
Insulin Injections Search Results


Hacker Hurdles: DEP & ASLR
This is the first installment in a new series that I am calling "Hacker Hurdles." These are things, methods, techniques that make our job as hackers more challenging and difficult. Don't misunderstand me, these items don't make our task impossible, but rather more challenging and, therefore, more gratifying when we are successful. One of the most important new hurdles for hackers is DEP and ASLR. Data Execution Prevention (DEP) and Address Space Layout Randomization (ASLR) are designed to pre...

How To: Hack Your Kindle Touch to Get It Ready for Homebrew Apps & More
Thanks to Yifan Lu, it's been discovered that the operating system running on the Kindle Touch is written mostly in HTML5 and JavaScript, unlike the previous models which used Java. This is exciting, because when a device is hacked or rooted, that means homebrew programs can be run on the device, maximizing its potential and getting the most for your money.

How To: Get rid of ugly scars
Scars can make you feel self conscious. Luckily, there are steps we can take to reduce their appearance without surgery. So, avoid the operating room and check out this video - its full of useful tips for hiding and eliminating your scars.

Hack Like a Pro: Metasploit for the Aspiring Hacker, Part 3 (Payloads)
Welcome back, my tenderfoot hackers! As you know, Metasploit is an exploitation framework that every hacker should be knowledgeable of and skilled at. It is one of my favorite hacking tools available.

How to Hack Wi-Fi: Choosing a Wireless Adapter for Hacking
Welcome back, my budding hackers. So many of you are interested in hacking Wi-Fi that I have decided to revisit my Wi-Fi Hacking series with some updated and more in-depth material. I strongly suggest that you look at some of my earlier posts, such as "Getting Started with Terms and Technologies" and "Getting Started with the Aircrack-ng Suite of Wi-Fi Hacking Tools," before continuing here. If you're ready, you can also check out our updated 2017 buying guide here.

Snack More, Fight Less: The Science Behind Being "Hangry" & How to Cure It
True story: a friend of mine regularly started a fight with her boyfriend everyday at 4 p.m. Every day. This went on for years until he finally got the bright idea of shoving a granola bar at her the minute she came home from work. Shazam! The fights were a thing of the past.

How To: Perform Directory Traversal & Extract Sensitive Information
With all the web applications out on the internet today, and especially the ones built and configured by novices, it's easy to find vulnerabilities. Some are more perilous than others, but the consequences of even the slightest breach can be tremendous in the hands of a skilled hacker. Directory traversal is a relatively simple attack but can be used to expose sensitive information on a server.

How to Hack Wi-Fi: Hunting Down & Cracking WEP Networks
While the security behind WEP networks was broken in 2005, modern tools have made cracking them incredibly simple. In densely populated areas, WEP networks can be found in surprising and important places to this day, and they can be cracked in a matter of minutes. We'll show you how a hacker would do so and explain why they should be careful to avoid hacking into a honeypot.

How To: Write an XSS Cookie Stealer in JavaScript to Steal Passwords
JavaScript is one of the most common languages used on the web. It can automate and animate website components, manage website content, and carry out many other useful functions from within a webpage. The scripting language also has many functions which can be used for malicious purposes, including stealing a user's cookies containing passwords and other information.

