Remember those old vinyl records? Remember jumping on the 8-track bandwagon? Switching over to cassette tapes? How much money you spent converting your music collection to compact discs? To MP3s?

Got video files on your computer? Watch them on your big-screen TV – using your Xbox! You Will Need

Smartphones are inherently bad for privacy. You've basically got a tracking device in your pocket, pinging off cell towers and locking onto GPS satellites. All the while, tracking cookies, advertising IDs, and usage stats follow you around the internet.

While you might suspect your MacOS computer has been infected with malware, it can be difficult to know for sure. One way to spot malicious programs is to look for suspicious behavior — like programs listening in on our keyboard input or launching themselves every time we boot. Thanks to free MacOS tools called ReiKey and KnockKnock, we can detect suspicious programs to discover keyloggers and other persistent malware lurking on our system.

Phone numbers often contain clues to the owner's identity and can bring up a lot of data during an OSINT investigation. Starting with a phone number, we can search through a large number of online databases with only a few clicks to discover information about a phone number. It can include the carrier, the owner's name and address, and even connected online accounts.

With all the web applications out on the internet today, and especially the ones built and configured by novices, it's easy to find vulnerabilities. Some are more perilous than others, but the consequences of even the slightest breach can be tremendous in the hands of a skilled hacker. Directory traversal is a relatively simple attack but can be used to expose sensitive information on a server.

The internet is constantly under siege by bots searching for vulnerabilities to attack and exploit. While conventional wisdom is to prevent these attacks, there are ways to deliberately lure hackers into a trap in order to spy on them, study their behavior, and capture samples of malware. In this tutorial, we'll be creating a Cowrie honeypot, an alluring target to attract and trap hackers.

Every Friday, Next Reality reviews the latest headlines from the financial side of augmented and mixed reality. This Market Reality column covers funding announcements, mergers and acquisitions, market analysis, and the like. This week's column is led by two companies cashing in on visual inputs.

to stay secure, you dont just need Tor, and a VPN. You need good browsing habits. What are Browsing Habits You Ask?

Not many people use their phone exclusively for making calls or sending messages today. If you're an Android user, the chances are high that you're using your phone or tablet for work-related activities. However, the basic set of apps and services your device was shipped with won't satisfy most users. The good thing is that Google Play Store has a nice selection of productivity apps for every task. Below you'll find a list of apps that will help you gradually optimize and organize your digita...

Welcome back, my greenhorn hackers! Throughout this series on Metasploit, and in most of my hacking tutorials here on Null Byte that use Metasploit (there are many; type "metasploit" into the search bar and you will find dozens), I have focused primarily on just two types of modules: exploits and payloads. Remember, Metasploit has six types of modules:

Downloading YouTube videos for offline use to watch later has always been a problematic endeavor. Dedicated third-party apps don't last long in the App Store, web-based converters aren't very functional on mobile, and rogue apps outside the App Store are tricky to sideload and open up the possibility of vulnerabilities. But that doesn't mean you still don't have a few good options.

These days, that pocket-sized computer we call a smartphone is home to your entire digital life. But with the onset of mobile payments and online banking, the line between your virtual world and the physical realm is becoming increasingly blurred.

I'm sure that many of us have heard of that nasty Shellshock vulnerability, but not very many people know how to exploit it. Try these few tricks on vulnerable websites!
Hello and welcome to my article. I have made this article for anyone who wants to become a hacker, and wants to know how to get started.

