Many popular apps automatically share your personal data. While I have accepted a certain amount of data collection from Google, to know companies such as Facebook perform this without my consent bothers me. After some researching, I've found a great solution, and it doesn't require root.
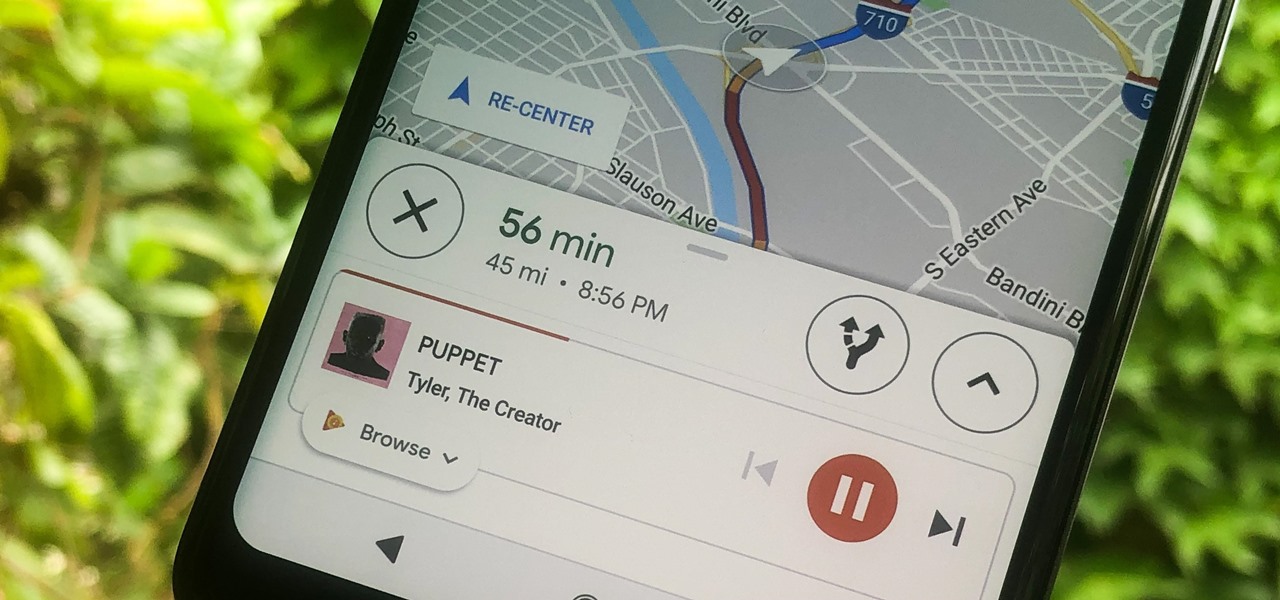
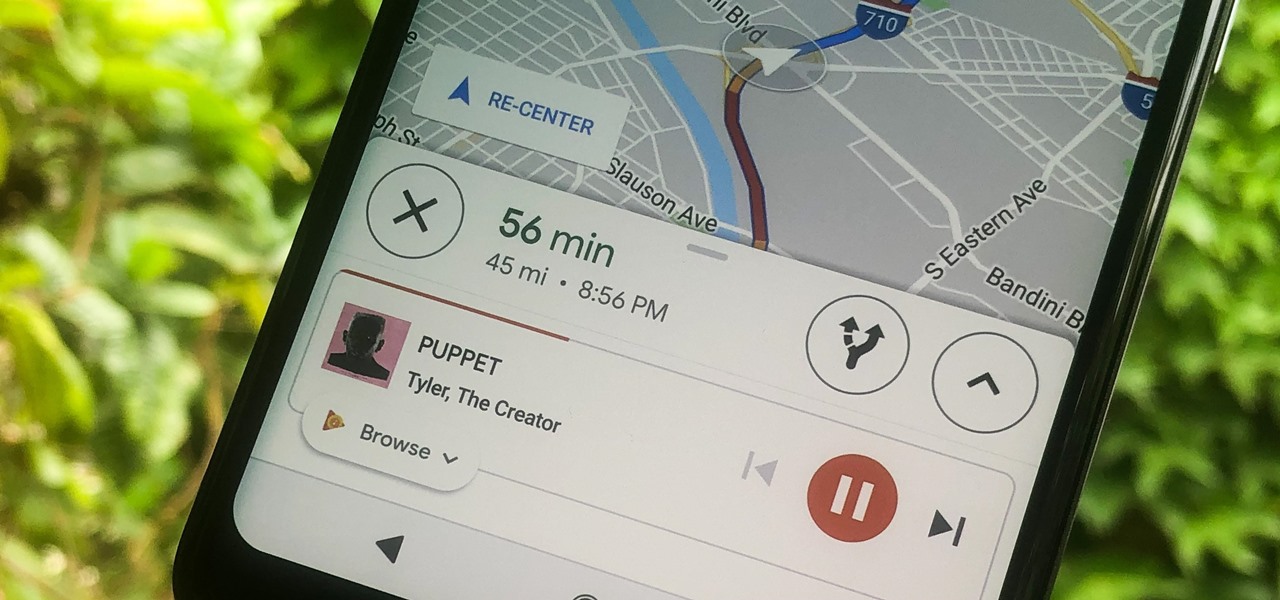
Staying alert to directions and changing the music you're listening to on your smartphone at the same time can be cumbersome, but Google Maps wants to fix that. One of the mapping service's features allows you to control music playing on Spotify, Apple Music, and Google Play Music from inside of Google Maps — while you're navigating in the car, on public transport, or even on your bike.

