Have you ever wondered why your cat does wacky things like head butt you? Do you wish you and your cat could speak the same language? With input from an expert animal behaviorists, you can! In this video, Sara gives you the low down on why your cat is so aggressive, why he won't stop scratching your furniture, and how to interpret your cat's meows. Now you can finally understand what exactly is your cat is trying to tell you. Here you'll find a brief introduction to some common behaviors you ...

If your clock will not respond to input, or does not regulate temperature, you will probably have to replace your oven electronic control board. You can follow the steps in this video to help you do this easy repair.

This easy to follow silent and accurate video will guide you quickly and easily through what you'll need, (like a Power Supply, a sound system that has a Subwoofer Pre-output and a High Input adapter, which may already come with your amp.) First learn what colored wires should be connected to simulate your PC starting. Then connect the amp to the power supply to simulate the car Head-Unit starting. Once the power issues are handled, the video assists you with connecting your audio input. It i...
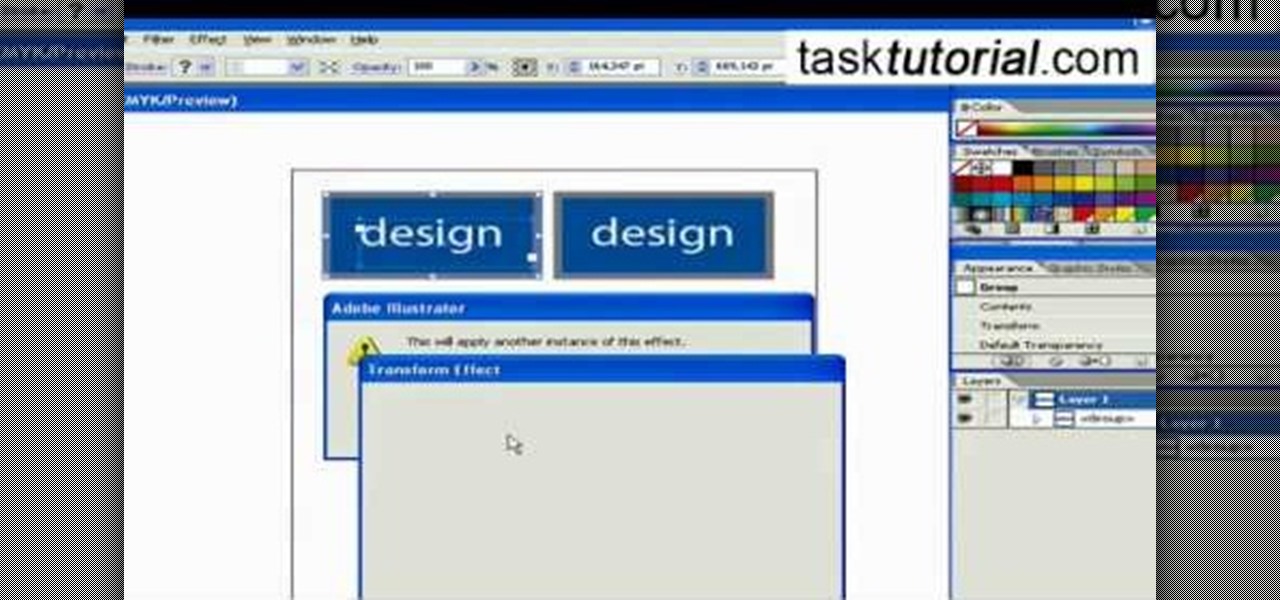
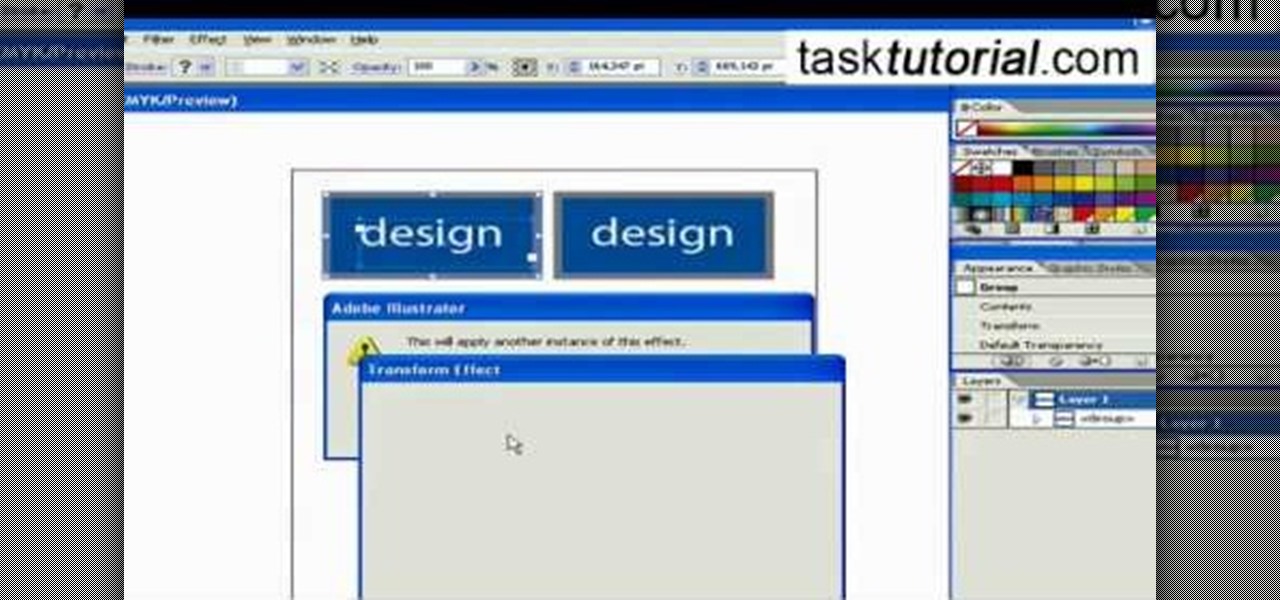
This video takes us through the procedure of creating a transform effect in Illustrator. First, choose a rectangular box and fill color in it. Input some text inside the box. The font and the color of the text can also be changed. Then position the text properly. Make a group of the shape and text. Now go to effect and choose transform. Transform is a very powerful effect which lets us create duplicates. Now select the number of copies, for example, one copy. Select preview. Now set the point...

