A young child becomes very thirsty very often and seems tired all the time. A visit to the pediatrician determines she has type 1 diabetes. The onset of type 1 diabetes may seem sudden, and it can be, but the disease may actually have been triggered by common childhood viruses years earlier.

Using mathematical modeling, researchers suggest weather and warming created the "perfect storm" that drove the Zika outbreak in 2016.

It's become a routine for many of us to ring in the New Year with pledges to finally get our budgets and finances under control. Unfortunately, it's also quite difficult to to keep those promises. Some of us will just dive into our resolutions and wing it as we move forward, which usually ends in failure. But even for those of us who plan carefully, obstacles along the way can spell doom for New Year's resolutions.
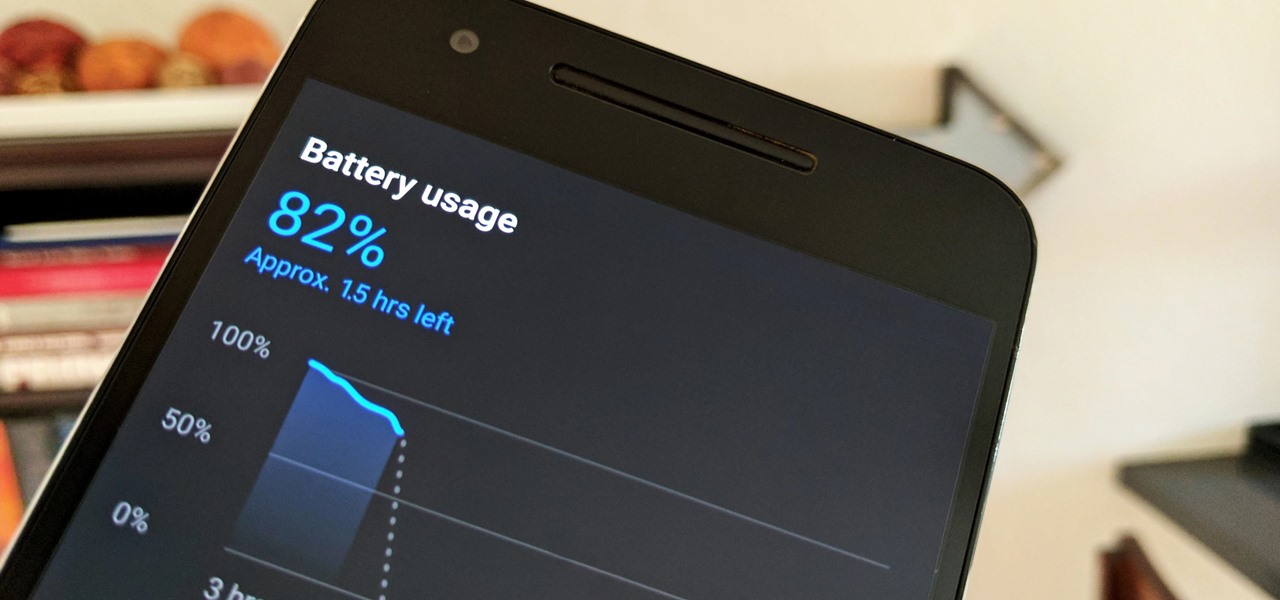
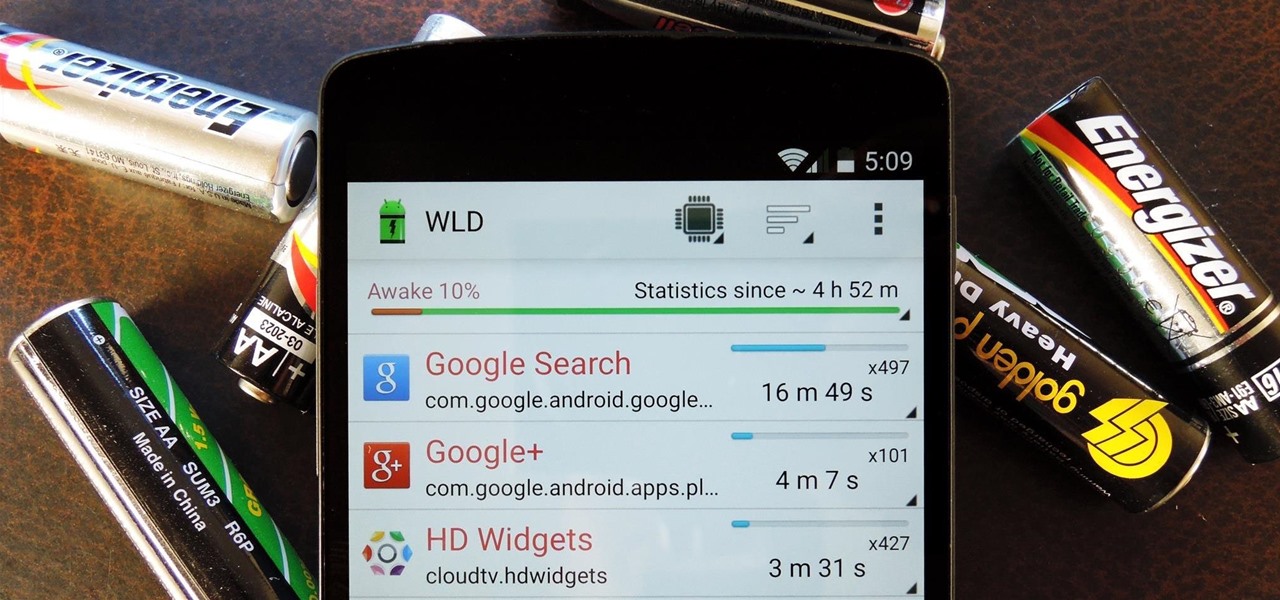
Starting in October, many Nexus 6P users have been experiencing a bug that causes their phone to completely shut down, even though there was 20% or more battery life remaining. At first, it was thought to be a direct result of the recent Android Nougat update, but a combination of factors indicate that this isn't necessarily the case—or, at least, it's not the only problem.

