As the largest wireless service providers in the United States, AT&T and Verizon Wireless carry some serious clout. Sadly, they use some of this power to heavily modify the Android phones that they offer.

Welcome back, my greenhorn hackers! Continuing with my series on how to crack passwords, I now want to introduce you to one of the newest and best designed password crackers out there—hashcat. The beauty of hashcat is in its design, which focuses on speed and versatility. It enables us to crack multiple types of hashes, in multiple ways, very fast.

Cold brewing tea and coffee are all the rage, and for good reason: they're idiot-proof. I, personally, am a total dunce at brewing coffee. It either ends up strong enough to peel paint from a car or so weak that you can see through it. Meanwhile, I have friends who inevitably brew green tea to the point where it's painful to drink it.
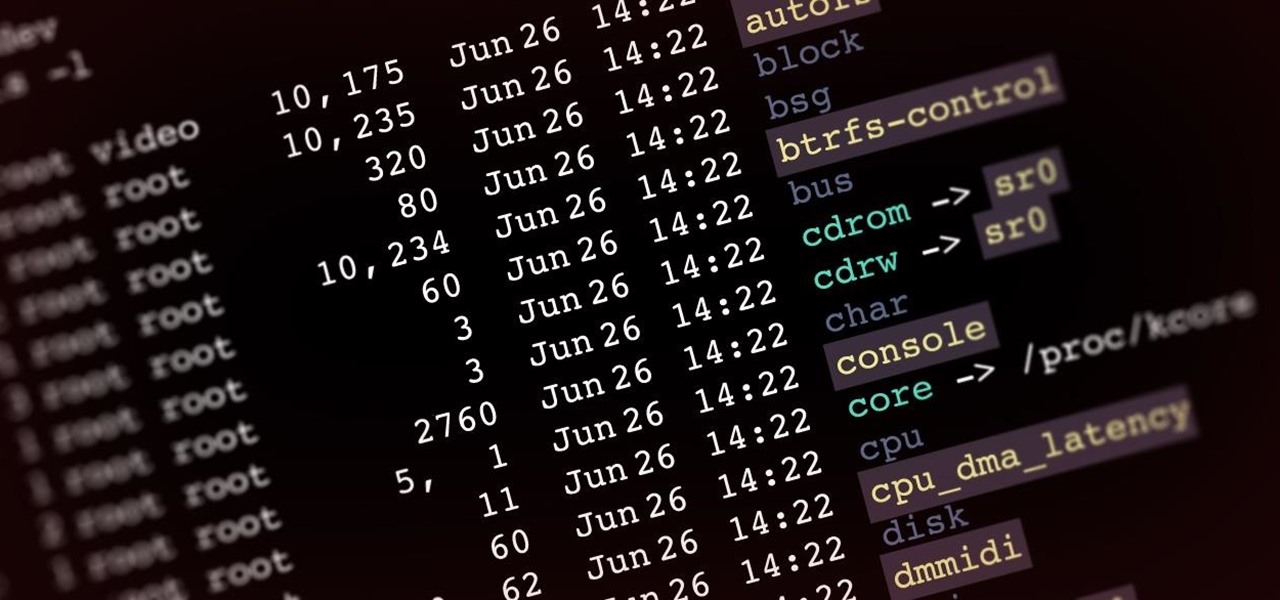
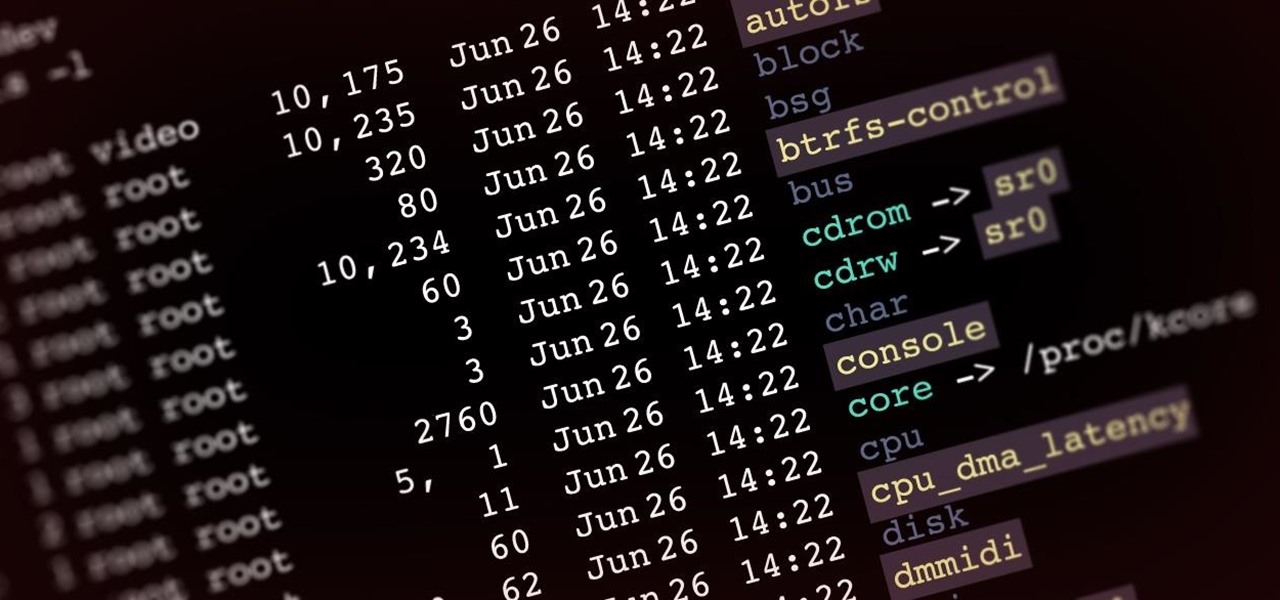
Welcome back, my aspiring hackers! In recent tutorials, I have made reference to the name and location of the Linux devices in the file system, such as sda (first SATA or SCSI drive). Specifically, I have mentioned the way that Linux designates hard drives when making an image of a hard drive for forensic purposes.
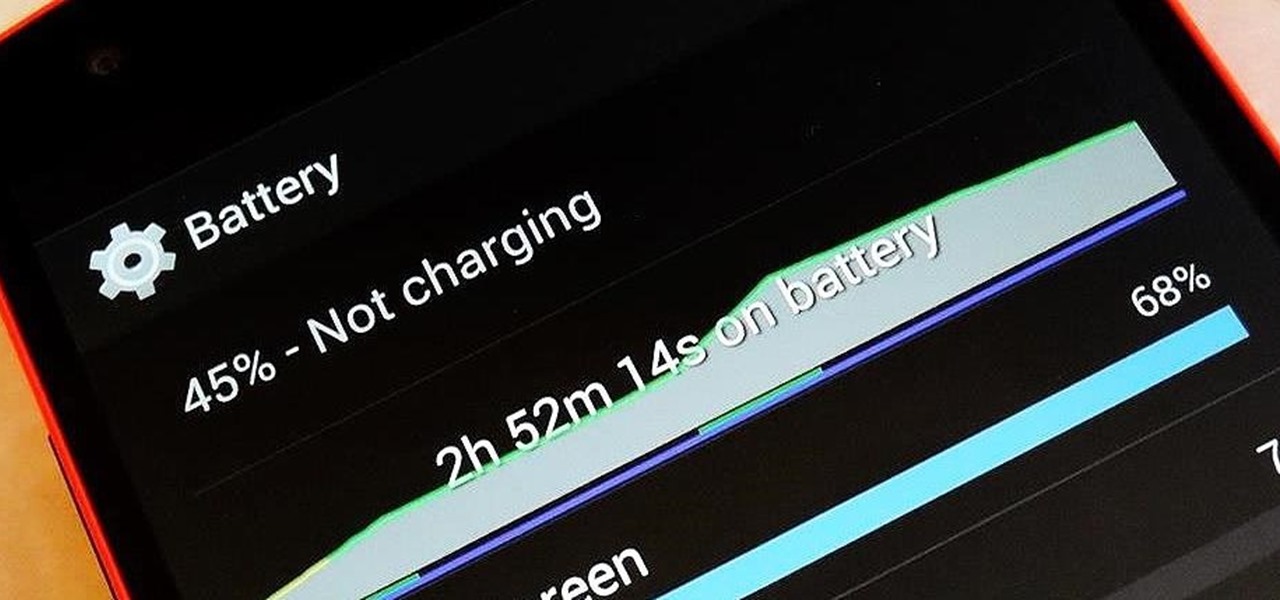
