
How To: Disable auto login in Mac OS X
This video shows how to enable automatic login for Macintosh Operating System users: 1.Click on the Apple icon in the top-left corner and select System Preferences.


This video shows how to enable automatic login for Macintosh Operating System users: 1.Click on the Apple icon in the top-left corner and select System Preferences.

Watch to learn how to replace the HEPA filter on a Dyson DC07 vacuum. This Dyson spare parts video we show how to remove and replace the Dyson DC07 Pre Motor Filter and Dyson DC07 HEPA Post Motor Filter. This vacuum maintenance video also outlines the Dyson airflow path as well as removal and replacement of the Pre Filter Housing, Post Filter Lid and Filter Seals. Prevent loss of suction and motor cut out by changing the filters on your Dyson.

Watch to learn how to replace an AEG fridge freezer door seal. You'll remove and replace the freezer door seal on an AEG fridge freezer. You will have a more efficient freezer and prevent energy loss if you replace a worn freezer door seal. One of many simple freezer maintenance tips that will help ensure you have the correct freezer temperature.

Watch to learn how to replace the HEPA filter on a Dyson DC04 upright cleaner. You'll remove and replace the Pre Motor Filter and the Post Motor HEPA Filter on a Dyson DC04 vacuum cleaner. It is important to change the filter regularly as part of regular vacuum maintenance and to prevent loss of suction.

Watch to learn how to replace the HEPA filter on a Vax VEC04 vacuum cleaner. See how to remove and replace the central HEPA filter and the post motor anti-bacterial filter on a Vax VEC04 vacuum cleaner. It is important to change the filter as part of regular vacuum maintenance and to prevent loss of suction.

Rogaine is a popularly used produce for hair loss and regrowing hair. Rogaine is a topical form of minoxidil and its use on the scalp to help thicken the hair. Minoxidil was initially use for blood pressure medication and has discovered the patients that took minoxidil had hair growth on their bodies. Learn more about Rogaine and hair loss in this how-to video on beautification treatments.

We prune roses for several reasons. Regular pruning helps to keep their size under control, though we must remember that all roses have a predetermined 'ideal' size. We also prune to shape the plant. We take out dead stems to prevent the dead area spreading back into healthy stems. But the main reason we prune is to make the rose more vigorous. This tutorial teaches you how to prune climbing roses for the best results.

This is a video showing the drilling of live rock from a saltwater reef tank. The 1/2" holes are used for mounting pegs made from acrylic rods or other types of pegs or frag plugs. The live coral are attached to the end of the peg and can easily be positioned in the tank. This process also facilitates moving the coral to another location at a later time, they can be removed from the holes somewhat easily. It also prevents coral from falling as once its pegged well, its pretty much going to st...

Learn how to clean your auto engine with these great tips. • Apply spray wax to fenders to prevent spotting on the paint, from engine degreaser. • An alternator is a crucial electrical device which must be protected from water and other chemicals. as a precaution, cover it with a plastic bag and the distributor cap if it is visible. • Spray WD40 on any exposed wires to prevent water or chemicals from penetrating. • Wet underneath the hood; wet the engine; use low pressure water on the engine ...

The iOS 16 update for iPhone has many new and exciting options, most of which improve the user experience overall. Some of the features and changes fix frustrating issues from iOS 15 and older, and some of those "fixes" can seem annoying if you're used to doing things a certain way.

It's easy to accumulate hundreds of Safari tabs on your iPhone, which makes hunting for specific tabs more difficult, especially when they're spread across different groups. Having too many tabs can even slow down Safari itself. You can close all tabs in a group quickly, but not if you want to save some. To prevent this mess, Safari can automatically weed out the tabs it thinks you don't need.