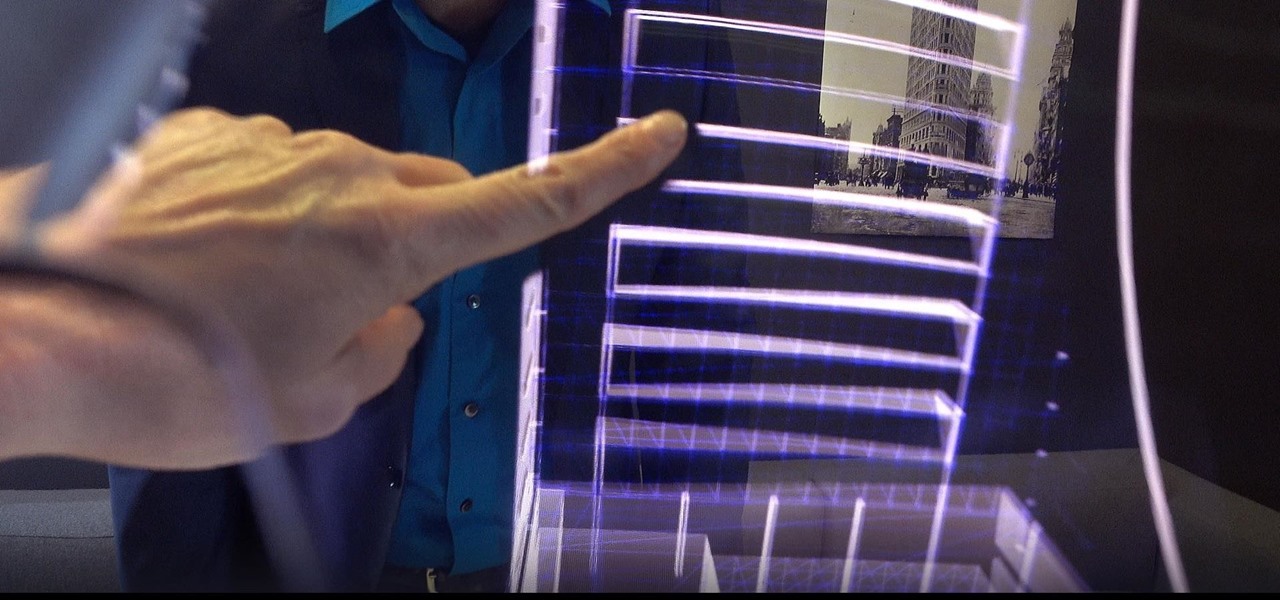
Every step in the evolution of computing brings an in-kind leap forward in user input technology. The personal computer had the mouse, touchscreens made smartphones mainstream consumer devices, and AR headsets like the HoloLens and the Magic Leap One have leveraged gesture recognition.

