In this clip, you'll learn how to use proxies to circumvent whatever Internet filters may be in place at your school or place of work. For more information, including a complete demonstration of the process and detailed, step-by-step instructions, watch this home-computing how-to.

Want to add a clickable button to your website, but want something a little more exciting than just the ordinary picture or text button? If you have Adobe Flash and After Effects CS4, then you can design yourself a really cool, electrified button with your logo on it. Click here for the source files.

A snippet is a piece of code which you may want to repeatedly use (like a login code). Snippets can also be global, which you can apply to every website you have. This tutorial shows you how to store and use snippets in Dreamweaver.

Do something fun with your child for Mother's Day and make a paper sunflower! Get crafty with your son or daughter and spend time with them while letting them explore their creative spirit! To make this sunflower you will need patterns which can be found here on the Cullen's ABCs website.
AVG Free from Grisoft provides you with basic antivirus and antispyware protection for Windows and is available to download for free. The only trick is finding it on the AVG website. In this video tutorial, you'll learn how to find and install AVG on your own Windows PC. Take a look!
If you visit the same pages over and over, you may want to consider setting multiple start pages. While you may not have even known such a thing was possible, the set-up procedure is simple in both Mozilla Firefox and Windows Internet Explorer 7. Learn how to use browser tabs to open up multiple websites when you launch your browser with this how-to.

Want to watch your favorite Internet clips in the woods? Or on a boat? This video tutorial offers step-by-step instructions on downloading streaming video from video sharing websites like YouTube and Dailymotion using the media-convert web application. For more, or to get started using Media Convert for yourself, watch this video how-to!

Interested in pen spinning? Want to pick up a few moves? Pen spinning is the skilled movement of a writing instrument or pen with one's hands. It is used as a source of self entertainment (often for students), but there is a great deal of pen spinning culture (competitions, websites, etc.). Watch this pen spinning tutorial video and learn how to perform the "Continuous Middle Backaround 1.5" move.

This tutorial demonstrates how to quickly and easily create graphical navigation bars with DHTML menus for your website, using Xara Menu Maker.

A quick demo of how easy it is to create graphical website button bars with DHMTL menus using Xara Webstyle.

This website (www.someecards.com) is full of interesting e-cards that say what you really think instead of sugar coating it. Have fun with this one :-)

This walks you through how to create an animated GIF image file that can be used in websites, as avatar's, as icons, etc. You'll be using Microsoft Paint to create each frame of the animation, and an application called Unfreez (found here) to animate them together.

The extract tool in Photoshop is one of the most frequently used - and useful - tools you'll ever learn to use. Extracting allows you to remove a picture from its background or even filter away flyaway hair.

You can make almost any website your homepage but what if you have more than one favorite? How do you choose? With FireFox you don't have to because you can set multiple homepages.

This video explains how to organize your photos into folders on the Pictage Photo Lab website.

See how to add grungie borders to your images to give them a cool effect in Photoshop. If your borders are white and the background of the background of the website or page you are uploading them to is also the borders will blend in giving it an even cooler look. This is a great Photoshop picture effect!

How to write Page Titles for your Title Tags from Search Marketing Vancouver. Learn how effective Title Tags can improve your SEO Results on Google and increase traffic to your website.

In this video, you'll discover how to upload files to your own website or blog using FTP.

This guitar lesson demonstrates how to play the recorder/keyboard intro to Stairway to Heaven as I have transcribed it on guitar. Tabs for this lesson are available on my guitar lesson website, on the "NEW STAIRWAY TO HEAVEN VIDEO" link:

This tutorial demonstrates how to create message boxes for a website using Adobe Dreamweaver.

Another NewDarkRoom.com Video tutorial. This tutorial will show you how to get more room out of your photo booth by hiding all the unwanted parts past your seamless paper. As usual you will be able to find a more detailed larger video at our website.

If you're putting your email address online on your own website, or sites like facebook or myspace, you may want to be a bit clever about it. Check out this tutorial and see how to protect your email address from spam.

Django is a Python web framework used for rapid application development in any environment. In under 10 minutes, you can go from a bare Linux (Ubuntu) installation to a fully functional Django server.