For those with small hands, smartphones have gotten out of control as of late. Nearly every flagship phone is over six inches in length, so many are forced to use phones that are too big for them and hope they don't fall. Well, thanks to one developer, using these phones can be a lot easier.

For those about to rock, Live Nation salutes you, now with augmented reality. This week, at the Cannes Lions Advertising Festival of Creativity in France, the live entertainment giant unveiled a suite of AR experiences that music festivals and their sponsors will be able to deploy in their mobile apps to engage attendees.
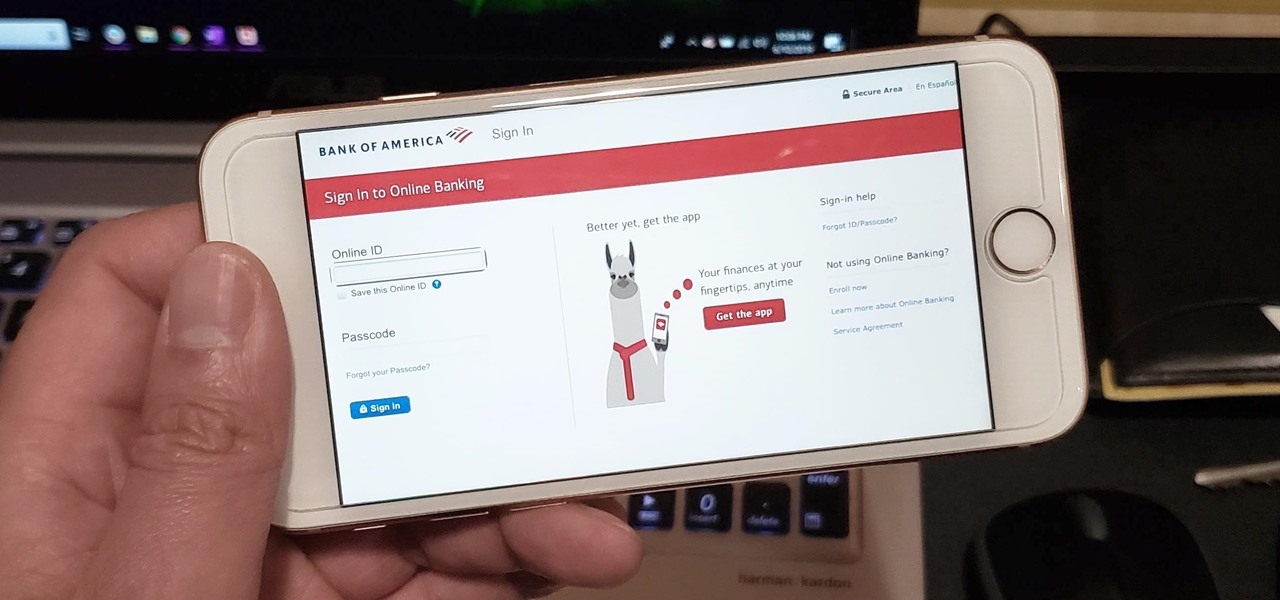
Ever since iOS 7, you could ask Safari on iPhone to show you the desktop version of a website, and in iOS 9, it became even easier to do. However, it's always been a hidden feature, something you wouldn't know is there without reading articles or tips online telling you what to do. Apple's iOS 13 update shines a light on it so everyone will know it's there, ready to use.