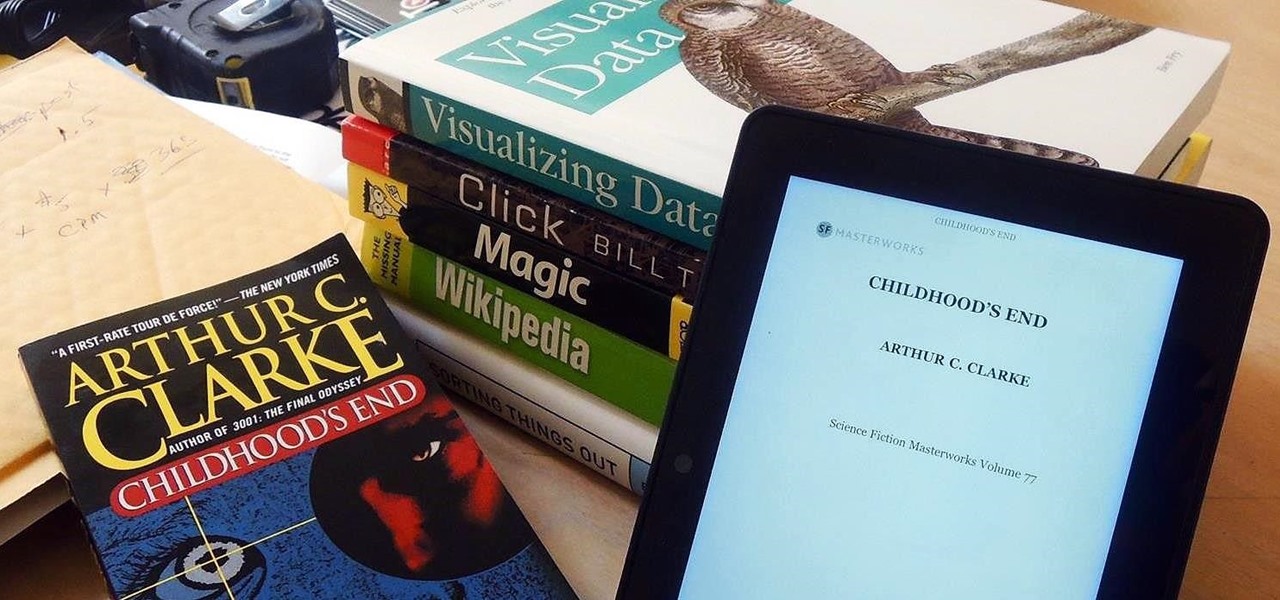
Loaded with a gorgeous display and a powerful processor, the Kindle Fire HDX is an impressive all-around tablet, especially when it's used for what Amazon Kindles were built for—reading electronic versions of novels, textbooks, and other printed works.

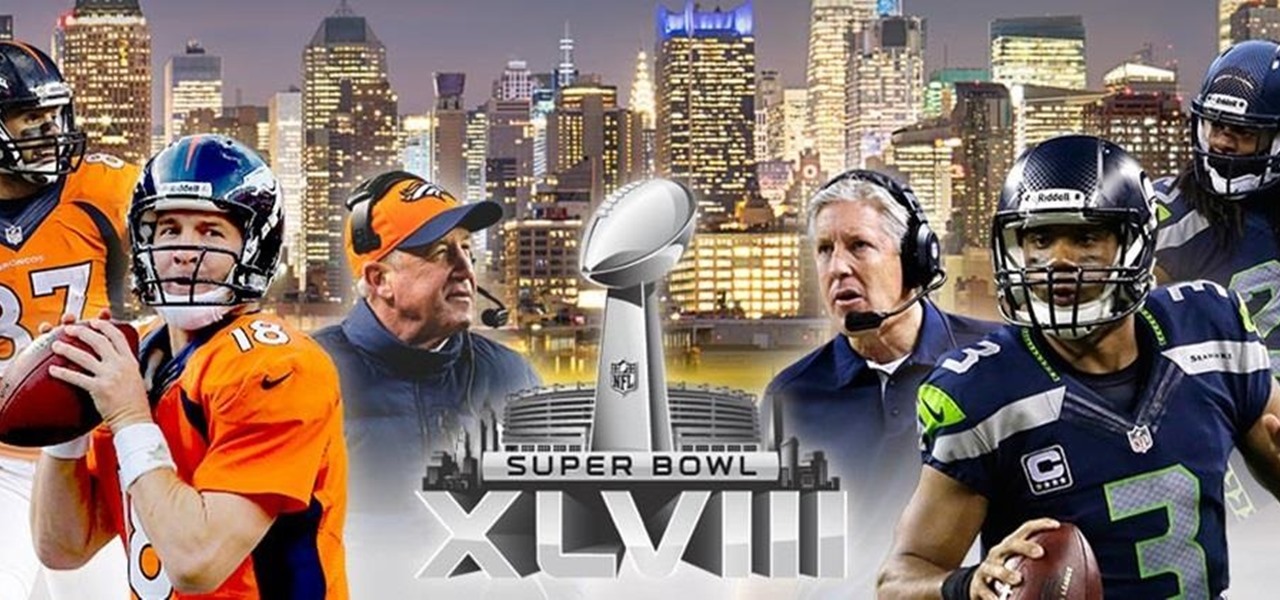
The mother of all games is almost here. Super Bowl XLVIII pits the Seattle Seahawks (or Seachickens, if you're from the Bay Area) against the Denver Broncos and regent exemplar of neck surgeries, Peyton Manning.

In order to bypass Megavideo and Veoh's viewing time limits you will first need Mozilla Firefox. To download Mozilla Firefox then go to Firefox and download the Mozilla Firefox browser. After downloading the browser you will need to install the add-ons. Go to the website Illumitux add-on in order to download the add on Illimitux, after downloading the add on then Mozilla will prompt you to close the browser window. Go ahead and close the window then re-open it. When you re-open it Mozilla wil...