When it comes to the ever-shifting sands of the augmented reality space, you never know which week will end up being truly historic. Well, this one was one for the history books.
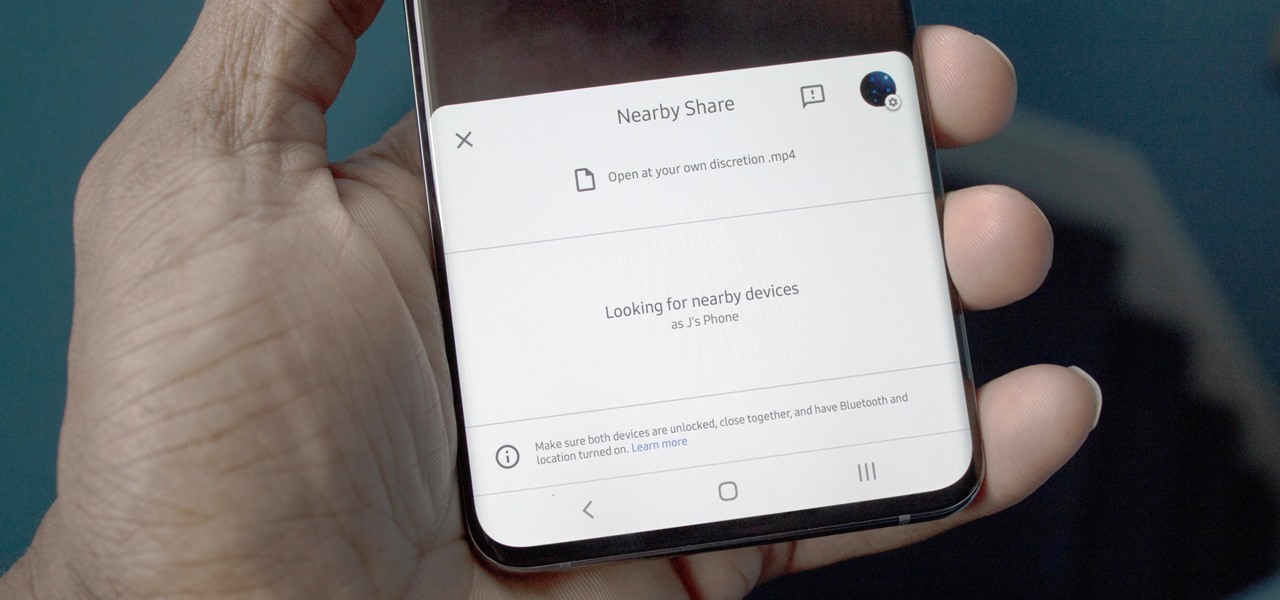
Android has finally got a proper alternative to Apple's AirDrop. With a few touches, Nearby Share lets you send files, links, and even tweets to Android, Windows, macOS, ChromeOS, or Linux. But AirDrop has not been without its share of issues, and thankfully, Google has learned from them.
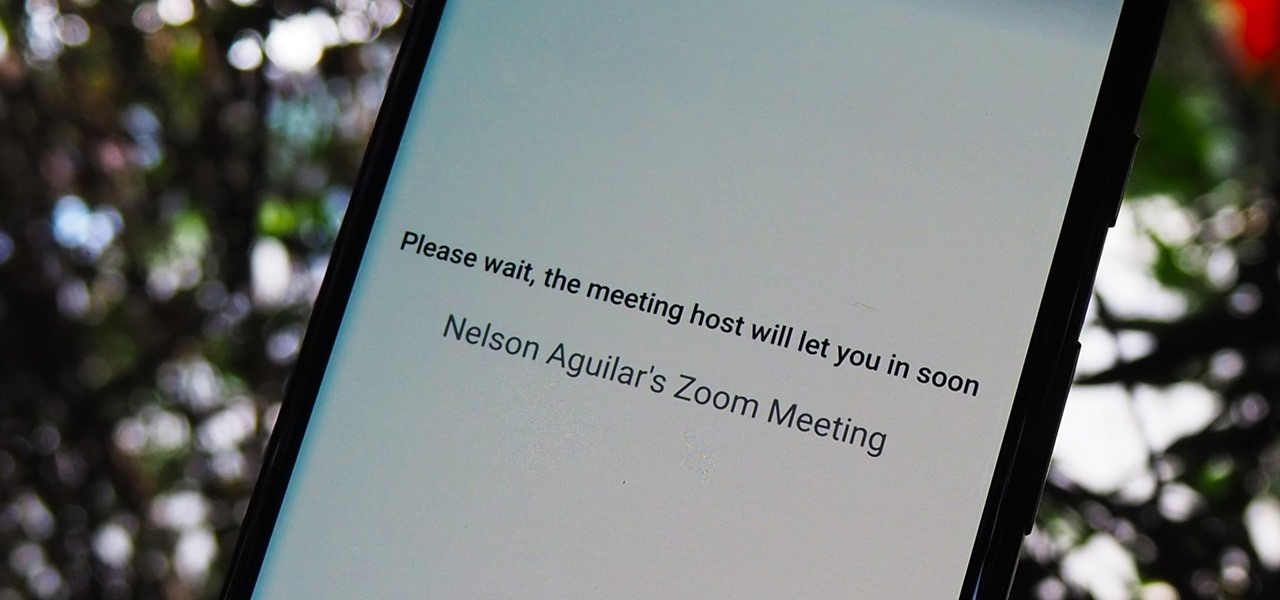
The "Zoombombing" trend is still strong on the Zoom video meetings service, despite security measures Zoom put in place to stop it. That's why it's up to you, as either a host or co-host, to be proactive about preventing Zoombomber harassment, as well as stopping it whenever it slips through the cracks.

