Looking to inject a little more processing juice into your HoloLens? Unity can fix you up with the Standalone Universal Windows Platform Holographic Emulation.

Google Calendar is a cornerstone of the Google Suite, perhaps second only to Gmail itself. Whereas email is constantly plagued by phishing attacks, as of yet, the calendar is a relatively untapped social engineering attack vector. But it's relatively easy for an attacker to inject a meeting or event into a target's Google Calendar and use it to exploit them.

Harry Potter fans can set down their wands for a spell, as the highly-anticipated augmented reality game from Niantic based on the franchise won't arrive until after July at the earliest.

JavaScript is one of the most common languages used on the web. It can automate and animate website components, manage website content, and carry out many other useful functions from within a webpage. The scripting language also has many functions which can be used for malicious purposes, including stealing a user's cookies containing passwords and other information.

Almost every Android device comes with a Google search bar embedded directly into its stock home screen app. But Google search is available in so many different places on Android that having this bar in your launcher is almost overkill. On top of that, Google recently changed the logo overlay to a more colorful one that may clash with your home screen theme, so there's plenty of reasons to dislike this feature.

The headsets of tomorrow offer some amazing possibilities in both gaming and work, but what we've seen so far only begins to scratch the surface. The US Navy saw the potential to use augmented reality in a helmet to provide divers with an incredible amount of information we have so far only seen in Hollywood movies.

Want to customize your Treo 750's Today screen and menu items? Watch this electronics tutorial video to learn how to customize your Palm Treo 750 to make it fit your personality and preferences. This video is great for new Palm Treo 750 owners.

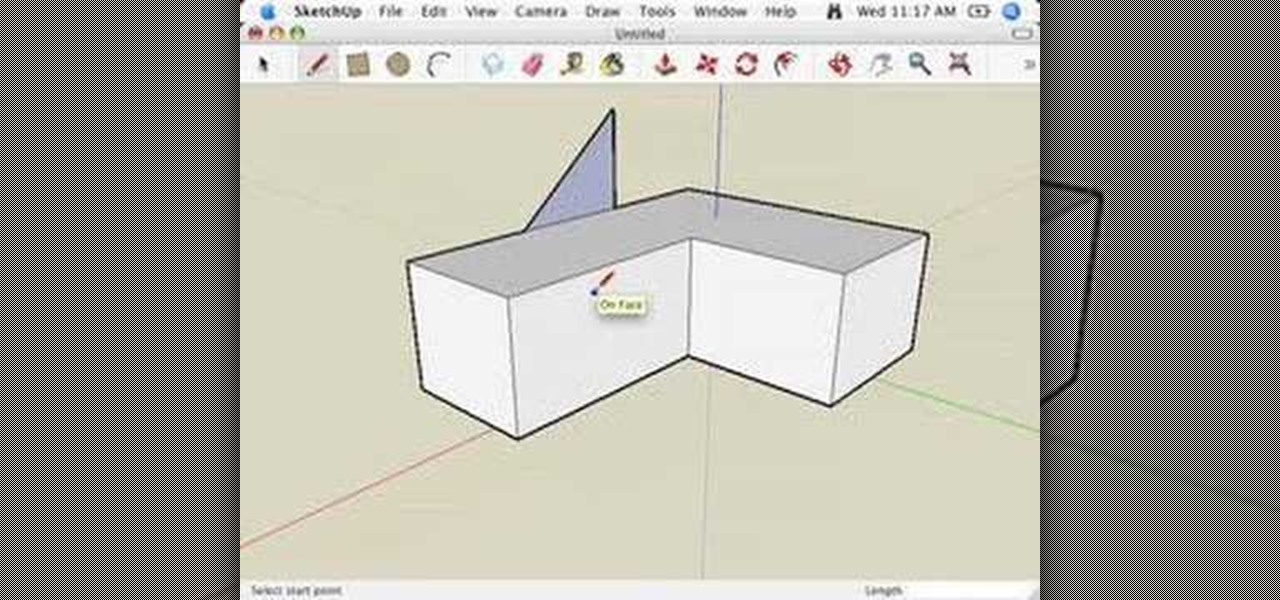
This video series helps you understand and get in the right mindset to model in SketchUp. It accompanies Chapter 2 of Google SketchUp for Dummies. PART 1 explains the relationship between edges and faces. PART 2 shows you how to give instructions with the drawing axes. PART 3 explains about keeping an eye out for inferences which help with accuracy. PART 4 shows you how to use those inferences to help you model - specifically locking and encouraging them. PART 5 covers how to get the best vie...

