Everything is documented these days, thanks to the Internet and mobile devices. Most people who own a smartphone use it to take lots of pictures. If you're one of those people, an app called Scoopshot can help you turn some of those photos into extra cash. Scoopshots lets you post your pics so that news organizations can pay you to use them. Companies can also post tasks, so if someone is looking for a particular photo in your area, you can accept the task, go take the photo, and earn money f...

Drinking games just got a little more sophisticated (kind of). Startup SmartThings built this awesome Arduino-based machine that automatically pours a shot whenever the US wins a medal in the 2012 Summer Olympics. Goldschläger for gold, Cuervo for silver, and Jack Daniels for bronze.

Are you getting that nasty "Application access set to not allowed" error on your Nokia 5300 cell phone? Unfortunately, it's a problem for most Nokia 5300 owners, ones who wish to use 3rd party applications on certain carriers, like T-Mobile, who restricts the uses for branding.

Want to be the John (or Jane) D. Rockefeller of Restaurant City? Watch this video tutorial to learn how to hack Restaurant City with Cheat Engine 5.5 (02/04/10).

Cashcroppimp teaches you how to open your XBox 360's NAT with Verizon Fios. You first have to find your IP address. For this, you simply point your internet browser to http://findmyip.com to find IP. This is also calling the default gateway. Make sure to write this down somewhere. Now you need to input this number in your internet browser. Enter your username and password and proceed to the next step. Now go to Firewall settings-DMZ Host. Here you will need the IP address from the XBox 360, w...

Learn a little bit about technology with help from EMBARQ. Watch this how-to video tutorial on testing your phone line (NID) if you have no dial tone. If there is no dial tone on your home lines, just test your NID (Network Interface Device) on your house to see what's going on. This is an important step to getting your High-Speed Internet up and running.

How to Use Your Mac as a Server: Turn your Mac Mini into a server! Yes, that's right, with a little know-how and a little spunk, you can turn an inexpensive Mac Mini computer into a server to provide services over you network. You won't even need the Mac OS X Server, just the Mac OS X Client, so there is no extra software to buy, just the Mac Mini and it's operating system.

Don't let Bejeweled Blitz get the best of you. Show it who's boss and get the highest score possible. Of course, you'll need Cheat Engine to overpower the game, so make sure you have Cheat Engine 5.5 or higher and check out this video for the hacking Bejeweled Blitz (10/09/10).

Tired of grandpa's baseball card collection rotting away in your attic? Well, unlike his pop bottle collection, baseball cards could yield a decent amount of income for you, if you know how to sell them. There are different outlets available for selling an individual baseball card or card collection. Know how to sell the fruits of your hobby and avoid getting ripped off.

Learn how to follow proper netiquette rules. You may be a model of decorum in person, but a bonehead online. Check out how much you know about Internet manners.

In general, hacking and information security is not just one discipline, but a number of them, and today we will look into some of the networking concepts.

Connecting your Nokia N900 smartphone to a wireless hotspot or your home wifi network is just a few quick taps away! Take a look at this tech support video from Nokia that will tell you exactly where to find the available internet connections on the phone and select the one you wish to connect to.

Want to give yourself extra points or resources in the online game Wild Ones? All your friends will be asking you how you passed them up so quickly! Make sure you have the most recent version of Cheat Engine downloaded, first!

If you're trying to use Cheat Engine to cheat for more money on Ninja Saga and keep getting an error message, this tutorial shows you a remedy. Make sure that you're playing Ninja Saga in either Firefox or Internet Explorer.

After playing Minecraft for a while, the old skins and textures can start to get old. But thanks to the internet, there's a LARGE community creating skins and textures that you can put right into the game! If you're wondering how to do this, this video will get you quick tutorial on how to quickly copy and paste your textures and skins right into the right folder and use them right away!

Making anonymous prank calls got a little difficult for a while there in the early 2000's. Not anymore though! Between Skype and PrankDialer there are very few people that you can't prank call anymore without having to worry about them finding you. This video will show you how to use Prank Dialer to make prerecorded prank calls to whomever you want for free. Good times.

Assuming you have already downloaded your desired theme off of the internet, this video will show you how to load it onto your PSP. Having custom themes on your PSP makes for a more spiffy design. It allows you to break free from the default ones loaded by Microsoft. Theming your Playstation Portable is fast, easy, and requires access to a computer.