Without admin privileges, installing additional software, or modifying the Windows 10 firewall, an attacker can alter a router and perform a variety of exploits. It's accomplished by forwarding requests from Kali through a backdoored Windows computer to the router gateway with simple SSH tunnels.

As fun as Twitter is, it can also quickly turn scary. Anonymous, aggressive, and troll accounts can attack you for your tweets and stalk your every move. While you could make your profile private and block users, there are lesser-known privacy and security features that you can switch to improve your safety online.

It wasn't long ago Apple released iOS 13.2 to the masses. The second major update to iOS 13 included 22 new features and changes that added a significant layer of depth to an already feature-filled experience. Apple isn't ready to stop the fun, however, as iOS 13.3, released Dec. 10, has a decent amount of new features too.

Apple's iOS 13 has been quite the disrupter. The initial update featured over 200 new features and changes, while its successor, iOS 13.1, brought another 22 to the mix. With the company's latest update, iOS 13.2, you'll see an extra 22 amendments on your iPhone, including new emojis, Deep Fusion on iPhone 11, 11 Pro, and 11 Pro Max, and Announce Messages with Siri, just to name a few.

Passwords on Windows are stored as hashes, and sometimes they can be tough to crack. In certain situations, though, we can get around that by using the hash as is, with no need to know the plaintext password. It's especially interesting if we can manage to get the hash of an administrative user since we can then authenticate with higher privileges by performing an attack known as pass the hash.

If you find yourself with a roommate hogging limited data bandwidth with video games or discover a neighbor has invited themselves into your Wi-Fi network, you can easily take back control of your internet access. Evil Limiter does this by letting you control the bit rate of any device on the same network as you, allowing you to slow or even stop data transfer speeds for them completely.

Whether we like it or not, our personal information and smartphones are tied together at the hip. The former needs the latter to deliver a personalized experience that matches our individual needs. This personal data, however, makes your phone a prime target for thieves of all sorts to turn your privacy into illicit profit.

WhatsApp is the go-to messaging app for millions worldwide and its easy to see why. The app can be considered the Swiss Army Knife of texting thanks to numerous features like Group Chats and Status Stories, in addition to striking a great balance between ease of access and overall security.

Among the younger generation, Roblox rivals major titles like Minecraft as one of the most popular online games out there. In fact, it's common to hear children tell new playmates to "friend me in Roblox!" so they can play together online. There's nothing inherently sinister here, but with all the online interaction, kids' safety becomes a factor.