SSH, or the secure shell, is a way of controlling a computer remotely from a command-line interface. While the information exchanged in the SSH session is encrypted, it's easy to spy on an SSH session if you have access to the computer that's being logged in to. Using a tool called SSHPry, we can spy on and inject commands into the SSH sessions of any other user logged in to on the same machine.

Cross-site scripting can be one of the easiest vulnerabilities to discover, but to be successful with this type of attack, it is essential to learn how to get past filters. In the previous guide, we explored some ways to do this, such as abusing attributes and event handlers and tricking the application into accepting unusual characters. Now, let's take a look at more techniques used to defeat filters.

There is no shortage of defenses against cross-site scripting (XSS) since it is so prevalent on the web today. Filters are one of the most common implementations used to prevent this type of attack, usually configured as a blacklist of known bad expressions or based on regex evaluation. But there is hope with a wide variety of techniques that can be used to defeat these filters.

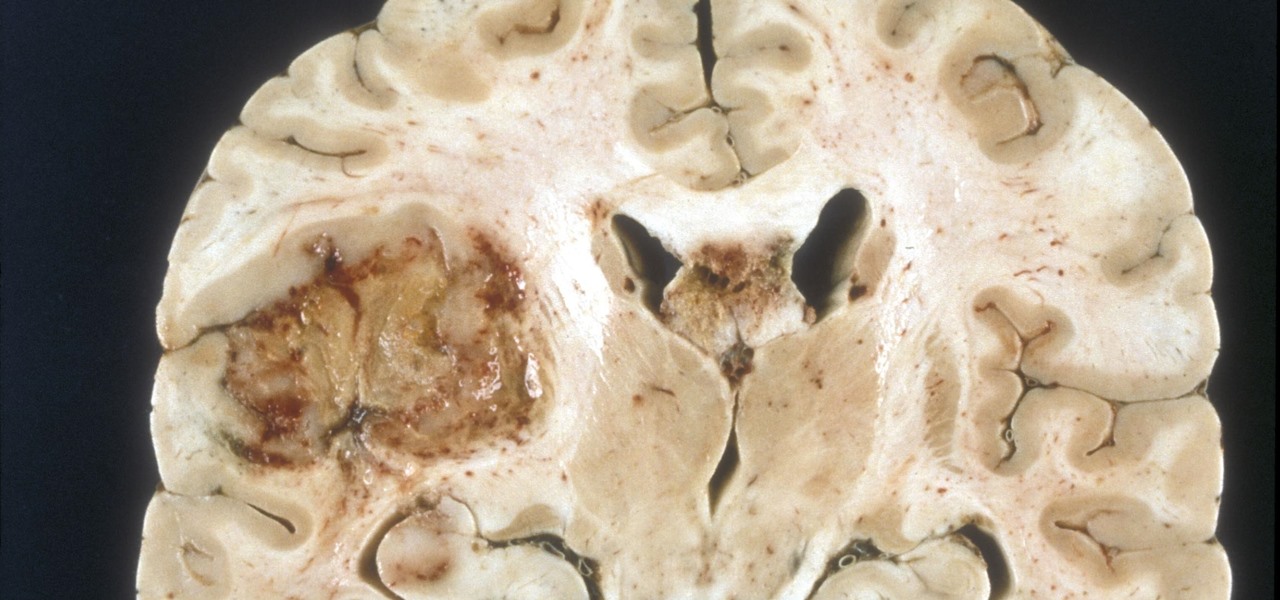
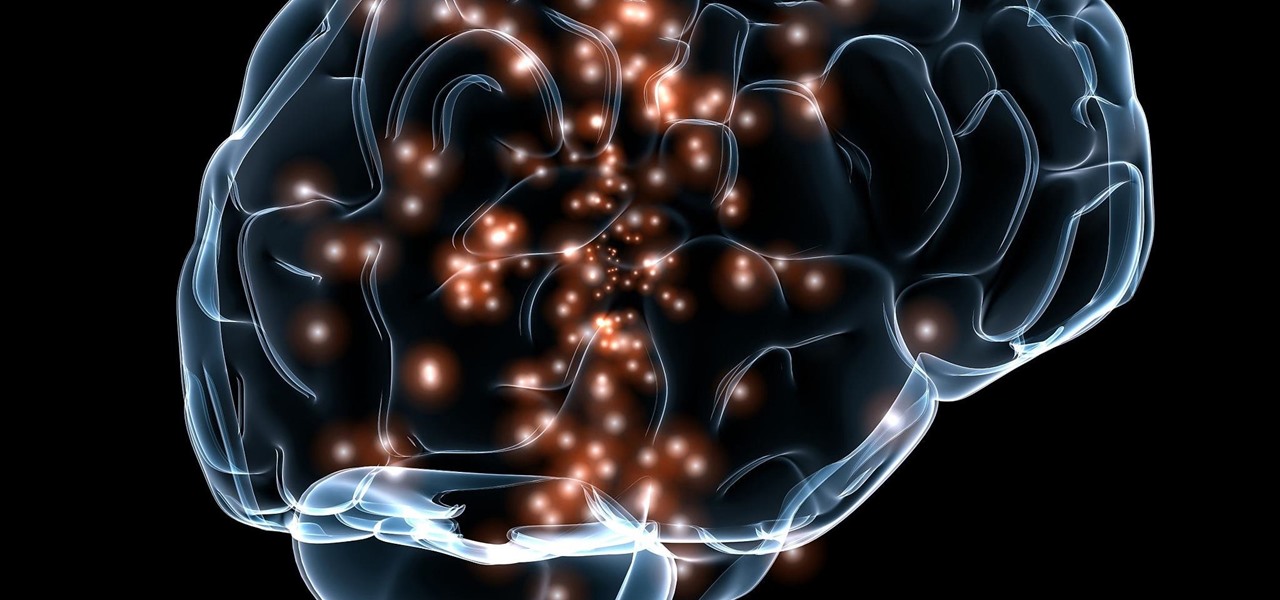
A deadly type of brain tumor and Zika-related brain damage in developing fetuses are devastating brain conditions that, at first glance, may seem unrelated. However, thanks to new research, their paths seem to cross in a way that could benefit patients. A new study has shown that Zika kills brain cancer stem cells, the kind of cells most resistant to treatment in patients with glioblastoma, a deadly brain tumor diagnosed in about 12,000 people in the US each year.

Chris Brogan is no stranger to using multiple social media platforms all from the comfort of his phone. In fact, not only does he have over 350,000 followers on Twitter, but he's also an avid YouTuber, Instagrammer, podcaster, and blogger.

If you need a tiny, flexible attack platform for raining down human-interface-device (HID) attacks on unattended computers, the USB Rubber Ducky is the most popular tool for the job. By loading the Ducky with custom firmware, you can design new attacks to be effective against even air-gapped computers without internet access. Today, you'll learn to write a payload to make "involuntary backups" through copying a targeted folder to the Ducky's USB mass storage.

Wondering what cat is best for you? If you’ve decided to adopt a cat, learn what different breeds can offer so that you can give your new feline a forever home.

Is your BFF getting married? Looks like you have a bridal shower to plan! Organize a bridal bash that people will actually want to attend using these innovative ideas.

Approximately 4 percent of women are diagnosed with gestational diabetes during pregnancy. Here's how to manage it.

While the USB Rubber Ducky is well known by hackers as a tool for quick in-person keystroke injection attacks, one of the original uses for it was automation. In this guide, I'll be going the latter, explaining how we can use it to automate Wi-Fi handshake harvesting on the Raspberry Pi without using a screen or any other input.