The natural marriage between fashion and augmented reality is charging onward, but not just from the major brands we already know about.

Lions and tigers and bears are just a few of the animals that Google users can now bring into their physical environments.

If you find yourself with a roommate hogging limited data bandwidth with video games or discover a neighbor has invited themselves into your Wi-Fi network, you can easily take back control of your internet access. Evil Limiter does this by letting you control the bit rate of any device on the same network as you, allowing you to slow or even stop data transfer speeds for them completely.

In order to save money, a few compromises had to be made when switching to Google Fi on an iPhone. No more Wi-Fi calling, no automatic network-switching, no hotspots outside the US, and no more visual voicemail. I've found that last one particularly frustrating — but not anymore. Visual voicemail is now available on Fi for iPhone, but it's not like it was before Fi.

Smartglasses maker Vuzix made a big splash at CES 2018 with the inclusion of Amazon's Alexa voice assistant among the AR superpowers of its consumer-centric Blade smartglasses.

Is there a bigger name in pop music than Taylor Swift right now? Her 116 million followers on Instagram would probably argue, "No." As such, if you're one of these many followers, you might have seen Taylor advertising a new "4.26" filter on her story. Problem is, there's no clear instruction for actually using the filter. That's where we come in.

Many of our online accounts now come with an added two-factor authentication (2FA) functionality to help keep our data safe. This essentially means no one would be able to access the account until a specific set of requirements were met. It could be a combination of a password with a security key or even a passcode with some form of biometrics, like a fingerprint or face scan.

The partnership between Magic Leap and leading South Korean wireless carrier SK Telecom took on an added importance earlier this week as the company unveiled the world's first nationwide 5G network.

So, you're on the way back from a restaurant and realize you left your iPhone there, but you're late for a meeting and can't go back yet. You may as well kiss that iPhone goodbye, right? Not yet, as long as the right person gets their hands on it first. But that potential do-gooder won't know to contact you, and that's where Find My iPhone's "Lost Mode" comes in handy.

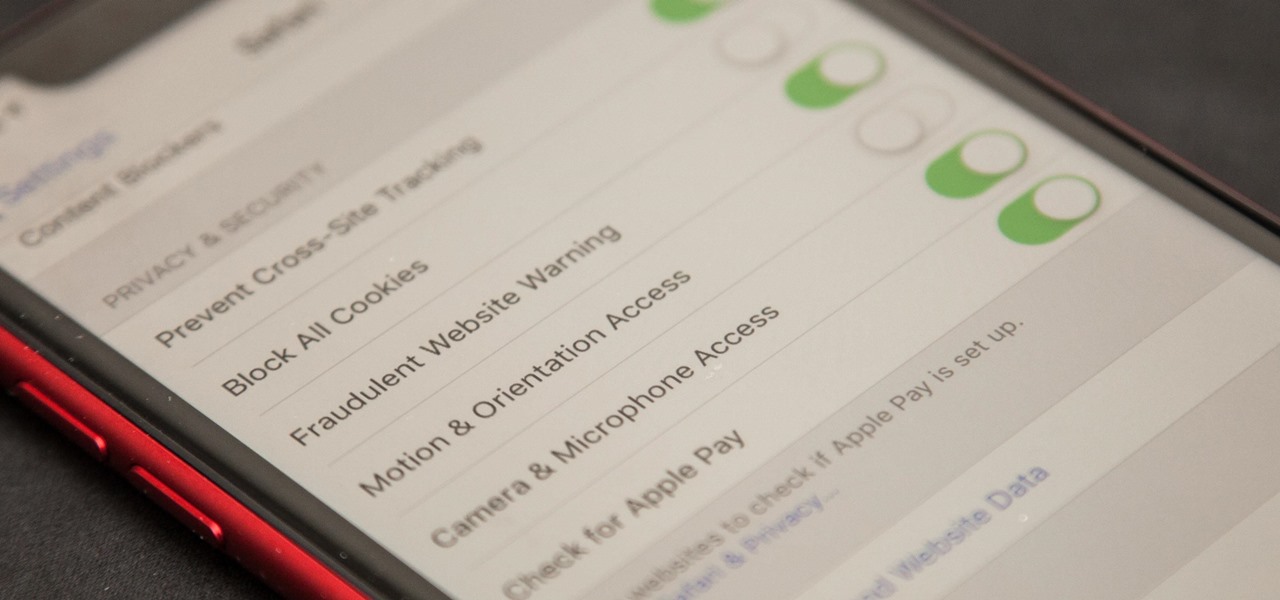
Apple first added the "Do Not Track" option to Safari in iOS 7, which sent a request to site owners and advertisers to not track your browsing activity. By tracking your activity, those third-parties could tailor content to you that you're more likely to interact with. While the feature was always opt-in, it's no longer a feature at all in iOS 12.2 on your iPhone.

