Jeans are tricky, especially if you're not entirely sure what your inseam is? To get the proper fit jeans, you need to break out the measuring tape and finally figure out what size you should be. The first step to finding pants and jeans that fit perfectly is measuring your inseam.

It seems like people are always trying to lose weight..but what if you have the opposite problem? Whether you’re recovering from an illness, are a growing teen, or you are an athlete trying to bulk up, a little information can go a long way in helping you pack on a few extra pounds.

Just like any other skill, to be good at flirting you will have to practice. It's not as hard as it may seem once you know what to do. With just a couple of key flirting skills you will be able to make a great impression on anyone.

If you've ever had bloating you know this can be an uncomfortable and even painful situation. You can alleviate bloating by preventing gas or taking measures to try to reduce gas. Food, exercise and stress can all effect bloating.

Runde Auto Group demonstrates how to change a flat tire. First, open your vehicle's trunk and remove the spare tire, the jack and the tools. You may need to loosen a wing nut to remove the tire from the trunk. Consult your owner's manual for limitations when driving on the spare tire. Put the jack under your car and line it up with the lip. Jack up the car using the lug wrench as an extender to take a little bit of pressure off the tire. Then, loosen the lug nuts using the lug wrench. Jack up...

Is it time for your planned hiking adventure? Hiking is great, but mountain hiking, through the brush and rocks, is even better. Going for a hike in the mountains can be exhilarating, but it also has its dangers. Make sure you pack for the occasion.

Want to supply your head with a little extra jazz factor? Why not tie a scarf around it? You have only one head, but any number of ways to decorate it with a scarf.

Not everyone in Hollywood owes their nice complexion to a dermatologist. Here are some homespun beauty secrets you can steal.

You're never too old to join in the fun. A 99-year-old woman helped Bismarck, North Dakota, recapture a snow-angel-making world record. Learn how to make snow angels.

All sports require physical conditioning. Volleyball is no different. Learn how to do physical conditioning for volleyball in this video tutorial.

In this video series, learn how to dress different plus size body types. Our expert, Michele Varon, shows you the different types of plus size women. With her plus size models, you can see which body type you most closely resemble. Once you know, you can start to find flattering clothing for various occasions.

In this video series our expert will demonstrate how to use makeup applicators to apply makeup. There are dozens of products to help women apply makeup and achieve a beautiful look, but it is important to know how to properly use each one in order to get the desired result. This free beauty series will give step-by-step instructions on how to use a variety of makeup tools, including makeup sponges, brow brushes, mascara brushes, and angled makeup brushes.

Finding a bra that fits correctly and looks good can be tough. For years women have dealt with uncomfortable and ugly bras and lingerie, but in this video series, our expert will give you the information to find the perfect bra. She will give tips and advice on how to measure for a bra, how to find the right bra for different occasions, and even how to use bra enhancing accessories.

The team at NASA is in full mission preparation mode as they prepare to send a new team to the moon for the first time in decades via the Artemis program in 2024.

The enterprise-focused category of augmented reality doesn't often get the headlines due to its relatively sedate profile as a mostly factory floor and training-based tool.

If you consider yourself an emoji master, you'll have to retrain yourself once you install iOS 14.5 on your iPhone. Why? Because there are 217 new ones available to incorporate into your sometimes cryptic emoji messages.