This one's for all you cheaters! Those who enjoy getting free money in flash games will certainly enjoy this video.

This is a video guide to wireless broadband from Top10.co.uk. Learn about wireless broadband in this interesting video. This "how-to" guide for wireless broadband explains the basics of what wireless broadband is, how and where it works and who offers it, not to mention how to set up a home Wi-Fi connection in minutes using a wireless router. Follow the steps in this guide and go wireless today.

This video explains how to speed up Opera to browse the Internet at fast speeds.

A quick guide on using the wonderful internet tool StumbleUpon - a great way to find new and interesting websites.

We all know that using a VPN not only has a ton of benefits but is essential in our digital age. But did you know that you can get access to your own industry-leading VPN for life with one one-time payment? Even better, we've found an amazing deal on one right now: for a limited time, a YoData VPN: Lifetime Subscription is on sale for just $17.99. That's 69% off the regular price of $59.

If you're living or staying out in the middle of nowhere or a rural area outside of a big city or town — where there are no reliable cable, fiber, or wireless networks available — how can you get an internet connection? There are several possibilities, but they all come with tradeoffs, which we'll go over in detail.

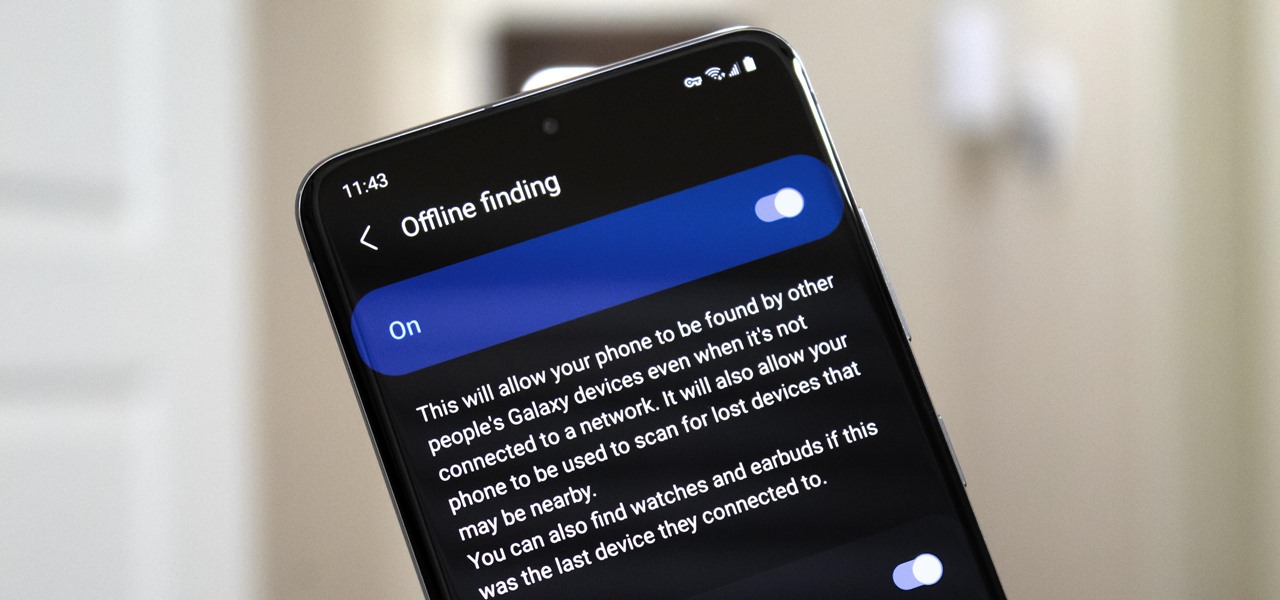
Nowadays, even the dumbest thieves know that the first thing you should do after you steal a phone is turn on airplane mode. Not only does this make it harder for police to track the phone through cell tower triangulation, but it also disables security features the person you stole it from may have implemented — for instance, Samsung's Find My Mobile service.

The Pi-hole project is a popular DNS-level ad blocker, but it can be much more than that. Its DNS-level filtering can also be used as a firewall of sorts to prevent malicious websites from resolving, as well as to keep privacy-killing trackers such as Google Analytics from ever loading in the browser. Let's take a look at setting a Pi-hole up and customizing a blacklist to suit your needs.

