In many programs on Linux, you'll come across programs which allow you to specify additional arguments instead of just simply running the program by itself. If you've used the Kali distribution, I'm more than certain you'll have come across these with the command line tools, else if you have been following these tutorials, we have already come across three tools which also use the same technique, i.e. gcc, gdb and wc. How do we do this with C? Let's find out.

This is a little c++ program that I thought would be handy in the future. Although, I apologize in advance for any errors in the code since I haven't had the chance to compile it yet. Anyway, please if you are a script kiddie please do me a favor and at least read this article fully. :)

Hello null_byters, after some time out here we are again with another tutorial, continuing our beautiful series, today we will write our first real world bash script.
And we meet again Crackers! Welcome to my 7th post (Part-2), this tutorial will explain about some more basics of Batch Scripting, with C00L Scripts, which in turn will help you learn and understand better

For some odd reason, the Chrome Browser on Android doesn't allow you to search selected text when you're in Incognito Mode. This must have been an oversight on Google's part, because the feature is definitely present with the browser in its normal viewing mode, allowing you to highlight text and quickly perform a Google search.

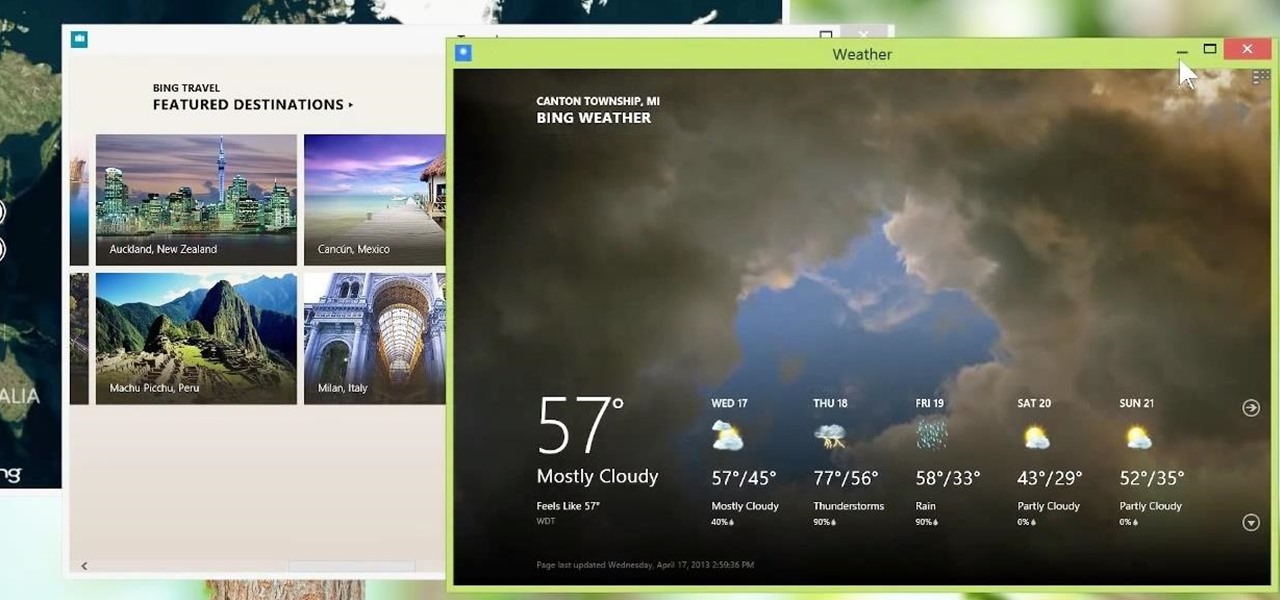
Metro apps are pretty nice, but they absolutely suck on a Windows desktop with a mouse and keyboard. That's to be expected though, since Metro (also known as Modern UI or Microsoft design language) was created mainly with touch input in mind for Surface Pros and Windows Phones.

