As we're all aware, recon is vital to a successful hack. We need to know everything we can about the target in order to perform the best possible attack. Port scanning is a basic recon concept that is introduced very early in learning proper reconnoissance. The issue with port scanning is that is makes a lot of noise. Every connection to every port will be logged. This is where stealth scanning comes in. Also known as SYN or half-open scanning, stealth port scanning is a bit quieter, and is l...

With intelligent grammar check, accurate predictive text, swipe gestures, and plenty of themes, it makes sense that Ginger Keyboard has well over a million downloads on the Google Play Store, making it one of the more popular keyboards available for Android users.
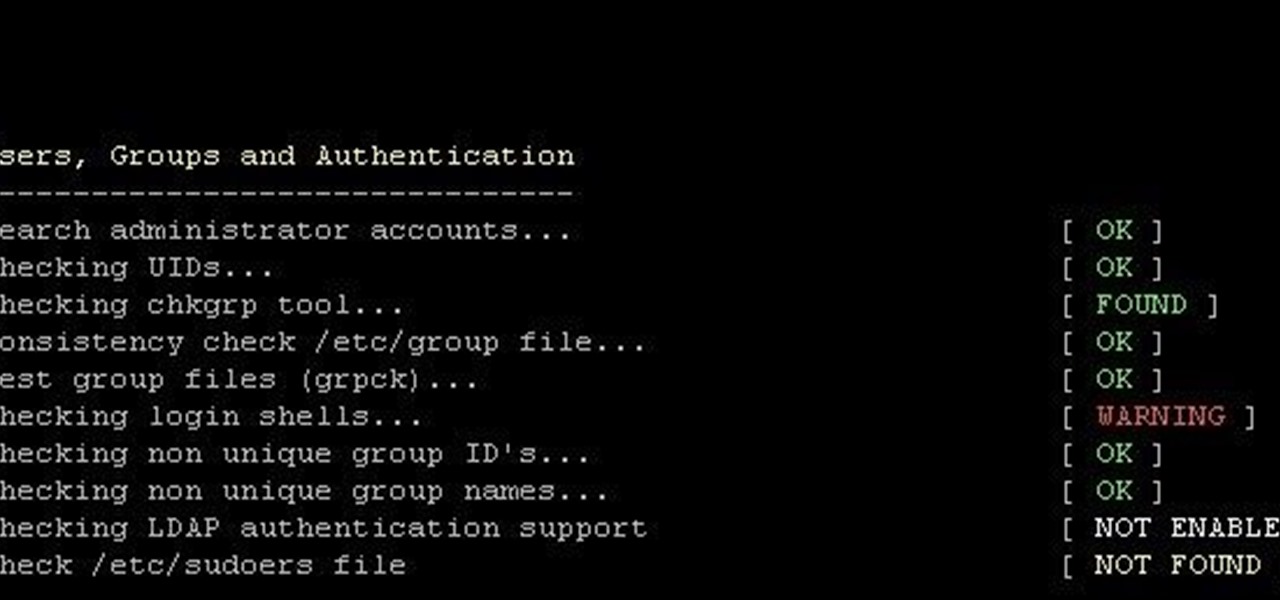
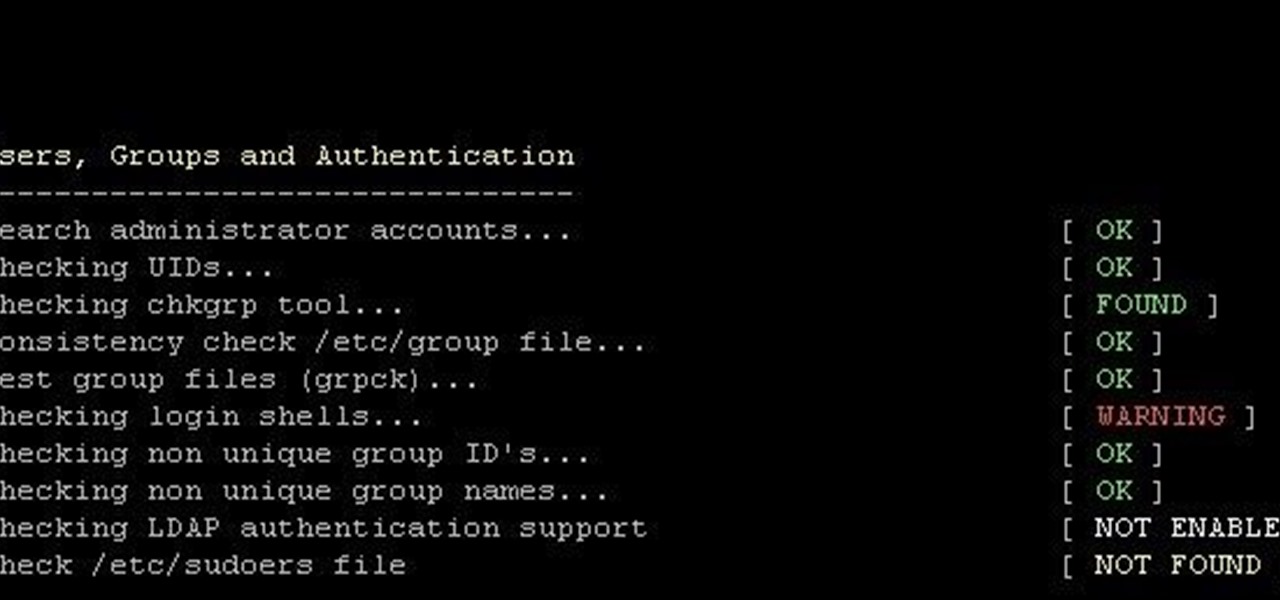
This is finding some of your vulnerability using Lynis. This tool Lynis is used on Unix and Linux type operating systems (sorry windows). So lets get started