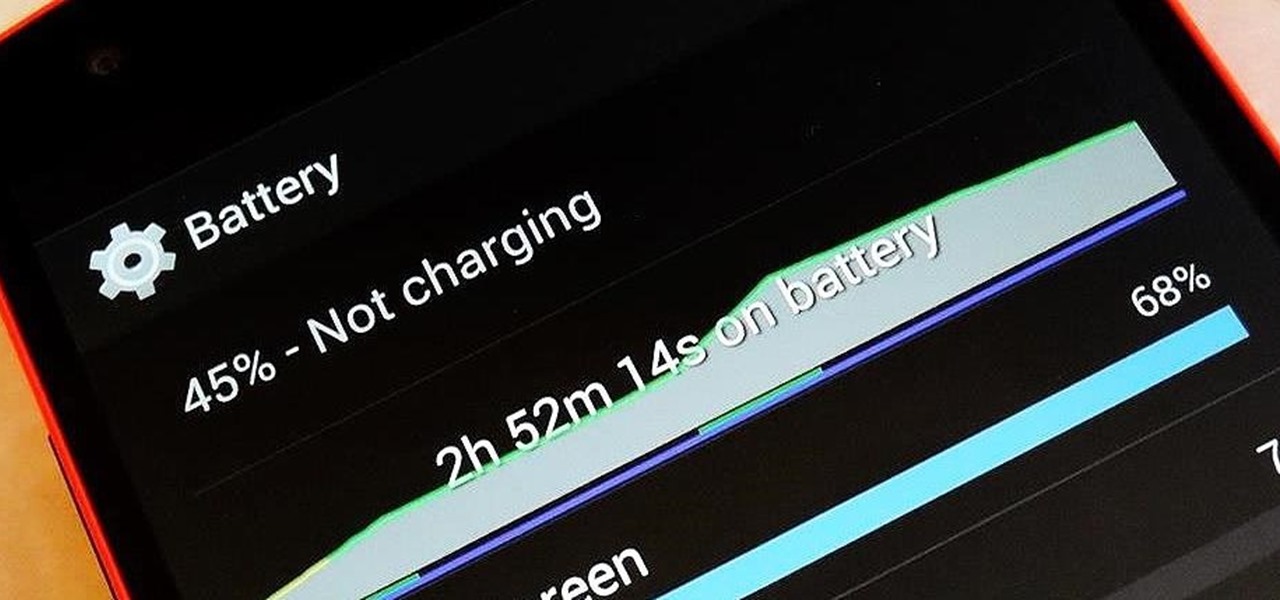
There are so many things to love about the Nexus 5, from timely updates to newer versions of Android to a terrific blend of price and specs. But while mobile phone tech keeps churning along, battery technology isn't quite up to snuff yet, and I find myself wishing that my phone's battery lasted longer on a single charge.
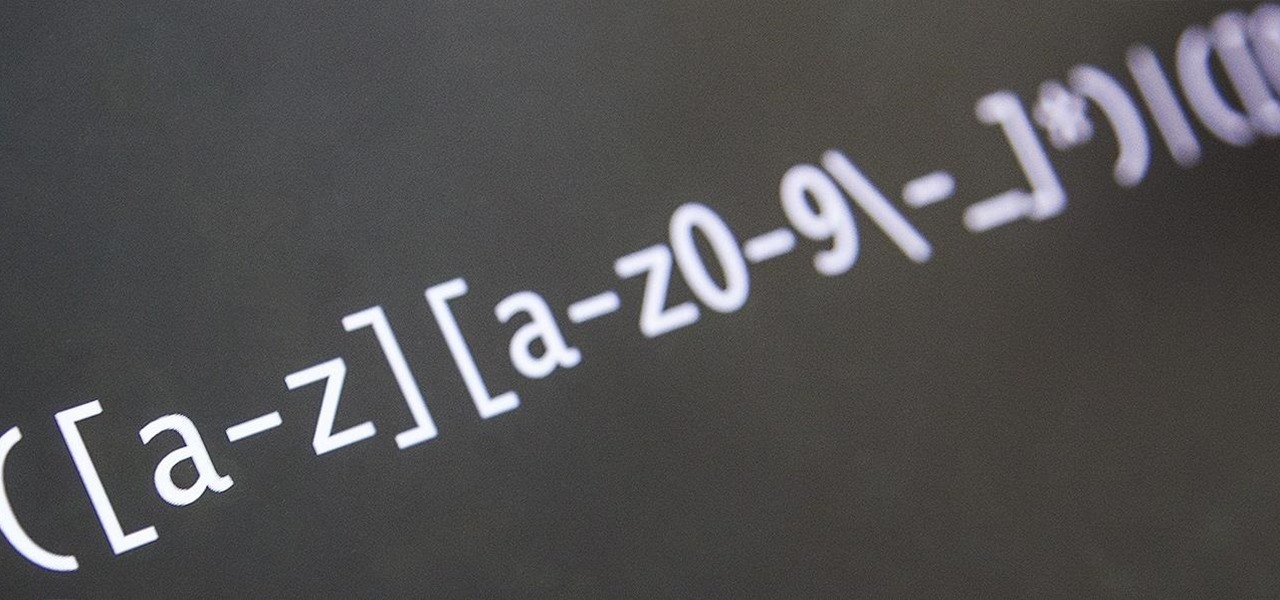
Welcome back, my novice hackers! This next subject might seem a bit obscure, but I promise you, this lesson will benefit you significantly either as a hacker or system admin. This tutorial will cover what is usually referred to as a regular expression, or regex for short.