You've had your fun swiping, but now it's time to walk away from all of your online dating apps. Whether it's because you found someone you're interested in or just need some time away, it's important to know how to permanently erase your online dating footprint — and that includes deleting your Bumble account.

On Thursday, Magic Leap decided to step up its efforts to foster its developer community by launching the Independent Creator Program.

With barely a whisper of augmented reality during the first day of its developer's conference, Samsung came out swinging on day two with the introduction of its version of the AR cloud and a partnership with Wacom that turns Samsung's S-Pen into an augmented reality magic wand.

As Samsung's very own take on Android 9.0 Pie, the newly-dubbed One UI (formerly Samsung Experience, and TouchWiz before that) comes with a slew of new features and redesigned elements for the Galaxy's interface. Many of the changes, like the redesigned native app icons, are readily apparent, but other features got subtle enhancements that greatly improve user friendliness.

Rooting. As an Android user, I'm sure you've heard the word once or twice. According to Kaspersky, 7.6% of all Android users root — but for the 92.4% who don't, we wanted to talk to you.

Apple unveiled the iPhone X-like redesign of its iPad Pro line Tuesday, Oct. 30. Among the many new changes to the company's famous tablet was a glimpse at its new wallpapers. These images, while clearly intended to take advantage of the new iPad's striking screen ratio, are clearly well suited for any iPhone as well. That's why we've made it easy for you to download them all.

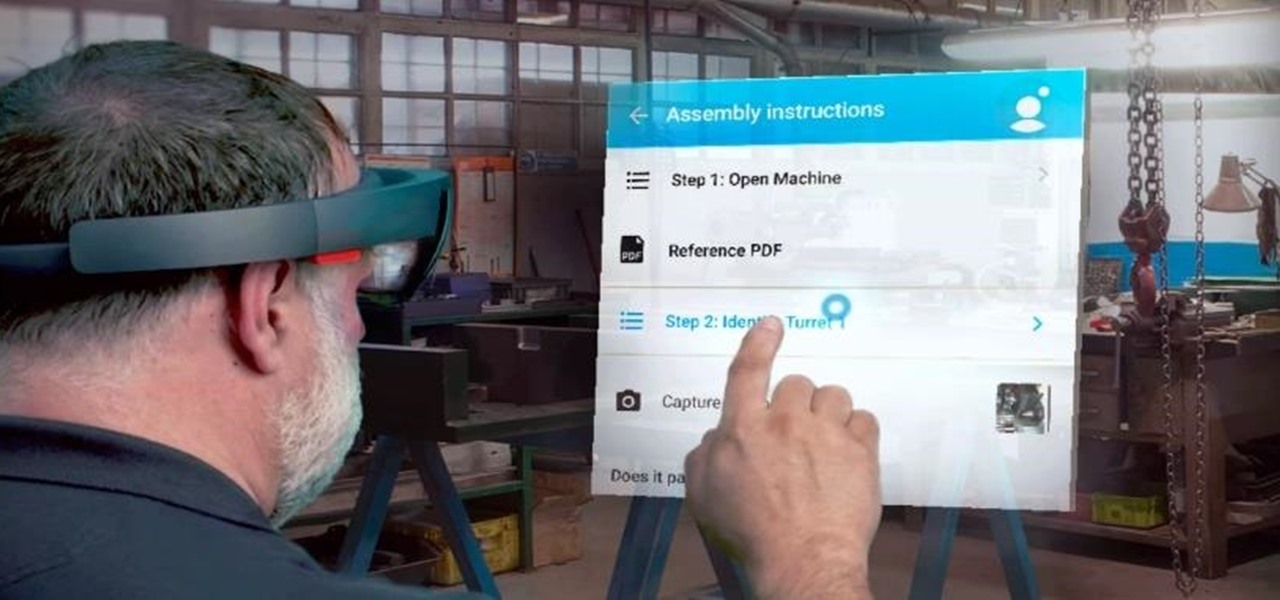
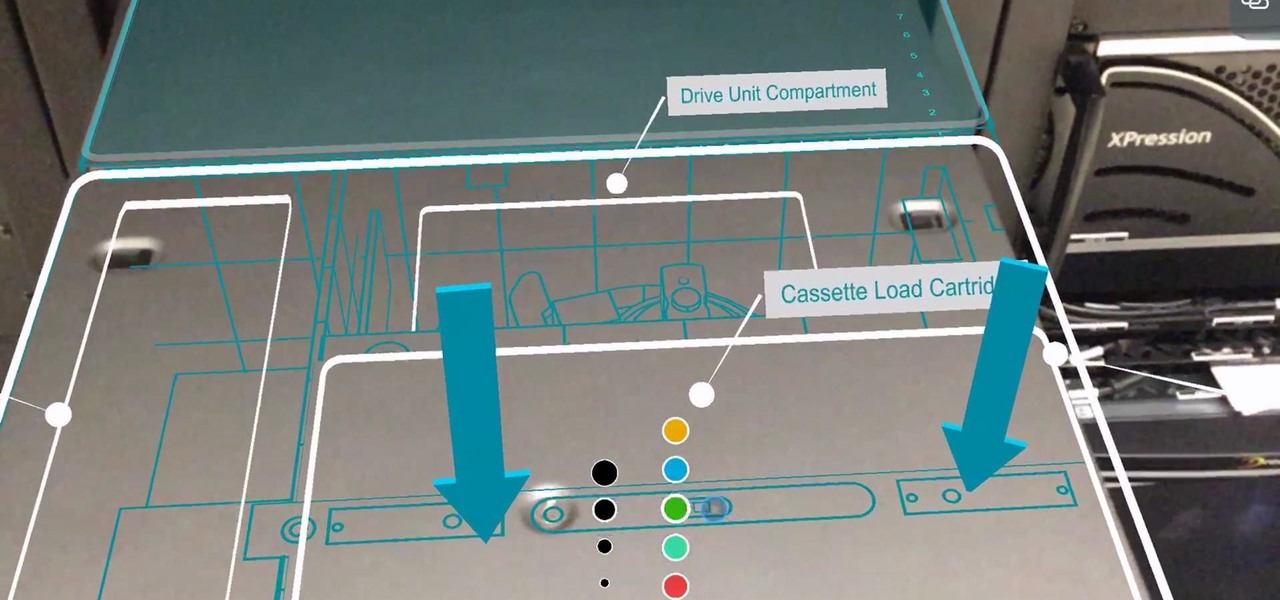
Augmented reality productivity software maker Upskill has expanded the reach of its Skylight platform with support for Microsoft HoloLens.