So you just bought a fancy new Nexus 6 complete with its gorgeous and gigantic display—now what? Unlike Samsung's TouchWiz, stock Android doesn't sport any cool split-screen features, so how do you really take advantage of all that screen real estate?

Yosemite brought a new, Alfred-like Spotlight search to our Macs, but at times I still find myself wanting more out of it. However, after stumbling upon Flashlight by developer Nate Parrot, I am now able to perform Google searches, look up weather, and even enter Terminal commands straight from Spotlight's search bar.

iOS 8's third-party keyboard functionality is one of the best new additions to Apple's mobile operating system, allowing us to use swipe gestures, custom backgrounds, minimal designs, and many other features that the stock keyboard lacks.

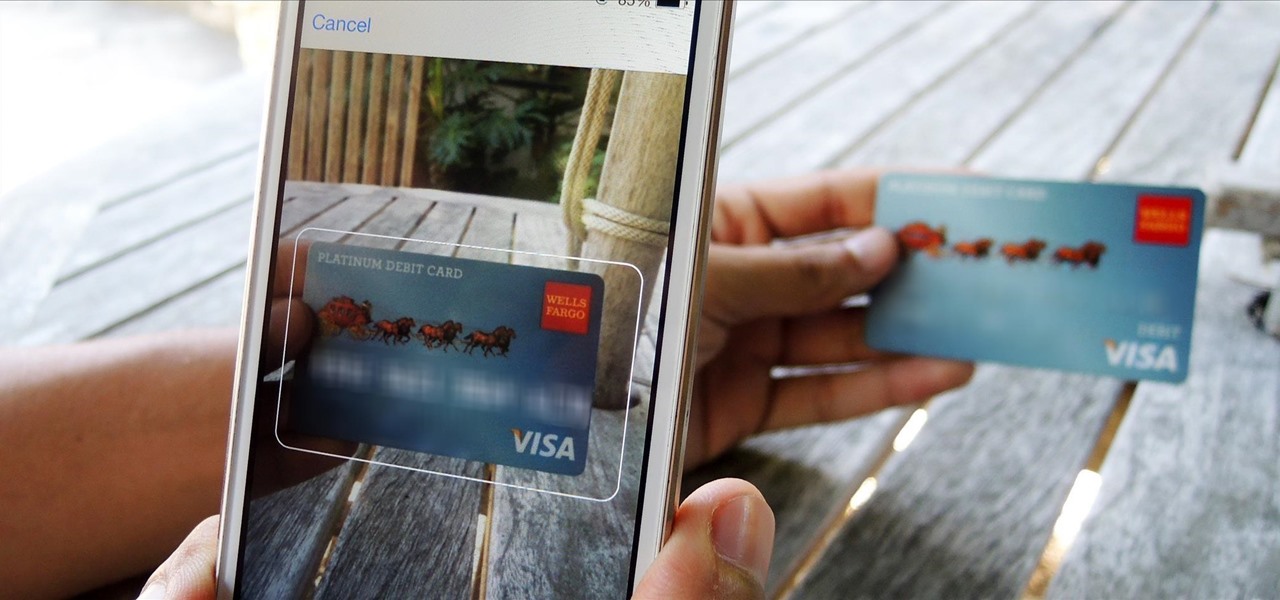
There's a feature that debuted in iOS 7 that lets you to save your credit or debit card information in Safari so that you can auto-fill text boxes when purchasing something online. Unfortunately, you still had to manually fill in your card info the first time, and if you wanted to disable the feature for security concerns, it was entirely useless.

Personality is something we're constantly attempting to inject into our lives, whether it be the car we drive or clothing we wear—and our mobile devices are no exception.

