
Minecraft Spa Getaway: Join Us This Saturday to Help Make a Fully Functional Bathroom!
Welcome to Minecraft World! Check out our tutorials, post to the community corkboard, and come play on our free server!


Welcome to Minecraft World! Check out our tutorials, post to the community corkboard, and come play on our free server!
Have you ever built a fancy redstone contraption just to find out that it needs those large clunky levers in order to work? Well, have no fear because there is a more complex method for fixing that problem. It is known as a T Flip-Flop and it can be the love of your life. Now, the version I'm showing you is compact and doesn't use pistons, which lag the server to no ends. Here we go.

With a lot of Null Byters playing around with Linux because of its excessive use in the hacking world, some of you are bound to run into some trouble with the installation at some point or another. If you make a mistake, or you're intimidated by the wonky-looking installation screen, you may want to just stick with Windows. However, you may notice it can be hard to go back once you've crossed a certain point in the installation. Your Windows installation may be broken or unbootable.

Welcome to Minecraft World! Check out our advanced tutorials and come play on our free server.

Battlefield 3 officially comes out tomorrow but people have figured out a way to play it today if you have it downloaded (digital pre-install). All you have to do is fake an ip to make it look like your timezone is ready to play. I'll try this when I get home, in the meantime:

Smartphones have already hit the shelves with glasses-free 3D displays, but now you can enjoy the luxury of a 3D display on your 2D devices, thanks to Japanese company Global Wave. They've developed a special film that allows you to enjoy three-dimensional content on existing two-dimensional products, from laptops to computer monitors, along with iPads and iPhones.

Age doesn't matter in the world of programming, only skills, and recent high school grad Jack Eisenmann definitely has them. He recently built a homebrew 8-bit computer from scratch, calling it the DUO Adept. A worn television makes up the monitor and speaker system, an old keyboard acts as the input controller and the actual computer itself is housed inside a clear Rubbermaid container, consisting of 100 TTL chips and a ton of wire.

As a kid, my favorite thing to do at the Natural History museum was a midday stop, when my family strolled past an antiquated looking vending machine in the museum's musty basement. The Mold-A-Rama machine was oddly shaped, George Jetson-esque, and spewed out made-to-order, brightly colored plastic dinosaurs. There was such joy in watching the liquid wax pour into the mold, and then eject a warm, custom toy—well worth the dollar or two demanded. A version of this tradition was recently elevat...
I'm having a hard time finding my older posts, so I'm sure you are too. I'll put them all here so you can find them easily. You can bookmark this if you want :)

That's a real Strat for the Rock Band game. Rock Band 3 will feature the option of playing on the six button toy guitar like before, or go Pro by using a real Start modified to give input to the game. You can plug this guitar to an actual amp and play away! Each song comes with a tutorial trainer and the career mode will teach you how to play from novice to expert.

Facebook's mobile app lacks many features from the desktop site. Even if you open Facebook in your phone's browser and request the desktop version, all that does is basically resize the mobile app. But there's a simple workaround that will force Facebook to appear in all its desktop glory on your mobile browser of choice.

Gone are the days of needing a specialized app or program to unzip files. In fact, you don't even need a computer. It's 2019 — cars drive themselves, robots take fast food orders, and you can unzip compressed files right on your iPhone.

Press renders for HTC's latest phone leaked out this morning, and it turns out that it likely won't be called the One M10 as many had expected. Instead, the company seems to be trying to clean up its naming conventions, and the next phone will simply be called HTC 10.

Hi all, in this tutorial, I'm going to show you how to block and delete unwanted adds (even those in apps, videos or music stream) without having to install an application or jailbreaking your iOS device.

In this how to, I'm going to explain how to install a new TV socket. Parts
EPUB ebooks are very popular, but are not supported by Amazon's Kindle. This How-to will show how to convert EPUB ebooks to MOBI format, which can be read by Kindle.

Most new stereos come with an auxiliary port built in, but if you drive an older car, you're usually stuck with the radio or CD player, and we all know both of those options suck.