My friends can be pretty shitty sometimes, but they're my friends nonetheless. On various occasions, they've secretly taken my device and made me look foolish by posting crude and embarrassing posts to Facebook, Instagram, or Twitter. With friends like these, who needs enemies, right? And it's because of these types of friends that we need to substantially upgrade the app security on our devices.

Welcome back, my greenhorn hackers! Recently, I asked the Null Byte community what subject they would most like me to cover in future tutorials. Many of you cited scripting, and I decided it's best to cover this subject soon, so here goes.

With all of the new features and third-party apps out there making Android better and faster every day, it's quite frustrating to me that keyboard advancements remain relatively static.

The absence of a physical keyboard is both a gift and a curse. When it was announced in 2007 that the first iPhone would have a touchscreen only, people literally lost their shit. Now, almost 7 years later, you'd be hard-pressed to find a smartphone that still has a physical keyboard.

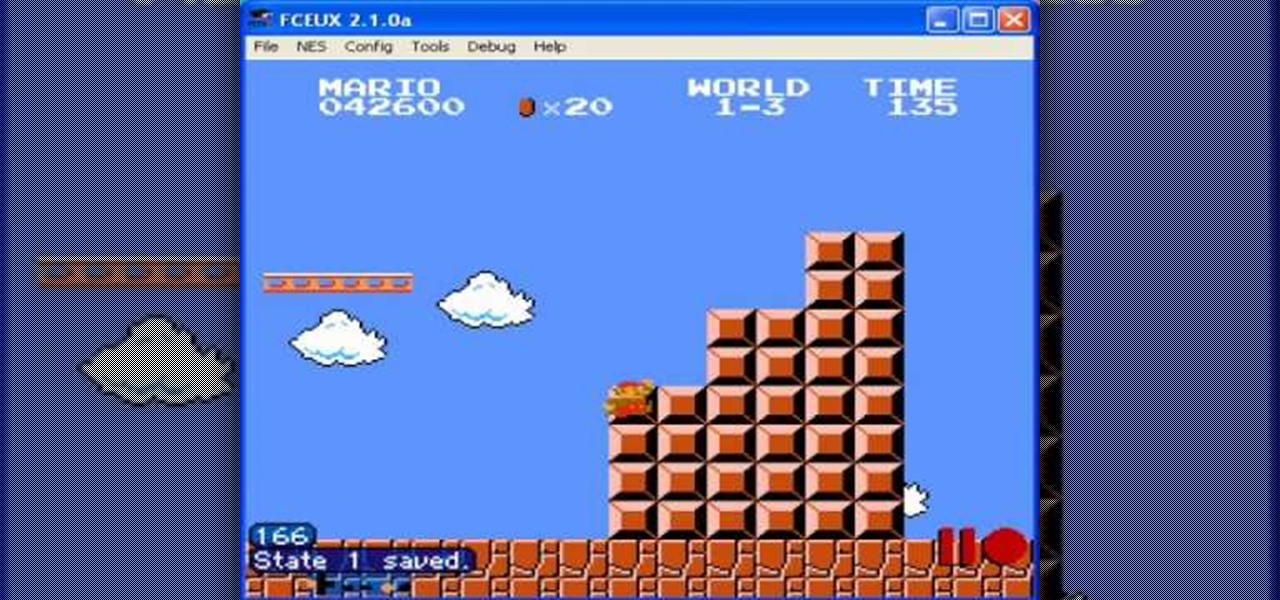
The flagpoles at the end of each level in Super Mario Bros are rewarding when you're playing the game, but if you're setting up a TAS they suddenly become infuriating wastes of time. This video will show you how to TAS skip the flagpoles, which should improve your time substantially.

Super Mario 64 is one of the most influential games of all time and a favorite of TAS aficionados the world over. This video will teach you a cool TAS trick that will allow you to skip the Dire, Dire Docks level and improve your competition time substantially.