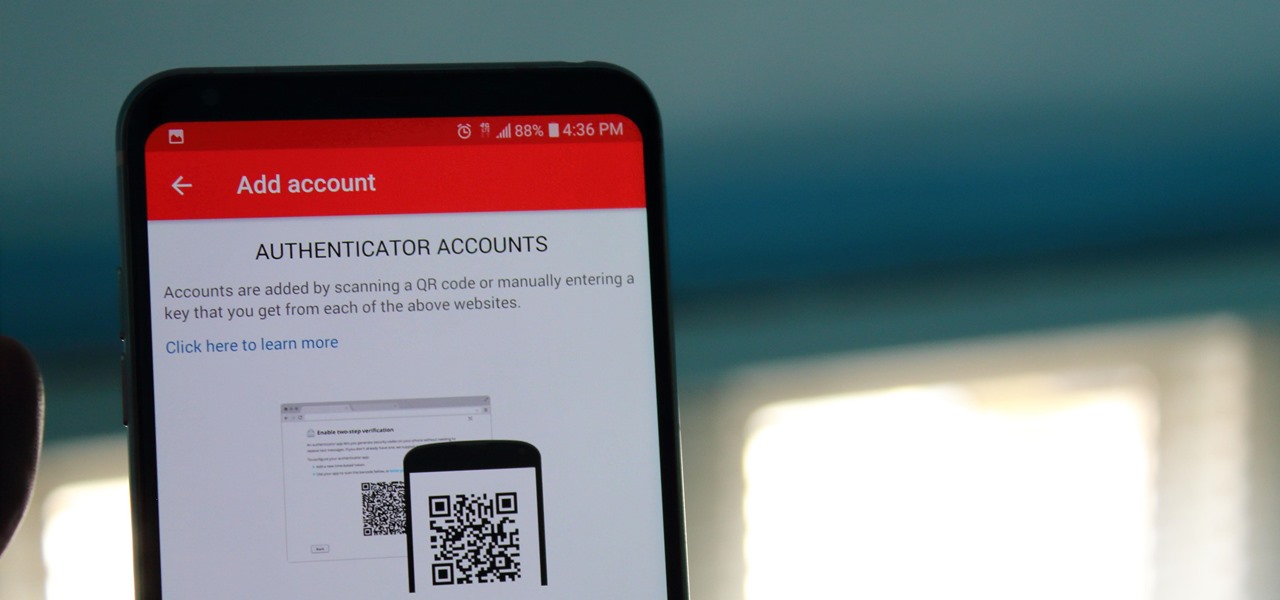
One of the main reasons Authy was able to top our list of the best two-factor authentications apps was its ability to transfer access to a new device. This feature ensures that whenever you get a new phone, you don't lose all your tokens. However, if the process is done incorrectly, you can leave your account vulnerable.

If you didn't get the memo, passwords aren't enough protection for your online accounts. Even a long and complex password offers only one line of defense which can falter. Two-factor authentication adds an additional layer, bolsters your defense, and decreases the risk of your account becoming compromised.

welcome back my masters , teachers and classmates , in this second part of this 0-day series we will learn the basic of fuzzing, and i bought some gift for nullbyte(a 0 day vuln that will be released today exclusively on null-byte) .

One thing I absolutely cannot stand is lag when I'm gaming. Every time I'm about to beat my killstreak record on Call of Duty, my internet connection drops and I'm a goner. It never fails. This usually happens because someone else on my Wi-Fi is streaming a movie or downloading a huge file.