Imagine being able to play a video instantly on hundreds of thousands of devices across the globe. It's totally possible, as long as all of those devices have a Chromecast plugged in. When Chromecasts are left exposed to the internet, hackers can use add them to a botnet that can play YouTube videos at will. The "attack" is made even easier thanks to a simple Python program called CrashCast.

Your social security number, credit card information, and medical history can fall into the wrong hands if you're not careful about how and where you share your data online. If you really care about your data, there are tools and techniques you can utilize to protect yourself from cyberstalkers, advertisers, and hackers in a time when digital lives are a high commodity.

A relay is an electrical component that works like a light switch, where it's turned on or off with an electrical signal. By connecting a relay to a Wi-Fi connected microcontroller like an ESP8266, you can build a connected switch that can be controlled from the web browser of any device connected to the same Wi-Fi network — all for just a couple of dollars.

While there are a variety of privacy-focused search engines available like StartPage and DuckDuckGo, nothing can offer the complete trust offered by creating one's own search engine. For complete trust and security, Searx can be used as free metasearch engine which can be hosted locally and index results from over 70 different search engines.

Ports allow network and internet-connected devices to interact using specified channels. While servers with dedicated IP addresses can connect directly to the internet and make ports publicly available, a system behind a router on a local network may not be open to the rest of the web. To overcome the issue, port forwarding can be used to make these devices publicly accessible.

So much information exists online that it's easy to get lost in data while researching. Understanding the bigger picture can take a lot of time and energy, but narrowing the question to one that's easy to answer is the first step of any investigation. That's why analysts use open-source intelligence (OSINT) tools like Maltego — to help refine raw data into a complete understanding of a situation.

Virtual private networks, or VPNs, are popular for helping you stay anonymous online by changing your IP address, encrypting traffic, and hiding your location. However, common IoT devices, media players, and smart TVs are hard to connect to a VPN, but we have a solution: Turn a Raspberry Pi into a router running through PIA VPN, which will ensure every connected device gets the VPN treatment.

Your smartphone is the perfect place to watch Hulu on the go. Whether you're looking to catch up on your shows in a hotel, or your phone is the only screen available, mobile streaming can be a lifesaver. But what about when you have access to a TV? Wouldn't you rather watch your favorite Hulu Original on the big screen than on your comparatively tiny smartphone?

Watching YouTube on your phone has never been a better experience than it is today — our smartphones have super-sharp displays that make watching the newest HD, QHD, and even 4K content look fantastic. But there are plenty of circumstances where we want to watch our content on a larger screen.

The USB Rubber Ducky comes with two software components, the payload script to be deployed and the firmware which controls how the Ducky behaves and what kind of device it pretends to be. This firmware can be reflashed to allow for custom Ducky behaviors, such as mounting USB mass storage to copy files from any system the Duck is plugged into.

Hello NullByte, it's mkilic! This time I'm here with the C.H.I.P from NTC. Although it is not too popular, the C.H.I.P is a brand new micro computer. It is very similar to the Raspberry Pi or Beaglebone Black. The key difference with this particular board is its cost and size. The C.H.I.P only costs $9 and measures 2.5 x 1.5 inches. In addition to this, the C.H.I.P has built in 802.11 b/g/n Wifi and Bluetooth 4.0. Considering these great specs, what could a Hacker use this for? Step 1: The In...

Greetings all. Today I intend to append a new series to my mini-collection of posts. This series will consist of informative guides for the purpose of depicting certain aspects of the White Hat profession that I believe are of profound importance. Furthermore, I will keep this series simple for everyone to follow, regardless of your tech level. So without further ado, let's get right into it.
Have you ever used an open wifi, which after you connect displays a website to enter your credentials to get internet? That website is called captive portal and widely used in airports, hotels, universities etc. Have you ever wondered what would happen if someone would set up an open wifi with the same name displaying a very similar web page asking for credentials? Usually if there are multiple wifi networks with the same name and encryption, devices only display the one with the highest sign...

Of course, if it were a perfect form of currency, it would have become the standard by now. But it hasn't. Wanna know why? The story begins with the advent of agriculture, when humans had settled down under groups as units called villages, over 10,000 years ago.

Over the past decade the Internet community has been witness to the rise of many new forms of online interaction. These new technologies have given rise to anonymous networks (like TOR), black markets within the deep web network (like the Silk Road), and even forms of digital currency, or more accurately crypto-currencies, such as Bitcoin. All of these technological advancements have contributed to securing users around the world and protecting their privacy. Therefore it is no surprise that ...