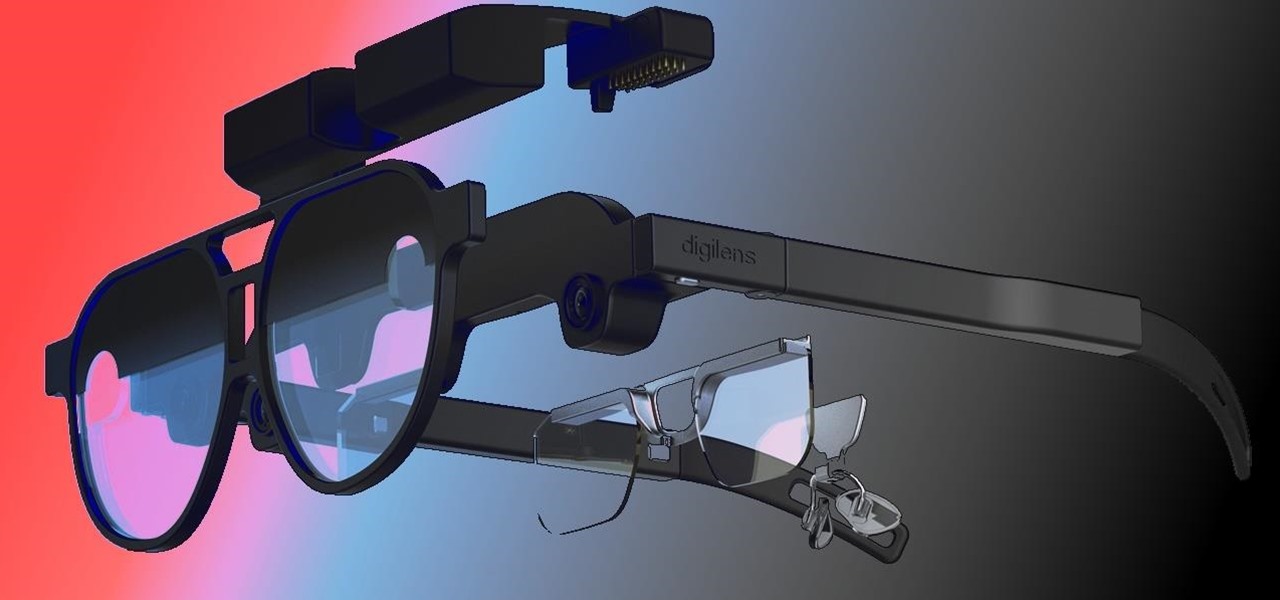
When it comes to the future of AR smartglasses, DigiLens has one word for you. Just one word. Are you listening? Plastics.

Over the past three years, Epic Games has raised billions of dollars in funding on the success of Fortnite as well as Unreal Engine, one of the top 3D engines available for developing games and AR experiences.

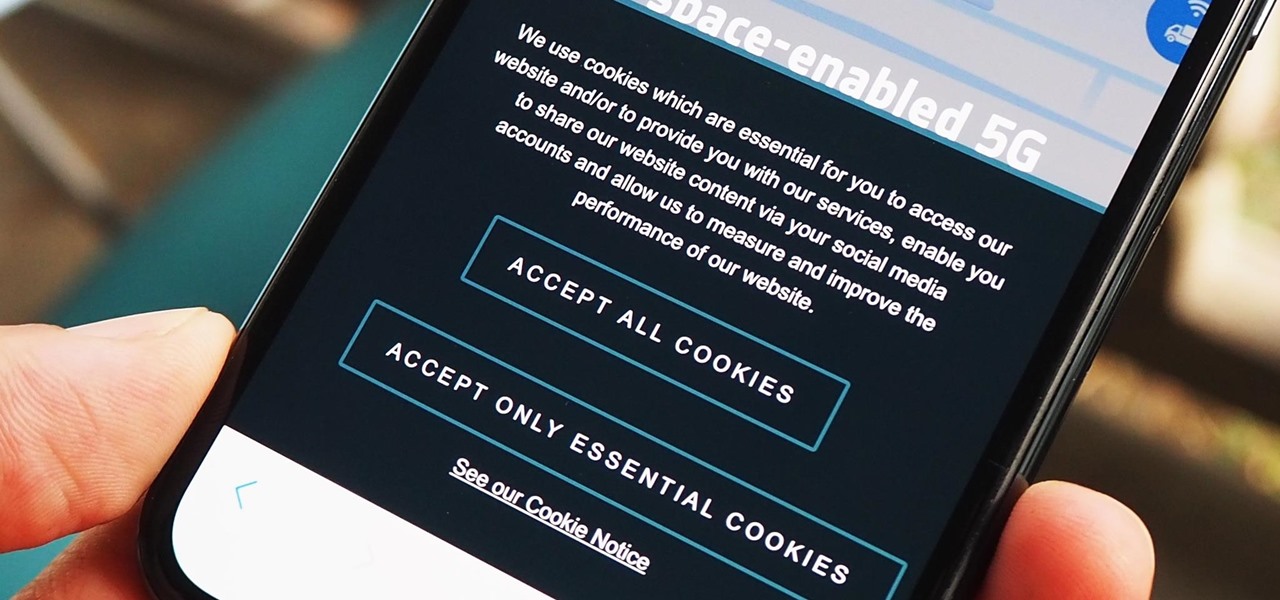
As a means to combat annoying and intrusive advertisements in Safari, Apple added native support for content blockers on the iPhone. Instead of being bombarded by notifications, banners, and pop-ups, content blockers prevent them from opening, which can also be said about those annoying cookie consent notices that many websites now have.

