
Hacking macOS: How to Create an Undetectable Payload
Encrypting payloads and encoding stagers are more effective against macOS than one might think. It's very easy to evade VirusTotal and macOS antivirus software using a few simple tricks.


Encrypting payloads and encoding stagers are more effective against macOS than one might think. It's very easy to evade VirusTotal and macOS antivirus software using a few simple tricks.

Magic Leap shows up in the weirdest places. Last week, right at the start of World Cup fever, for some reason, the Magic Leap One appeared on a Brazilian television show.

We watched the first piece of public-facing content Magic Leap has released so you don't have to, and, well, you didn't miss much.

HBO is only a couple of episodes into the second season of Westworld, the television version of the classic science fiction movie about a robot resort gone awry, and the fan theories about the show are already reaching Season 1 levels of weirdness.

One of the most popular sports shows on television, Inside the NBA on TNT, gave viewers a tech-powered treat on Tuesday night by dropping them into a broadcast version of augmented reality.
When I'm with my friends on the weekend, we always end up Snapping shots of one another, adding in whatever stickers and lenses we've accumulated over the last week. But these filters are fleeting, so it's always a challenge to keep up with the best new ones. If you want to get a leg up on the competition, this is your one-stop-shop.

In the previous article in this short series, we learned how to find our neighbor's name using publicly accessible information and how to monitor device activity on their home network. With this information at our disposal, it's time to get into installing and configuring the necessary tools to begin our attack on John Smith's computer.

The internet is constantly under siege by bots searching for vulnerabilities to attack and exploit. While conventional wisdom is to prevent these attacks, there are ways to deliberately lure hackers into a trap in order to spy on them, study their behavior, and capture samples of malware. In this tutorial, we'll be creating a Cowrie honeypot, an alluring target to attract and trap hackers.

PowerShell Empire is an amazing framework that is widely used by penetration testers for exploiting Microsoft Windows hosts. In our previous guide, we discussed why and when it's important to use, as well as some general info on listeners, stagers, agents, and modules. Now, we will actually explore setting up listeners and generating a stager.

Hacking from a host machine without any form of proxying is reckless for a hacker, and in a penetration test, could lead to an important IP address becoming quickly blacklisted by the target. By routing all traffic over Tor and reducing the threat of malicious entrance and exit nodes with a VPN, we can configure Kali to become thoroughly private and anonymous.
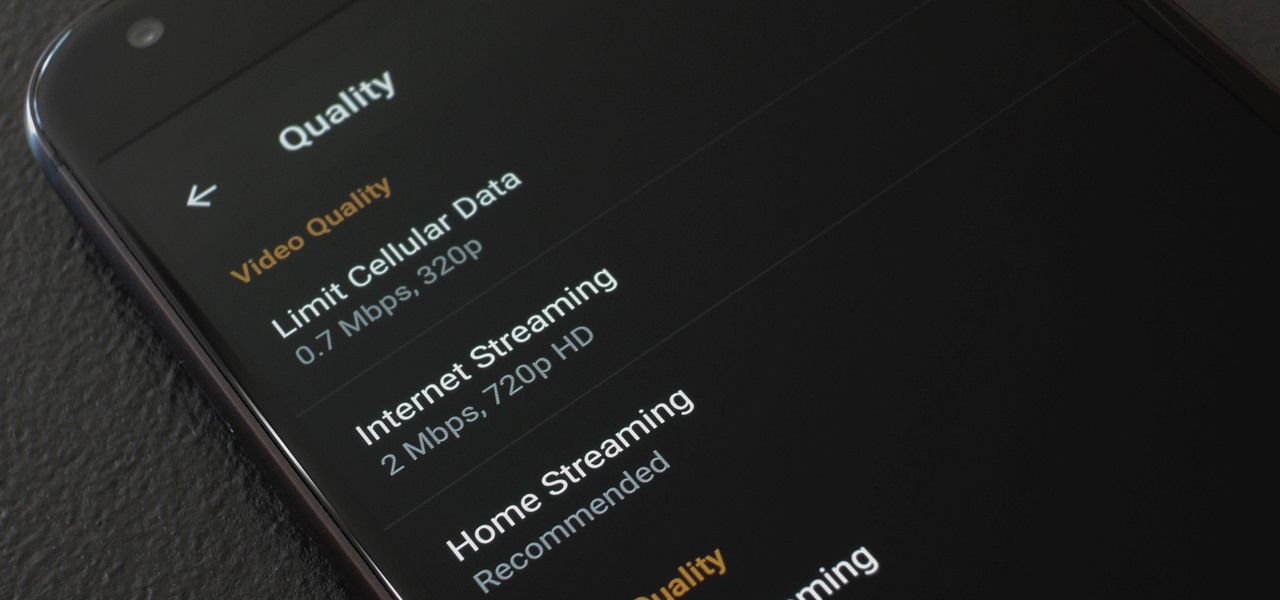
When you're on the go, Plex makes sure your media always stays with you. Just install the server app for Mac or PC and enable remote access, then you can stream movies and TV shows from your computer to your phone over the internet.

