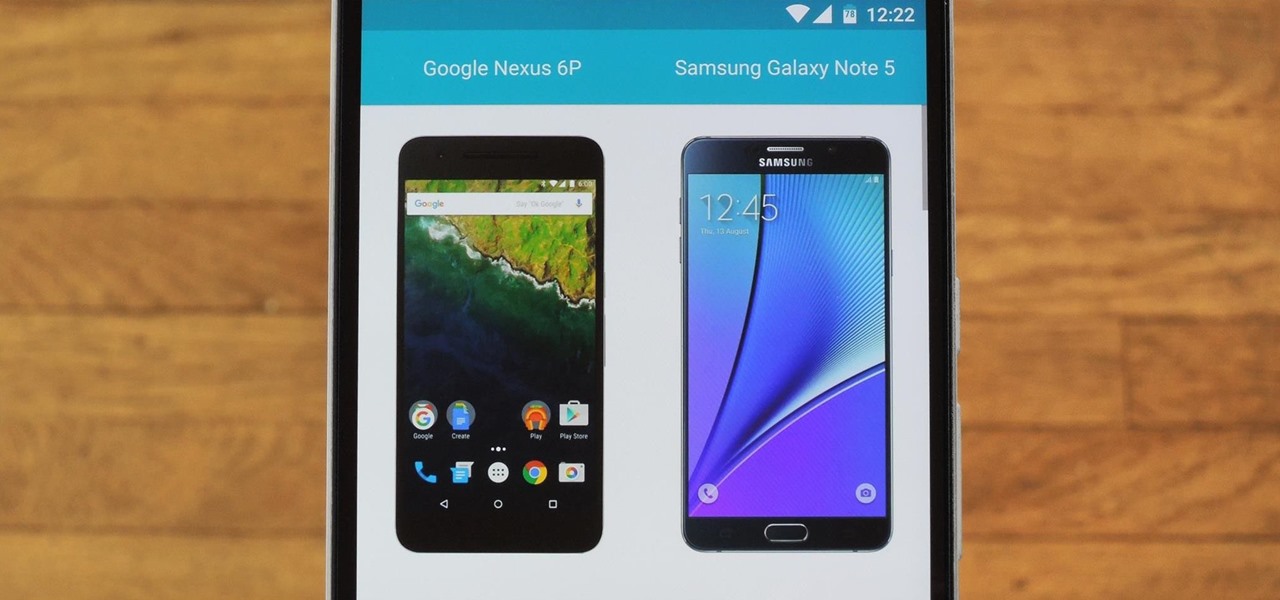
Shopping for a new phone is an entire ordeal. Even when you've narrowed it down to a few choices, comparing the finalists can be difficult, because specs and prices are scattered around on various different manufacturer websites, and if you're trying to do this on your current phone, most of these websites aren't optimized for mobile viewing.