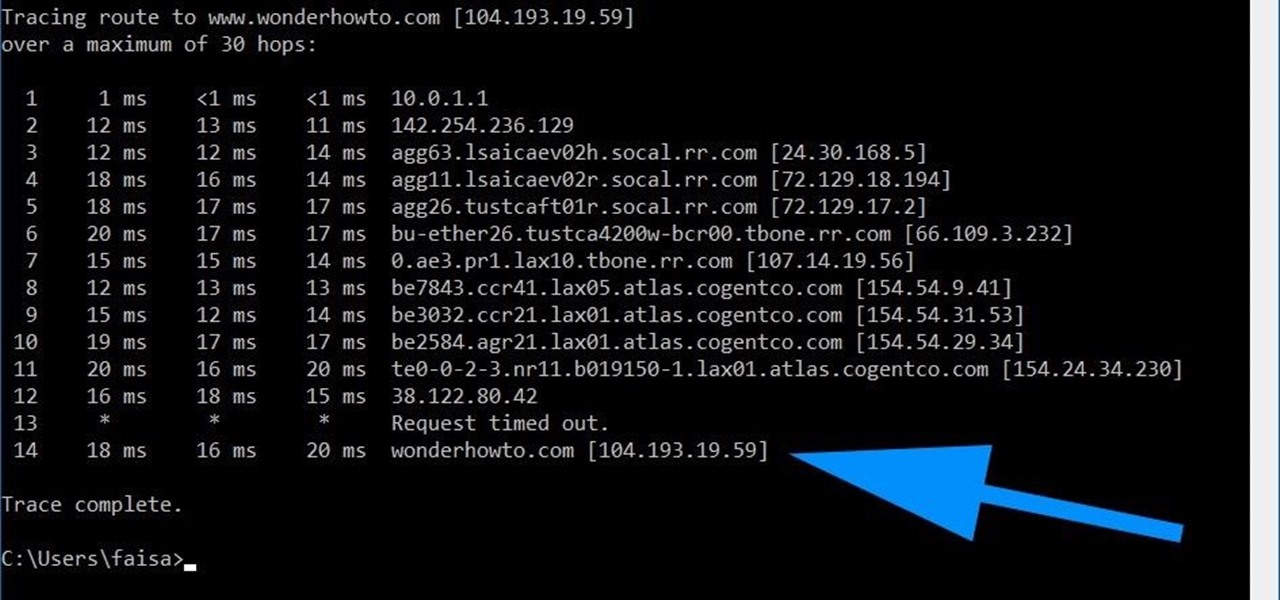
Using a simple trace trick, you can easily look up the IP address and its location for any website. This method uses a command line command to first find the IP address of a given website, and then uses a free online tool to get that IP's location.

We are now in the age of 5G. Carriers worldwide are upgrading their networks to the newest standard for mobile, which will dramatically improve your phone experience. How? By giving it download speeds and latency that surpass Wi-Fi. But before you upgrade, there are few things you should know first.

An attacker with shell access to a Linux server can manipulate, or perhaps even ruin, anything they have access to. While many more subtle attacks could provide significant value to a hacker, most attacks also leave traces. These traces, of course, can also be manipulated and avoided through methods such as shell scripting.

For the most part, Google Wifi and Nest Wifi systems take care of themselves. But there are still a few manual features that might come in handy, like being able to check on network activity to see which devices are using the most bandwidth when your connection gets bogged down.

The $35 Raspberry Pi is an amazingly useful single-board computer (SBC) with a good balance of price, performance, and connectivity options. But for some projects, it just isn't enough. Whether you need more computing power, a smaller size, or better machine-learning capabilities, there are other options available.

Step 1: What Exploit Development Is and Why Should I Be Interested on About This Topic

Welcome back, my hacker novitiates! In the previous two posts in this series, we looked at the basics of buffer overflows. In this post, we will look at one technique for finding buffer overflows. We will try to send random, oversized, and invalid data at a variable to see whether we can make it crash or overflow. This process is known as fuzzing. It is often the first step to developing an exploit, as we need to find some variable that is susceptible to overflowing.