Welcome back, my hackers novitiates! As you read my various hacking tutorials, you're probably asking yourself, "What are the chances that this hack will be detected and that I'll land behind bars, disappointing my dear mother who already thinks I'm a loser?"

Welcome back, my tenderfoot hackers! I recently began a new series on digital forensics to help tenderfoot hackers from being detected and ultimately, incarcerated. In this installment of that series, we will look at recovering deleted files. This is important to hackers because you need to know that even when you delete files on your computer or on the victim's computer, a forensic investigator can usually recover them.

The holidays are quickly approaching, which means everyone will be scrambling over the next couple of weeks to find the cheapest options for flights to wherever home is. There are so many sites to buy them from that it can be hard to know where to start, so we've compiled some tips and tricks for making the process as painless as possible, whether you're flying home for Thanksgiving, Christmas, or whenever.

There are few apps on my iPhone that I visit on a daily basis, and one of them is Drippler, the discovery and news app that tells you everything you need to know about your device.

Welcome back, my hacker novitiates! Many of you have probably heard of a man-in-the-middle attack and wondered how difficult an attack like that would be. For those of you who've never heard of one, it's simply where we, the hacker, place ourselves between the victim and the server and send and receive all the communication between the two.

Welcome back, my greenhorn hackers! Now that we're familiar with the technologies, terminology, and the aircrack-ng suite, we can finally start hacking Wi-Fi. Our first task will be to creating an evil twin access point. Many new hackers are anxious to crack Wi-Fi passwords to gain some free bandwidth (don't worry, we'll get to that), but there are so many other Wi-Fi hacks that are far more powerful and put so much more at risk than a bit of bandwidth.

Welcome back, my tenderfoot hackers! This is the third installment of my series on basic Linux skills that every hacker should know. Although some hacking tools are available for Windows and Mac, every real hacker uses Linux—for good reason.

Okay, so you've decided to take the plunge, and participate in our Love. Earn program with a how-to article. But, for whatever reason, your article keeps getting rejected by WonderHowTo, and you're wondering, well, where's the love?

There's an iOS feature that benefits many users, but it's absolutely vital if you wear AirPods or other headphones models connected to your iPhone. A large number of iPhone users don't even know about it, especially since it's disabled by default and hidden deep in the system settings.

A hidden TikTok feature changed how I watch videos in the app, and it's about to transform your TikTok video-watching habits too.

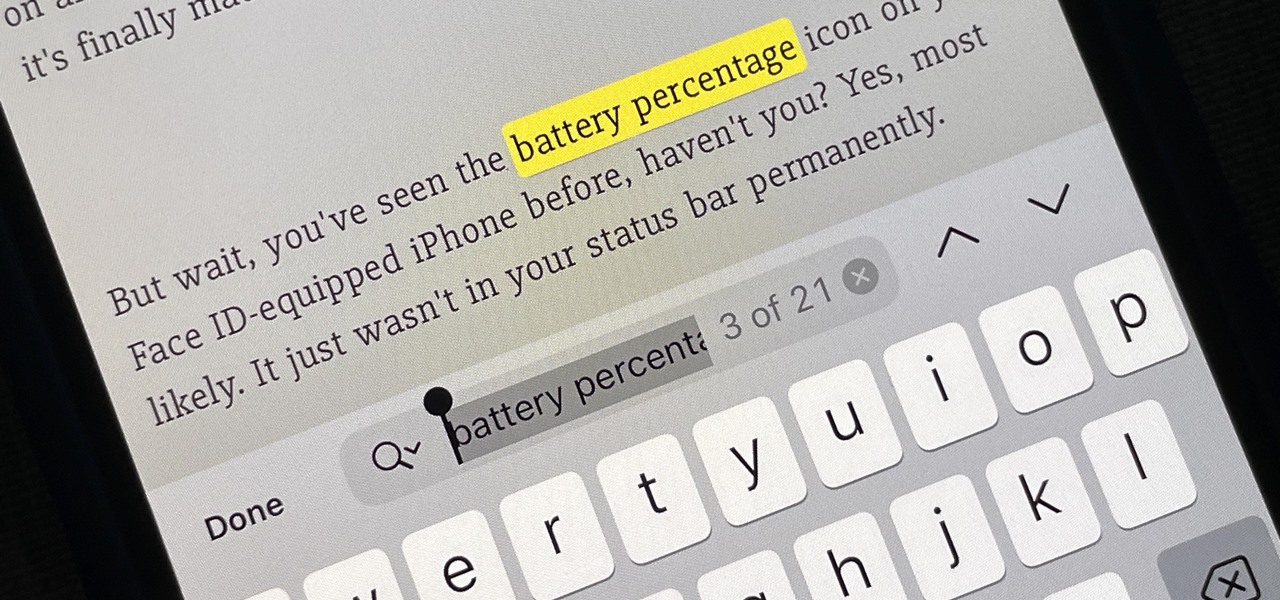
There's a new hidden Safari feature for your iPhone, one that makes it even easier to find words, numbers, phrases, and other text on a webpage.