If you're new to DreamCoder for Oracle, one of the very first features with which you'll want to acquaint yourself is the data table browser, which will permit you to display entries in a given Oracle database. For a detailed walkthrough of this feature, take a look at this video tutorial.

Got ballet tickets? Learn to appreciate and enjoy the performance with these steps. You Will Need

Low battery – two words you never want to hear. Banish them with these tips. You Will Need

Turn your possessions into cash and become an online selling machine. You will need: Something to sell, a computer with internet access, an eBay account, a digital camera, shipping supplies, something to sell,a computer with internet access, an eBay account, a digital camera, & shipping supplies.

1. First of all you need go to the 'view' button at the top bar menu. From the drop down click on 'view options'. Then click a 'check mark' against the 'kind' and then click 'ok'.

In this Computers & Programming video tutorial you will learn how to make a favicon for your site in Photoshop CS3. A favicon is a little symbol that shows up on url bars and also on browser tabs. Open a new project in Photoshop by pressing ctrl+N. Select height and width to 64 pixels and click OK. Now open the title tool and type in whatever you want. In the video, it is ‘F’. Open the background layer and do a color overlay of black. Now change the color of the title to white so that it ...

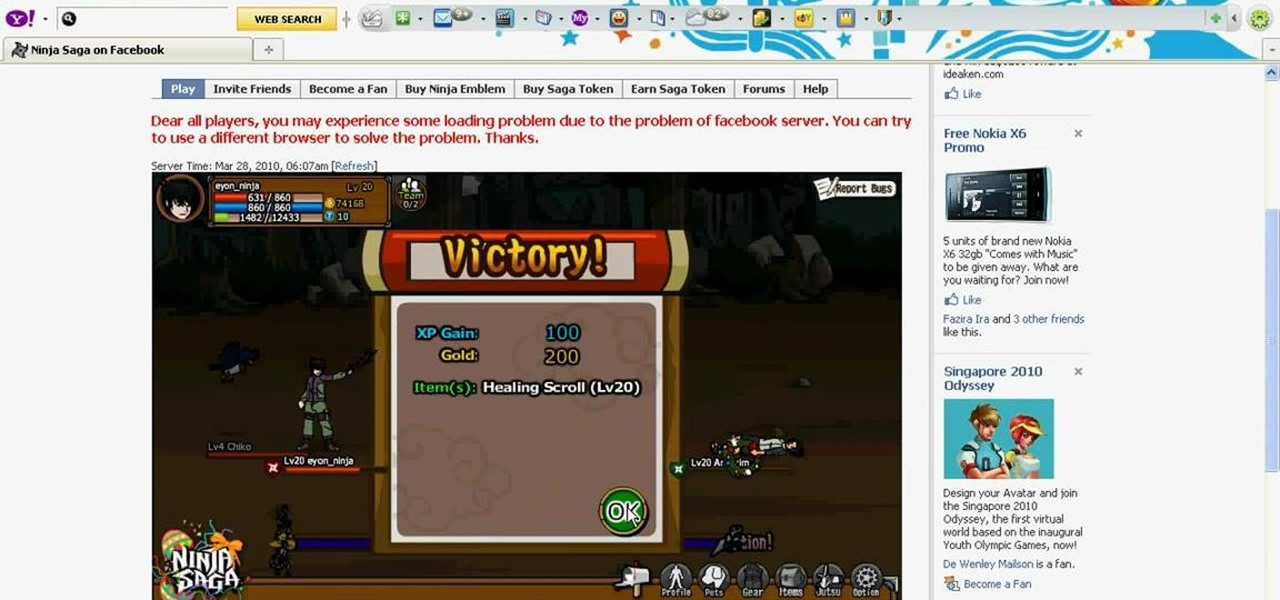
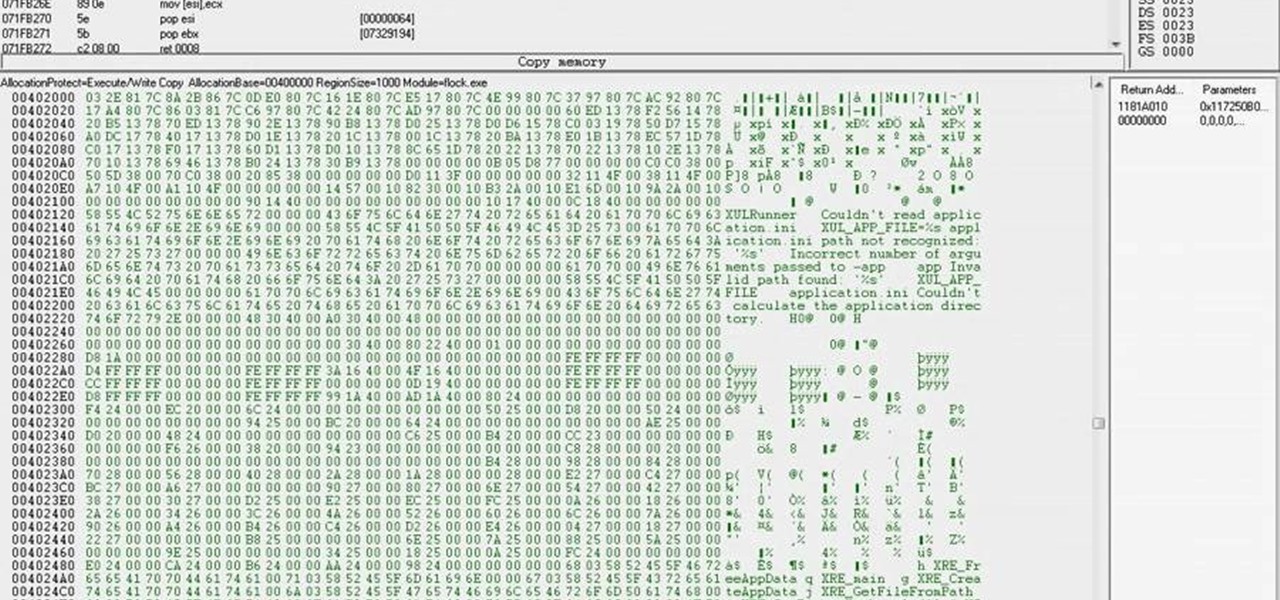
Want to vanquish even the toughest of foes with the greatest of ease? This hacker's how-to demonstrates a method for killing your Ninja Saga enemies with a single hit.