The future of augmented and mixed reality offers many possibilities, mostly because we're still figuring out everything it can do. While Meta is open to exploration, they've spent a lot of time thinking about what the future of this technology will be.

In Pokémon GO, having an in-depth understanding of your Pokémon's stats and abilities is crucially important to becoming a better player. Not all Pokémon are created equal; as such, it's critical that you look at each of your Pokémon—even duplicates—with a keen eye.

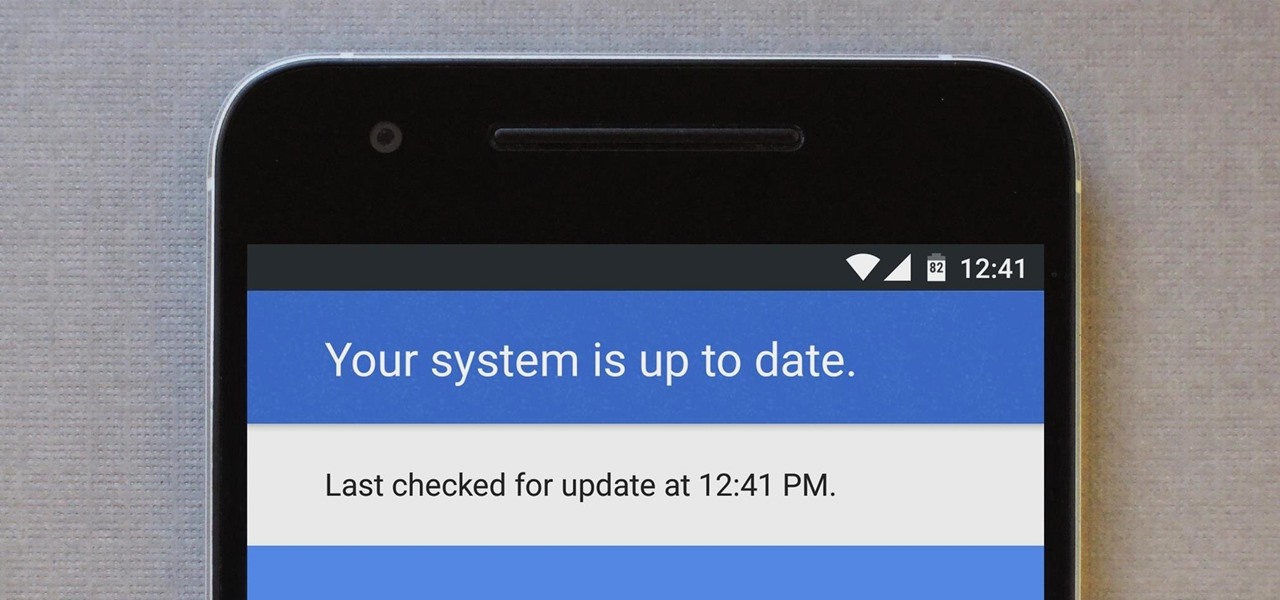
For many people, the two main advantages of buying a Nexus device are prompt updates and the ability to root without much hassle. But in a cruel twist of fate, these two features are almost mutually exclusive, since OTA updates will refuse to run on rooted devices.