Even if you have the fastest internet connection in the world, it's not going to be fast if your Android device isn't optimized to use all of the bandwidth. I have pretty fast speeds at home, but every now and then my web surfing on my Nexus 7 tablet is halted in its tracks—for seemingly no reason.

Interested in amplifying your ukulele? Provided your ukulele has an electrical pickup, it's quite easy. And this free video ukulele lesson from Live Ukulele will show you how it's done.

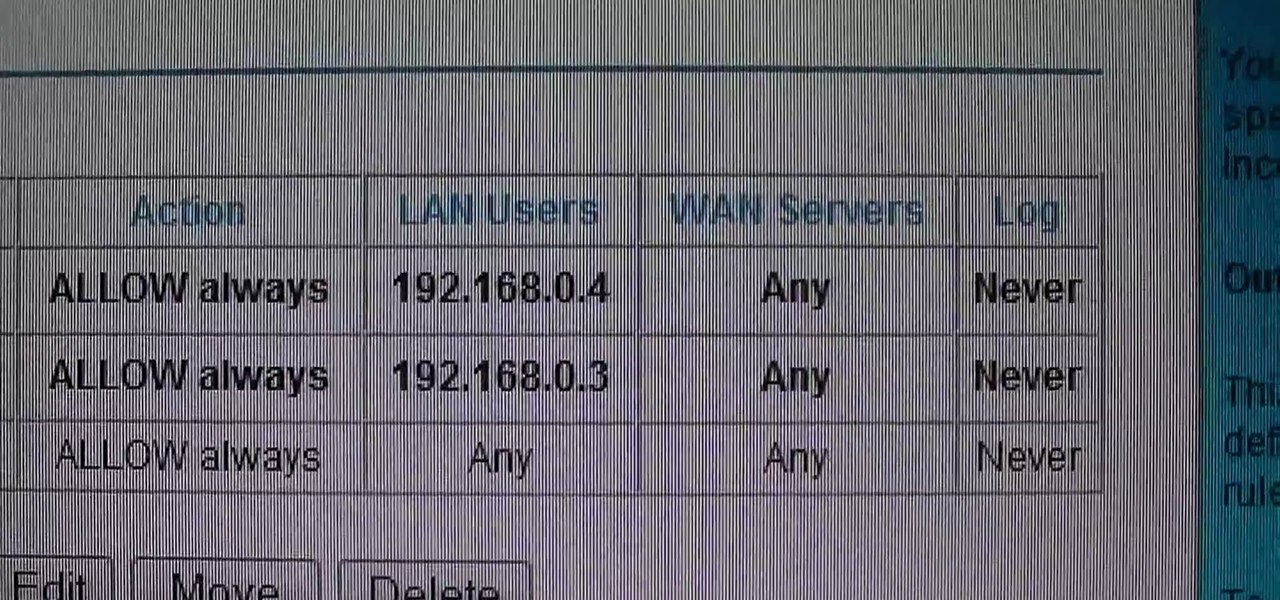
This video shows how to change the NAT type on a PS3. Go to connection settings>network settings>internet connection settings>OK>custom>wired connection>auto detect>manual. Choose an IP address that is different from your router, any other consoles, etc. Click right>automatic>do not use>enable. Press x to save settings, and test your connection. In this example, NAT type is 2. Now go to your PC and open IE. In the address bar, input router IP address, username and password. Go to Firewall Rul...

Learn how you can remove the blue haze from photos in Photoshop with this tutorial! 1. Select any image and right click on the menu click on Levels. 2. Select each and every channel and set input levels for red, blue and green and see the preview of the image. Set as RGB in Channels. 3. Now, click on "Sample in image to set gray points" and click on the area of the image which need to be set gray click on ok button. 4. From the picture icons select eye dropper and make sure it is set as 5 by ...

If you've ever had a little trouble trying to program your calculator, you may find a little relief with this four-part video tutorial. Here, a Texas Instruments (TI-84 Plus) calculator will be used to explain the programming process. The four parts include:

First you need to do is press the t button in your keyboard and add a new mono track. Choose mono in format and click OK.