News: Change of Tune? Not Everyone Needs to Finish That Course of Antibiotics
After years of telling patients to finish any prescribed course of antibiotics completely, a group of researchers in the UK say it is no longer necessary, and could even be harmful if we want to preserve the antibiotics we can still use.
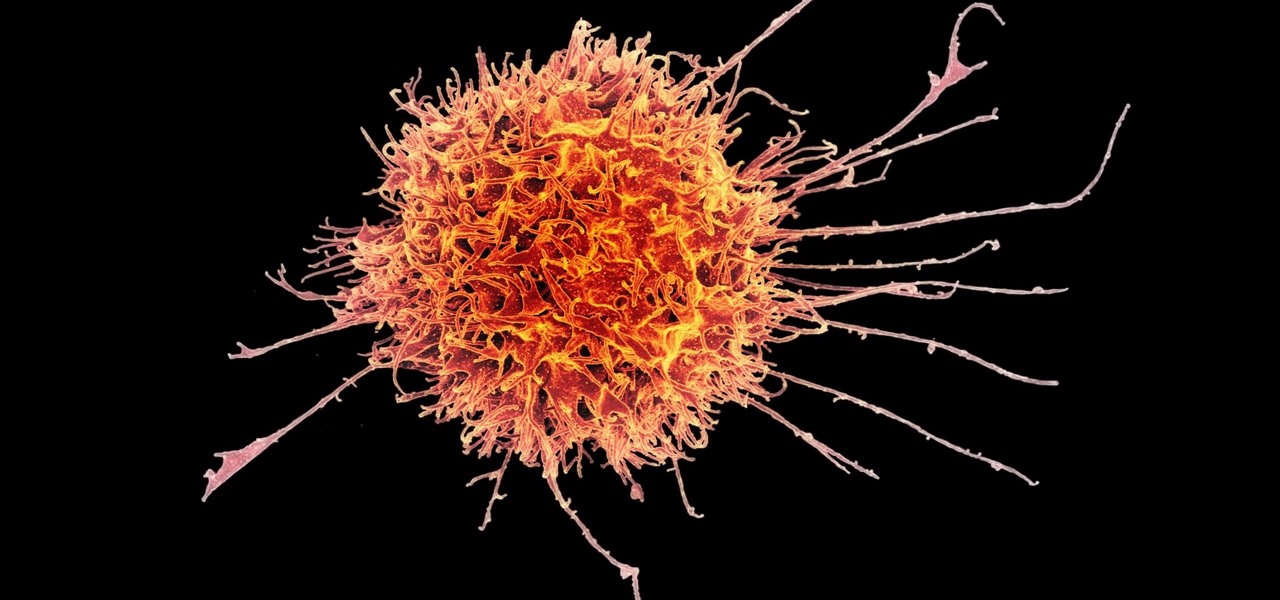
News: Artificial Viruses Provoke the Immune System to Fight Cancer
Cancer cells do a pretty good job of flying under the radar of our immune system. They don't raise the alarm bells signaling they are a foreign invader the way viruses do. That might be something scientists can change, though.

How To: Successfully Hack a Website in 2016!
Hello partners, first of all I would like to thank all those who have sent me positive feedback about my posts, to say that I'm always willing to learn and teach. I'm also open to answer the appropriate questions.

How to Hack Databases: Running CMD Commands from an Online MS SQL Server
Welcome back, my hacker novitiates! There are many ways to hack databases, and most of these techniques require SQL injection (SQLi), which is a way of sending SQL commands back to the database from a web form or other input. In this tutorial, we will use SQL injection to get access to the underlying server. So instead of getting access to the database and its data, we will use the database as an intermediary to gain access to the underlying server.

How To: Easily get rid of acne scars without surgery
One can easily get rid of acne scars without surgery by means of following steps. Identify the type of acne scars you have. See a dermatologist who can tell the difference between types of scars. For example, scars may be classified as ice pick, boxing, rolling or hypertrophy scars. Not every nonsurgical removal techniques will work with each type of scar. Get a chemical peel. A solution is applied to the skin which causes the top layer to peel off. This encourages new skin growth. Peels are ...