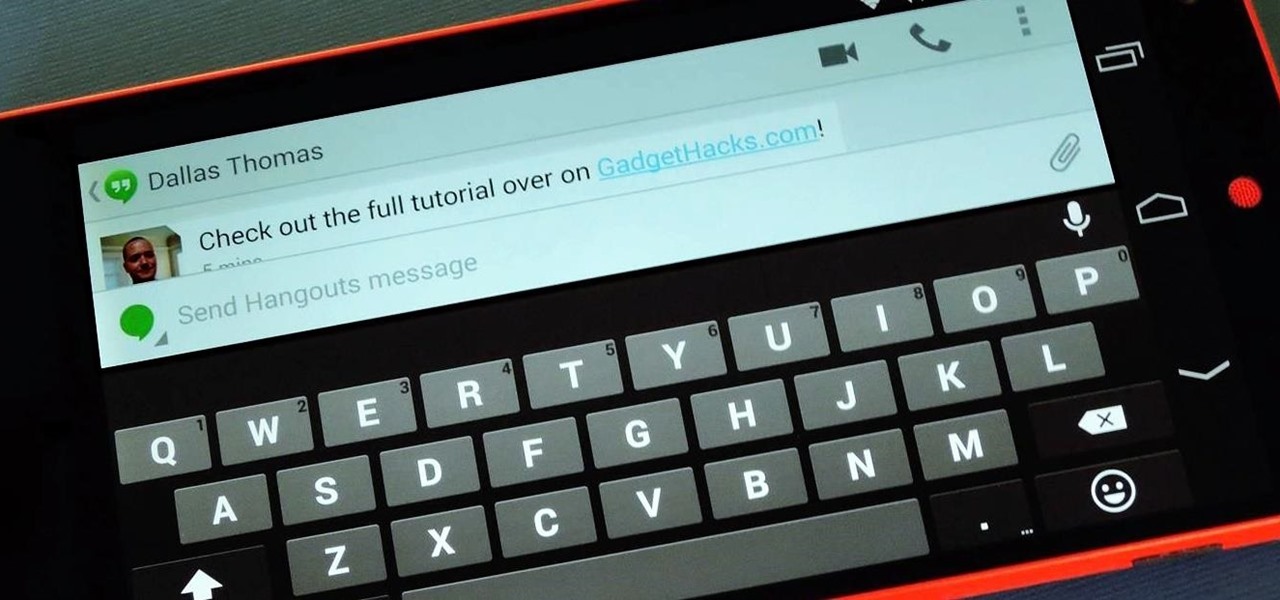
For some reason, when you're typing in landscape mode, Android extends the text input field to cover every bit of the screen that the keyboard's not occupying. This gets pretty annoying sometimes, especially with messaging apps where you might need to reference what the other person just said in order to properly form your response.

Google Now is a quick and intuitive way to tailor your device to work for you and, unlike other personal assistants, provide you with up-to-date information based on search habits, emails, and the general all-knowingness of Google.

Thanks to a recent back-end update to Google's Search app, every KitKat-running device can use "Okay, Google" from within any app—even the lock screen. However, the default settings for the OnePlus One's mic leave it unable to detect your voice unless you have it right up to your face. That isn't a good look for anyone, but thankfully there is an easy fix to get this working correctly.

In an attempt to keep things simple, Snapchat has a limited amount of editing features, made up of "smart" photo filters, drawing pens, and special text captions. If you want more editing capabilities, you'll be pleased to know there's a way, no thanks to Snapchat, but you will need to be rooted.

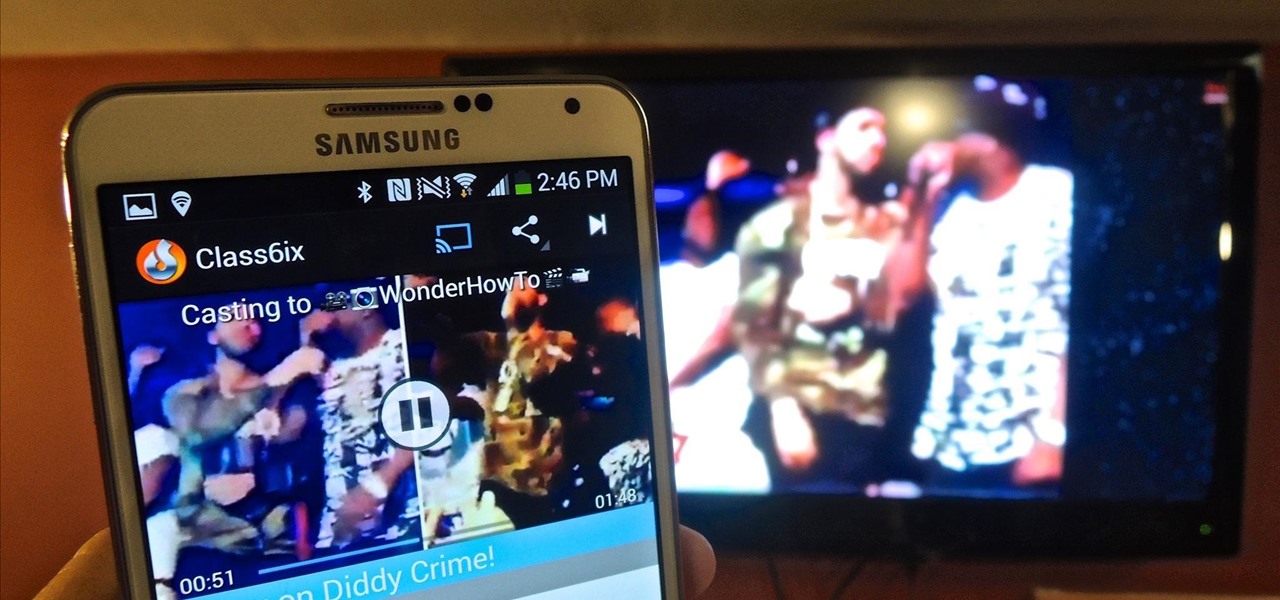
With Chromecast-capable applications slowly seeping into the market, it's difficult to find useful ones that we might use on a daily basis.