Have an older car with nowhere to plug in your iPod? Rather than paying to have one installed, you can mount your iPod nano on your car's dash like Redditor hyeinkali did in his 2001 Honda Accord. Normally, there's just a boring digital clock between the air vents, but it's perfectly suited for a nano-mod. This is a great hack if you plan on getting one of the new nanos or iPod touches, because it gives you a chance to get some more use out of your old nano and its old school 30-pin connector...
I will illustrate a simple, yet effective way to stop tracking and third-party cookies without installing any additional software on your computer. Third-party cookies are often used to track your visits and activities on webpages and can slow down your browser and hinder your privacy. They are often the most common detected adware or spyware installed on most computers.
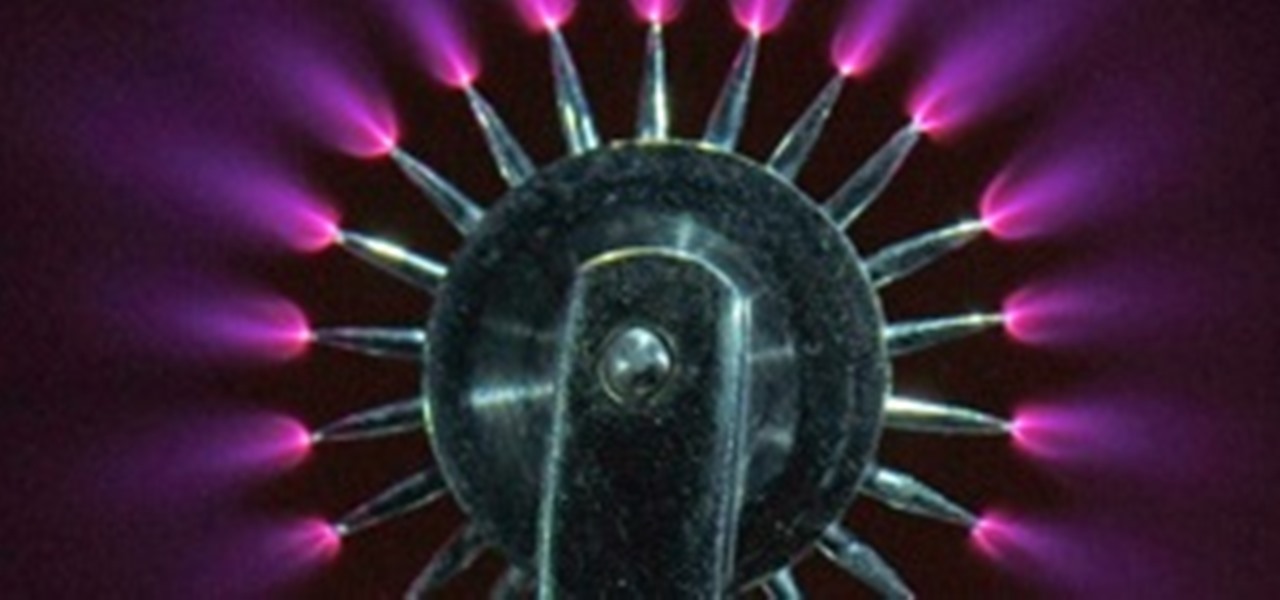
In this article, I'll show you how to build a simplistic circuit to generate negative ions. Negative ions have been known to contribute to fresher air, happier mood, and general health benefits. However, they also look amazing in the dark (check out the photos below, purple plasma is amazing!). And if all else fails, they make a cool nightlight. If you've ever been around a Tesla coil, cathode ray tube TV or sometimes even on a trampoline, you've probably noticed that smell; the smell of "sta...

Introduction I will not go into some time-waster of a story about how I came to build this app. It was a prerequisite in a bigger project I am still tinkering with from time to time.

Bash (Shell) Scripting for Beginners Intro

Working from home is already challenging. Add the threat of a cyberattack into the mix, and the situation gets even hairier.

I have looked into this several times because I find it interesting to think about how the tongue works when making a recipe. I say "looked into" it because I wouldn't really describe it as research. How the flavors are going to be perceived can affect how you might want to layer the flavors in your dish. This information mostly comes from an artical in How Stuff Works website. There are several parts of the tongue that you need tobe familiar with when you study it.