Welcome back to another episode of Java Tutorials, In today's tutorial, we'll be learning about what methods are, proper syntax when writing Methods, and why they are beneficial in a program's code.
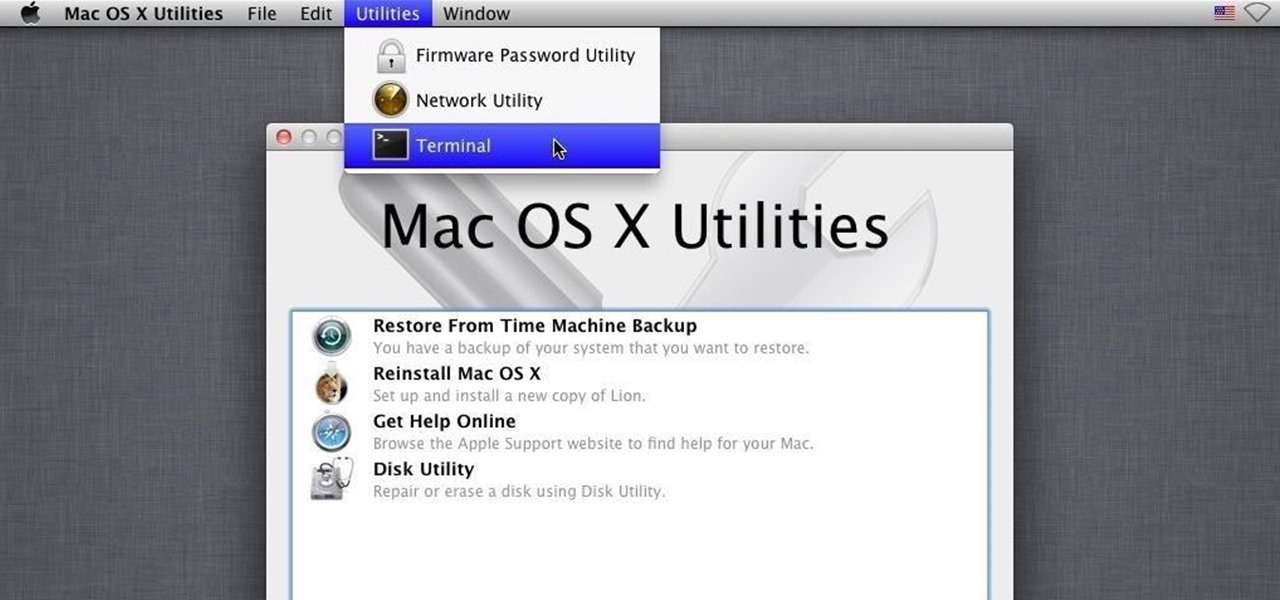
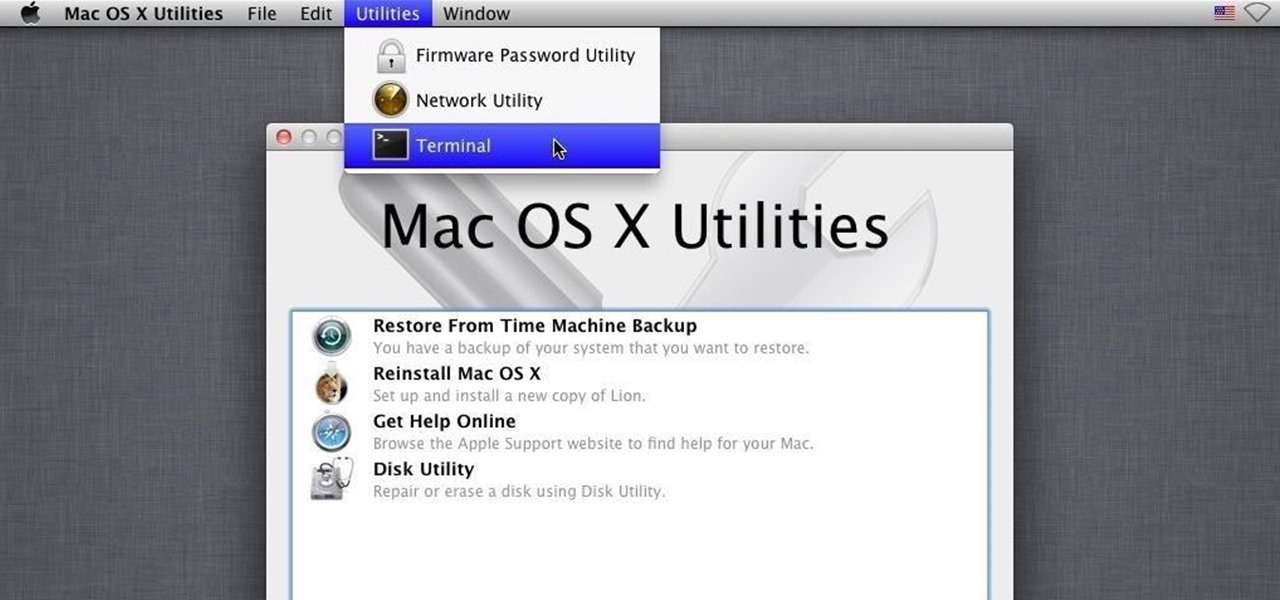
Hello, my fellow hackers. My name is cl0ck. I am a senior majoring in Computer Engineering with an emphasis is Security. I have been lurking the site for a while now reading and learning from the great minds that reside here. I, too, have some knowledge that I would like to share with all of you. This post actually comes from a personal problem I faced and had to find a solution for. Without further ado, here it is:

Step by step directions for finding the height of a trapezoid. Video: .