Dispatch your enemies with a single sword strike. This cheater's guide will show you how to smite even the toughest of opponents with a single hit (and a few keystrokes in Cheat Engine 5.5).

This is a Computers & Programming video tutorial where you will learn how to change your NAT to OPEN with a Linksys router. Go to your browser and type in 192. 168. 1. 1 and that will take you to the basic set up. The authentication dialog box comes up. Type in ‘admin’ for the username as well as the password. These are default settings. In the Linksys page, go to ‘applications and gaming’ and on the Port Range page fed in these information. Your application you can name anything. Start 80, E...

The video explains how to hack the game Agony: The portal. First he clicked the start game and created new character by entering the name as test dummy and set the difficulty level as normal. The he clicked the start campaign. While entering the game he skipped the tutorial and directly he went into the game.

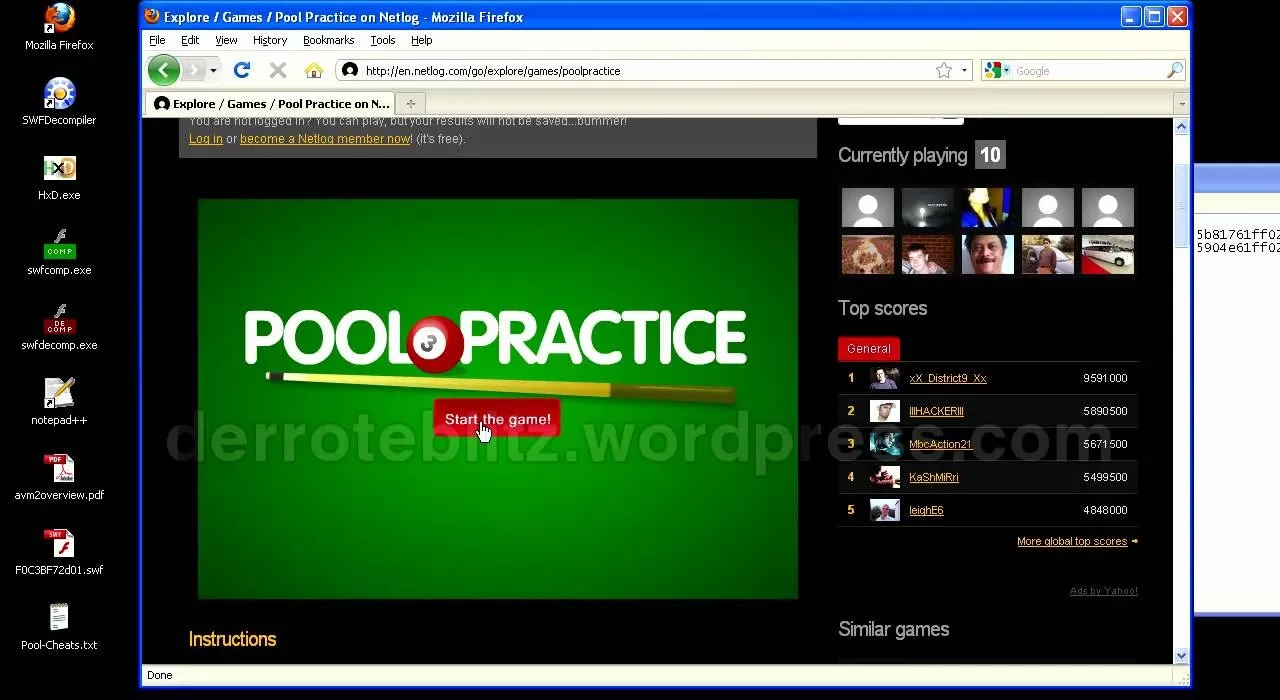
You want to know how to get extreme scores in the flash game Pool Practice? This is how. Watch this video tutorial to learn how to cheat in the flash game Pool Practice (01/01/10).

