
News: Do the Do!
We are embarking upon a new year. As usual, some of us will make "resolutions." There isn't anything wrong with setting goals for the year. It's actually a good idea. It may help focus the energy we bring to life.


We are embarking upon a new year. As usual, some of us will make "resolutions." There isn't anything wrong with setting goals for the year. It's actually a good idea. It may help focus the energy we bring to life.

Have one of the most beloved characters on jackass(steve-o,jhonny,bam) fake his death for the world to see, have them pretend to rob a bank and have a cop in there at the same time, so when they hold up the bank they get shot and since its a bank there will be cameras so thats how they got it on tape, remember this will all be fake but nobody will know. or you could fake a car crash and it would have the crew in there about to go film but only 1 would die and the rest would b just hurt.or som...

In this article, I'll show you how to make a high-powered, long-range, air-powered rocket gun. This launcher is based on a sprinkler valve, a modified propane tank, and a few other components. Though not hard to make, this device is VERY dangerous! The rocket can seriously harm, if not kill any living thing it's shot at. Here's a video of it in action, quite an accurate shot by my friend Chris... Parts

Taking apart batteries is one of those things that every adult you've ever known has warned you against. Today, we break the taboo and dive into a lithium battery. Lithium has some pretty cool properties—it burns instantly in water and glows blindly bright under flame. And with just one AA battery, you can make a blinding light beam inspiring supernatural awe in all dictatorial adults who doubted you.
I'm back with the third part to my laser weapon series (see part one and two), and I'll be explaining the function, application, and potential of semiconductor lasers, aka laser diodes.

Did you know there is hidden data in your digital pictures? Well, there is, and that data might be a security risk to you. Think back at all of those pictures you're in and are connected with. I'm sure some of those you'd like to distance yourself from. And surely you wouldn't mind checking out the metadata in a few of those images. In this article, we'll be going over how to do just that.

Today's tutorial will teach you how to erase data permanently so that it cannot be recovered. Many believe that having a file shredder on the computer means you are up to no good.

Friday's Community Byte was weird. The intent was to do a HackThisSite mission, but upon time to begin, everyone in there was programming without my assistance, with the help of Sol Gates. This is great! It's really awesome that everyone enjoys programming that much and will make the effort to learn even when I am not present. So, a tip of my hat to Mr. Sol Gates and the rest of you fine people.

Cross-Site Request Forgery (CSRF, pronounce "sea-surf") is a common web exploit. However, for unknown reasons it's not used very often. It plays on a given website's trust in a web browser by executing another website's form action, for example, sending money to another person. It's usually placed in abnormal places like HTML image tags.

It's one of the greatest fears among parents and politicians the world over—video game violence spilling out into reality. The shooting at Columbine and the more recent tragedy in Utøya, Norway have touched deep nerves in Western consciousness. And that's why there's a giant pink, juggling elephant in the corner of every production meeting and press conference for each shooter game that comes out.

Even with Apple's forthcoming iOS 5 updates to its default camera application, those upcoming features can't match what already exists in Global Delight's Camera Plus Pro. For $1.99, Camera Plus Pro provides users with over 100 tools for every part of the picture taking process, including video recording. It works with all versions of the iPhone, iPod touch, and iPad 2 with iOS 4.1 or the later update. Let's examine what it can do, and why you will want to replace Apple's default camera with ...

The philosophy of street art is a long and complex one. This is just the first in a series of the individual street art philosophys i have come across.

Not every DIY project is as executable as, say, making a potato gun. Occasionally, we observe a quixotic project that is just plain wonderful. Consider rich guy Philip Anschutz and his eponymous Anschutz Entertainment Group (AEG). His ambition to bring an NFL team to Los Angeles is a Fitzcarraldo-sized DIY project that, if the stars align, might happen in time for the 2016 season.

If you want to install laminate flooring on your stairs I would recommend that you do a lot of research and find the information you will need to do it correctly. Installing laminate flooring on stairs can be tedious and time consuming and is a lot different than installing laminate flooring on a floor.

While a lot of internet threats are rather over-hyped, there are some serious things to be cautious of when going online. Probably the biggest risk to the average internet user is malicious software. Commonly knows as "malware," this term refers to any program that exists solely to do harm. This may include damaging your computer or accessing your data without you knowing. Viruses, trojans, and spyware are all forms of malware. Now, malware can seriously mess up your system, and the idea of s...