If you're looking for Halloween ideas to scare your little trick or treaters or family and friends, here are a few! You'll only need simple household items and for a couple of these pranks you'll have to purchase some fake blood which is not expensive.

Cooking Steak directly on the coals with no grill. Given many different names including caveman steaks or dirty steaks, this method involves placing the steak directly on red-hot lump charcoal to obtain a fantastic texture & taste that's as good as most restaurants.

The title says it all, Using tape and a bottle of coca cola I cleverly came up with this sneaky Hair Brush booby trap. Your victims will not see this coming until its too late. It works every time!

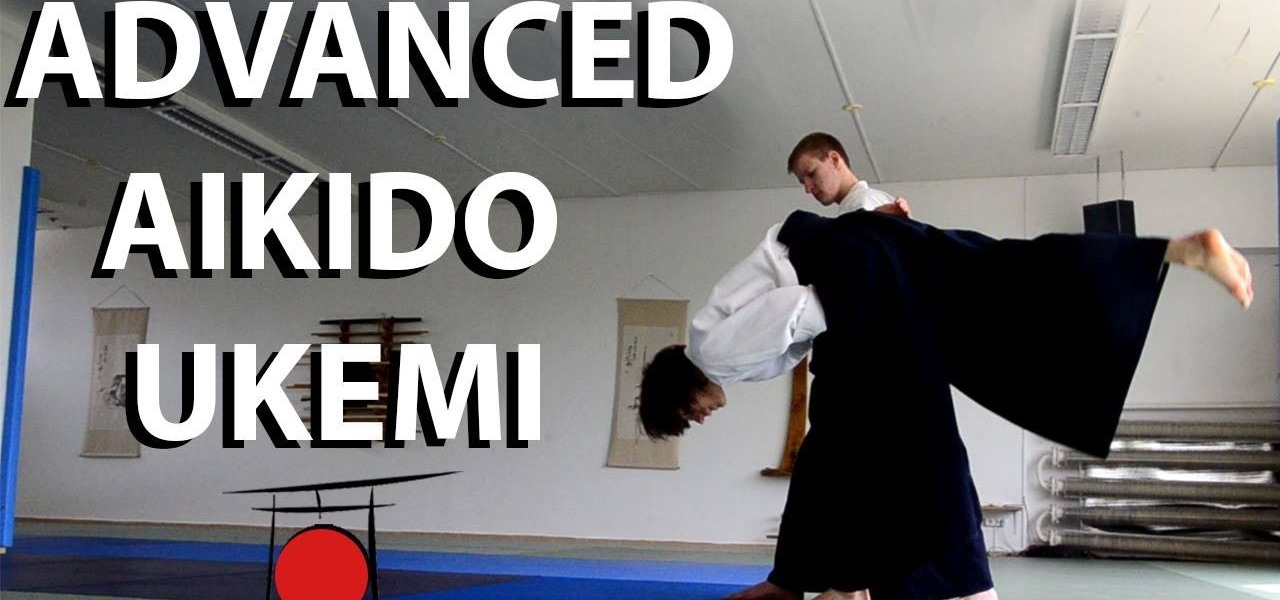
This is an advanced Aikido Ukemi tutorial which explains 11 different exercises seen and unseen. The tutorial includes detailed explanations of how to perform soft high falls from different techniques, various backward rolling tricks and other unseen ukemi variations.

The following are 5 very simple pranks that you can do at home on friends and family. Only a few household time are needed which would include, magnets, eggs, pantyhose stockings, dustpan, cups and a party popper. Just watch the video tutorial to get a better idea of how you can turn those items mentioned above into a hilarious pranks and booby traps.