Welcome back, my budding hackers! In previous tutorials, we've looked at some of the basic commands and concepts for using Linux. Along the way, I realized that I've failed to provide you with some basic background material on the stdin, stdout, and stderror.

Steam is an online platform that lets you download and play over 2,000 video games, from first-person shooters to RPGs, as well as a pretty long list of indie games. You can play on your PC, Mac, mobile device, or even your television, and it has a community of over 40 million gamers. Prices are different depending on the type of game and how new/popular it is, but they're generally about the same as what you'd pay for an Xbox or PlayStation version. They also have a decent list of free games...

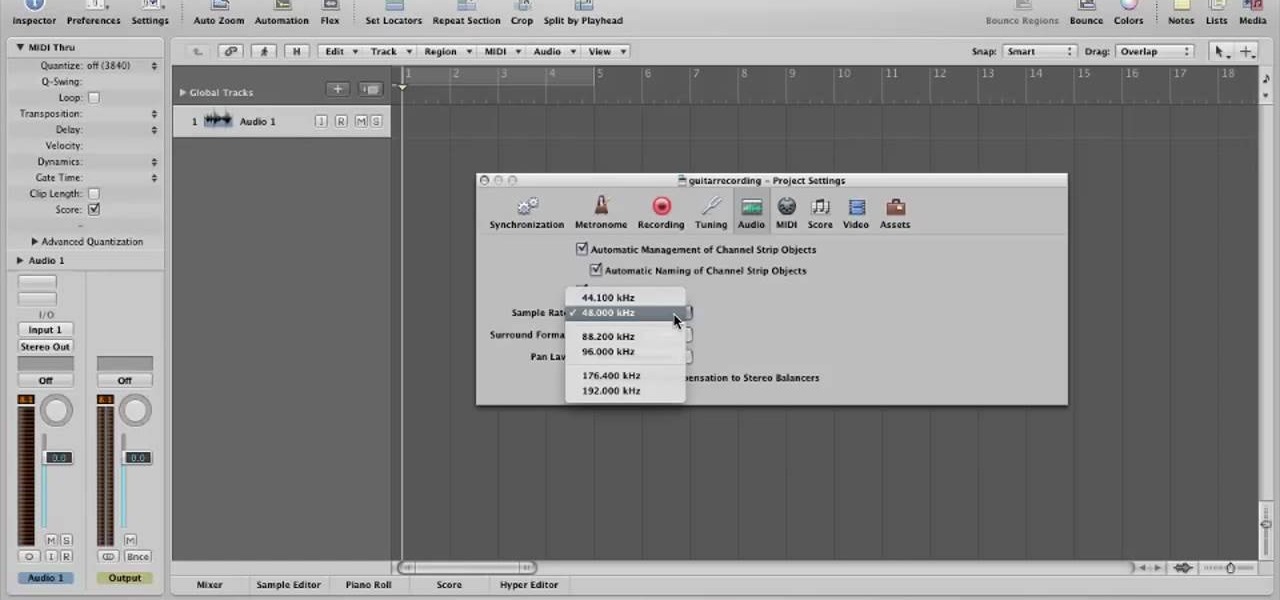
In this video, you will learn how to record using Apple Logic Pro 9. First, open the program and save the session. Make sure your audio interface is set before recording. Go to global settings and navigate to audio. Click on the general tab and change the audio settings. Wave files are the industry standard. Make sure 24-bit recording is checked. Software monitoring will allow you to monitor the audio. Save this and change the project settings. You can adjust the sample rate of your recording...

Two-factor authentication (2FA) is a great way to add another layer of security to sensitive third-party apps and websites like Venmo. However, before iOS 12, to log into a particular 2FA-secured app or site on your iPhone, you'd have to memorize or copy the SMS code from Messages, then jump back in a timely manner to log in. Apple's latest iOS version streamlines this process.

New York-based startup CTRL-Labs has closed a $28 million Series A round of funding from Google parent Alphabet's GV and Amazon's Alexa Fund, among others, for its next-generation neural interface technology for AR/VR and robotics.