Every photo you take is brimming with metadata such as iPhone model, date and time, shooting modes, focal length, shutter speed, flash use, and geolocation information. Share these pictures with friends, family, or acquaintances via texts, emails, or another direct share method, and you unwittingly share your location data. Even sharing via apps and social media sites can compromise your privacy.

Encrypting payloads and encoding stagers are more effective against macOS than one might think. It's very easy to evade VirusTotal and macOS antivirus software using a few simple tricks.
Smartphones and laptops are constantly sending Wi-Fi radio signals, and many of these signals can be used to track us. In this guide, we'll program a cheap IoT device in Arduino to create hundreds of fake networks with common names; This will cause nearby devices to reveal their real trackable MAC address, and it can even let an attacker take over the phone's data connection with no warning.

Although the Galaxy Note 9 is an amazing phone, many members of the Android community won't even look at it. This isn't just because of the Samsung Experience skin, but the large amount of bloatware that comes with this device. However, with a little work, you can remove all of it.

Three new iPhones means you have to make a choice: Do you go with the smaller iPhone XS, the larger iPhone XS Max, or the cheaper iPhone XR? There's lots to like about each model, but if you want to make an informed decision, it's time to learn what each has to offer. Here's what the iPhone XS Max brings to the table.

Back in July, Google rolled out a new design for the web version of Gmail. The rollout included new features alongside the visual changes, one of which being Confidential Mode. This new privacy-centric feature has now finally arrived on the mobile app version of the service, and here's what you need to know.

If you want to use your iPhone with another carrier, all you have to do is contact the original carrier to request an unlock, which is usually granted in a few days. Unfortunately, you need to meet specific criteria to officially carrier-unlock your iPhone, like paying off the device in full and completing any contracts. But that doesn't mean there isn't a workaround you can use beforehand.

Command injection is a technique used by hackers to execute system commands on a server, usually via a web application or some kind of GUI. This can happen when an application provides some sort of functionality to the user involving the use of system commands. When the input is not properly sanitized, commands not originally intended to be run are allowed to be executed.

Hacking Wi-Fi is a lot easier than most people think, but the ways of doing so are clustered around a few common techniques most hackers use. With a few simple actions, the average user can go a long way toward defending against the five most common methods of Wi-Fi hacking, which include password cracking, social engineering, WPS attacks, remote access, and rogue access points.

We need to take our privacy and security much more seriously. Whether it's malware-infected apps or the mishandling of our data by companies like Facebook, there are threats all around us in this digital world. Fortunately, some smartphones are simply designed to protect us better.

Don't think because your MacBook is using FileVault disk encryption your device is secure or immune to hackers. Here's how to find out if that FileVault password is strong enough to withstand an attack from a motivated attacker.

Many operators use elevators to control access to particular floors, whether it be the penthouse at a hotel or a server room in an office building. However, the law requires them all to have a fire service mode, which gives emergency access to restricted floors, and a hacker can use that to bypass security altogether.

Realizing there's no voice to guide you while using your iPhone to navigate can be problematic, causing serious headaches from getting lost to unscheduled pit stops or worse. And while this problem can hit Apple Maps like other navigation apps out there, there are a number of fixes you can try to get navigation audio working again.

| Update: ZTE's issues with the US government have finally been resolved. Check out the details below.

Using a keylogger to intercept keys pressed on an infected computer can circumvent encryption used by email and secure chat clients. The collected data can often reveal usernames, passwords, and potentially compromising and private information which hackers abuse for financial gain.

With ultra competitive games like Fortnite Battle Royale and PUBG taking the mobile world by storm, gamers are looking for ways to get a leg up on the competition. One of the biggest advantages you can give yourself is the ability to aim and shoot while on the move, but that's not exactly easy with a touchscreen.

Even though most phones don't have Oreo yet, Google has released Android 9.0 Pie. It's available on Google's own Pixel devices, and updates should soon be available to partnered devices from Essential, Nokia, Oppo, Sony, Vivo, and Xiaomi. We're already digging into it to highlight all of the features and changes.