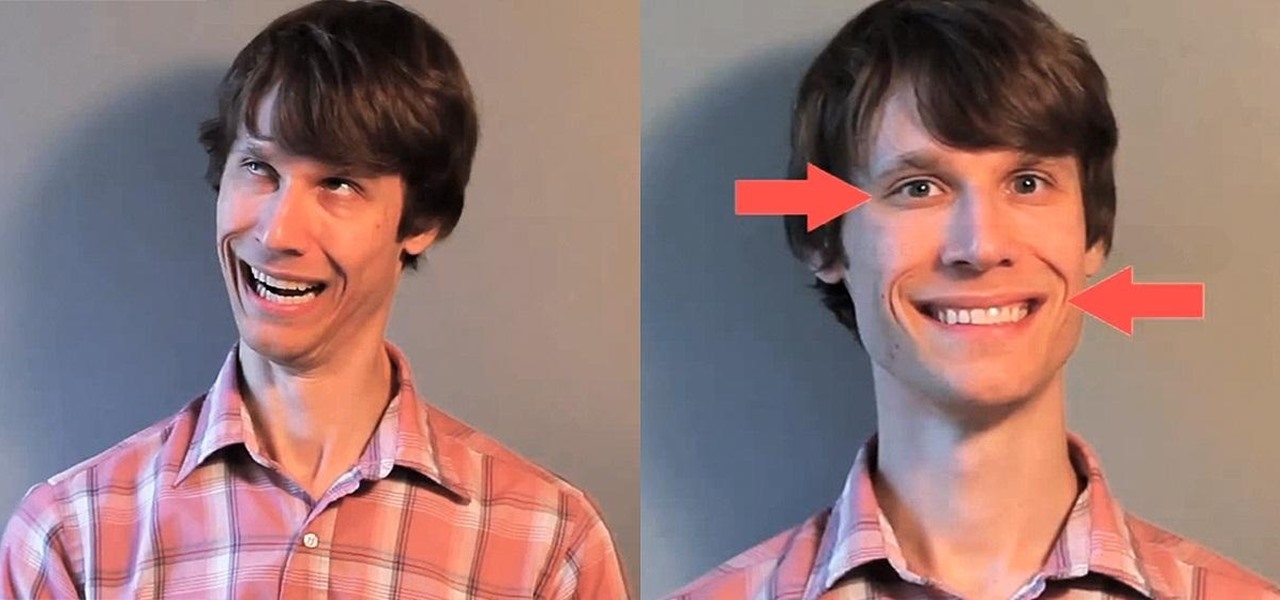
I hate having my picture taken. It's awkward, and I almost always end up thinking, "Is that what I look like all the time?" Most of us think we look awful in photos, probably because we all subconsciously act and carry ourselves a little differently when we know there's a camera on us.

The cell phone has come a long way. The very first "mobile devices" were made and used by the military in the late 1930s, with the first commercial mobile telephone service introduced by Bell in 1946. These devices were hardly what we'd call mobile today—some took up the whole trunk of a car, and others had to be carried on your back in a heavy bag.

Being able to run mobile apps on a computer is nothing new. Maybe you don't have a mobile device, or maybe you just like seeing the apps on a larger screen. Whatever the reason, with programs like Bluestacks, you can use your laptop to Instagram, play Angry Birds, and run countless other apps made for smartphones.

There are plenty of times when it would be nice to be able to give other drivers a piece of your mind, or let them know you're having car trouble so they go around instead of riding your bumper.

Last month, Google changed the placement of search options from the left side of the page to the top, right above the first result. In theory, this shouldn't be such a bad thing—it's just looks, right? Well, not quite. Turns out, it actually got rid of a few of the options as well, and a lot of people were not too happy about it. The problem is that the change gives you less functionality, and makes the options that are still there harder to get to. One of the most frustrating changes was how...

