Today's Tidbit: Why Women Live Longer Than Men
Life has many perils: parasites, predators, and pitfalls. Eventually, any organism will succumb, and if that organism has not first passed on its genes, those genes will face extinction.

Life has many perils: parasites, predators, and pitfalls. Eventually, any organism will succumb, and if that organism has not first passed on its genes, those genes will face extinction.

Anyone that has ever watched a member of the opposite sex play a video game knows that the other gender does it wrong.

When we surf the web, we tend to do it for selfish reasons. Whether it's on Facebook, Twitter, YouTube, Pinterest, or Wikipedia—we're trying to connect with people, voice our opinions, watch funny videos, or do research for that 12-page paper due tomorrow. Whatever it is, it's usually to benefit ourselves. Well, what if you could not only benefit yourself while surfing the web, but benefit others in need, without even having to alter your habits?

Thanksgiving is pretty much the only day out of the year when you can be a complete fatass. It's totally expected, if not encouraged. In fact, if you aren't stuffing your face with a bunch of delicious and unhealthy food, people start to look at you funny.

In this project, you'll learn how to re-purpose low-cost sprinkler parts into a high-powered CANDY CANNON. Be the coolest person on the block by building a pneumatic device that will launch candy 100 feet in the air—you can make it rain down all kinds of sugary treats!!!

TIFF 2012 Wrap-Up - Pounds Personally Gained: 4.5

The mighty Arduino microcontroller can be used to show children how robots work, it can be used to hack into hotel rooms, or it can be used to let you know when you've got a new job opportunity!

At the recent DefCon conference in Las Vegas, researchers opened many of the top commercially available gun safes with simple tools like a straw or a paper clip, and in one case, just by shaking it a bit. The investigation began after the researchers, Toby Bluzmanis, Marc Tobias and Matt Fiddler, learned that certain Stack-On safes, issued to some law enforcement officials to secure their firearms at home, could be opened simply by jiggling the doorknob.
I'm sure a lot of people have been following the news and depending on your position on the issue, you might have been happy or dissappointed about the fact that Obamacare has been OK'd by Congress. Let's see what this really means to us.

Save money on your kid's next party by making your own hats! These hats are made with newspaper, which makes them virtually free to create. Making your own hats is also a great activity to do with the kids at a party or anytime!

Lose weight with this handy Chindogu invention. Shaving Cream Man Solution show teaches us how to diet using the Mirage Meal - Mirror Bowl. You can purchase the children's book featured in this video by following this link: http://www.blurb.com/bookstore/detail/176116

In this video series, our expert Katalin Toth will teach you how to do crafts with children. She will show you how to make a toy boat including how to paint the boat, glue the popsicle sticks, cu the popsicle sticks, and test the boat out in water. Katalin and her children will also teach you how to make a toy water mill including how to cut the popsicle sticks, how to add soil, and how to make a decorative star for the toy water mill.

In this instructional video clip series, our expert will show you how to make many types of simple crafts with your children using easy to find materials. Show you child how to make simple Christmas and holiday crafts, projects using simple materials like clothes hangers and clay, dinosaur projects and much more!

In this kids’ crafts video series, learn how to nurture the growth of your child’s mind and imagination, as well as how to train them to create—through clay pottery in this instance. Our expert will give you some basic instruction on how to make pottery and what craft supplies you need. Then get some free ideas and projects to work on, including a Christmas ornament and a pinch pot. Finally, learn how to use a pottery wheel, and how to teach your kids to use one.

The enterprise-focused category of augmented reality doesn't often get the headlines due to its relatively sedate profile as a mostly factory floor and training-based tool.

The USB Rubber Ducky and the Digispark board both suffer from the same issue when attacking macOS computers: a keyboard profiler pop-up which tries to identify any non-Apple USB keyboards. While it's an annoying setback, the solution is a simple modification that allows Mac computers to be targeted, which affects the ability to target Windows and Linux devices.