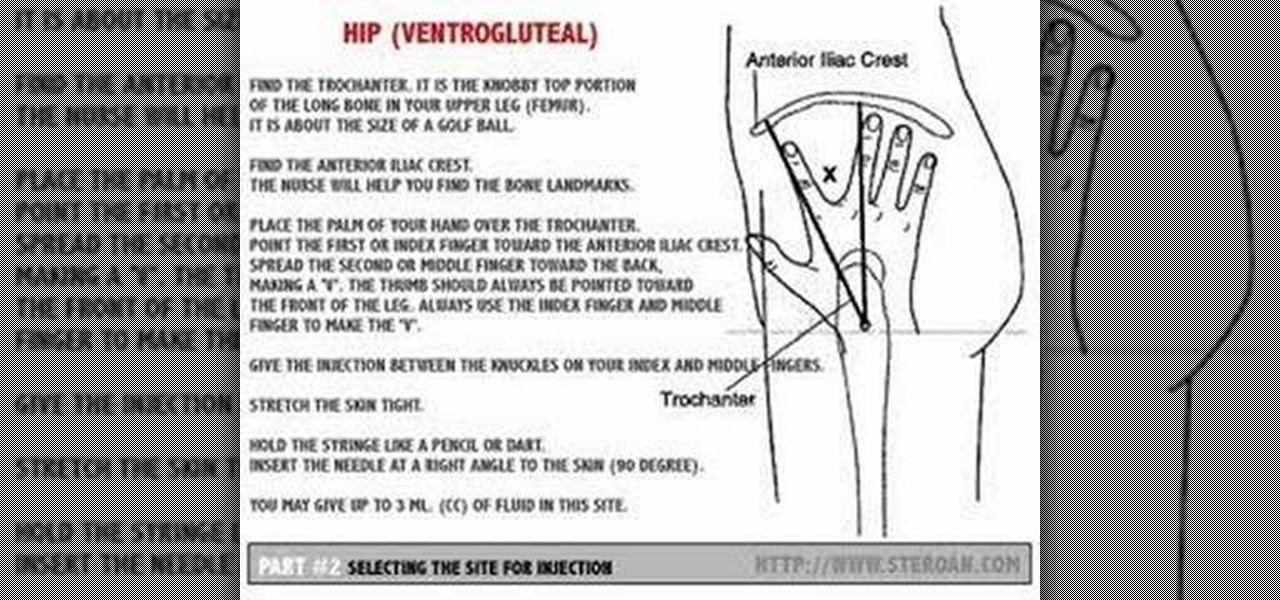
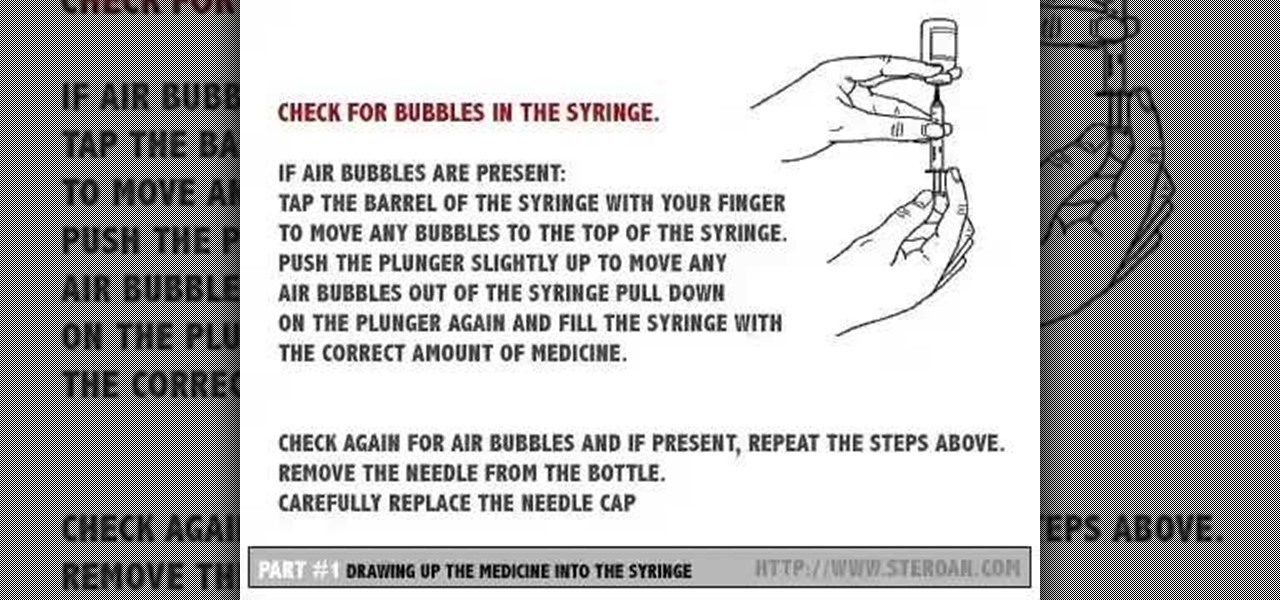
Injecting intramuscularly is a difficult thing to learn and it takes a lot of practice. This instructional medical how to video guides your through the step by step process of giving an intramuscular injection. Watch and read along. It is important to wash your hands before handling any injection material.