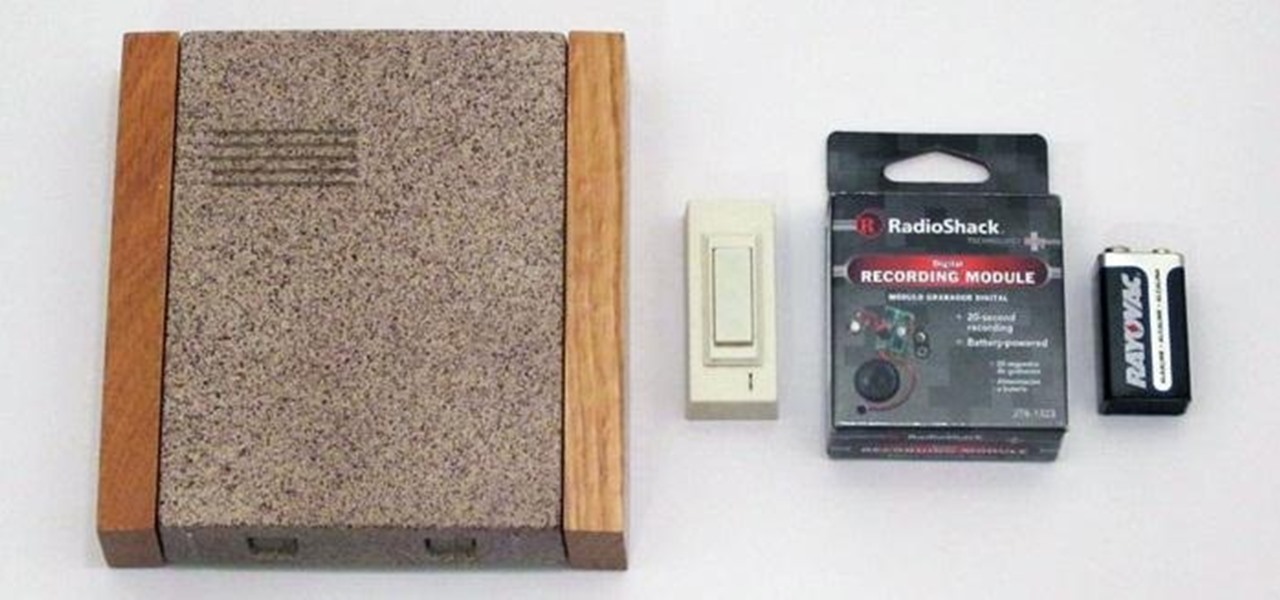
Doorbells are useful and all, but most of them are boring as hell. They use the same old generic sounds to let you know when guests have arrived, as demonstrated below.

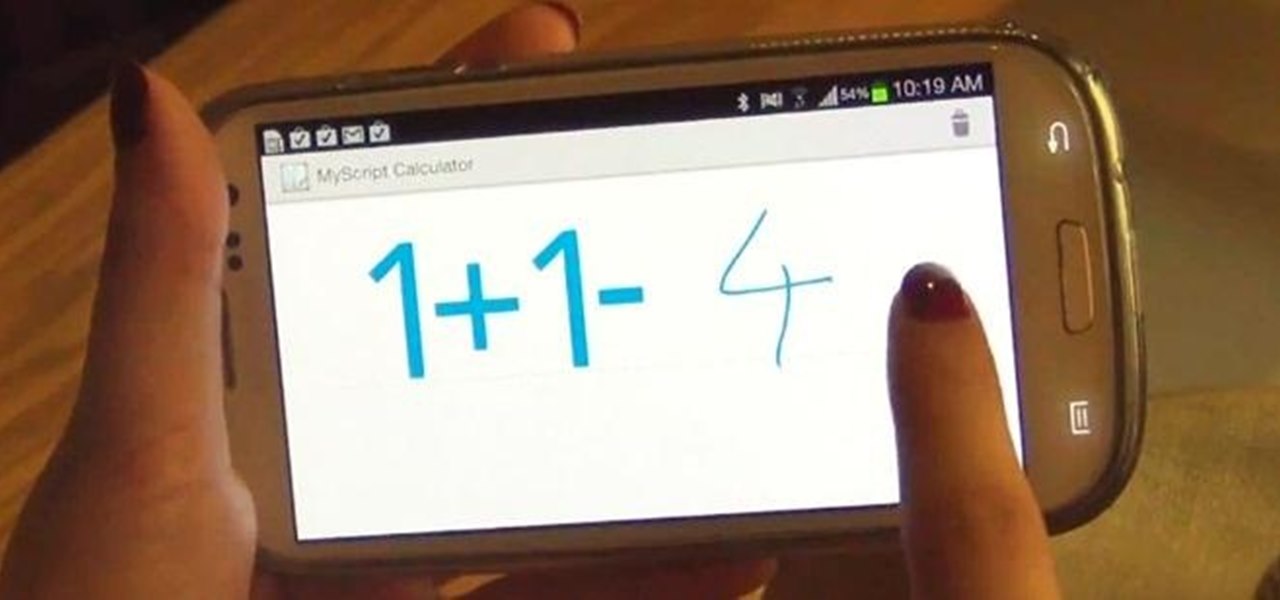
Solving long and extensively complicated equations in grade school was tough to do by hand. Keeping track of which part of the equation to solve first took time, training, and lots of bad grades.

Playing advanced games on your phone can be pretty frustrating sometimes. Touchscreen devices are great for everyday apps and games designed solely for them, but when it comes to games that require multiple actions in conjunction with directional movement, it gets ugly.