After laying off 40% of its staff this month to cut costs, SoundCloud appears to be struggling to stay afloat. While blog posts from the company have assured fans that the music platform is not in danger of shutting down, some people aren't so sure this is the truth. Internet Archive — a non-profit dedicated to preserving websites and services — announced today that they will be conducting a partial backup of SoundCloud to safeguard the site's content in case of closure.
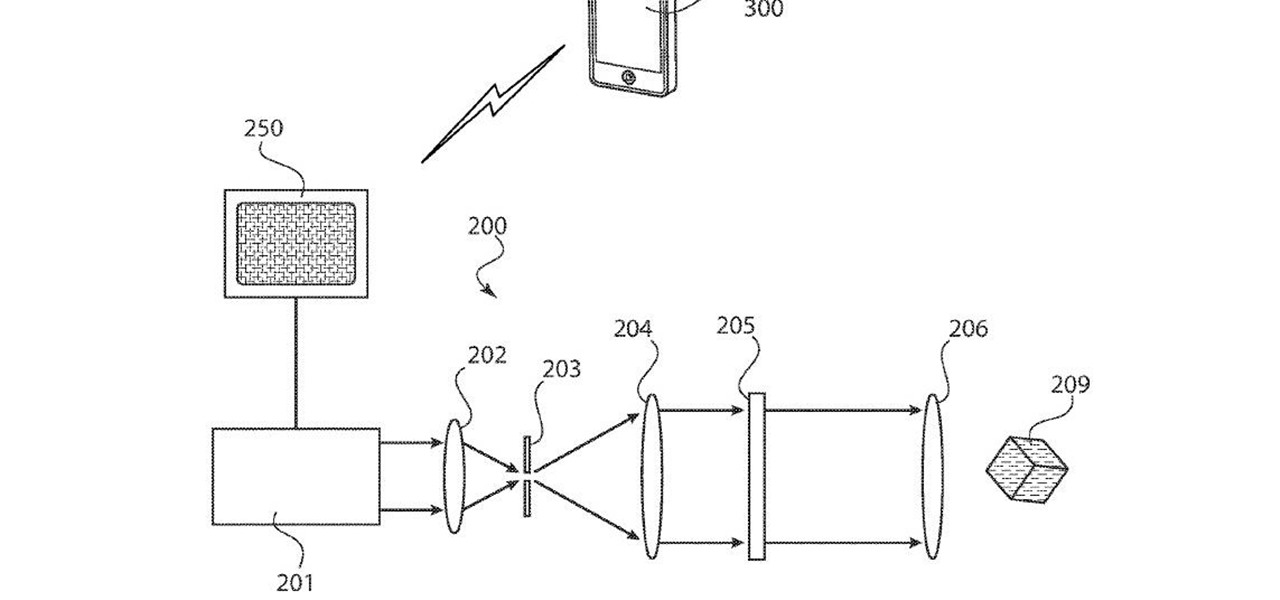
One inventor wants to bring augmented reality to internet radio and home audio speakers. Meanwhile, a leading consumer electronics company has opened up access its deep learning tools for building augmented reality apps. In addition, analysts examine how augmented reality will impact the design and construction and profile the top developers in augmented and virtual reality.

The Easter Bunny is about to get his first experience with mixed reality. Virtual Reality Los Angeles (VRLA) will host its third annual expo in April, and this year's attendees will get to experience a fun Easter egg hunt sponsored by AfterNow and VRLA, in partnership with mixed reality king, the Microsoft HoloLens.

With a predicated increase in the number of Lyme disease cases in the coming spring season, new research endorses the use of bait boxes to control ticks on the rodents that serve as their hosts.

No matter which smartphone you buy, it will come with an internet browser preinstalled. Depending on your OEM, the default browser might be called Samsung Internet, HTC Internet, Silk Browser by Amazon, ASUS Browser, or Google Chrome—there's just so many stock browsers available.