There's a little-known secret in the world of microwave ovens that even the manufacturers don't care to tell you in their manuals. And once you know it, you'll never go back to using your microwave as you used to.

The US Department of Treasury isn't generally known for being on the very edge of technology innovations (see the current hubbub around crypto), instead usually waiting until certain tools have been battle-tested in the mainstream or enterprise sector.

Now that Snapchat has extended its virtual try-on powers from the face and feet to the wrist, Samsung is leveraging the new capability, along with an interactive twist, to sell its smartwatches.

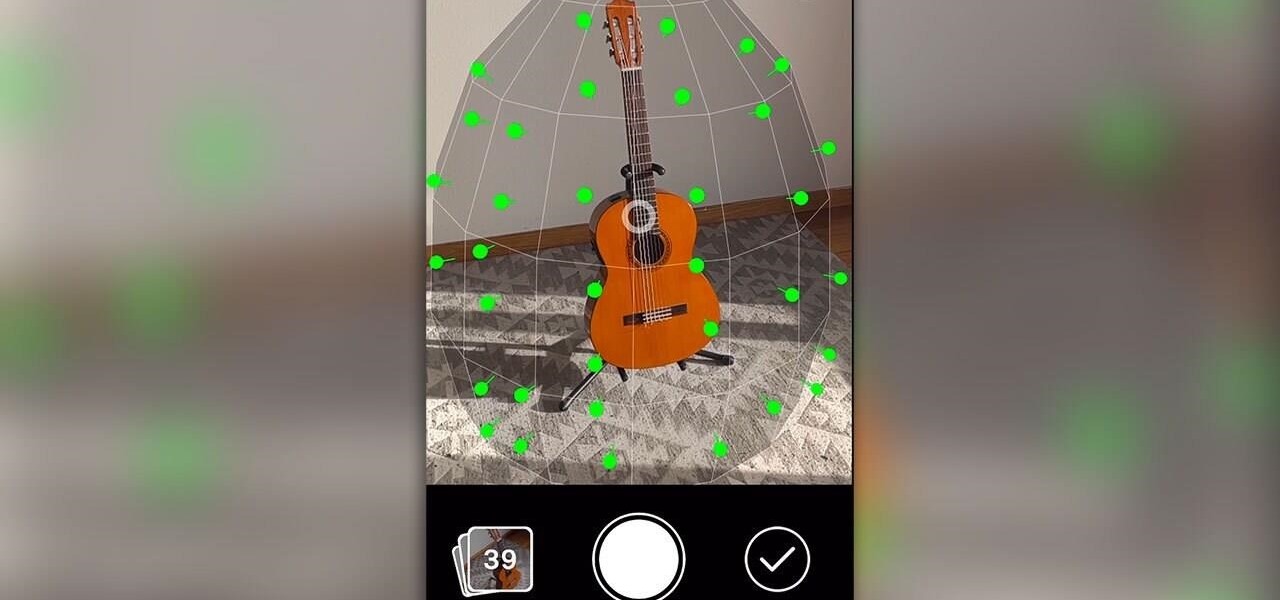
One of the more exciting augmented reality announcements Apple made during its WWDC keynote on Monday came in the form of Object Capture, a new 3D scanning feature coming to macOS Monterey.

If you save your passwords in Chrome or even just use Android's default password manager, Google has some new security tools you'll be interested in.