When playing word association with Star Trek, the first thing to come to mind with regards to augmented reality is likely Holodeck, not The Game, an obscure episode from season five of Star Trek: The Next Generation.

When most people first become aware of Kodi (formerly known as XBMC), they hear about its ability to stream illegal content. But the real Kodi community knows that it's much more than just a haven for pirated material — it's an all-in-one media player that addresses the majority of home theater needs, particularly for those that decided to cut the cord.

While Meta Company has agreed to a settlement in its lawsuit against a former employee and his company, they find the tables have now turned on them in the form of patent infringement allegations from another entity.

North American users get a raw deal when it comes to Sony devices. For some reason, the critically-acclaimed Xperia lineup of smartphones is hardly ever available here, whereas in Europe, the Sony Xperia Z series is one of the most popular flagship devices around.

Welcome back, NB community, to my series on sorting. I introduced in my last article the concept of complexity. When I say complexity, I'm talking about time complexity.

In this tutorial I will be explaining the purpose of unique encryption/decryption scripts ( I will be referring to these at "UEDS" for this tutorial). Then, I will show you how to make one. Finally I will talk about the downsides to the method I use. I will also provide links explaining the concepts and algorithms used in encryption to anyone who wants to see what is going on under the hood.

Hello my fellow hackers, Welcome to my republished revision of the ruby programming language, Part 1.

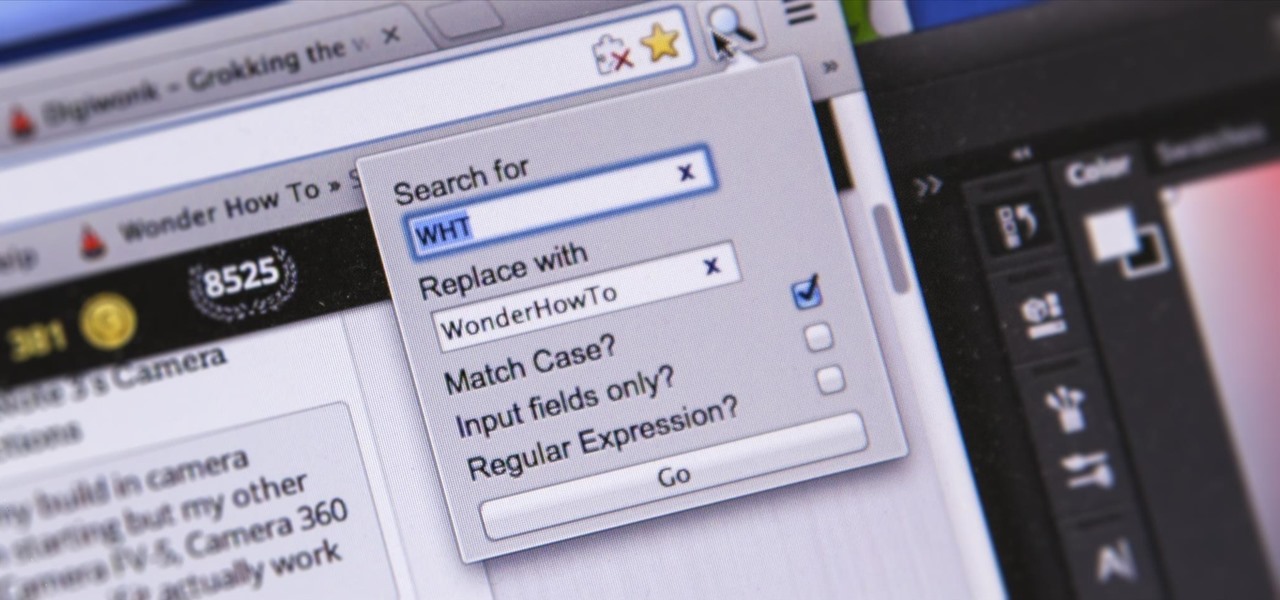
I'm sure you've been there—halfway through typing something out, you realize that one word you've been using more than any other has been misspelled. Perhaps it's a single word, acronym, or line of code that you find yourself typing quite often at work, but this one requires complicated hand gymnastics that you'd simply rather not perform over and over again.