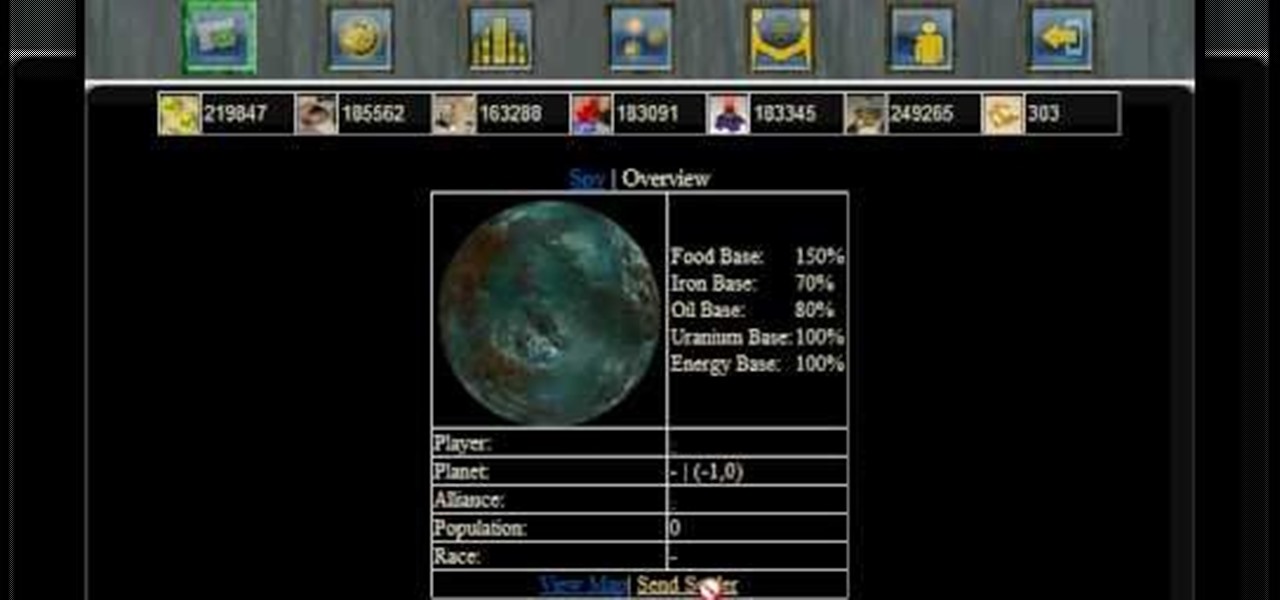
Settling a new planet will decrease your pride ratio, because your population will increase when you're settling a new planet. If you're not sure how to even settle planets...

In order to spy and gain intelligence on your Conrohl enemies, you need to make an intelligence agency. Then you recruit your spies to perform simple espionage.