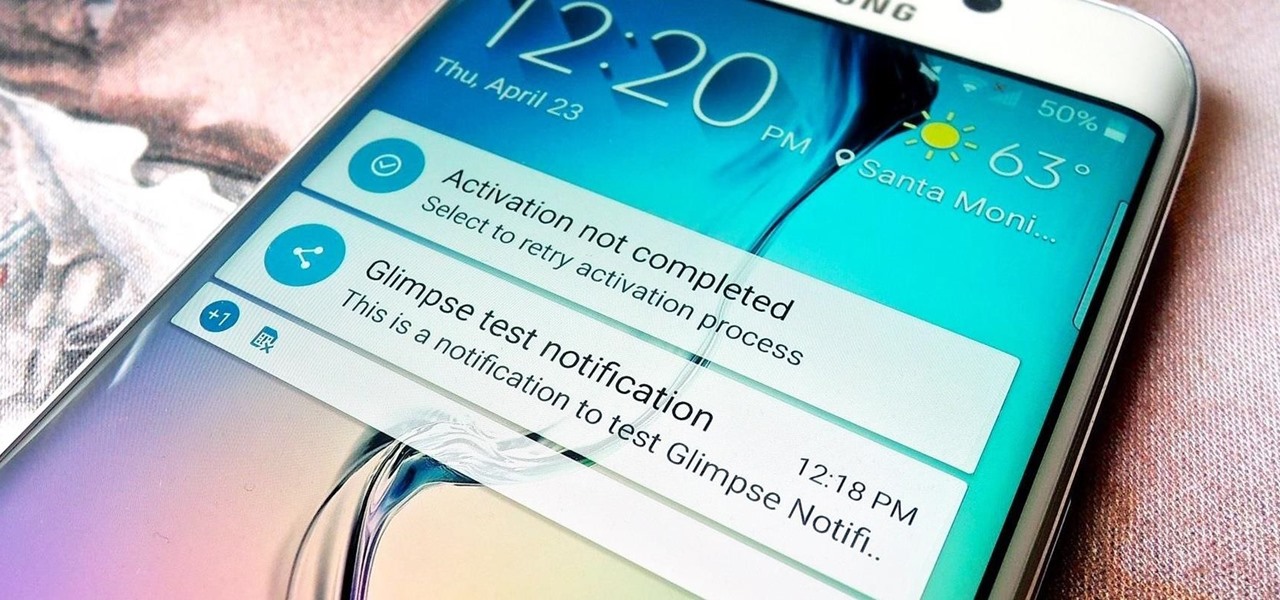
Unlike the Moto X with its Active Display or the Nexus 6 and its Ambient Display, some devices (especially those now running Lollipop) do not include a function that permits the display to turn on upon getting new notifications while the device remains locked or the display inactive.

Some third-party keyboards, like SwiftKey for example, include a convenient feature that suggests emojis as your type based on the content of what you're saying. Unfortunately, many keyboards, including most stock ones, don't include this function.

With troves of sensitive information, like receipts and password reminders, hiding in your email, your inbox can become a sort of Holy Grail for hackers—or anyone with your password. Although my crazy ex-girlfriend had no hacking experience, using my email login, she was able to find a lot of account information with just a general search for "password" in my inbox.

Welcome back, my budding hackers! With this article, I am initiating a new series that so many of you have been asking for: Hacking Web Applications.

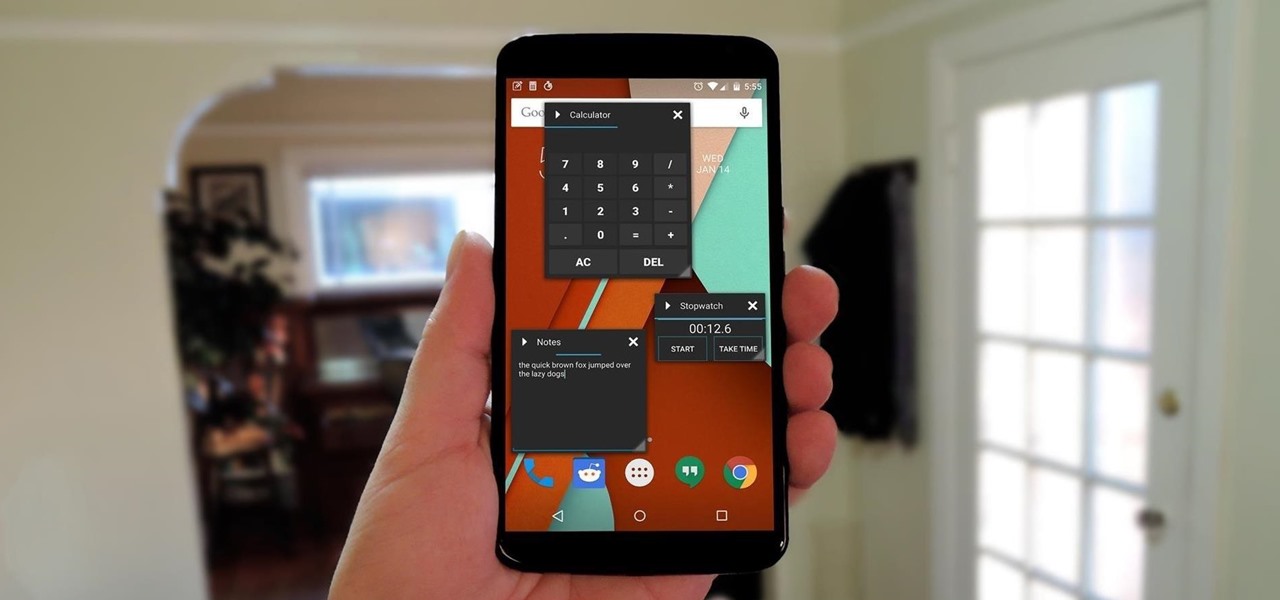
With Android devices getting bigger by the year, you'd think there would be a native multitasking solution by now. While Samsung and LG have included such features in their customized builds of Android, the stock base that manufacturers start with still doesn't include multitasking support.