Welcome back, my budding hackers! One of the most basic skills the forensic investigator must master is the acquisition of data in a forensically sound manner. If data is not captured in a forensically sound manner, it may not be admissible in court. In my Kali Forensics series, I showed you how to acquire a forensically sound, bit-by-bit image of a storage device such as a hard drive or flash drive, but now let's dive into live memory.

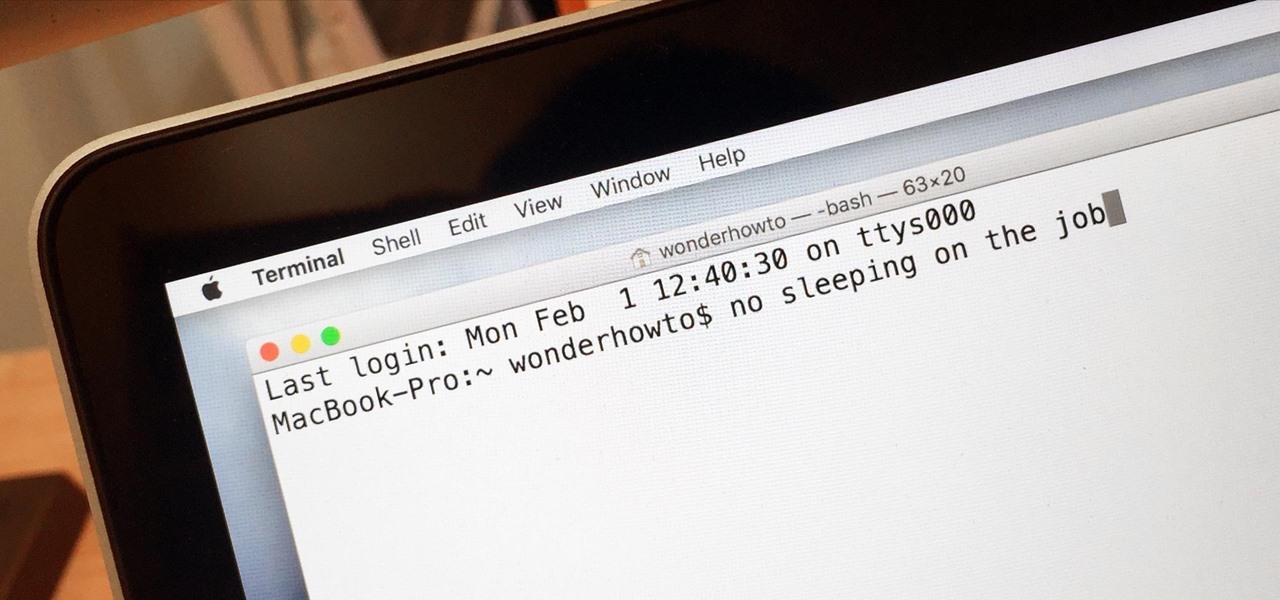
Macs are generally highly power efficient due to, in part, the optimized sleeping schedule with OS X. Yet in certain scenarios, you might not want your Mac to go to sleep: downloading a huge file, reading a book, reviewing a spreadsheet, analyzing some content on the screen... the list goes on. To resolve this, you can go to System Preferences and mess with the settings, but this can be an annoying process if you need to do it often.

Welcome to an introduction on writing basic malware, an optional sub-series in which I expose you to malware and its technologies. This is written for those who wish to seek a beginning in malware analysis or enlightenment on the subject. We will be justifying the writing and covering types of malware.

In previous tutorials we have encountered these things called pointers and addresses but we still don't know what they really are. Let's learn a bit more to clear things up.

I think it was 1986 when I first discovered my love for making computers say stupid things out loud. My older brother got a Commodore 64 for his birthday, which came bundled with software that would speak out any term you typed in—and boy, that computer sure made a fool of itself after my five-year-old imagination got a hold of the keyboard.

With T-Day on the horizon and approaching rapidly, you are probably in one of two camps. The one that is eagerly awaiting the holiday feast with barely-contained drool. Or the one that involves breathing heavily into a paper bag while worrying about your lack of oven and stovetop real estate, while also bemoaning the lack of multiples of you to get all the prep work done.

Practically every smartphone comes with a built-in camera app, but these apps are generally created by the device's manufacturer. And let's face it, manufacturers are hardware companies first and foremost, so they don't always produce the best software.