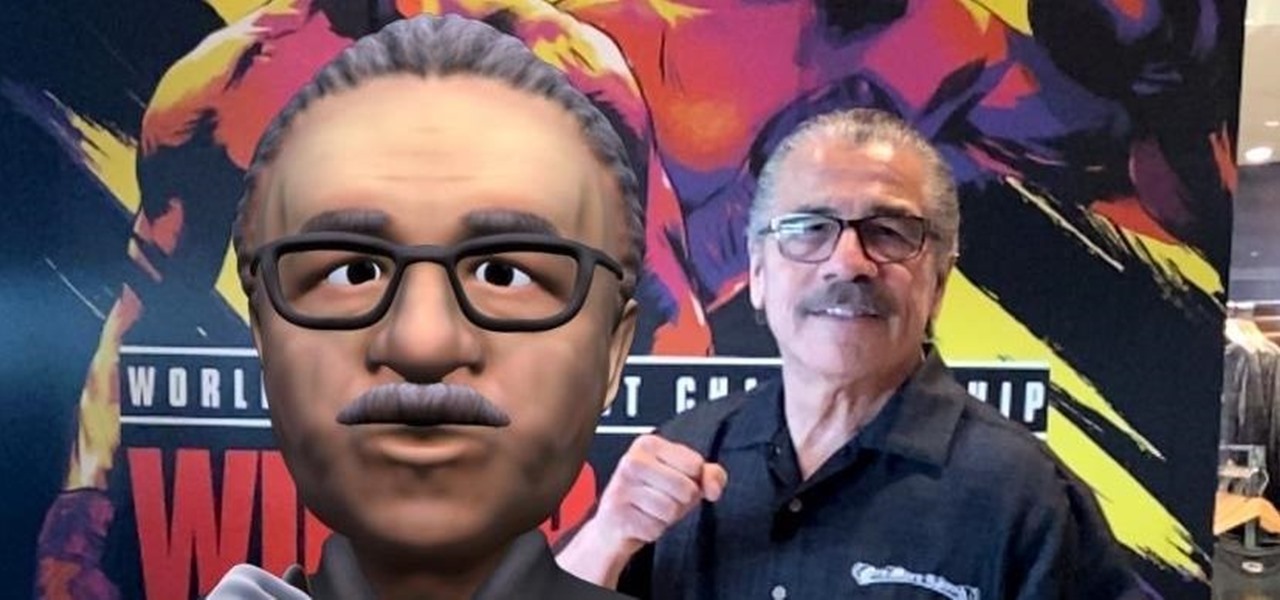
As augmented reality continues its collision course with mainstream adoption, the technology will now have a role in one of the most anticipated boxing matches of the year.

In the late nineteenth century, the advent of the motion picture wowed audiences with a new storytelling medium. Nearly a century and a half later, augmented reality is establishing a new frontier in film.

It's time to make some more room at the augmented reality cosmetics counter. This week, social media giant Pinterest unveiled "Try On," a virtual make-up visualization tool running on its Lens visual search tool.

The newly enhanced focus from Magic Leap on enterprise, announced on Tuesday, also came with a few companies opting to weigh in with their experiences developing for the platform.

The USB Rubber Ducky and the Digispark board both suffer from the same issue when attacking macOS computers: a keyboard profiler pop-up which tries to identify any non-Apple USB keyboards. While it's an annoying setback, the solution is a simple modification that allows Mac computers to be targeted, which affects the ability to target Windows and Linux devices.

Former soccer star and current celebrity David Beckham has the augmented reality abilities of Facebook and Instagram as allies in the effort to eradicate malaria from the world.

Emoji are, without a doubt, an integral part of messaging on smartphones. Whether you're team iPhone or Android, chances are you send emoji daily. However, years after their introduction, emoji remain static in most cases, even with animated stickers and GIFs supported on almost every major chat app. That said, one of those chat apps, Telegram, makes things more lively.

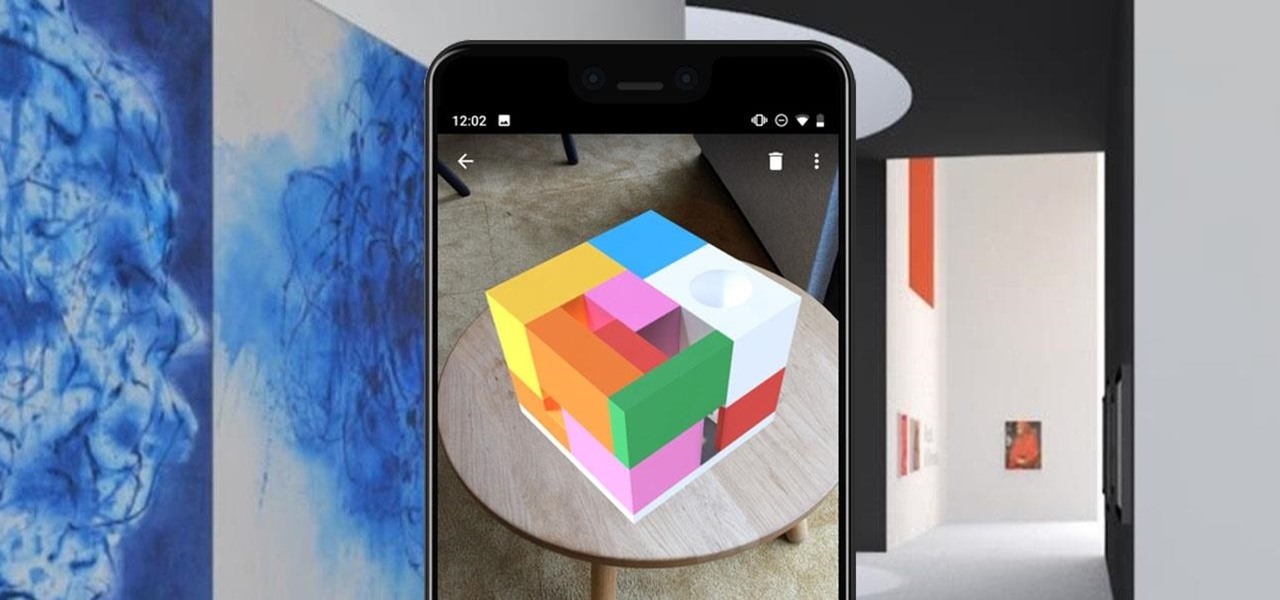
After debuting its virtual Pocket Gallery last year with the works of Johannes Vermeer, Google Arts & Culture has released a sequel that brings even more artists into your home via augmented reality.