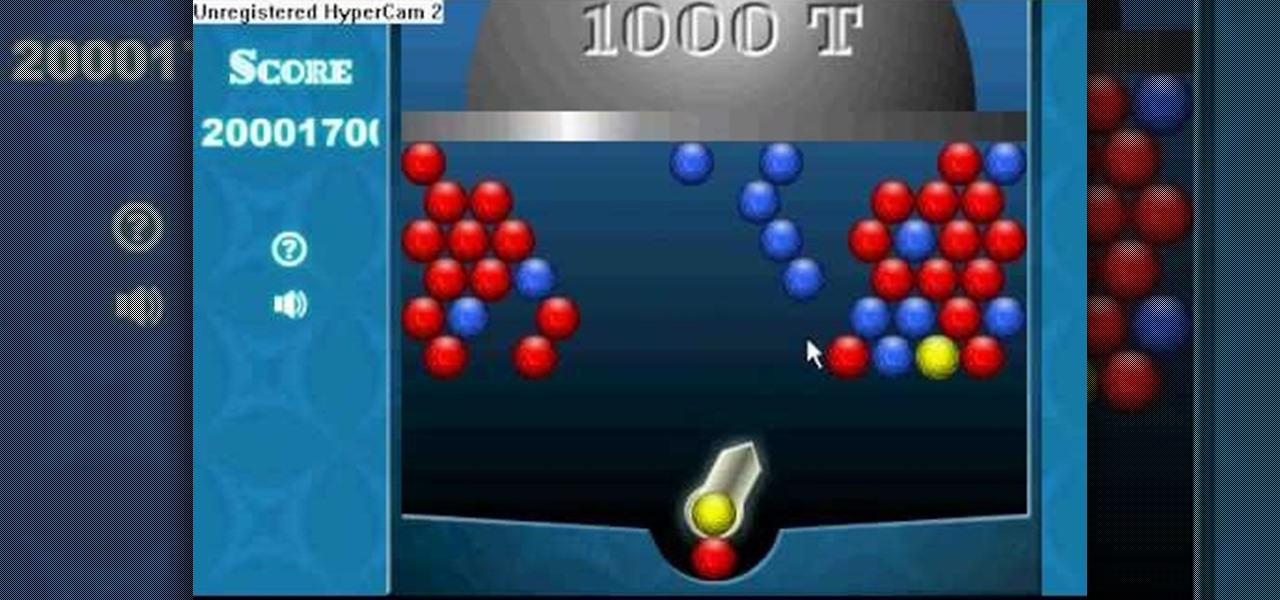
Flash games are addicting, especially Bouncing Balls. But can you actually beat all of those high scores you see? Probably not, but you can if you use Cheat Engine.

Systm is the Do It Yourself show designed for the common geek who wants to quickly and easily learn how to dive into the latest and hottest tech projects. We will help you avoid pitfalls and get your project up and running fast.

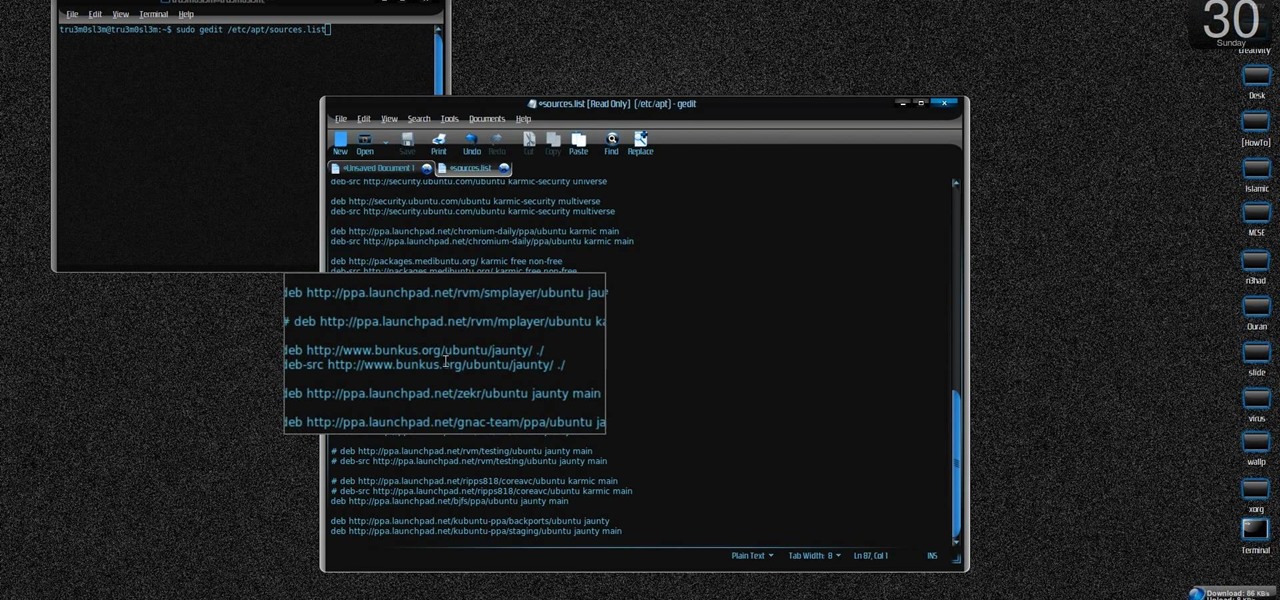
New to Ubuntu Linux? This computer operating system could be a bit tricky for beginners, but fret not, help is here. Check out this video tutorial on how to install KDE 4.3 Plasma on [k] Ubuntu Linux.