Spent the weekend with Sprint's new phone, the HTC Evo G4. Specification wise, it's better than Verizon's Incredible and T-Mobile's HD2. Apple will be announcing the new version of their phone this week. If it's comparable to leaked phone shown over at Gizmodo, then to say which phone is better is debatable. The iphone might have a better battery life but the Evo has an unlimited data plan, unlike AT&T's new tier pricing structure.
You know it's crazy out there when governments start blocking social websites like Facebook, Twitter and even YouTube. But that's what happened in Egypt, when tens of thousands of anti-government protesters took to the streets on Tuesday (January 25th) in hopes of ending President Hosni Mubarak's 30 years of authoritarian power.

Today, we are going to combine what we learned from the Introduction to Cryptography article with our Java programming skills. If you are new to Java, check out Matthew's Learn Java: Part One for a quick beginner's lesson, or check out some of the Java tutorials directly on Oracle.
In this article, I'll show you how to make a simple touch-triggered switch. This is very useful for various electronic projects, from a simple bedside light to a flat panel touch keyboard. The circuit can vary in switching power depending on the transistors you use. For example, if you're looking into creating a 120V light that turns on when touched, you'd need two powerful transistors and an isolation relay. However, a simple flashlight that turns on when touched would only take a couple of ...

Here's another delicious Byte. Ucha Gobejishvili, a Georgian Security Researcher under the handle of longrifle0x, discovered two cross site scripting (XSS) vulnerabilities on the official website of Forbes. He discovered the hole in two different locations on the site, and has already informed the website of the vulnerability.

In this article, I'll show you how to create a simplistic AES python based text encryptor. You'll need python 2.7 and PyCrypto (found here). The code is fairly simple, a user enters an encryption key (which basically tells the program how to scramble the text, using an algorithm), then the text to be encrypted. The program takes the key and text and inputs it into the "cryptograph" or code-based algorithm from PyCrypto. PyCrypto can use 16, 24, or 36 character encryption keys, but for the sak...

Your first, very basic web crawler. Hello again. Today I will show you how to code a web crawler, and only use up 12 lines of code (excluding whitespaces and comments).

Null Byte is looking for forum moderators! Last Friday's mission was to accomplish solving HackThisSite, basic mission 9. This mission delves a little further into Unix commands and remote directory traversal (which is just a fancy term for going through folders blindly).

Welcome to the closing of the second HackThisSite and programming Community Byte. First and foremost, I would like to ask that people start showing up on time to the Community Bytes. If you need help converting your time zone to PST, go to Time Zone Converter. When users do not show up on time, we have to go backwards and catch everybody up. This wastes time and will also make other users' experience less enjoyable when they have to watch and listen to the same thing 100 times. Punctuality as...
JavaScript is the language of the internet. It is what allows us to create dynamic, interesting webpages that are fast, web-based applications and so much more. The primary use of JavaScript is to write functions that are embedded in or included from HTML pages and that interact with the Document Object Model (DOM) of the page. This is the magic that allows all of what we see to happen, and for our browser to be manipulated.

Password strength and encryption are important things when it comes to computers. A password is the entire security of your computer, and OS passwords are not hard to break. Most users believe that if you have a password on your computer via the OS, that you are safe. This is not true at all, sadly.

Social networks like Facebook and Google+ are great for staying connected with family, friends and coworkers—even fans. But sharing and communicating with practically anyone in the digital realm has alienated us from most of the flesh-and-blood beings we see everyday—our neighbors. How well do you know your neighbors?

In this Null Byte, I'm going to teach you about Null Byte Injections. Null Bytes are an older exploit. It works by injecting a "Null Character" into a URL to alter string termination and get information or undesirable output (which is desirable for the malicious user).

Great controls are the most important and difficult part of game design. Games with vector graphics and non-existent stories are classics because their creators managed to create a system where using buttons to control a shape on a screen was intuitive and fun. This is the tradition that Pac-Man has left us with, a gaming world in which controlling the character onscreen in an engaging way is the crux of the game's enjoyment.

Hello readers again! Sorry about the long wait (scary computer problems). Today I am going to talk to you about security problems on Wizard101. I have recently encountered many security flaws on Wizard101, including hacking, frauding and other crazy things. Wizard101 is the target for many online predators, many of who are fully-grown adults aged 60 or 70. Here is the link to an article I found about it: Wizard101 Internet Predators

The internet is a scary place, and if you're like me, you don't want anyone tracking you or learning your search habits. It's a blatant invasion of privacy for companies to do this, but at least we have methods of fighting back—one of which is Tor.