Injecting intramuscularly is a difficult thing to learn and it takes a lot of practice. This instructional medical how to video guides your through the step by step process of selecting a site for an intramuscular injection. Intramuscular injections should be given in areas where major blood vessels and nerves are avoided. Watch and read along. It is important to wash your hands before handling any injection material.

Injecting intramuscularly is a difficult thing to learn and it takes a lot of practice. This instructional medical how to video guides your through the step by step process of drawing up a substance for an intramuscular injection. Watch and read along. It is important to wash your hands before handling any injection material.

If you're interested in nabbing superhero memory strength, the secret behind training your brain is not necessarily what you might expect. Your standard G-rated brain strengthening exercises range from crossword puzzles to Sudoku to calculating fairly simple math problems to improve short term memory, but the real clincher used by some of the pros is essentially... porn. Yep, you read right.

Miis are tiny versions of you that live inside your video games. On the Nintendo Wii you can personalize all of your games and add a little bit of your personality and appearance to the screen. Check out this video tutorial, and learn how to create a Mini Mii on your console for gameplay.

One vital part of Android 10's new navigation system is the "QuickStep" gesture. Swipe up from the bottom of your screen, then pause. You'll see your recent apps along with a dock containing a handful of icons for quick access. This dock is provided by the phone's launcher, which means your home screen is now integrated into the multitasking UI. So what happens if you change your home screen app?

If you need to know whether you are really a Hufflepuff or a Gryffindor, then it's time to get yourself an augmented reality sorting hat.

Ever since Skynet took over the world in the Terminator film franchise, a large segment of the world's population has feared artificial intelligence.

While Gucci is among the most recognizable brands in fashion, you would be excused for not realizing that the company makes sneakers as well.

After some social media teasing, the Star Wars universe's Magic Leap debut has finally arrived. On Tuesday, Magic Leap announced the release of Star Wars: Project Prog, which is available for free via Magic Leap World.

Despite the relatively small size of Magic Leap's first annual L.E.A.P. conference, there was a lot to see and experience. Apparently missed by many was one of the best experiences I had at the event: Wingnut AR's unreleased Pest Control game.

One option you won't find buried in the Galaxy Note 9's Settings is the ability to return the navigation bar to black. Samsung changed the default color to white with the Note 8, removing any ability to bring the black color back. But thanks to a neat app, Note 9 users can do it themselves.

The Super Bowl of bicycle racing, the Tour de France, added augmented reality to its TV broadcast this year.

In the latest example of life imitating art, IBM has applied for a patent for a video censoring system that looks a lot like the "Arkangel" child monitoring system from the latest collection of modern sci-fi fables from Black Mirror on Netflix.