This is a great solution if you need to get something off your computer, but you are not home. Want access to your files stored at home? How about hosting a home web server? Static IPs are expensive, if you can even get one. We set up Dynamic DNS instead!

Mike Biggly shows us how to set up our home internet and networks. Part 1 of 20 - How to Set up your home internet and network.

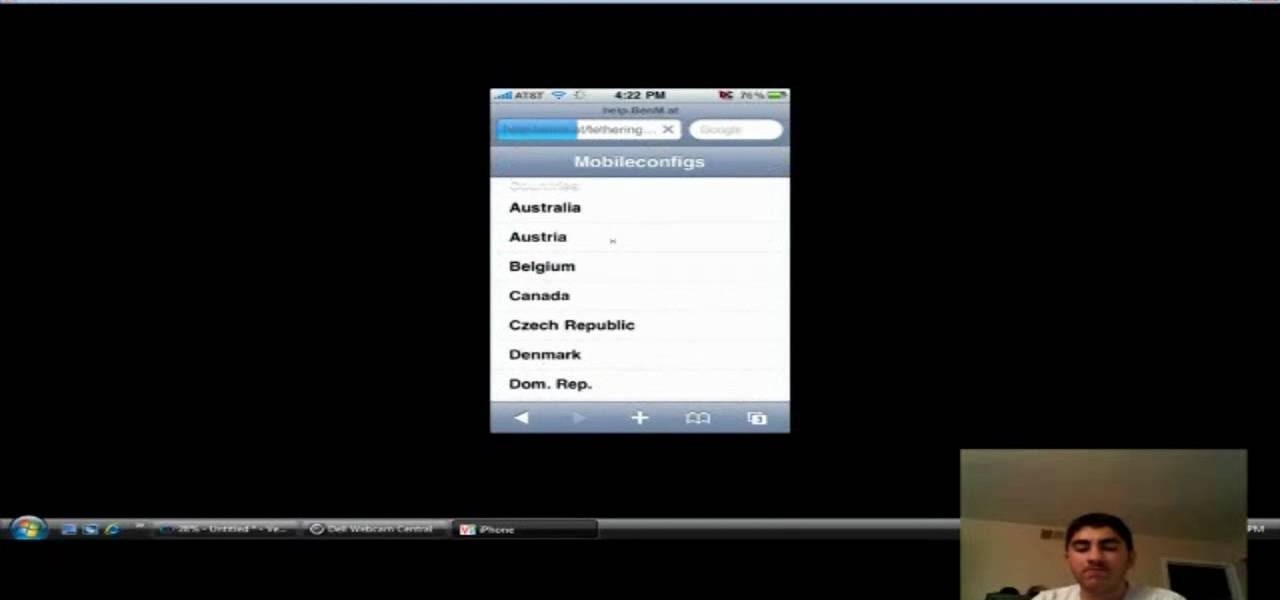
This video shows you how to enable internet tethering on your iPhone 3GS. What are the perks to internet tethering? Well, for starters, it allows you to log into the internet from just about anywhere by sharing your laptop's internet connection. This will also allow for faster browsing speeds if you don't have the fastest cell service at the time.

This weekend, hackers broke into the servers of the popular shoe shopping site Zappos, giving them access to the personal information of 24 million Zappos customers. The user data taken included names, email addresses, billing and shipping addresses, phone numbers, the last four digits of credit card numbers, and encrypted passwords. However, full credit card data was not lifted, and passwords were cryptographically scrambled.