How To: Roast a pig Hawaiian style
This video shows how to throw a Hawaiian pig roast. Remember, the most important part is to drink while you prep the pig and build the fire. Just do not burn yourself or undercook it. The longer you leave it in the ground, the better it is.
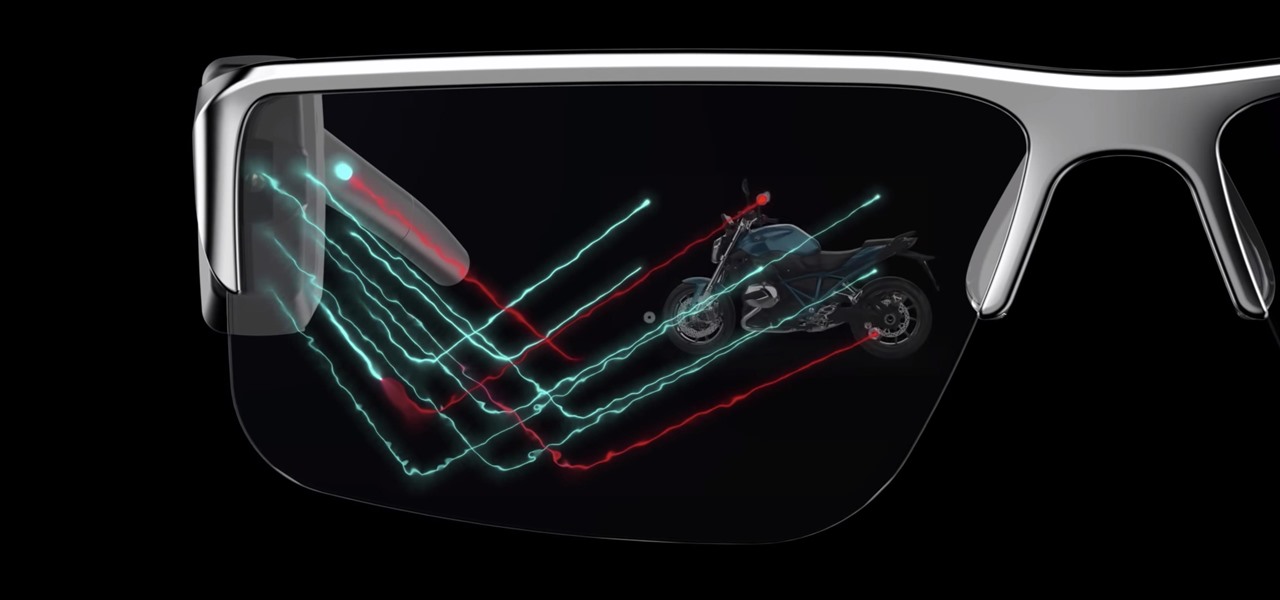
News: Samsung Joins Niantic in Backing DigiLens with $50 Million Funding Round
Smartglasses are the future of augmented reality, and Samsung is betting on waveguide maker DigiLens to emerge as a leader in the growing AR wearable industry.

News: Nickelodeon Reels in AR Mode for Popular Mobile Game Sky Whale
One of the most popular mobile games out there for kids has added an augmented reality mode that brings the titular character into the real world.

Video: How to Crack Weak Wi-Fi Passwords in Seconds with Airgeddon on Parrot OS
A weak password is one that is short, common, or easy to guess. Equally bad are secure but reused passwords that have been lost by negligent third-party companies like Equifax and Yahoo. Today, we will use Airgeddon, a wireless auditing framework, to show how anyone can crack bad passwords for WPA and WPA2 wireless networks in minutes or seconds with only a computer and network adapter.

Today's Top News: BMW Slashes Combustion Engine Costs by 1 Billion Euros in Auto Industry Shift to Driverless & EVs
The auto industry continues to shift into high gear to lay the groundwork for driverless cars with an electric vehicle (EV) emphasis.
How To: Use "SET", the Social-Engineer Toolkit
Welcome back my social engineers/hackarians! Today we'll be looking into a fantastic piece of software, The Social-Engineer Toolkit or just SET for short. SET is designed, Developed and used by several Social-engineers. So... Let's get started!

How To: Make the Deadliest Looking Redneck Pen Set Ever
Do you guys remember those things you hold with your fingers to write stuff down? I think they're called pens, or something like that...

How To: Coordinate your life with your menstrual cycle
Perform tasks when you’re at your best, hormonally speaking, by scheduling around your menstrual cycle.