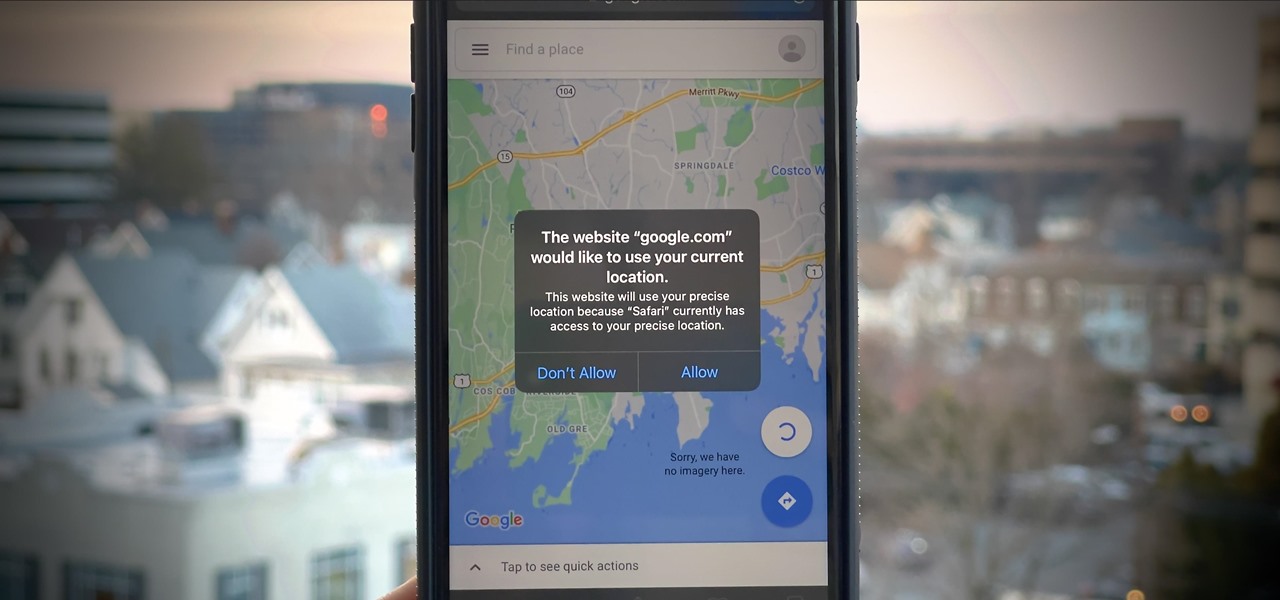
If you surf the web on your iPhone, you no doubt run into this problem all the time: a website wants your location. It can happen when performing a location-based task, such as using a store locator, or whenever a web app just wants to deliver better ads or local recommendations. If you're tired of allowing or denying permission each time, there's an easy way to stop the annoying security pop-ups.

No website, service, or platform is immune to being abused or exploited by hackers, and Google Analytics is no exception. To better understand how Google Analytics can help deliver payloads and bypass security protocols, one might want to learn how to use Google Analytics from a user's perspective first.

It's pretty much a given at this point that Facebook has a lot of data on us. While you might be conscious of the data you share with Facebook when you post, upload photos, or chat with friends on Messenger, you might not be thinking about all the data it receives from websites and apps you use outside the social media giant. Now, you can actually do something about it.

In just a few weeks, on May 29, the annual AWE (Augmented World Expo) conference will take place once again in Silicon Valley (Santa Clara, California, to be exact).

Your social security number, credit card information, and medical history can fall into the wrong hands if you're not careful about how and where you share your data online. If you really care about your data, there are tools and techniques you can utilize to protect yourself from cyberstalkers, advertisers, and hackers in a time when digital lives are a high commodity.

Augmented reality and computer vision company Blippar has a new lease on life, as previous investor Candy Ventures has completed a successful bid to acquire the assets of the beleaguered company.

Nmap is more powerful than you know. With a few scripts, we can extend its functionality beyond a simple port scanner and start to identify details about target servers sysadmins don't want us to know.

Reconnaissance is the phase of an attack where a red team or hacker designs a strategy based on the information they can learn about the target, as well as what the available attack surface looks like. These scans can take time to discover relationships, but Raccoon OSINT scanner coordinates multiple automated scans to produce invasively detailed reports on a target with a single command.

A convincing domain name is critical to the success of any phishing attack. With a single Python script, it's possible to find hundreds of available phishing domains and even identify phishing websites deployed by other hackers for purposes such as stealing user credentials.

Identifying vulnerable devices and services on a target router can be difficult without leaving logs and other traces of an active attacker on the network. However, there is a way to covertly decrypt and view Wi-Fi activity without ever connecting to the wireless network.

If competition in the augmented reality space was a spectator sport, then ARKit, ARCore, and HoloLens dominate the prime-time broadcasts on ESPN.

so i have just signed up to this, and i dont know much about this website but i wanted to show my recent upload

Custom Timelines (CTs) allow you to control exactly which Tweets appear in a column on Tweetdeck. So if a particular event catches your eye as newsworthy you can tailor your CT to show what you consider to be the most relevant Tweets. These CTs can then be customized, shared and embedded on your website. This is a great way of increasing interaction on Twitter and sharing current, interesting and breaking news stories from any niche or subject

Apple's new iOS 8 has a ton of new features, and so does their revamped Safari app, only some of the features aren't quite as obvious as others. In this guide, I'll show you my 5 favorite Safari secrets in iOS 8 for your iPad, iPhone, or iPod touch.