Venom, the latest in a long list of comic book characters to headline its own movie, is known by comic book fans by his catchphrase, "We are Venom."

If the iPhone XS, XS Max, or XR is your first Home button-free iPhone, you might have some questions, such as "How do I access the app switcher?" and "How do I use reachability?" While iPhone X owners have had over a year of practice, newcomers to Apple's buttonless revolution might feel a bit confused when it comes to actions they used to perform on iPhones with ease.

This year marks the first for Apple to exclude the Home button from any new iPhones. If you're going from a Home-button iPhone to a new XS, XS Max, or XR, you might be a bit stumped when trying to perform basic tasks, such as activating Siri. While you can't hold down the Home button any longer, there's a new method that's just as quick.

With iOS 12, Apple is offering users more options than ever to create, store, and manage their saved passwords. Not only can iOS 12 make you new passwords via the AutoFill feature, you can quickly and efficiently access your entire iCloud Keychain using Siri. Why go hunting for the passwords yourself when you can ask your iOS assistant to find them for you?

MacOS isn't known as an ideal operating system for hacking without customization, but it includes native tools that allow easy control of the Wi-Fi radio for packet sniffing. Changing channels, scanning for access points, and even capturing packets all can be done from the command line. We'll use aliasing to set some simple commands for easy native packet capture on a macOS system.

On Thursday, Epic Games released Unreal Engine 4.20, which finally includes support for the latest iterations of ARKit and ARCore, as well as Magic Leap One early access.

Augmented reality experiences created in Lens Studio now have a permanent home in the Snapchat app. On Tuesday, Lens Explorer will begin giving users access to a scrollable screen full of a variety of new Lens Studio creations.

With developers chomping at the bit to play with ARKit 2.0, Unity has updated its ARKit plugin to enable access to the new augmented reality superpowers of the toolkit.

Enterprise augmented reality software maker Scope AR is bringing the powers of its two productivity apps together like the Wonder Twins into the form of a single app.

Badges? We don't need no stinkin' badges! That is, unless they have augmented reality content embedded in them and give us full access to Facebook's annual F8 developers conference — in that case, yes, we'll take all the badges.