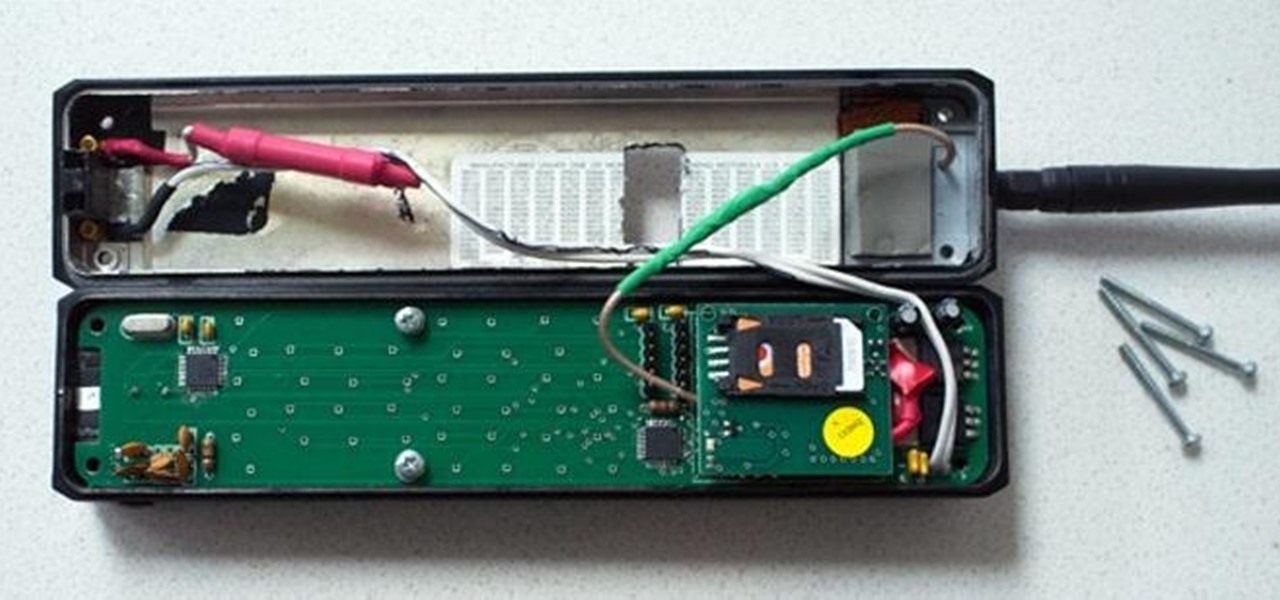
Before my time, people used to listen to music recorded on these things... I didn't really know what this thing was until my parents clarified and told me that they were called cassette tapes. These "cassette tapes" were utilized to store sound recordings on either side of the tape, which could usually hold between 30 to 45 minutes. I laughed at that information as I took out my iPhone 5 (roughly the same size), which can store roughly 40,000 minutes worth of music.

If you're at all like me, you constantly get frustrated that repeaters only boost redstone signals in one direction. It's annoying!

Cropping images can be a huge pain if you have a bunch to do at once. Even if you have Photoshop or a similar program, the process of opening each individual photo and cropping them one at a time can take forever. A free web-app called Cropp.me makes that task a lot easier by auto-cropping your photos to whatever size you choose. All you have to do is upload an image, choose what size you want it to be, and click Cropp My Images. You can choose from a list of sizes or input a custom size of y...

Having already solved for functionality and form factor, Nreal appears poised to pull ahead of its consumer smartglasses competition as the third piece of the puzzle now falls into place.

If you have a five BNC input on your plasma or LCD tv, here is how you can make a cable to the length you need.

Learn the difference between Speakon, Jack, and XLR inputs. Also learn how to wire all of these connectors to hook up your speaker system on your PA or DJ system.