MyShoppingGenie is an online shopping application that can help you find the best deals on products you search for.

The sudden deceleration, shifting in the knee, popping sound and screaming from the intense pain that immediately follows is becoming increasingly common among our young athletes. Those who
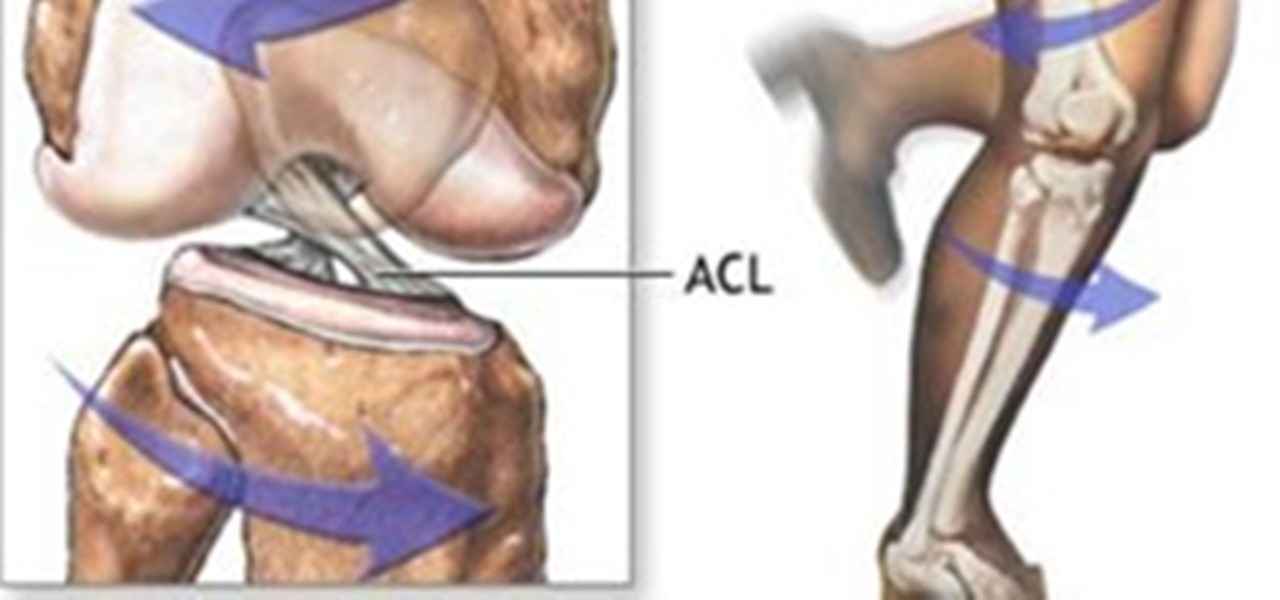
The sudden deceleration, shifting in the knee, popping sound and screaming from the intense pain that immediately follows is becoming increasingly common among our young athletes. Those who have witnessed or suffered a torn anterior cruciate ligament (ACL) are familiar with the pain, surgery and intense 6 to 8 month rehabilitation that accompanies the injury, not to mention the disappointment of ending a season. Nationwide, this will occur more than 500,000 times this year, and female athlete...

Wireless networks. Nowadays, everyone uses 'em, but most don't secure 'em. On average, I can drive up and down any block in my city and find at least one or two open or semi-open networks on any given day. With some changed MAC addresses for good measure, an attacker can use your network as a spring board for who knows what. When the police come a few days after, they are coming to your door—and not to talk about how nice your lawn is. Don't be that guy.

I want to write this article because in my childhood, I had experienced internet stalking which ultimately ended in physical stalking which then lead to several attempted abductions. I have now learned how to use the internet safely, who to communicate with and I've learned how stalkers work.

Just a couple Saturday's ago, we were blessed with the Supermoon, where the moon was at perigee with our planet, creating a larger than usual Moon for us here on Earth. Now, we've got another spectacular show in the skies coming up, only this one isn't at night. There will be an annular solar eclipse on Sunday, May 20th!

