hello my dear colleagues, I made a visit to nullbyte and found that there is not a complete tutorial about the google dorks, so I felt the need for this tutorial, and seeing that there are many newbies around, so here's a tutorial that will teach you how to use google to hack.

You may not have thought of dorks as powerful, but with the right dorks, you can hack devices just by Googling the password to log in. Because Google is fantastic at indexing everything connected to the internet, it's possible to find files that are exposed accidentally and contain critical information for anyone to see.

Before attacking any website, a hacker or penetration tester will first compile a list of target surfaces. After they've used some good recon and found the right places to point their scope at, they'll use a web server scanning tool such as Nikto for hunting down vulnerabilities that could be potential attack vectors.

Computers all over the world rely on a program called "libssh" to use the SSH communications protocol, which allows trusted users to log in and administer computers remotely. Due to a flaw in libssh, fooling a computer into granting SSH access is as easy as telling it you already have permission. The vulnerability can lead to an attacker gaining complete control over a device.

Hacking Wi-Fi is a lot easier than most people think, but the ways of doing so are clustered around a few common techniques most hackers use. With a few simple actions, the average user can go a long way toward defending against the five most common methods of Wi-Fi hacking, which include password cracking, social engineering, WPS attacks, remote access, and rogue access points.

There's no doubt Kali has established itself as the most popular penetration distribution available. However, just because it's the fan favorite of beginners and security researchers doesn't make it right for everyone. Manjaro Linux is a beginner-friendly Arch-based distribution which can be easily weaponized with the Black Arch expansion, creating a friendlier first-time Arch experience.

The dark web is an intimidating place for a newbie hacker, but it's a powerful tool once you've learned to navigate it safely. To help you out with that, this guide will cover some need-to-know information for traversing the dark corners of the internet while keeping your identity and data safe. (Hint: Using Tor is not enough.)

In the ever-evolving world of podcasting, Apple has once again turned up the volume with new upgrades to its beloved Podcasts app. As the go-to platform for millions of listeners worldwide — thanks to its seamless integration with iOS, iPadOS, and macOS — Apple Podcasts continues to refine how we discover, enjoy, and manage our favorite shows.

The new Material You theme engine with its fancy widgets is a sexy change for Android, but there's another new Android 12 feature that's more than just pretty colors and curves.

Microsoft's new mobile operating system is officially out on the market, and programmers are hard at work developing new mobile apps for Windows Phone 7 devices. But there's a lot going on in this new platform, which means there's a whole lot to be learned, and the only man in the world with a Windows tattoo is here to help— Charles Petzold.

Since its launch in 2001, Wikipedia has become the number one reference site on the web, used by anyone and everyone, written by anyone and everyone. With over 18 million collaboratively written articles, there's backgrounds and descriptions on practically everything—if it exists, there's probably a Wikipedia page for it.

You've probably seen those deep-web images floating around on the Internet. Usually, it goes something like this: There is a towering iceberg and the deeper the underwater portion extends, the more “hidden” and “exotic” the content is described to be. Sometimes these images are accurate to a point, but most are just making things up.

Hundreds upon hundreds of free origami diagrams and animations are available at the Origami Club. I caught Design Sponge's recent post on some late night folding (I like how they spelled out their name), and recalled WonderHowTo's old favorite.

BrickLink is the Craigslist/Ebay/master aggregator of all LEGO commerce on the web. (Almost 100 million products currently for sale!)

I've been watching my Bocas del Toro, Panama weather for the last several months and the reports are correct. It rains a lot!