Pretty much anything in the world can be booby trapped and that includes deodorants such as Spray or Bars. It's so unexpected that it's the perfect prank. Check out the instructional video for instructions and demonstrations on how to pull this off.

Maybe it is inspiration for some people around here. I have done this in AE and want to share it. Feel Free to download and use or customize it however you want. Download the template here (music not included).

In previous posts here, I have pointed out that hackers are in high demand around the world and in nearly every industry. Every military and espionage unit of every country is trying to hire high-quality, experienced hackers as fast as they can to hack their adversaries' computer systems in order to gain a strategic advantage and to spy.

The video link included shows in text how I do it from start to finish. The description tells a little more. This particular vase is made of Aromatic Cedar and is 10 inches around.

With root access, you're granted greater control over your device, allowing you to do things that your Android system wouldn't allow otherwise. Things like installing Xposed mods are made possible with root, but other advantages address performance and security, like stopping your Android logging, which is exactly what we'll be going over today.

This video will guide you 5 useful tricks and tips for Google search engine. These tips include search operators, search in a single site, get definition, calculation and currency conversion, fast essential information etc. So please watch the video and follow all the steps to employ in your machine.

If you thought iOS 7 was a drastic change from previous iterations, iOS 8 will certainly continue to rock the boat. From a revamped Control Center to enhanced "Continuity" to ephemeral messaging, Apple's newest mobile operating system will have many of you relearning the "basics."

This video shows top 10 useful tricks in windows 7. This video includes window key application, inserting program or folders in start menu or task bar, enabling or disabling windows7 features, notification area customization, reliability history etc. These tips will help you to operate windows 7 more efficiently. So please watch the video.

This video will show you 4 useful tricks related to you windows7 operating system. This video includes areas like speedier mouse, preventing display rotation, restore previous versions and monitoring of audio recording. Watch the video and follow these computer support tips.

When looking at weather applications and widgets, one major characteristic I look for is efficiency; something that will separate it from the rest of the herd. The stock weather widget looks great on my home screen, but I have to exit whatever app or game I'm in when someone asks me about the weather.