How To: Get rid of stretch marks, scars and acne blemishes
This video will show you how to get rid of stretch mark scars and acne blemishes. Your treatment options depend on the type and severity of your scarring. One way to improve the appearance of a scar is through a collagen injection, given by your dermatologist. Corticosteroids can also be injected to a hypertrophic scar to flatten and soften the raised area. Another technique is laser treatment, which reduces redness and evens out the scar tissue. Skin surgery is used in severe cases to remove...
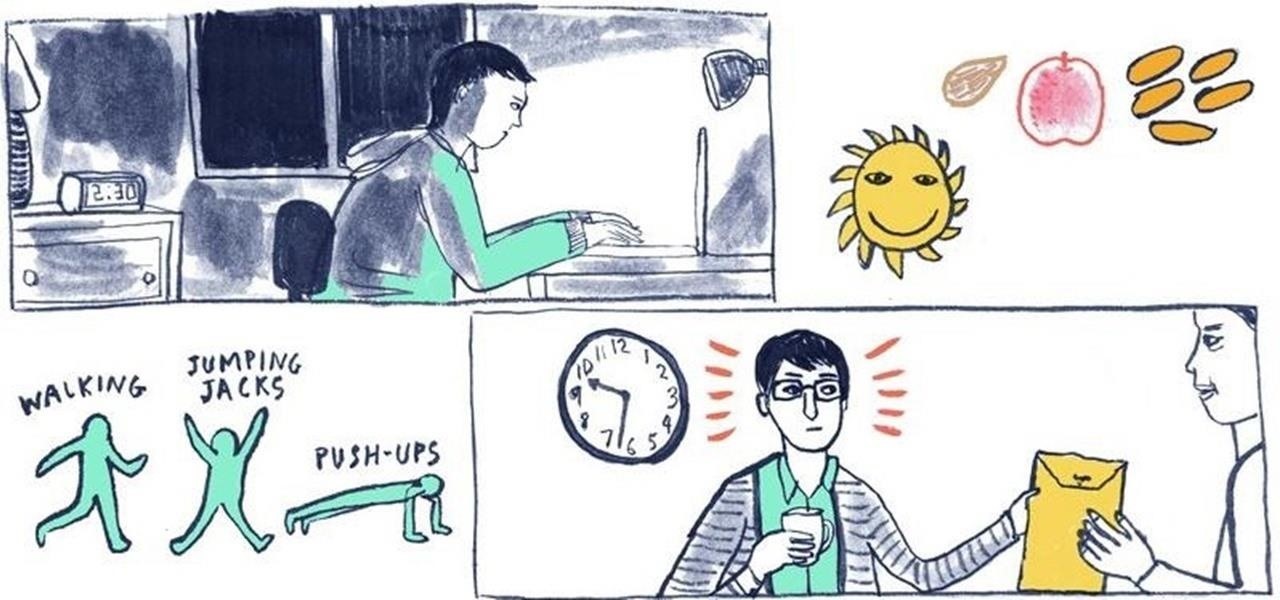
How To: 16 Tips for Staying Awake When You're Tired
While there's an art to surviving the all-nighter, there's also an art to staying awake throughout the day when you're operating on little to no sleep. In 1964, the record for sleep deprivation was set by 17-year-old Randy Gardner, who stayed awake for an incredible 264 hours and 12 minutes. Now while we're not out to challenge Randy for his title, we can certainly look to him for inspiration in beating back our own fatigue.

How To: Create Malicious QR Codes to Hack Phones & Other Scanners
QR codes are everywhere, from product packaging to airline boarding passes, making the scanners that read them a juicy target for hackers. Thanks to flaws in many of these proprietary scanning devices, it's possible to exploit common vulnerabilities using exploits packed into custom QR codes.

How To: Automate Hacking on the Raspberry Pi with the USB Rubber Ducky
While the USB Rubber Ducky is well known by hackers as a tool for quick in-person keystroke injection attacks, one of the original uses for it was automation. In this guide, I'll be going the latter, explaining how we can use it to automate Wi-Fi handshake harvesting on the Raspberry Pi without using a screen or any other input.