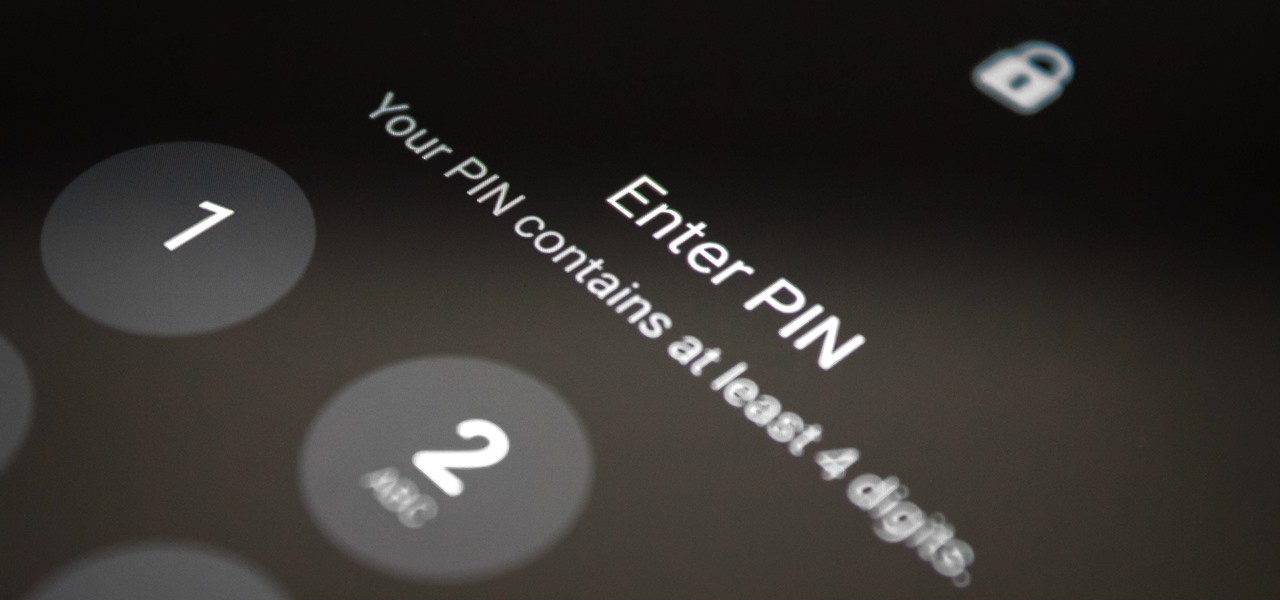
You know the drill: After booting up your iPhone, you need to swipe up or press the Home button, then punch in the passcode to unlock Face ID or Touch ID. It's the way things have always been — but it doesn't have to be. Instead, you can unlock your iPhone using just your voice, even after a restart.

After awarding $410 million to the company that supplies it with VCSELs and LiDAR sensors, Apple has made another strategic investment into a company that may contribute to future augmented reality hardware innovations.

Pretend you're a phone thief for a moment. You might be a pickpocket or a stickup kid, but you're in possession of other people's phones on a regular basis. Now ask yourself this: what's the first thing you do after you steal a phone?

Ah, the dreaded "green bubble" group chat. All it takes is one non-iPhone contact to turn an entire thread from iMessage paradise to SMS slog. Normally, it isn't that bad since the group chat still functions. However, sometimes, you end up getting messages individually instead of in a single group thread. Before you go blaming your Android friends, know that the issue is probably on your end.

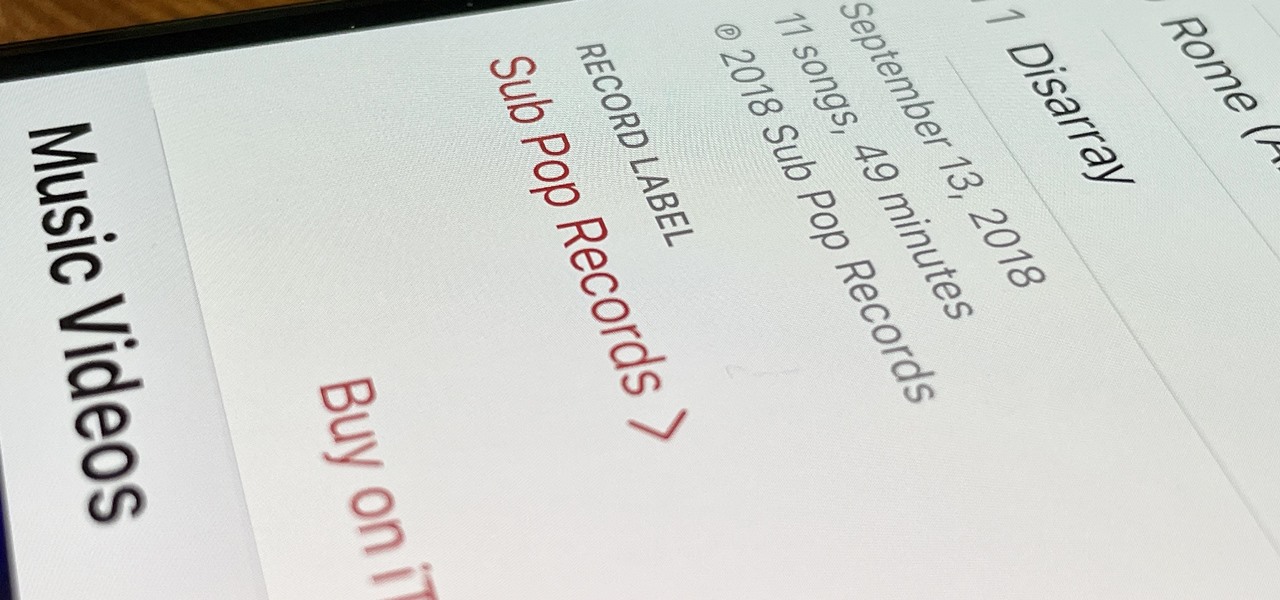
Some record labels release albums across the entire music spectrum, dipping their toes into every genre, sub-genre, and language imaginable, while others attack only the categories they're good at. So if you're hunting for new music, and the Listen Now, Browse, and Radio tabs in Apple Music are getting stale, iOS 14.5 lets you browse like-minded artists, albums, and playlists by specific record labels.