As hard as you try to protect your valuable information with strong passwords and anti-doxing measures, there's nothing you can really do when someone else gives up your goods. And that is the case with the recent Global Payments breach.

As a web developer, I often read articles about hackers (from the lowly to the knowledgeable) infiltrating websites via the dreaded 'SQL Injection' method and completely taking control, changing, gaining access, or destroying the owner's data. As a fellow web developer, I'm sure you want to know how to protect against it. Well, here it is! In this article, you will find out what SQL Injection is, what you can do to protect against it, and additional recommendations that are easy to do and onl...

Accounting and Finance Degree

In my second article of the laser weapon series (see the first part here on CO2 lasers), I'll be expanding on the potential of pulsed lasers.

There are so many hackers around these days, and they are becoming very smart. So smart that they have successfully taken down many government websites. The most recent attack was on the Department of Justice (DOJ). To read about the history of these hackers, check out Wikipedia.

This is Part II in the Lockdown: The InfoSecurity Guide To Securing Your Computer series. Before beginning, check out Part I. This article will cover using alternate software to increase your security and will provide you with some information about websites and programs that test a computer's security. It will also guide you to software you can install or follow so you know what programs need to be updated on the computer. Lastly, I will talk about some features that should be disabled when ...

Previously, we talked about how to secure Firefox. Today, we will talk about securing a Chromium based Browser. Why? Because Chrome recently beat Firefox in holding more customers.

The relationship between developers and publishers in the video game industry has always been awkward. Many great game developers such as Bizzare Creations, Clover Studio, and Bullfrog Productions have been disbanded due to corporate shenanigans involving their publishers and owners. The indie game movement has risen largely as a response to this.

RESPECT - What It Means (in the picture above are my parents, both of whom I respect and cherish dearly)
Back in the eighties, I used to hate television commercials, but I eventually got used to them. Had to, in order to enjoy my favorite shows. Then, the increasing number of billboard ads annoyed me in the nineties. They followed me everywhere I went—no escape—persuading me to buy the newest whatever. It seemed like Big Brotherism—like They Live. But, I got used to it. When I finally entered the digital age and became a web addict, I was peeved at the constant sight of online ads everywhere I v...
Proposition 22 Prohibits the state from borrowing or taking funds used for transportation, redevelopment, or local, government projects and services. Initiative constitution amendment.
Final Fantasy 14 the MMO is now live. The special edition priced at $75 enables people to play eight days earlier than people getting the regular edition, which comes out on September 30th. Mine arrived yesterday and here are some pictures of what's inside the special edition version of the game:

Join the Pilot program and learn how to fly! But you're not going to be flying airplanes in this Pilot program, you'll be trying your hands at Google's first laptop computer.

You can get healthier looking skin in just three easy steps! Sarah shows you how... Cleanse For morning, Use an electronic facial cleansing brush; it will make a huge difference in your skin. It helps circulation and removes old makeup and dirt and can be used in the shower. For evening, use facial cleansing cloths.

WikiLeaks. In recent weeks, it's been the hottest topic on the web. It's been attacked on a multinational level by political influence peddling.

STANDP'S WINDOWS 7 "ASTON-2" CUSTOMIZED DESKTOP IT ROCKS COMPLETELY!. DEC

Hello, everyone. My friend and I recently released a Defense of the Ancients (DotA) map that went viral and thought I should share it with Minecraft World on WonderHowTo since you guys helped me out when I first started making videos! We were featured on Kotaku, RockPaperShotgun, Gamespy, The Verge, Joystiq and many more websites!Exciting!You can see the full details below are head straight here for the downloads.

The community here on Null Byte has always been great and helpful in sharing their know-how, even before I took up admin duties in this World. I jumped at the chance of leading Null Byte because I enjoy teaching and informing people on all of the important need-to-know things out there, but more so than that—there is a deeper reason.

If you follow the Anonymous, Occupy, and IT security scenes, you have no doubt heard about a dox release. What is it? How can it hurt you? And most importantly, how can you protect yourself from it? Some of these steps might seem common sense, while others will be an ah-ha! moment. Your private info is both your biggest weakness and your biggest weapon in your battle to remain anonymous. You must learn how to use it as both.