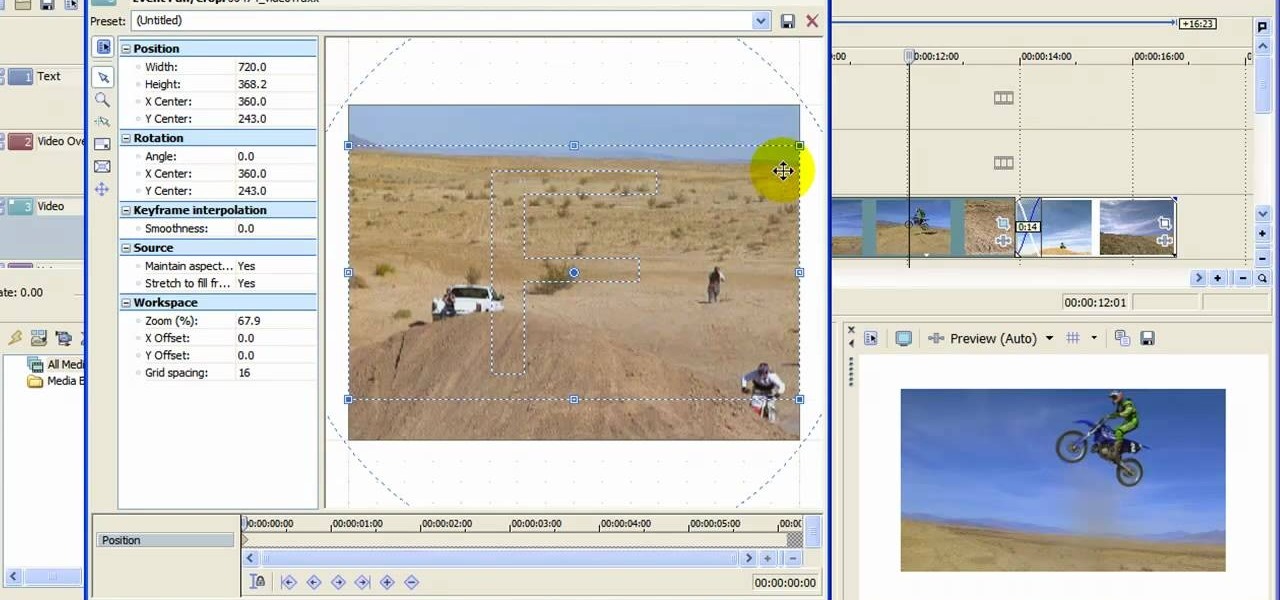
When you upload your videos onto YouTube, you will need to have your video in wide screen format, if you want to avoid having black bars on either side of your video. In order to do that, with Sony Movie Studio, you will need to go to "project". Click on "properties".

If you've rooted your Motorola Droid chances are that you are enjoying the results, but are concerned about the consequences if you phone updates or in any way become incapacitated since your phone manufacturer will not be pleased with what you've done to the phone. One way to ameliorate these fears is to back up your phone. This video will show you how to use Nandroid to make a backup of your rooted phone.