MouseJack vulnerabilities were disclosed over three years ago. Some wireless keyboard manufacturers have since issued firmware updates, but millions (if not billions) of keyboards remain unpatched worldwide, either because they can't be updated or because the manufacturer never bothered to issue one.

Until very recently, Apple apps were among the only ones that would play nicely with Siri on iPhones. If you wanted to take advantage of the digital assistant to, say, compose an email, you would need to go with Apple Mail instead of the email client you actually use. As of iOS 12, this is no longer the case.

As penetration testers, we sometimes need to securely store customer data for prolonged periods. Bruteforce-resistant, vault-like containers can be created with just a few commands to protect ourselves from physical attacks and unintended data disclosures.

Gmail conversations, Facebook private messages, and personal photos can all be viewed by a hacker who has backdoor access to a target's Mac. By livestreaming the desktop or exfiltrating screenshots, this information can be used for blackmail and targeted social engineering attacks to further compromise the mark.

Most users don't realize how much valuable data is in their network traffic. With a few simple tools, an attacker can quickly pick out cookies, passwords, and DNS queries from a macOS device as it covertly streams the victim's network traffic to the attacker's system. Here, we will cover two methods for analyzing packets flowing from a Mac.

Command injection is a technique used by hackers to execute system commands on a server, usually via a web application or some kind of GUI. This can happen when an application provides some sort of functionality to the user involving the use of system commands. When the input is not properly sanitized, commands not originally intended to be run are allowed to be executed.

Passwords and data stored in web browsers are extremely valuable to hackers. If not for financial gain, black hat hackers may still leak your passwords and personal information for amusement. Never undervalue what you're worth to a hacker.
Apple released iOS 12 on Sept. 17, and most of the announced features have been released for the iPhone's latest available operating system. However, some brand new features can be accessed with Apple's latest beta, iOS 12.4. If you want to try out all its new features before everyone else, you can install the developer or public beta on your iPhone right now.

Google, Amazon, and Facebook are always listening. But what's worse? Hackers are listening, too. Windows PCs are particularly vulnerable, but with a few simple commands, a remote attacker can even take over the microphone on someone's Mac computer, streaming audio and listening to private conversations in real time without the victim's knowledge, abusing an overlooked security consideration.

While hackers have taken advantage of numerous vulnerabilities in Adobe's products to deliver payloads to Windows users via PDF files, a malicious PDF file can also wreak havoc on a Mac that's using the default Preview app. So think twice before double-clicking a PDF open on your MacBook — it might just be a Trojan with a rootkit inside.

A convincing domain name is critical to the success of any phishing attack. With a single Python script, it's possible to find hundreds of available phishing domains and even identify phishing websites deployed by other hackers for purposes such as stealing user credentials.

Using a keylogger to intercept keys pressed on an infected computer can circumvent encryption used by email and secure chat clients. The collected data can often reveal usernames, passwords, and potentially compromising and private information which hackers abuse for financial gain.

After setting up your phone, there are a number of things you should do immediately before download your favorite apps. Specifically, now that your data is on the device, you need to take steps now to ensure it's both protected and retained. Fortunately, most of these steps are a one-time process.

At Build 2017, the annual developer's conference, Microsoft featured a Windows Mixed Reality Academy. This class was designed to get a developer started creating Mixed Reality experiences quickly. For those of us already developing for the Microsoft HoloLens, while the class — which is now available on the Microsoft website — did offer our first real chance to work with the new Acer HMD, there was not much depth.

The food TV chefs prepare make our mouths water. From one scrumptious creation to another, they fly through preparation without frustration or error. They make us think we can do the same with similar ease and delectable, picture-perfect results. Some of us have noticed, though, that these TV chefs don't always adhere to the same safe food handling guidelines we've been taught to follow.