I'm a long-time and loyal Android user, but one iOS feature that I'm truly envious of is their keyboard shortcuts, which lets you assign a short macro that inputs a longer phrase. For example, typing "home" can input your home address.

This video will show you how to block flash auto play in a web page. These videos not only consume bandwidth but, also irritates. Here first showing this for Google Chrome Browser. Through this tutorial you could get rid of that. Watch the video.

This video will show you how to stop flash auto play in Chrome and Firefox Browser. Flash auto play consumes unnecessary bandwidth and slow down speed also. Now with the help of this video you could stop this auto Play feature in Chrome and Firefox browser.

Back in college, there were many instances where I'd have to meet up with a partner that I was randomly paired with in order to work on a project or to study for an exam. Besides the awkward interactions, the most difficult part was always figuring out where we would meet off-campus. I live here and they live there, so what's reasonably halfway?

While it may not serve much of a purpose here in sunny Los Angeles, it's still a good idea to keep constant tabs on the weather forecast, because you don't want anything to rain on your parade.

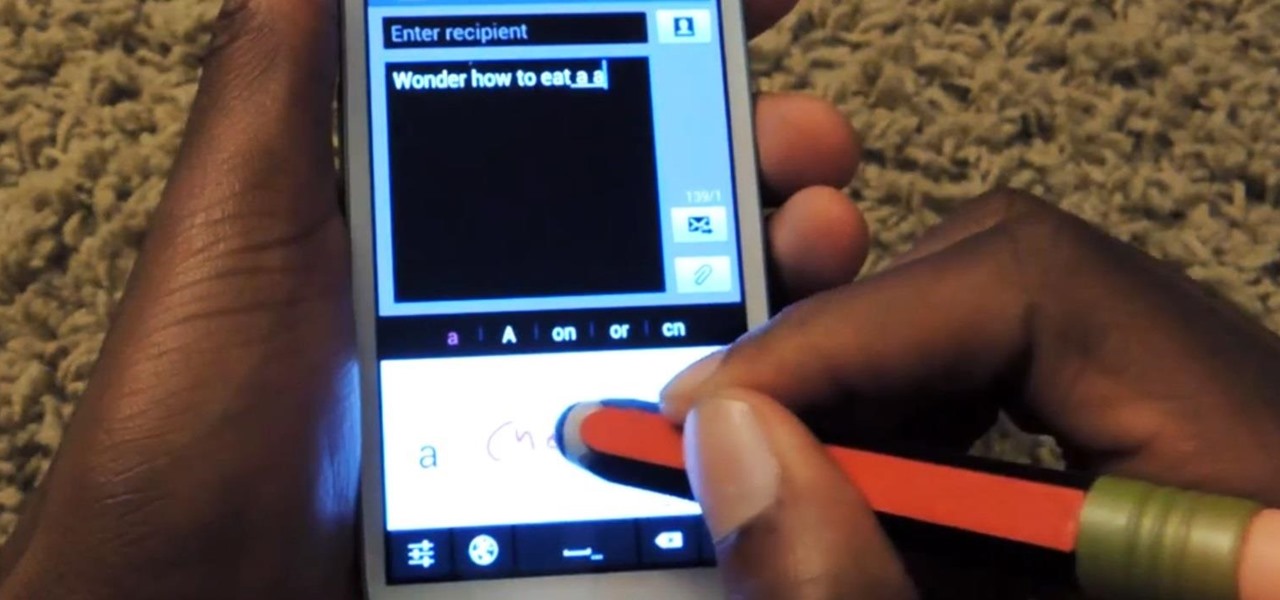
I can't say that my handwriting skills are the best, and my cursive is even worse. I mean, I still don't know how to write a capital L in cursive, but who really cares when I do all my everyday writing with a keyboard now. I've gotten pretty fast at typing on my computer, but those tiny buttons on the Samsung Galaxy S3's keyboard is a totally different thing.

There was a dynamic mic in my junk box, but without any stand or connection cable. I needed a high-quality microphone to narrate my project videos, so I had to think of a way to build a stand for the mic. This is what I came up with.