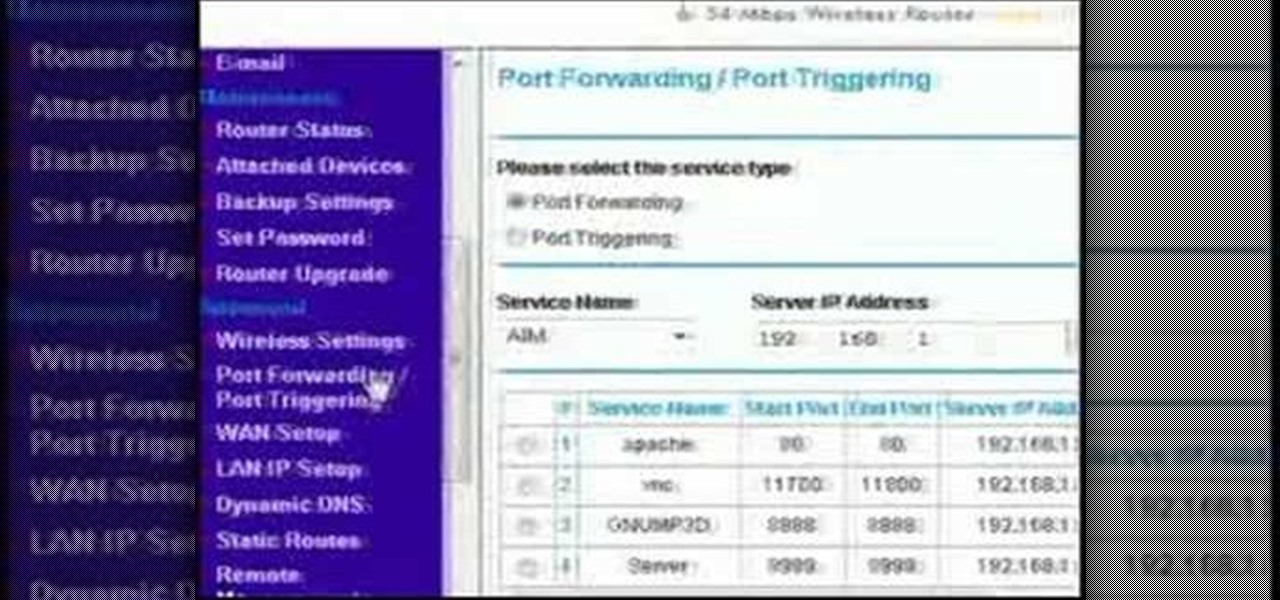
This video discusses how to bypass your router to access your server. In the search window type in CMD to open up a command prompt. Then type in ipconfig to bring up the ip configuration. You want to look for the ip address for the default gateway and the one for your computer. They should both start with 192.168. Once you find them open up internet explorer and type in the ip address for your default gateway and it should then prompt you for a user name and password. Log in and look for a po...

With the Android platform on a large amount of mobile phones today, chances are you have one. Sometimes messaging on the phones can be a little confusing, but there's a simple explanation for texting your friends and family. Best Buy has answers. The Best Buy Mobile team explains how simple it is to send a text message on your Android enabled cell phone.

In its heyday the Atari gaming console was the Playstation of the 80s. Sure, you could download some wannabe emulator, but why not go a step further and purchase an actual Atari. They're still floating around and just think how cool it'll be to play pong in hi-definition.

Circuit bending an audio device typically involves removing the rear panel of the device and connecting any two circuit locations with a "jumper" wire, sending current from one part of the circuit into another. Results are monitored through either the device's internal speaker or by connecting an amplifier to the speaker output. If an interesting effect is achieved, this connection would be marked for future reference or kept active by either soldering a new connection or bridging it with cro...