Snapchat isn't the only tech company transforming landmarks with augmented reality for Pride Month. About four miles southwest of New York's iconic Flatiron Building, which is getting its own Pride makeover via Snapchat's Landmarker AR, Stonewall National Monument is also receiving some augmented reality treatment by way of the Stonewall Forever mobile app published by the Lesbian, Gay, Bisexual, and Transgender Community Center (better known as The Center) in partnership with Google.

MouseJack vulnerabilities were disclosed over three years ago. Some wireless keyboard manufacturers have since issued firmware updates, but millions (if not billions) of keyboards remain unpatched worldwide, either because they can't be updated or because the manufacturer never bothered to issue one.

In just a few weeks, on May 29, the annual AWE (Augmented World Expo) conference will take place once again in Silicon Valley (Santa Clara, California, to be exact).

Until very recently, Apple apps were among the only ones that would play nicely with Siri on iPhones. If you wanted to take advantage of the digital assistant to, say, compose an email, you would need to go with Apple Mail instead of the email client you actually use. As of iOS 12, this is no longer the case.

As penetration testers, we sometimes need to securely store customer data for prolonged periods. Bruteforce-resistant, vault-like containers can be created with just a few commands to protect ourselves from physical attacks and unintended data disclosures.

Gmail conversations, Facebook private messages, and personal photos can all be viewed by a hacker who has backdoor access to a target's Mac. By livestreaming the desktop or exfiltrating screenshots, this information can be used for blackmail and targeted social engineering attacks to further compromise the mark.

Most users don't realize how much valuable data is in their network traffic. With a few simple tools, an attacker can quickly pick out cookies, passwords, and DNS queries from a macOS device as it covertly streams the victim's network traffic to the attacker's system. Here, we will cover two methods for analyzing packets flowing from a Mac.

Command injection is a technique used by hackers to execute system commands on a server, usually via a web application or some kind of GUI. This can happen when an application provides some sort of functionality to the user involving the use of system commands. When the input is not properly sanitized, commands not originally intended to be run are allowed to be executed.

Passwords and data stored in web browsers are extremely valuable to hackers. If not for financial gain, black hat hackers may still leak your passwords and personal information for amusement. Never undervalue what you're worth to a hacker.

Apple released iOS 12 on Sept. 17, and most of the announced features have been released for the iPhone's latest available operating system. However, some brand new features can be accessed with Apple's latest beta, iOS 12.4. If you want to try out all its new features before everyone else, you can install the developer or public beta on your iPhone right now.

Google, Amazon, and Facebook are always listening. But what's worse? Hackers are listening, too. Windows PCs are particularly vulnerable, but with a few simple commands, a remote attacker can even take over the microphone on someone's Mac computer, streaming audio and listening to private conversations in real time without the victim's knowledge, abusing an overlooked security consideration.

While hackers have taken advantage of numerous vulnerabilities in Adobe's products to deliver payloads to Windows users via PDF files, a malicious PDF file can also wreak havoc on a Mac that's using the default Preview app. So think twice before double-clicking a PDF open on your MacBook — it might just be a Trojan with a rootkit inside.

A convincing domain name is critical to the success of any phishing attack. With a single Python script, it's possible to find hundreds of available phishing domains and even identify phishing websites deployed by other hackers for purposes such as stealing user credentials.

Using a keylogger to intercept keys pressed on an infected computer can circumvent encryption used by email and secure chat clients. The collected data can often reveal usernames, passwords, and potentially compromising and private information which hackers abuse for financial gain.

After setting up your phone, there are a number of things you should do immediately before download your favorite apps. Specifically, now that your data is on the device, you need to take steps now to ensure it's both protected and retained. Fortunately, most of these steps are a one-time process.

Identifying vulnerable devices and services on a target router can be difficult without leaving logs and other traces of an active attacker on the network. However, there is a way to covertly decrypt and view Wi-Fi activity without ever connecting to the wireless network.