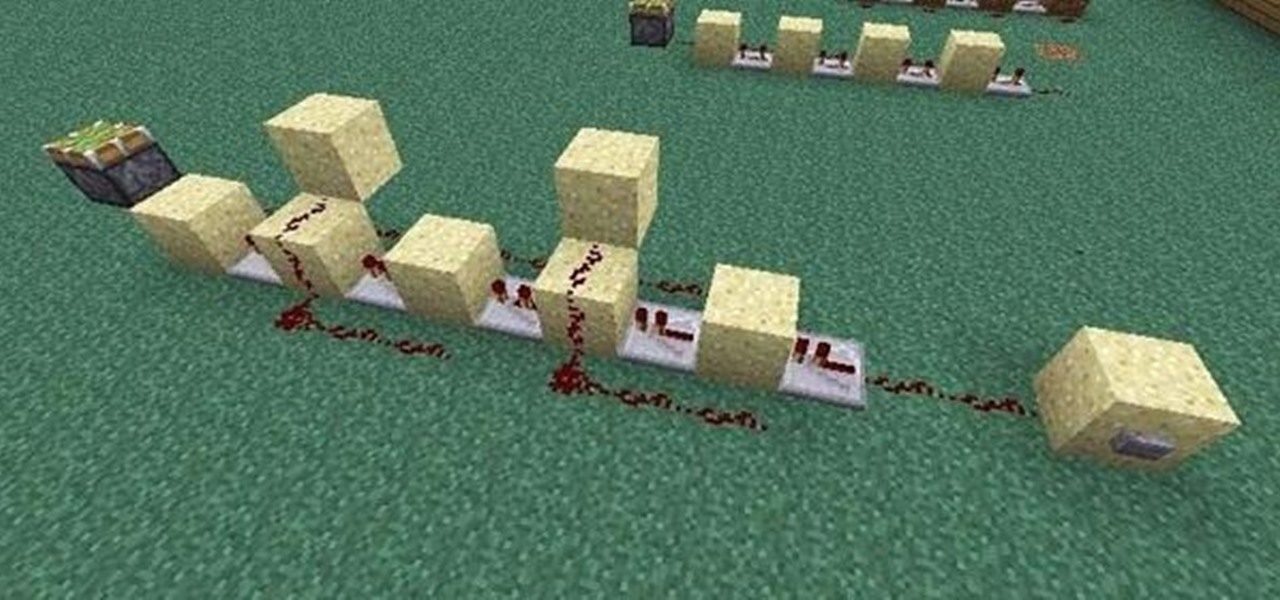
If you're like me, the words 'monostable circuit' mean nothing to you. Until just recently, I had no idea what a monostable circuit did, or why anyone would ever need to use one.

QR codes allow you to quickly and easily store and retrieve data within a single image. Much like barcodes at grocery stores, QR codes are images that can be scanned to discover data, such as an online website URL. Additionally, they can also be created by inputting text data into a QR code generator. Try scanning some of the QR codes in this video with an app on your phone or tablet to see how they work!

To test how fast your internet speed is an intermediate level skill. Start by picking an internet speed test. You can use Google or another search engine to find one. A service that is recommended in the video is DSLreports. This site does not require you to know a lot of information about your service. To test your speed start by picking a city that is near to you. Then shut down all tabs and every application that you have running. It's important to do this on every computer on your home ne...

In order to prevent accidental CAP LOCKS, you can use a number of new, innovative and free software solutions. With your Windows 7, there are functions available to assist you.

The key to a great essay or dissertation is a strong thesis. In this two part tutorial from teacher Jennifer Mensink, learn exactly what a thesis is, why it is important and how to craft the perfect one. This video lesson will cover everything including an anticipation set, input and an assessment. Jennifer teaches as though you are her only student, and you will love listening to her step by step breakdown. So, get ready for finals with this refresher course on thesis statements.

Want to program your own Java games and applications but don't know beans about object-oriented programming? Never you fear. This free video tutorial from TheNewBoston will have you coding your own Java apps in no time flat. Specifically, this lesson discusses how to receive and work with keyboard input data from a user when writing code in the Java programming language. For more information, including detailed, step-by-step instructions, watch this helpful programmer's guide.