As you're surely aware, your phone can be used against you. Thanks to our cameras and microphones, a clever hacker can obtain access to your device and invade your privacy. But spying isn't limited to just these two sensors — gyroscopes, proximity sensors, QR codes, and even ads can be used to paint a very clear picture about who you are and what you're currently doing.

The augmented reality and VR arm of Verizon, Envrmnt, wants to make it really easy for anyone to create AR apps.

It looks like Google's feud with Amazon won't end anytime soon. A war has been brewing ever since Amazon pulled Chromecast, Apple TV, and other competing devices from their store in 2015, but the latest exchange is a huge blow to people using Amazon Fire tablets and streaming TV sticks.

If you're a golf fan who can't attend the Arnold Palmer Invitational in person, you can still follow the next stop on the apparent Tiger Woods comeback tour in augmented reality with an iPhone or iPad.

Hackers often rely on lazy system admins and unpatched vulnerabilities to get access to a host. Keeping intruders off of our machines requires us to update daily, only run the services we need, and read the code, among other things, but we can still make mistakes. Luckily for us, we can limit the damage caused by those mistakes by running SELinux.

As with most social media platforms, Instagram can be a double-edged sword. On one hand, it's a great way to share and express yourself — but on the other, it can be just as effective at compromising your privacy. Thankfully, there are a few things you can do to protect yourself.

When first released, Snap Map made a lot of users uneasy. Beaming their location to the world at all times isn't necessarily the definition of privacy, but Snapchat's map is nonetheless intriguing, offering users a view into the lives of people across the globe. Now, you don't even need to have an account to access Snap Map — you can view it right from your web browser.

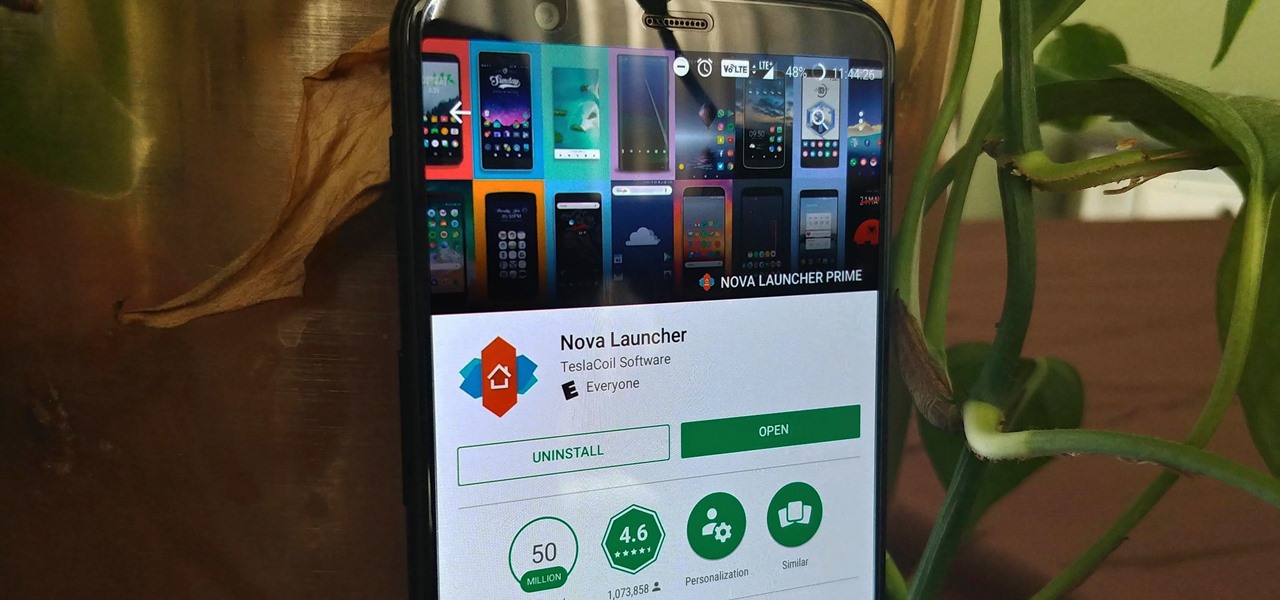
Nova Launcher is more than just a home screen replacement. It is a tool which can reshape how users interact with their Android devices. Thanks to a regularly growing feature list, Nova has evolved into more than just a launcher. Now, Nova is an effective way to increase your productivity.