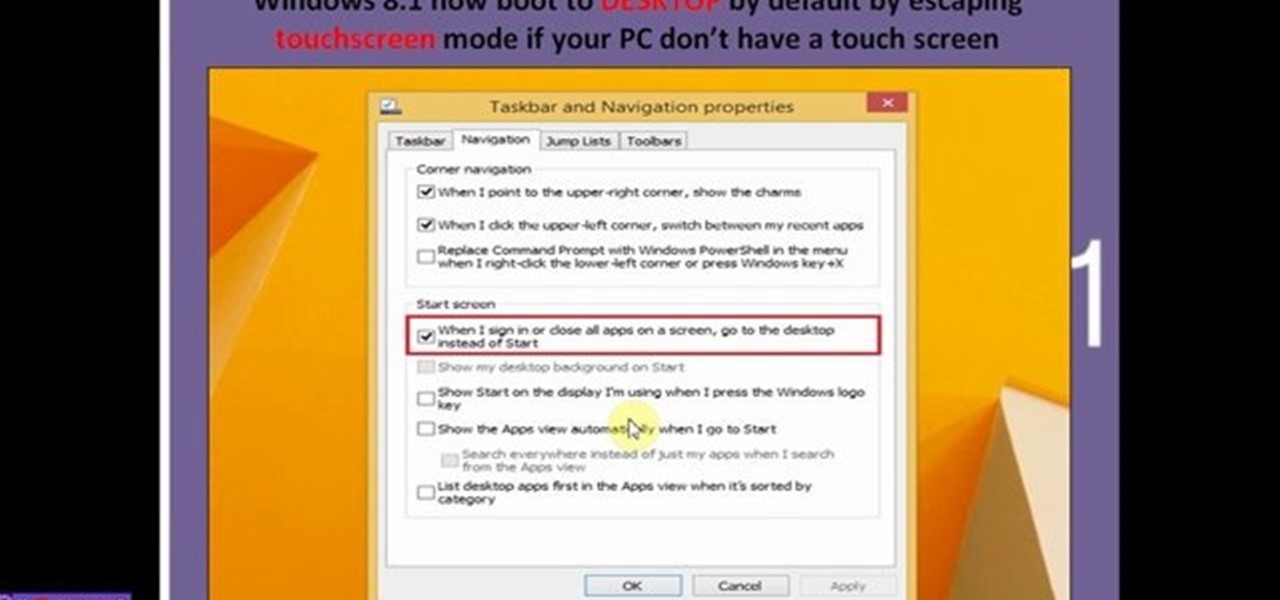
This video will describe 10 new features of windows 8.1 update. This video will highlight in those new features which are expected to be included in the coming update. Hope this version will be popular among professionals.

Incorporating features such as CarPlay, UI enhancements such as the new call screen, and several bug fixes, iOS 7.1 was the first major update to Apple's operating system since iOS 7 was released in June of last year.

There were some pretty amazing things included in the Android 4.4 KitKat update, but unfortunately, most of them were left inactive on our Nexus 7 tablets. Some, like full-screen immersive mode and the hidden battery percentage status bar icon, could be enabled on rooted devices, but not everyone wants to root.

After all the leaks and peeks of the HTC One M8, it has finally been officially introduced to the public, available for purchase at most U.S. carriers. HTC also unveiled Sense 6 during the launch event, the newest iteration of its operating system, and thanks to their new Advantage Program, the update shouldn't be too far behind for the older One (M7).

Watch the video and animation for to see how it works. The drawing(free PDF download) is included in the description of the videos.

The use of smart phones is not limited only as a mode of communication now-a-days. There are many things that can be done with the help of a smart phone.

NSA aside, Apple makes it difficult for users to extract and download text messages from their iPhones onto a computer. For whatever reason (legal, devious, neurotic, etc), we've all found a time where we'd like to save backups of certain meaningful, important, or perhaps incriminating conversations (including all MMS or iMessage pictures and videos). While there are a handful of third-party applications that can help with this process, the majority of them cost money and implement certain te...

Halloween pumpkin can be an interesting model for beginners, even if Halloween was a few weeks ago. In the video below are detailed instructions that also includes a small map to see how are triangles assembled. You will need 198 orange, 36 light brown, 22 yellow and 5 dark brown triangles.

This video will show you how to bleed the air out of the burner oil line on your furnace if you run out of oil. Shown on a Carlin EZPro burner, Weil Mclain Gold boiler. Also would work on most burners the same way including a Beckett.

In this video Henry shows you how to finish all the exterior trim on the shed. This video includes lot of tips to make the finish carpentry in this video easy and accurate.

Henry shows you the right way to install roof sheathing (1/2" Plywood) including the proper spacing and importance of using H-Clips to extend the life of your roof.

Depending on where you live, the type of skirting option you choose is important (Skirting is the base trim around the shed). Henry shows you three different ways to do this including the Drip Cap options for wetter climates.

Henry shows you how to build homemade trusses. This video includes instruction on how to layout your truss jig to make sure all trusses are identical. After you watch this video, you'll see how easy it is to build your trusses!