Your Instagram bio could always be used to link to other websites or profiles or just to show off your witty personality. Now, you also have the ability to use this section to tag other Instagram accounts as well as add tappable hashtags. Whether you want to link out to your best friend, company, or the latest trend in your city — if it has a profile name or tag, it can be in your bio.

These days, location-based augmented reality gaming pioneer Niantic is best known as the developer behind Pokémon Go, but the uber-popular mobile game was not its first foray into the AR gaming genre.

While millions eagerly await the stable Android 8.0 release for the Galaxy S8, the beta is already in the wild and readily available. Notable improvements include notification channels and the revamped Samsung keyboard. One aspect often overlooked are new customization options, a huge part of Android. Let's take a look at what's new for customization on the S8's home screen in Oreo.

A vaccine against HIV might prevent the disease that we can't seem to cure. Some HIV patients make antibodies that can take down the virus, much the way a vaccine might. But, scientists haven't been able to provoke that type of response in other people. However, in a process that might work in humans, a group of researchers has successfully generated antibodies in cows that neutralize multiple strains of HIV.

More than one in ten people in the US have type 2 diabetes — that's over 29 million people. It's characterized by excessive sugar (glucose) in the blood due to the development of resistance to insulin, the hormone that normally metabolizes glucose.

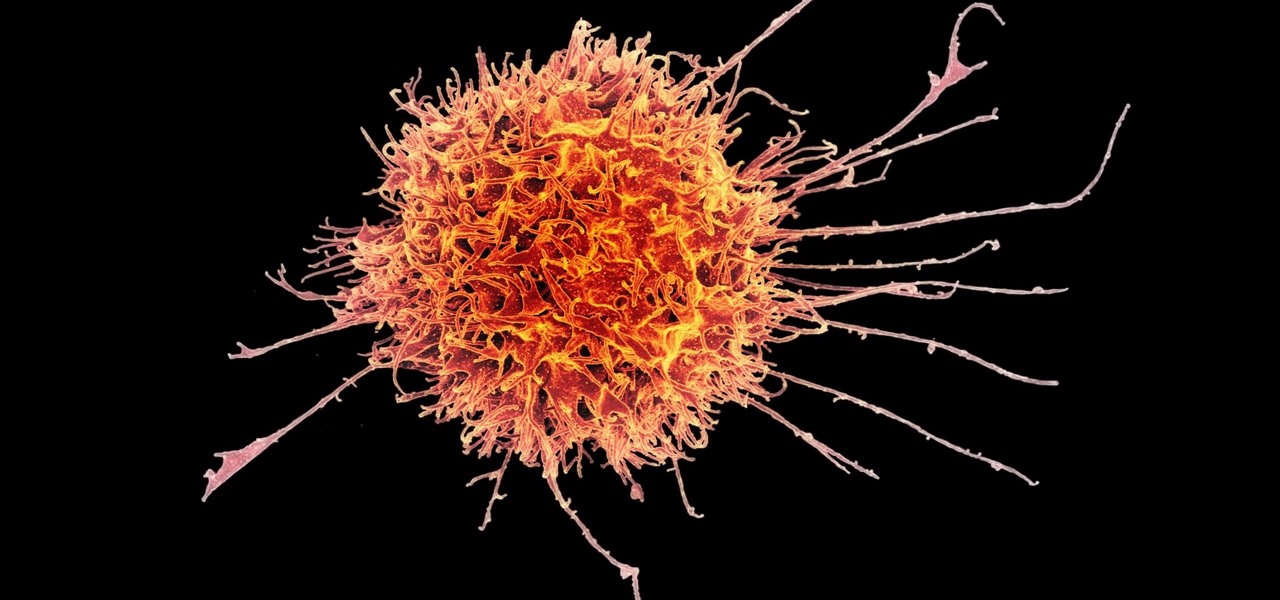
Cancer cells do a pretty good job of flying under the radar of our immune system. They don't raise the alarm bells signaling they are a foreign invader the way viruses do. That might be something scientists can change, though.

Despite mounting scientific evidence that viruses can cause changes in learning and memory, the reasons have remained elusive.