Today in Los Angeles, Unity will be at the Loews Hollywood Hotel to host Unite '16, its annual developer conference. Unite is Unity's platform for showing the development community its upcoming direction and roadmap for augmented and virtual reality, game development, 3D technology, and more.

Augmented and mixed reality experiences attempt to break us out of windowed computing experiences and allow us to place software anywhere in the room. But that software doesn't have to take a rectangular form—theoretically, the web doesn't have to restrict itself to a page in a browser any longer. Does this mark the end of the web browser entirely? Probably not. A lot of information works well on the page, and the Microsoft HoloLens still uses a pretty standard version of their own Edge brows...

Welcome aboard my inquisitive comrades. I am starting a new series that nobody expected coming. It may not seem very exciting at first, but await the last few parts as many startling discoveries will be made. This is a series which I plan to continue after the completion of Nmap, unless you have major objections.

Welcome back, my novice hackers! In this series, we have been exploring how a forensic investigator can find evidence of illegal or illicit activity. Among other things, we have examined the registry and prefetch files for artifacts and have done some rudimentary forensic analysis. For those of you who are seeking career as a forensic investigator or security engineer, this can be invaluable training. For hackers, it might be life-saving.

Welcome back, my greenhorn hackers!

When you're in a bind and need an internet connection for your laptop, look no further than your iPhone. Using the Personal Hotspot feature in iOS, you can share your iPhone's internet connection with other devices by way of Wi-Fi, Bluetooth, or even USB.

I'm lucky enough to have internet access on my laptop practically everywhere I go because of my mobile hotspot plan. All I have to do is enable the personal hotspot feature from my iPhone and I can surf the web on any Wi-Fi enabled device. But of course, there's a catch.

If you're just starting out with Android—or smartphones in general, for that matter—there are a lot of little things to learn. One of the first terms you'll likely encounter is "Wi-Fi," which is a wireless internet connection served up by a router in your home, office, or local coffee shop. This differs from your smartphone's regular "Mobile Data" connection, which is provided by your cellular carrier and included as part of your monthly bill.
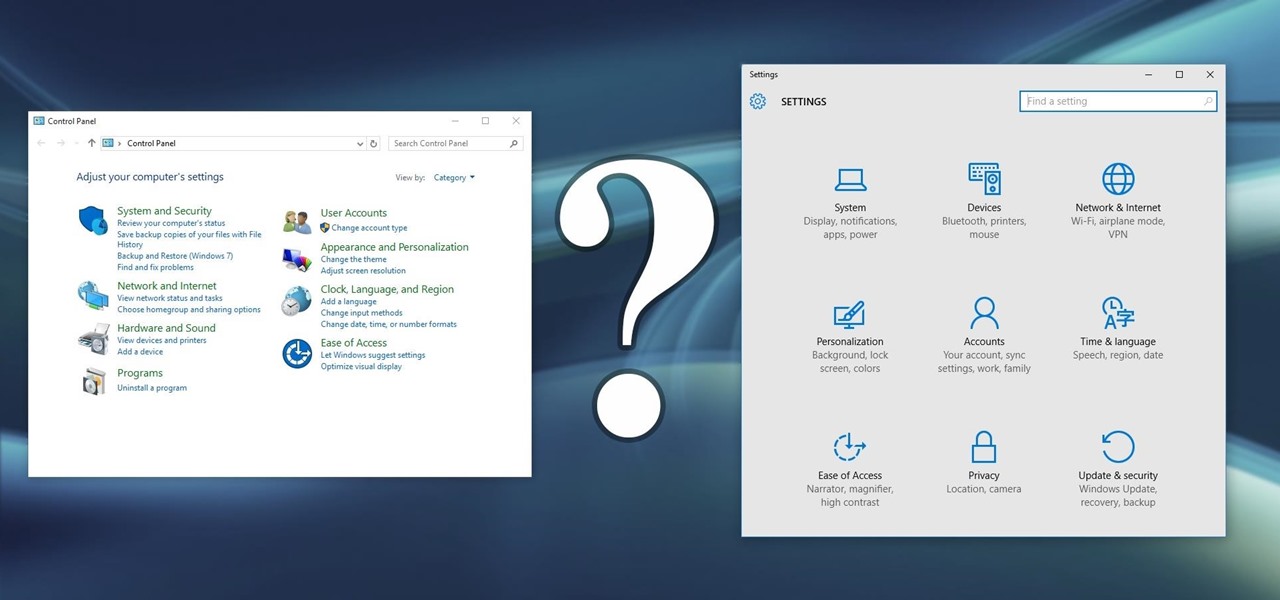
Slowly but surely, Microsoft is pushing more and more options out of the Control Panel and into a new menu simply called Settings. This new Settings menu debuted with Windows 8 and mainly focused on touchscreen-related options, but starting with Windows 10, you'll find quite a few general options residing here as well.