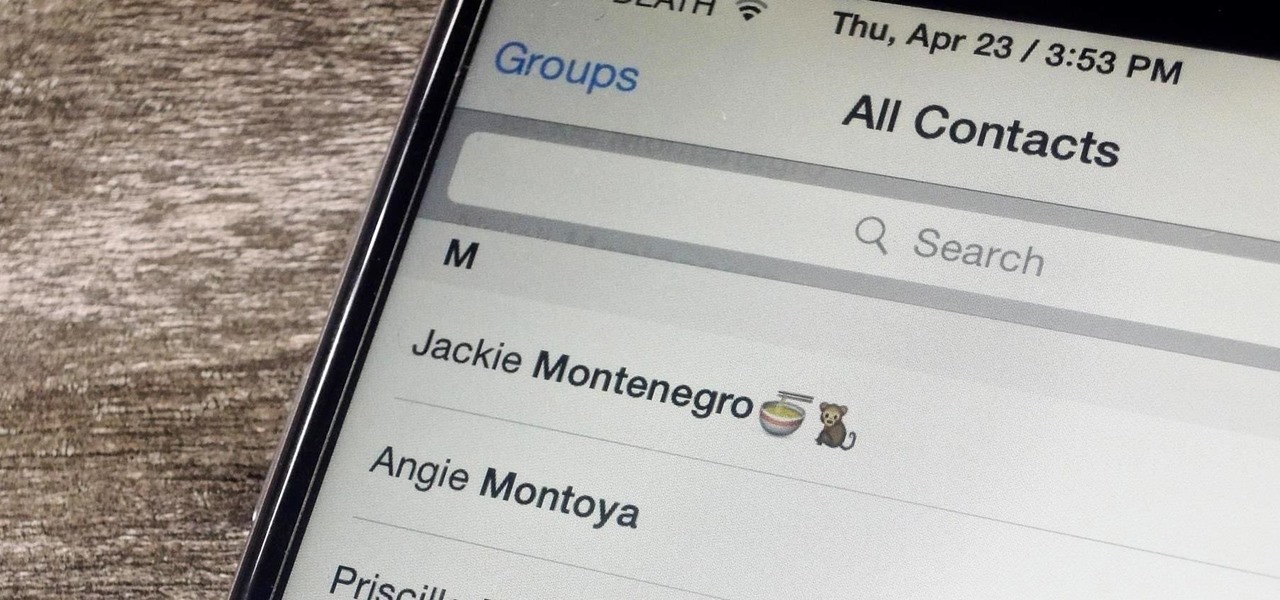
Organizing contacts is a bitch, especially on the iPhone. Some contacts will have multiple entries, you can only delete contacts one by one, and certain types of contacts can't be deleted at all. If that isn't enough to make you pull your hair out, then I don't know what will.

Essay writing is the bane of most students' educational existence. Whether you're a college student tired of slaving away over 30-plus page research papers or a high school student just trying to get through AP Language, chances are you'd love to find a way to cut down on all the writing. Before you spend hours googling facts and figures to cram into your next paper, work smarter by cutting down on content.

Welcome back, my tenderfoot hackers! In continuing my series on digital forensics using Kali, I want to introduce you to two complementary tools, both built right into Kali Linux. These are Brian Carrier's tools Autopsy and Sleuth Kit.

Android uses a set of permissions that apps can request to perform certain actions, and you're notified of these permissions each time you install an app. The problem here is the fact that you aren't given any built-in way to deny apps these permissions (although Danny just showed a workaround for this).

Everyone told you that smoking was bad for you, but sometimes it takes a visual lesson to finally quit smoking tobacco products.

Tired of running around and destroying blocks with a sword? Or your fist? Looking for a solution that involves explosives, a little ingenuity, and a much faster destruction rate!? Well, you ask, and you receive! In this video you will learn how to make your very own canon! Just remember, the water is NECESSARY to keeping the canon intact, since it absorbs the shockwaves of the TNT. Enjoy!

This next tutorial is a classic prank that is easy to perform and will trick everyone around your car. It involves leaving a bag full of groceries, items, goods, whatever on top of your car and driving around with it on there.

Celebrity chef Bobby Flay teaches us to make an elaborate seafood stew. If you really want to impress some open-minded guests and have some experience making your way around the grill, than this recipe is for you. It involves several kind of shellfish, anodouille sausage, and a secret ingredient that even the aforementioned open-minded guests are better off not knowing about: anchovies. Don't be scared, when combined with all of the other ingredients they go from dominating the dish, as they ...