Cats give us so much—companionship, loyalty, love... and now the bird flu. Several weeks ago, a veterinarian from the Animal Care Centers of New York City's Manhattan shelter caught H7N2 from a sick cat. According to a press release from the NYC Health Department on December 22, "The illness was mild, short-lived, and has resolved." This isn't the first time cats have passed infections on to humans, but it is the first time they passed on the bird flu—avian flu H7N2, to be exact.

The internet was blowing up recently over this mind-blowing, mouth-watering video of a woman making a cake decoration out of… wait for it… chocolate bubble wrap. Yes, that's right: she turned the ubiquitous packing material into the mold for an absolutely gorgeous cake embellishment that, deservedly, went viral. You can watch the video below.

Throwing a party means making sure everyone has fun, but that pursuit can quickly get out-of-hand. Before you know it, you're once laid back get-together has received so many RSVPs that it becomes obvious you're throwing the party of the century. With an over-abundance of beer and an inflated guest list, your newly-formed epic reputation must live up to the hype.
Bad news, guys. The shelf life for liquor leftovers does not apply to your two-buck chuck. While an opened bottle of your favorite whiskey will stay respectable for ages thanks to its high ABV (which makes it inhospitable to outside elements), an opened bottle of merlot will sour quickly. However, it turns out that red and white wines have different life spans once they're opened—for reasons which we'll cover below.