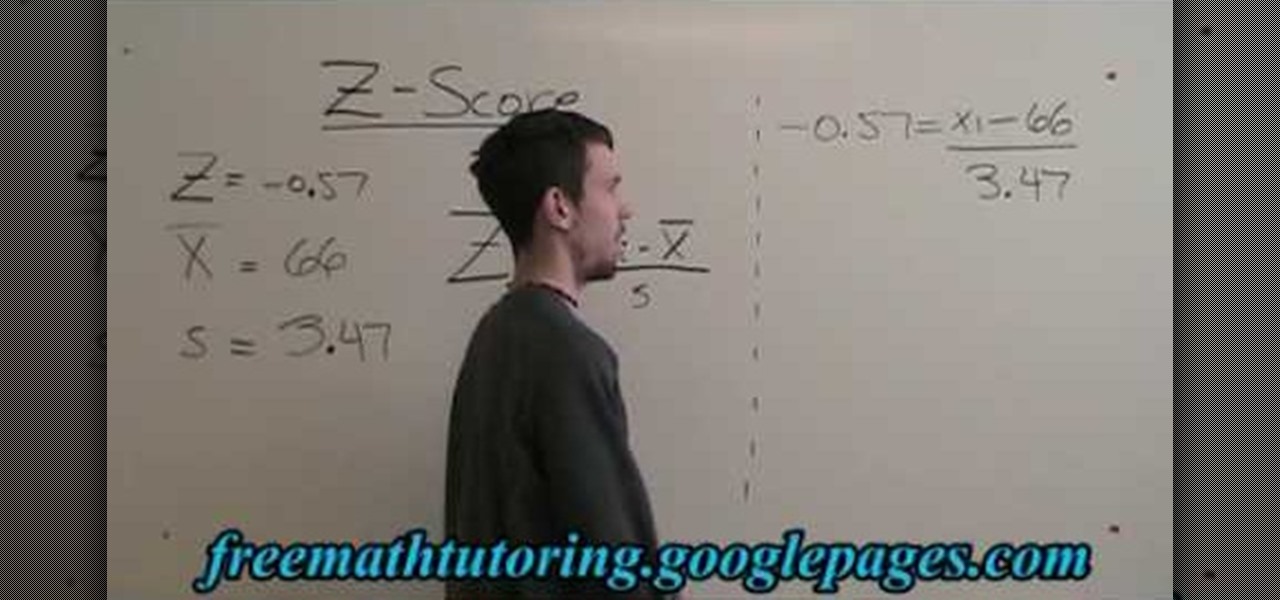
In this free video math tutorial, we learn how to use the Z-Score formula to find a data point (Xi) in statistics. With mathematics, as with anything else, not everyone progresses at the same rate. Stats is no exception. Happily, in the age of Internet video tutorials, this isn't a problem. Those who progress quickly can go beyond what's being taught them and those who are struggling likewise have all the time in the world to catch up. Whether you need help finishing your homework or studying...

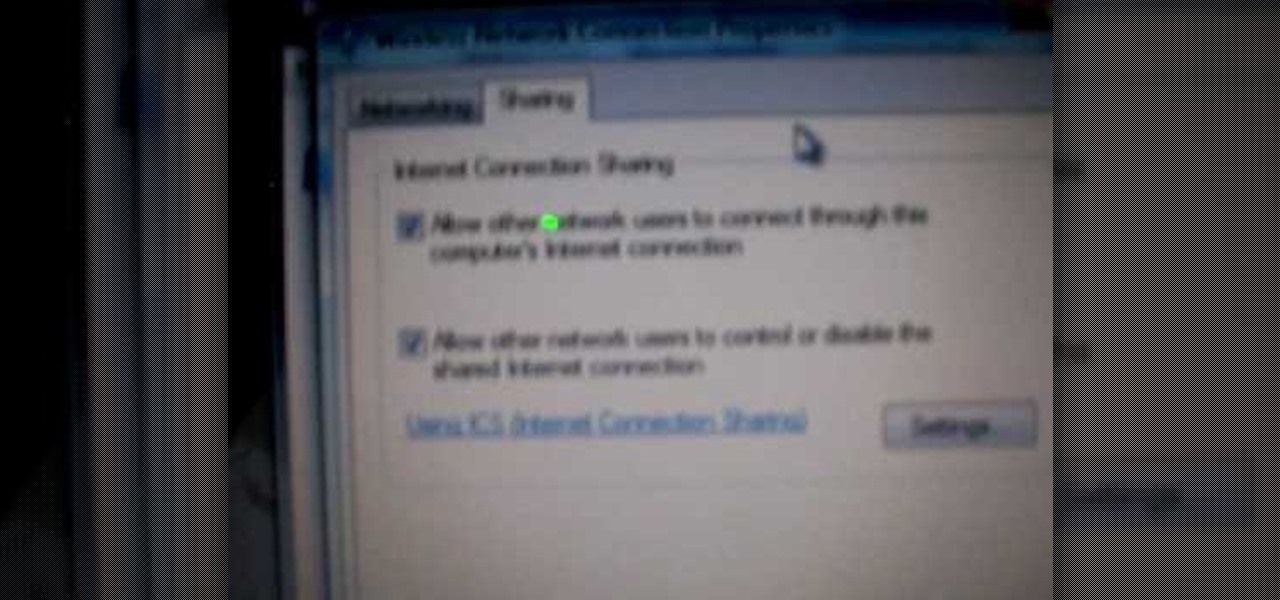
If you want to connect your XBOX to your ISP's Wi-Fi network, there is a simple way to do it.