It's no secret that Apple and Spotify haven't exactly gotten along in the past, but things are looking better than ever in iOS 14.5.

Disney Plus shows WandaVision and Falcon and the Winter Soldier are both streaming hits, but the two series could not be more different in terms of giving fans a taste of the Marvel Cinematic Universe.

Over the past three years, Epic Games has raised billions of dollars in funding on the success of Fortnite as well as Unreal Engine, one of the top 3D engines available for developing games and AR experiences.

The signal bars in your iPhone's status bar are great visual indicators for knowing how good your cellular reception is, but they're not very accurate. Instead of showing the actual amount of signal you're receiving, they just give you a general range, and you'll have no idea if three out of four bars is actually a good connection or not. But there is a trick to see the real numbers.

When it comes to augmented reality wearables, it's currently an enterprise world. As such, Magic Leap's latest Lumin updates are centered on features that appeal to enterprise customers. And Epson and Spinar are joining forces with a solution for distributed workforces.

Modern life is almost completely digital ... almost. While you can get by in many cases with just your iPhone, sometimes a situation requires a hard copy. In the past, there was really no convenient way for you to get a Reminders list from your iPhone onto paper, but iOS 14.5 changes that.

Apps don't need to come bundled with an entire browser just to be able to display web pages — instead, they can call on the system WebView browser to render content for them. Android's default WebView renderer is Google software, which isn't quite as privacy-forward as some other options.

Compared to Apple's products like the iPhone and iPad, Android phones and tablets are very flexible devices. For instance, you can set a new home screen, replace the lock screen, or even beam files using NFC — but that's just the software side of things, and the flexibility goes well beyond that.

Help me, George Clooney. You're my only hope. If that mash-up of cultural references doesn't make sense, it will momentarily.

After updating to iOS 14 or getting a new iPhone with iOS 14 preinstalled, you'll notice orange and green dots that occasionally appear at the top of your iPhone. These dots appear on all supported iOS 14 devices, from the iPhone 6S to the iPhone 12 Pro Max, and are there to protect you, but how?