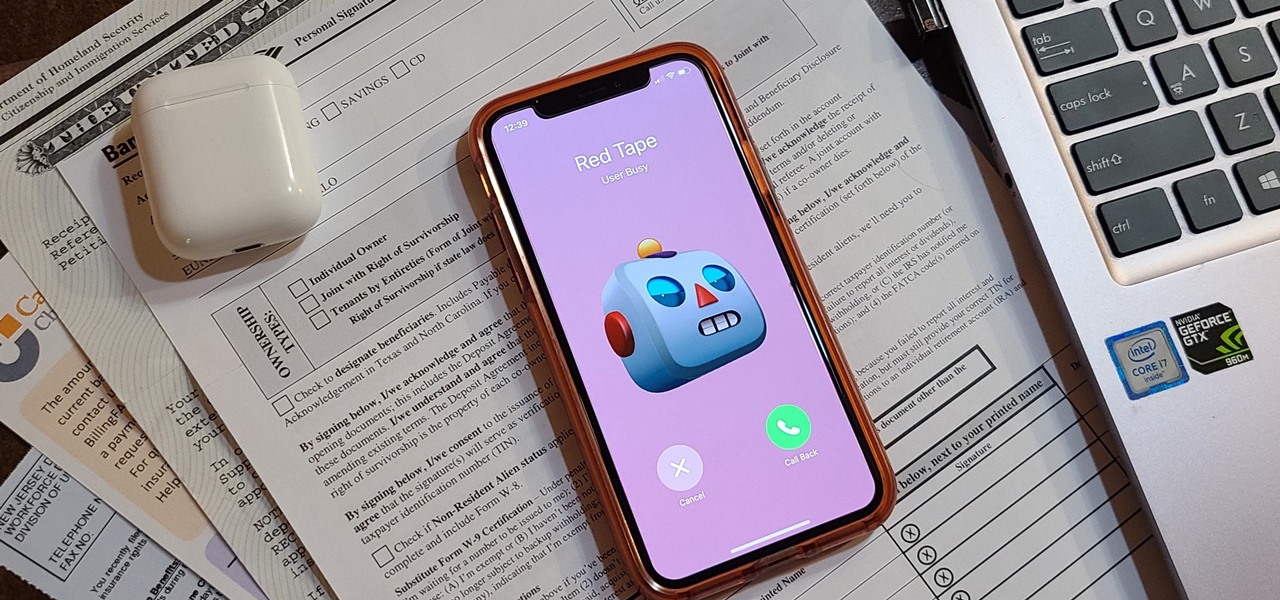
Even under normal circumstances, it's almost impossible to speak to a representative for a government agency or company in just one try. Many systems will put you on hold for long periods or ask to call you back when someone is available, but there are still some out there that just give you the busy signal over and over again. In those cases, there's a jailbreak tweak that can help.

Up until Android 5.0 Lollipop, the actual text of incoming notifications would scroll by in your status bar. These ticker style alerts didn't pop on screen or interfere with what you were currently working on, but you could still read the message. They were replaced by the new "heads up" alerts, but you can still bring them back.

The landscape of podcasting has exploded in recent years, with everyone from dedicated longtime podcasters reaching the mainstream spotlight, to traditional media personalities moving from TV, radio, and newspapers to grab a slice of the listening pie. The good news is that the barrier to entry is relatively low, so even if you're not a celebrity or media luminary, you can still get your voice out there by starting a podcast.

There's a new trend on Instagram Stories: People are making viral AR filters where images of popular characters from TV shows, movies, and other mediums shuffle above your head until one sticks. The filters range from Disney and Pokémon characters to Harry Potter and Friends, but you're not limited to just that because you can create your own "which are you?" filter.

When Apple acquired the popular Workflow app in 2017, many were worried that it would either get replaced with something much worse, or just disappear entirely. Thankfully, Apple put these concerns to rest with the launch of Shortcuts. In iOS 13, Shortcuts is becoming more powerful than ever, providing functionality on the iPhone that the original Workflow team could only dream of.

We know that Microsoft's HoloLens 2 is due to start shipping later this year, but despite the trickle of news about the device, we still don't know when.

Introduced to Apple Podcasts back in iOS 11.2, whenever one episode of a show ends on your iPhone the next one begins right away for an uninterrupted experience. While the continuous playback feature for each show or station is incredibly useful for lengthy commutes, long drives, or to catch up on what you've missed, it may not be ideal for other situations.

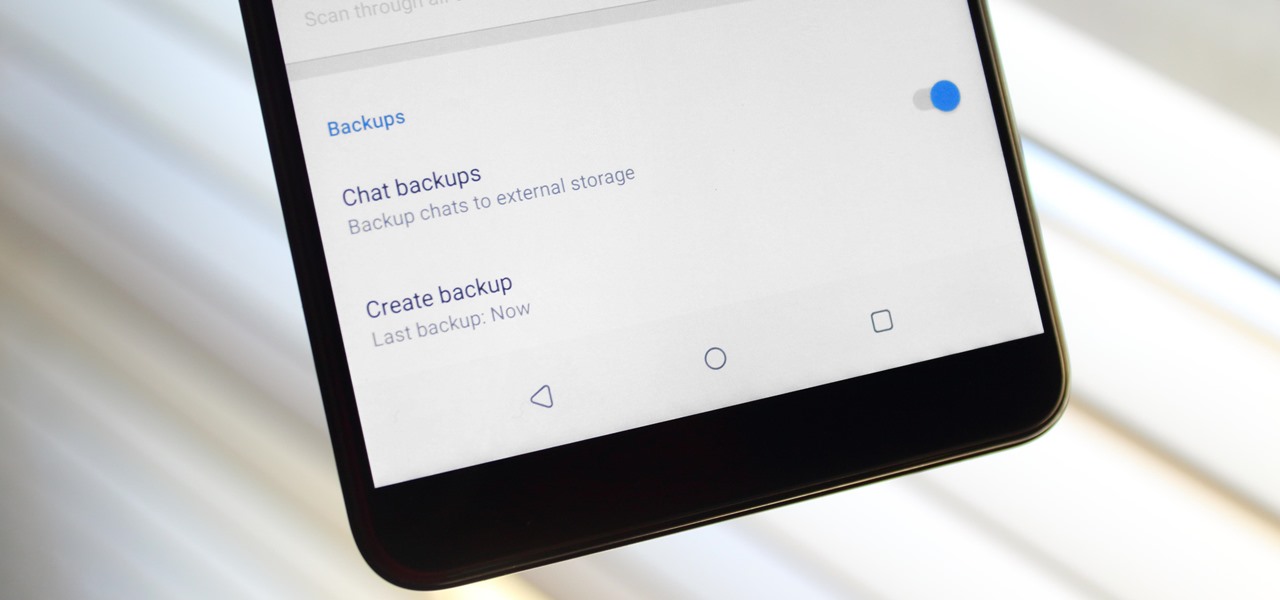
Switching phones has never been easier. Google backs up most of your app data on the cloud, which can then be restored onto your new phone. Sadly, Signal doesn't use this feature since it could compromise your security. Instead, Signal stores encrypted backups locally, requiring a bit of work to restore these messages.