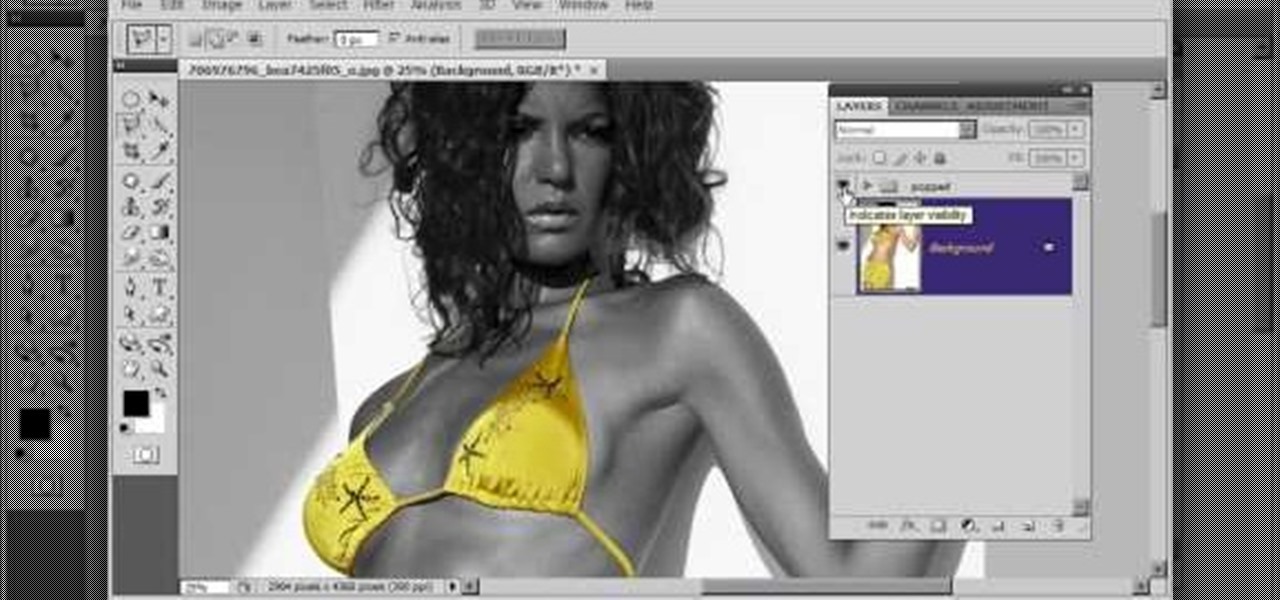
Learn to create a fashion editorial style color in Photoshop! 1. From CHANNELS button select color of the Model. It will show different colors select as per your choice. 2. Click on Levels it will show the image selected. 3. Right click and select Black&White it will open ADJUSTMENTS button adjust the color. 4. Go back to CHANNELS button they all images will look same. Copy channel Blue and Select Blue copy3 and color model's body and hair with black. 3. Click on ADJUSTMENT button and adjust ...

This is the 12th puzzle, entitled "Titans of Industry", in Assassin's Creed 2. Code wheel puzzle 1: The key here is in the “4=1” on the blueprint at the left of the screen. Line up the red 4 over the gray 1 and input the following code: 917240. Image 1: This one’s the opposite of the light-bulb “puzzle” from before – just move the dollar sign over the bulbs to extinguish them. Image 2: Highlight the glowing ball at the center of the image. Code wheel puzzle 2: Your hints here are the “2” on t...

Congratulations! You're the proud new owner of an Xbox 360. But before you can play, you need to hook it up.

This Houdini 9 software video series focuses on examples of when and how to use Attribute Transfer. Part 1 covers Attribute Transfer One Point:

I love making beeps and bloops with the Arduino pitches library, but sometimes archaic 8-bit tunes just don't cut it. Whether you want your robot to terrify your enemies with a demonic synthetic voice, you just need a pocket boom box on the go, or you want to a miniature guitar amp, a simple LM386 amplifier can crank up those signals loud enough to play through any speaker.

Building a DIY Alarm System: The Concept So, you want to protect your property, or maybe a room, car, or even your backyard. The concept of an alarm system is to notify the "alarm administrator" that there is an intruder entering the previously designated boundaries. The triggers for this boundary could be as simple as a pressure sensor, or as complicated as a laser network. They all do the same thing, but some work better than others.

Mrs. Victoria explains us how to change the language on your Keyboard (Windows)1. Go to the control panel and select the option ‘Change keyboard or other input methods’ and a dialog box (regional and language options) pops up.2. Click on change Keyboard, and another dialog box pops up.a) In the new dialog box, click ADD Button, and select the input language you require and click OK.3. You have the feature to alter your language input whenever you want by coming to this (Change keyboard langua...

Password cracking is a specialty of some hackers, and it's often thought that raw computing power trumps everything else. That is true in some cases, but sometimes it's more about the wordlist. Making a custom, targeted wordlist can cut down cracking time considerably, and Wordlister can help with that.