In this video tutorial, viewers learn how to import, manage and export 16:9 footage in Adobe Final Cut Pro. Begin by opening the Log and Capture.Then configure the Logging, Clip Settings and Control Settings. For the Control Settings, set the Device Control as Fire Wire NTSC and the Capture/Input as DV NTSC 48 kHz Anamorphic. Then scroll through the sequence setting of the footage and check Anamorphic. To export, click on File and select Export. Click in Options set the the size to Compressor...

Street Fighter IV : Blanka, the Brazilian Beast unleashes havoc upon the World Warriors once again. Street Fighter IV is a 2008 fighting game produced by Capcom. Street Fighter IV is currently released for PlayStation 3 and Xbox 360, with a Microsoft Windows version in the works as well.

Street Fighter IV : Vega, the beautiful Spaniard delivers gruesome damage. Street Fighter IV is a 2008 fighting game produced by Capcom. Street Fighter IV is currently released for PlayStation 3 and Xbox 360, with a Microsoft Windows version in the works as well.

In this episode of Full Disclosure we are explaining the website attack known as Cross-Site Scripting (XSS). Cross-Site Scripting is a type of security vulnerability that affects web applications that do not sanitize user input properly. This kind of vulnerability allows an "attacker" to inject HTML or client side script like JavaScript into the website. Cross-Site Scripting is most commonly used to steal cookies. Cookies are used for authenticating, tracking, and maintaining specific informa...

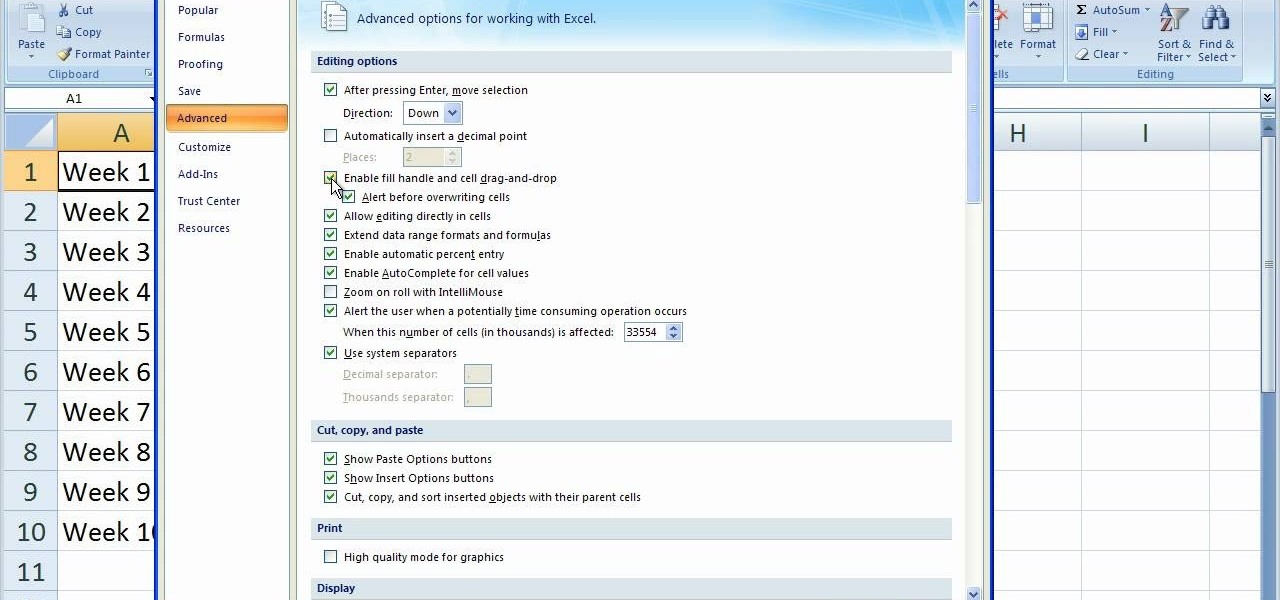
In this video tutorial, viewers learn how to disable the quick fill handle and drag and drop option in Microsoft Excel. This task is very easy, simple and fast to do. Begin by clicking on the Office button and click on Excel Options at the bottom. Then click on the Advanced tab and deselect "Enable fill handle and cell drag and drop" option under Editing Options. Finish by clicking on OK. This video will benefit those viewers who use Microsoft Excel for their work, and would like to learn how...