One of the ultimate goals in hacking is the ability to obtain shells in order to run system commands and own a target or network. SQL injection is typically only associated with databases and their data, but it can actually be used as a vector to gain a command shell. As a lesson, we'll be exploiting a simple SQL injection flaw to execute commands and ultimately get a reverse shell on the server.

Cross-site scripting can be one of the easiest vulnerabilities to discover, but to be successful with this type of attack, it is essential to learn how to get past filters. In the previous guide, we explored some ways to do this, such as abusing attributes and event handlers and tricking the application into accepting unusual characters. Now, let's take a look at more techniques used to defeat filters.

Cross-site scripting is one of the most common vulnerabilities found on the web today, with repercussions of this type of flaw ranging from harmless defacement to sensitive data exposure. Probing for XSS can be tedious and time-consuming for an attacker, but luckily there are tools available to make things a little easier, including Burp Suite, Wfuzz, and XSStrike.

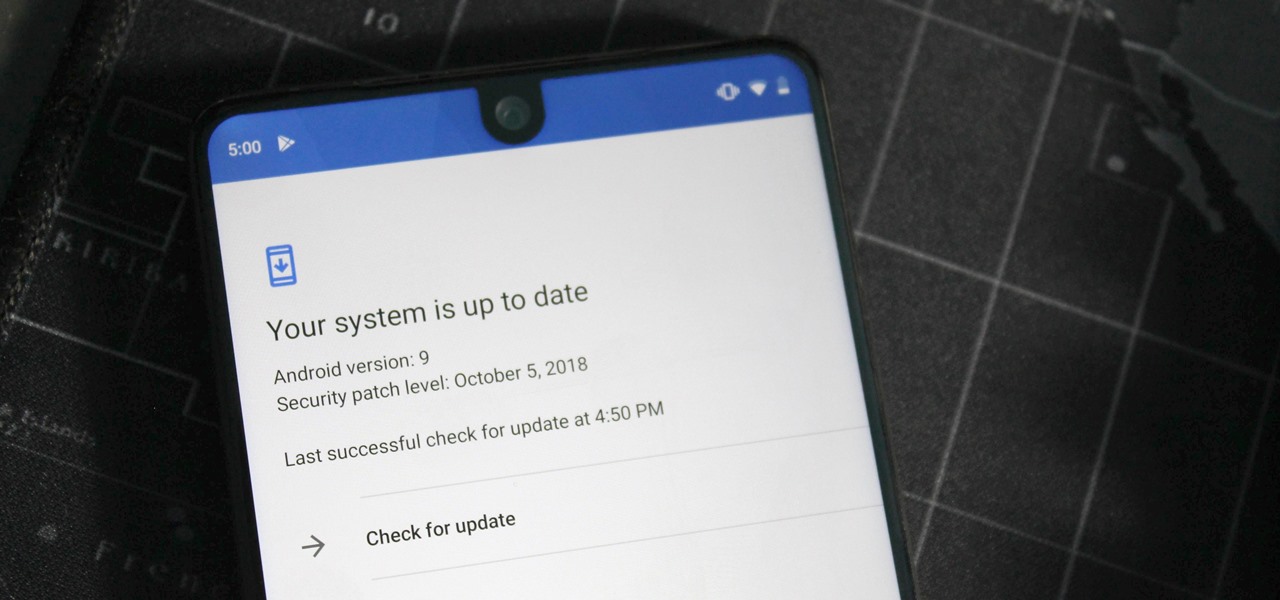
One of the issues with rooting your device is the inability to update your phone via OTA. Any security patches or software updates pushed out by the OEM are lost because your bootloader is unlocked. However, you still can update your device, it just a take a bit more effort.

After gaining access to a root account, the next order of business is using that power to do something more significant. If the user passwords on the system can be obtained and cracked, an attacker can use them to pivot to other machines if the login is the same across systems. There are two tried-and-true password cracking tools that can accomplish this: John the Ripper and Hashcat.