In this video tutorial, viewers learn how to become a golf coach. Most coaches are high school teachers. You don't have to be a teacher to coach. You just need to be great a player and enjoy the sport. You need to have the desire. They need to set up the programs and setup the tournaments. There is not a lot of teaching involved. They mainly have one on one lessons. But to become a college golf course, you need a college education. This video will benefit those viewers who enjoy the sport of ...

This short origami video tutorial will teach you how to fold an origami birthday hat napkin design. Decorative origami napkins are perfect for any table and any occasion. Folding napkins into 3D objects is not only beautiful on the table, but fascinating. Origami napkin folding should be a trick up every table decorator's sleeve. Celina Table Linens shows you the simple steps involved in the napkin origami birthday hat.

Check out this short video tutorial on how to fold an origami bird napkin design. Decorative origami napkins are perfect for any table and any occasion. Folding napkins into 3D objects is not only beautiful on the table, but fascinating. Origami napkin folding should be a trick up every table decorator's sleeve. Celina Table Linens shows you the simple steps involved in the napkin origami bird.

Learn how to solve the infamous Rubik's Cube. Yes, that's right, watch this three-part video tutorial to see how you can solve Erno Rubik's Magic Cube, now known as the Classic 3x3 Rubiks Cube. Learn the notation and the algorithms involved.

Dolphins are some of the best, most graceful swimmers in the sea. Majestic and beautiful, they achieve both speed and form while looping from wave to wave.

Offense tactics are important in rugby, where the ball cannot be thrown forward. Learn how to play rugby, including rules and skills, in this video rugby lesson.

This how to video shows you the step by step process of making a baby beaded frog. This is easy and fun activity to do with your kids. Beading is a great way to introduce your children to the creativity of arts and crafts. This is a good project for older children because it does involve small beads that can be swallowed. With this how to video you will be able to teach your children how to make a beaded frog.

Kung fu is an ancient Chinese martial art that involves using powerful punching techniques. Learn several punching combinations from a professional kung fu instructor in this free video series.

In this 5 part manicure tutorial you will learn how to apply acrylic nails. This process is quite involved and a bit difficult so it will take a lot of practice. Watch this 5 part how to video and you can apply acrylic nails in your own home.

During the video tutorial, you'll learn how to simply solve the easy and fun fifteen number puzzle. You'll learn a couple different moves to help you solve the 15 puzzle, which are called the curl and the box and twist. The curl is easy, but the box and twist is a little more complicated.

The Jitterbug is a popular swing dance, also known as the Lindy Hop and East Coast swing. This how to video demonstrates a Jitterbug dance sequence. These steps are quick and easy to learn. The routine involves the Texas Tommy step, the left side under-arm turn, the left side waist turn, the tuck turn and the right side under arm turn. Watch this dance tutorial and you will be doing the Jitterbug in no time.

In this math lesson we will learn how to solve problems involving simple interest. When you deposit money in a savings account, the bank pays you interest at a certain rate called interest rate. There are two types of interest: simple interest and compound interest. In this lesson we will talk about simple interest. We will use the following important formula:

To learn how stop worrying involves regular fasting from fear, learning to plan without worrying and to accept the future as it comes. Part of a Yoga class on Rasa Sadhana, the Tantric practice of emotional fasting.

Hello! My name is Nicole Valentine and on behalf of Expert Village, I'm here to talk to you about how to coordinate birthday games for a birthday party. Its time to party. Now we're going to discuss the appropriate games for the birthday party. For example, if you're having a party for a 5 year old, you want to choose games that are lively. Invite a clown, have face painting. Have games that are going to make the children, and when they leave they'll be glad that they came to the birthday par...

HomePod and HomePod mini are excellent smart speakers if you're entrenched in the Apple ecosystem. They even offer ways to protect your sensitive information from friends and visitors who try to ask Siri to spill your secrets. But there's an extra layer of privacy you can put in place to make sure nobody gains access to any important notes, reminders, and calendar events.

The true crime genre has long been popular on television and more recently on podcasts with shows like Serial.

With all this time spent stuck at home because of the COVID-19 pandemic, HQ Trivia would be a prime way to beat the boredom. Unfortunately, HQ went belly up in February, just before everyone had stay-at-home orders. While HQ has teased a potential comeback, there are other trivia games out there that are live right now. One of those brings the spirit of HQ Trivia back to our phones.

Without admin privileges, installing additional software, or modifying the Windows 10 firewall, an attacker can alter a router and perform a variety of exploits. It's accomplished by forwarding requests from Kali through a backdoored Windows computer to the router gateway with simple SSH tunnels.