Social Engineering was mentioned a few times here on Null Byte, but not very many explained what it is, or how to do it. I love this quote because it's true: Social Engineering is the key to carrying out client side attacks, and all you need is a little creativity!

Since the Nexus Player is an Android device at heart, there are already several internet browsers that can be used on the streaming set-top box. Chrome, Firefox, and a few others will run perfectly fine, but the trouble with these is that you need a mouse to use them.

Thanks to Verizon Wireless, I pay over $220 a month for my phone bill. It's just me on the plan—no family members, and it's not even unlimited data. So, when I receive that data alert message telling me that I've used up 90% of my plan and that I've still got a few more week until my billing cycle starts over, you know that I'm left scrambling to connect to some Wi-Fi.

While CNN, FOX News, and MSNBC are valuable sources of information for what's going on in the world today, they may not be the best news stations to watch if you actually want to learn something. They, along with local news stations, are great at grabbing your attention, but if you truly want to learn something about recent events, you're tuning into the wrong channel.

The older I get, the more my Friday nights involve watching Netflix at home with a bottle of Maker's Mark and a box of Oreos. Netflix is a big part of my life, and I'm not alone. YouTube and Netflix make up over 50% of all activity on the Internet, so it might be worth your time to understand why Netflix seems to cause so many headaches and what can be done about it.

Flappy Bird is the extremely difficult, overly frustrating, strangely similar, yet highly addictive smartphone game from .GEARS STUDIOS that has catapulted its way to the top of the charts on both Google Play and the iOS App Store—seemingly out of nowhere.

When we surf the web, we tend to do it for selfish reasons. Whether it's on Facebook, Twitter, YouTube, Pinterest, or Wikipedia—we're trying to connect with people, voice our opinions, watch funny videos, or do research for that 12-page paper due tomorrow. Whatever it is, it's usually to benefit ourselves. Well, what if you could not only benefit yourself while surfing the web, but benefit others in need, without even having to alter your habits?

Microsoft's updated web browser, Internet Explorer 10, has only been out for a few days on Windows 8, and there is already a storm of controversy surrounding its launch.

This video gives you the lowdown on making a lag switch for gaming. But why would you want a lag switch? What is a lag switch?

Club Penguin is a flash-based website with an a virtual world of online games for kids to play. Learn how to hack Club Penguin with tricks and cheats. Watch this video tutorial to learn how to hack Club Penguin for loads of money with WPE Pro (03/22/09).

Hosting a Twilight-themed party? Of course you're going to want a cake! This video shows you how to use gumpaste or fondant to make a ruffled tulip like the one on the cover of New Moon. Fondant is an edible, easy to work with material that you can use to shape just about any kind of cake decoration you can think of. You'll need: wire, wire cutters, a rolling pin, a cutting board, grease, water, an orchid press, a veining tool, a fondant cutter and a thin piece of foam.

Learn how to use organizational folders on an Apple iPad running iOS 4.2.1 or 4.2! The 4.2 release of Apple's iOS 4 mobile operating system for the iPhone, iPad and iPod Touch brings with it a host of new features. While that's certainly a cause for celebration, there's also, believe it or not, a downside: learning how to take advantage of them. Happily, the web is awash in helpful video tutorials like this one which make the process a pleasure (and a simple one at that).

Learn how to multitask when running iOS 4.2 or 4.2.1! The 4.2 release of Apple's iOS 4 mobile operating system for the iPhone, iPad and iPod Touch brings with it a host of new features. While that's certainly a cause for celebration, there's also, believe it or not, a downside: learning how to take advantage of them. Happily, the web is awash in helpful video tutorials like this one which make the process a pleasure (and a simple one at that).

This is a video tutorial in the Hosting & Entertaining category where you are going to learn how to decorate your Christmas tree with big impact using ribbon. You begin the process by fluffing. Choose two beautiful ribbons. Try different ribbon combinations like metallic and satin or velvet and harlequin. The ribbon must be wired. Make a simple loop and twist the ribbons together. Wrap one loop around one piece of the tree branch. Then make another loop on the ribbons and wrap it around anoth...

Most people save up their baking for Christmas time, when the home traditionally smells like sugar, cinnamon, and a plethora of baked goods. But Halloween is just as great an opportunity to both create something delicious and gorgeous looking.