News: What to Expect from Null Byte in 2015
Welcome back, my greenhorn hackers, and happy New Year! Now that your heads have recovered from your New Year's Eve regaling, I'd like to grab your attention for just a moment to preview 2015 here at Null Byte. I hope you will add your comments as to what you would like to see, and I'll try to honor as many requests as I can.

How To: Inject Keystrokes into Logitech Keyboards with an nRF24LU1+ Transceiver
MouseJack vulnerabilities were disclosed over three years ago. Some wireless keyboard manufacturers have since issued firmware updates, but millions (if not billions) of keyboards remain unpatched worldwide, either because they can't be updated or because the manufacturer never bothered to issue one.

Android for Hackers: How to Backdoor Windows 10 Using an Android Phone & USB Rubber Ducky
With an inconspicuous Android phone and USB flash drive, an attacker can compromise a Windows 10 computer in less than 15 seconds. Once a root shell has been established, long-term persistence to the backdoor can be configured with just two simple commands — all while bypassing antivirus software and Windows Defender.

How To: Detect Vulnerabilities in a Web Application with Uniscan
With the number of web applications out there today, it comes as no surprise that there are just as many vulnerabilities waiting for hackers to discover. Finding those vulnerabilities can be a difficult task, but there are plenty of tools available to make the process easier. While it won't help find any zero-days, web scanners such as Uniscan will detect common vulnerabilities.

How To: Discover XSS Security Flaws by Fuzzing with Burp Suite, Wfuzz & XSStrike
Cross-site scripting is one of the most common vulnerabilities found on the web today, with repercussions of this type of flaw ranging from harmless defacement to sensitive data exposure. Probing for XSS can be tedious and time-consuming for an attacker, but luckily there are tools available to make things a little easier, including Burp Suite, Wfuzz, and XSStrike.

How To: Exploit Shellshock on a Web Server Using Metasploit
One of the most critical bugs to come out in the last five years was Shellshock, a vulnerability which allows attackers to execute arbitrary code via the Unix Bash shell remotely. This vulnerability has been around for a while now, but due to the ubiquity of Unix machines connected to the web, Shellshock is still a very real threat, especially for unpatched systems.

Advanced Phishing: How to Inject Meetings into Anyone's Google Calendar
Google Calendar is a cornerstone of the Google Suite, perhaps second only to Gmail itself. Whereas email is constantly plagued by phishing attacks, as of yet, the calendar is a relatively untapped social engineering attack vector. But it's relatively easy for an attacker to inject a meeting or event into a target's Google Calendar and use it to exploit them.

How To: Modify the USB Rubber Ducky with Custom Firmware
The USB Rubber Ducky comes with two software components, the payload script to be deployed and the firmware which controls how the Ducky behaves and what kind of device it pretends to be. This firmware can be reflashed to allow for custom Ducky behaviors, such as mounting USB mass storage to copy files from any system the Duck is plugged into.

How To: Set Up Kali Linux on the New $10 Raspberry Pi Zero W
In five short years, three generations of ultra-low-cost Raspberry Pi devices have challenged the boundaries of what a person can do with a $35 computer — especially with Kali Linux.

News: How Diet, Gut Bacteria & Time Work Together to Form Your Potbelly
Potbellies don't have to happen as we age, according to two studies done on twins published online in the International Journal of Obesity.

News: Research Published in mBio Shows How Gut Bacteria Can Help Chubby Dogs Live a Better—& Longer—Life
As fun as it is to see Fido's face light up when you feed him table scraps, American dogs are getting fat. The good news is that research is homing in on nutritional strategies to boost canine capabilities to maintain a healthy weight.

How To: The Art of 0-Day Vulnerabilities, Part3: Command Injection and CSRF Vulnerabilities
INTRODUCTION Hello dear null_byters here we go again with our third part of this serie.

Hack Like a Pro: How to Hack Web Apps, Part 3 (Web-Based Authentication)
Welcome back, my novice hackers! In this third installment of my Hacking Web Apps series, we will look at the authentication of web applications. Remember, there are many ways to hack web applications (as I pointed out in my first article), and cracking authentication is just one method.