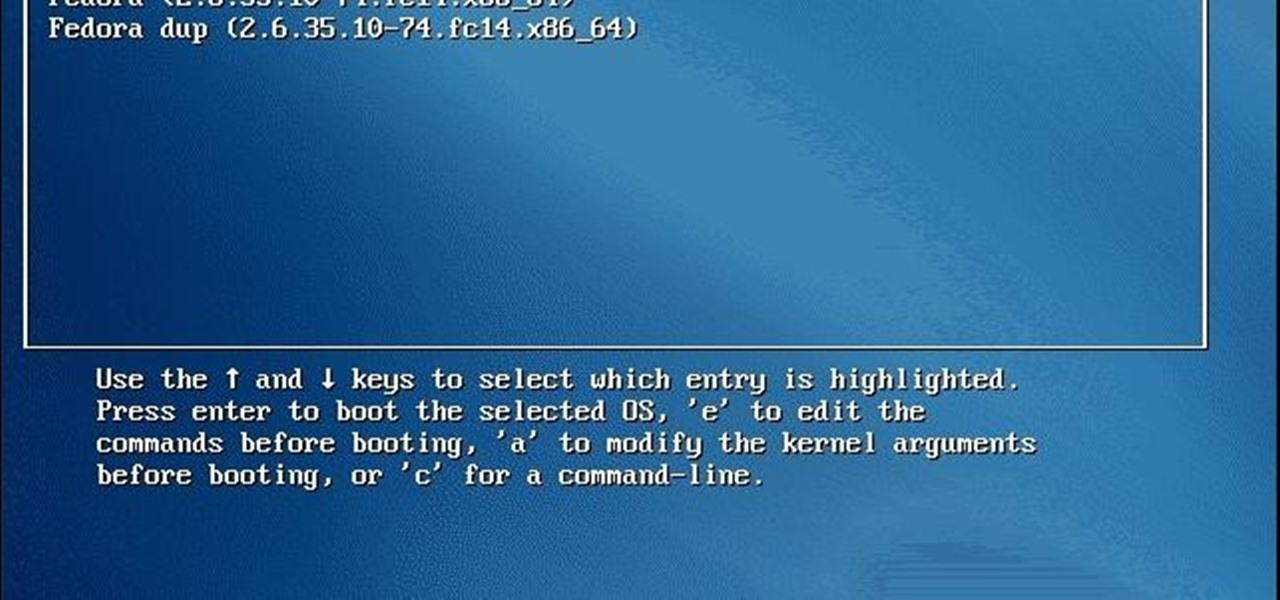
Hey guys, I am back this time with a small trick. Many of us do not like the old background in GRUB BOOT LOADER, you might be using kali linux or any other linux and using GRUB BOOT LOADER then this is for you.

Rube Goldberg meets Cool Hand Luke. Arguably pointless. Arguably quite satisfying.

Properly produced, a pointless bar trick is as much a how-to as a Mario Batali cooking instructional. We are non-discriminatory in that regard. While curating, we focus primarily on the INTENT of the video.

Anonymity is something that doesn't exist today. Everything you do in the world is tracked, from the purchases you make to surfing the internet—even taking pictures on your iPhone. Everything you have ever said and done on the internet is still there—somewhere. This is called caching. For example, when a site is down, you can view its cached page on Google.

What's cuter than a puppy? Not much, especially when you omit all the peeing, barking and furniture chewing, as Remedie Studio did with this sweet time-lapse homage to their beloved pup. Below, watch Dunder the German Shepherd grow from 8 weeks old to 1 year in 40 seconds. Inspired? Make your own time-lapse video and post it to the WonderHowTo company blog. We'll show off the best ones. Here are three different methods to get you started:

If you know anything about search engine optimization and online marketing then you know that having as many links going into your site from good sources is very important. And if you’re not really experienced at building links or SEO in general then you might not know the best way to get good links for your site. So please read on and I’ll present to you what I feel is the best way to get good quality links for your site.

GRUB, or the GRand Unified Bootloader, is a program that installs to your Master Boot Record and controls what operating system you load at boot time. Normally, it is used for multi-boot systems. Multi-boots allow you to switch between operating systems installed on seperate drives, or partitions at boot time. Linux actually uses it as its default bootloader, even without multiple operating systems.

Welcome to part three in a series about steganography, the art of hiding things in plain sight. We are practicing steganography because it can be a useful skill if you don't have access to encryption software, or need a quick solution to make sure the sender and recipient are the only ones who are able to read your message.

Last week, I demonstrated how to go a little deeper into your Google+ profiles, photos, and introduced cross-posting. This week, I'm highlighting a bunch of different unofficial resources that have sprung up that will help improve your Google+ experience, and give you the latest updates on Google+ Photos.