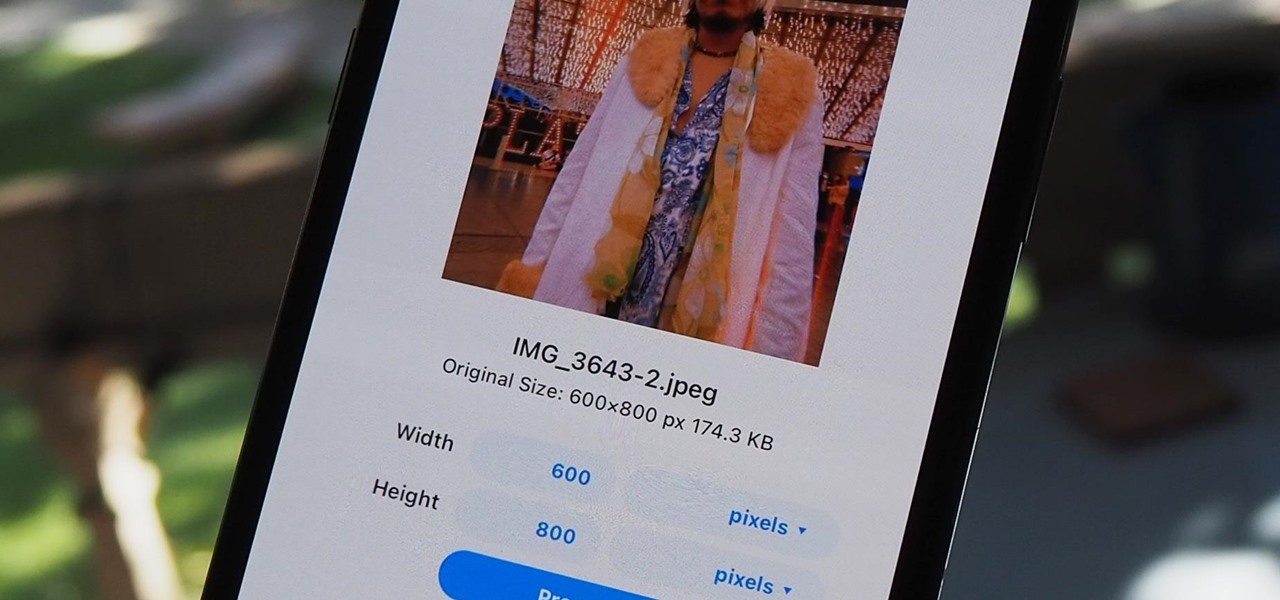
The rear cameras on iPhones have remained at 12 megapixels since the iPhone 6s, but with each new iPhone model, more data is going into photos. That means larger file sizes. If you're running into issues with your pictures being too large, whether you're sharing or uploading them, there's an easy way to resize an image or group of images using a shortcut.

One of iCloud Photo's biggest perks is its ability to store large video files taken with your iPhone, so you can fill up your iPhone's storage with other items. That said, when you play back those videos, you may not be watching the footage in its original quality. Instead, they may be low-res versions. To view the high-quality originals — or to make sure that's what you see — just follow this trick.

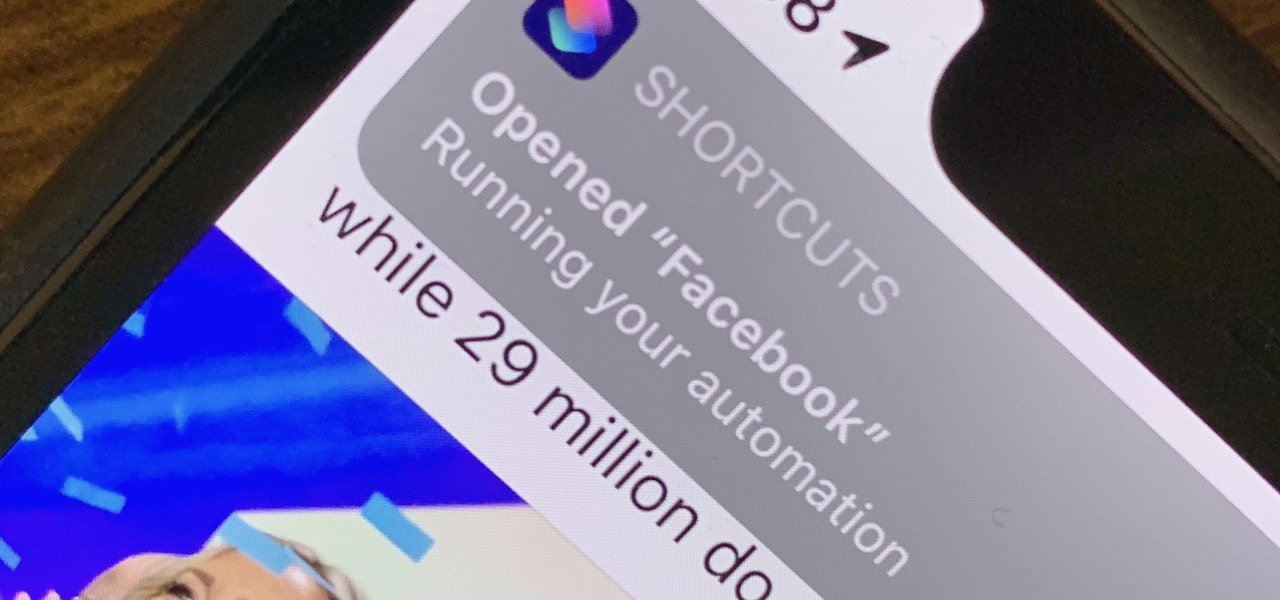
There are a lot of cool shortcuts you could run on your iPhone, but in iOS 13 and iOS 14, you'll likely see a notification any time you try to run an automation. Shortcuts should feel seamless when their actions are performed, and getting a banner alert each time one initializes takes away the seamlessness of it all. But there is a way to block them.