If you're anything like me, you started down the Android-modding path for two distinct reasons; to run cutting-edge software and squeeze every bit of performance out of your hardware. Utilizing the new F2FS file system on your rooted Nexus 4 or 5 fulfills both of those desires at the same time.
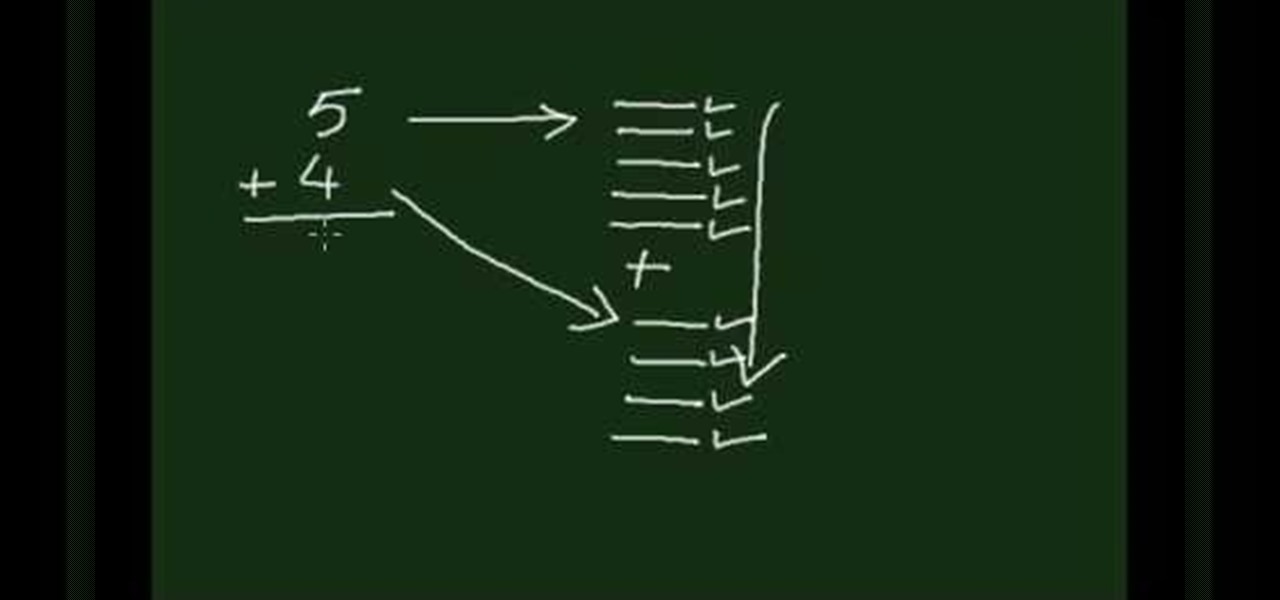
It may seem elementary to some, but there are still those (especially young children) who cannot add two numbers together. The easiest way to start out with addition is with the number line trick. This math video shows you the quick trick to learning simple addition problems. From here, things only get tougher.
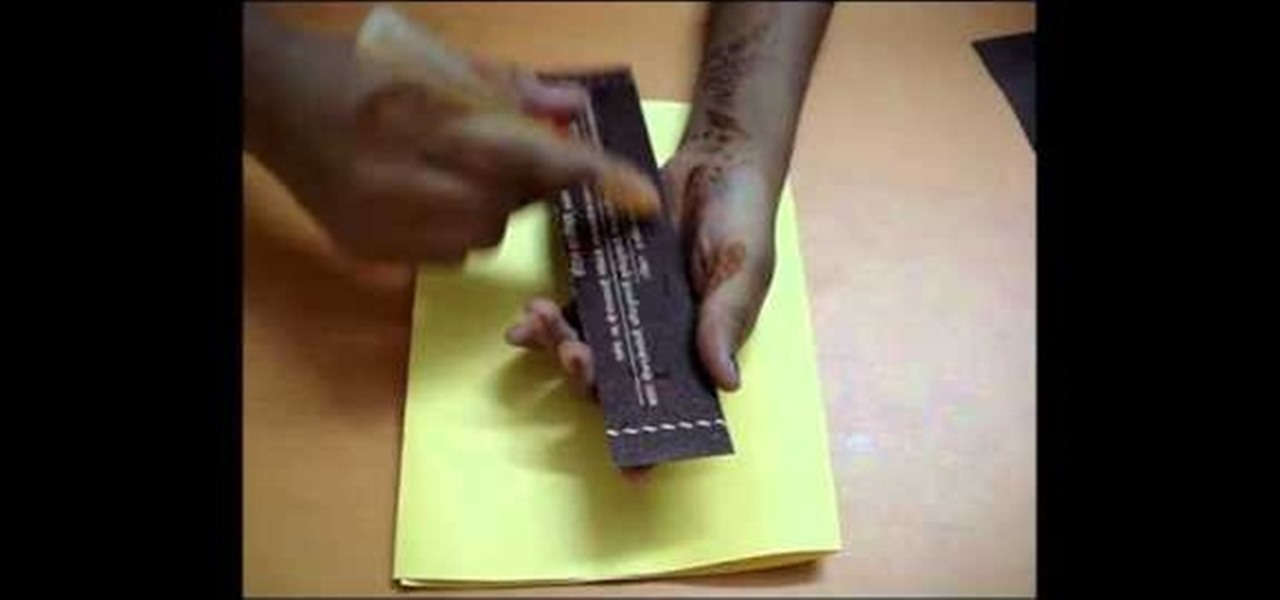
For this Diwali, try making your own homemade greeting card for family members and friends. You don't need much to make your own card for Diwali (aka Divali, Deepavali or the festival of lights). Even children can make DIY cards with some raw or unused materials. Diwali is a five-day festival, celebrated by Hindus, Sikhs and Jains, and usually occurs from mid-October to mid-November.

In a special Mother's Day installment of their weekly instructional series on Chinese painting, Blue Heron Art's Henry teaches us to paint Chinese Carnations in watercolor, with calligraphy highlights done in ink with a brush. His grace and accuracy with both the watercolor and the ink would be challenging for many of the less-artistically-inclined to emulate, but the finished product is beautiful and should impress all but the choosiest of moms if their child were to make / buy it for them.

Hairbows are adorable and can be expensive if you buy them often. In this two part tutorial, learn how to make cute little bows for you or your child. These bows are cheap and very fast to make. So, next time skip the store and get crafty!