
How To: Do a dolphin kick when swimming
Dolphins are some of the best, most graceful swimmers in the sea. Majestic and beautiful, they achieve both speed and form while looping from wave to wave.


Dolphins are some of the best, most graceful swimmers in the sea. Majestic and beautiful, they achieve both speed and form while looping from wave to wave.

Offense tactics are important in rugby, where the ball cannot be thrown forward. Learn how to play rugby, including rules and skills, in this video rugby lesson.

This how to video shows you the step by step process of making a baby beaded frog. This is easy and fun activity to do with your kids. Beading is a great way to introduce your children to the creativity of arts and crafts. This is a good project for older children because it does involve small beads that can be swallowed. With this how to video you will be able to teach your children how to make a beaded frog.

Kung fu is an ancient Chinese martial art that involves using powerful punching techniques. Learn several punching combinations from a professional kung fu instructor in this free video series.

In this 5 part manicure tutorial you will learn how to apply acrylic nails. This process is quite involved and a bit difficult so it will take a lot of practice. Watch this 5 part how to video and you can apply acrylic nails in your own home.

During the video tutorial, you'll learn how to simply solve the easy and fun fifteen number puzzle. You'll learn a couple different moves to help you solve the 15 puzzle, which are called the curl and the box and twist. The curl is easy, but the box and twist is a little more complicated.

The Jitterbug is a popular swing dance, also known as the Lindy Hop and East Coast swing. This how to video demonstrates a Jitterbug dance sequence. These steps are quick and easy to learn. The routine involves the Texas Tommy step, the left side under-arm turn, the left side waist turn, the tuck turn and the right side under arm turn. Watch this dance tutorial and you will be doing the Jitterbug in no time.

In this math lesson we will learn how to solve problems involving simple interest. When you deposit money in a savings account, the bank pays you interest at a certain rate called interest rate. There are two types of interest: simple interest and compound interest. In this lesson we will talk about simple interest. We will use the following important formula:

If you like 2D side-scrolling video games, then Shank's your man. Shank is full of "beat 'em up" action and combat, perfect for any gamer addicted to the old style of play. Shank is available on both the Xbox Live Arcade (Xbox 360) and PlayStation Network (PS3). But this Mahalo walkthrough for Shank is for the PlayStation 3.

If you've ever wanted to start learning to code but haven't known where to start, then one of the best places is with Python. It's great for introductory programmers, and it's also a must-have addition to the repertoire of anyone experienced in the industry. As of 2019, over eight million programmers have used Python, and the industry has only grown since then, so the best time to start practicing is today!

HomePod and HomePod mini are excellent smart speakers if you're entrenched in the Apple ecosystem. They even offer ways to protect your sensitive information from friends and visitors who try to ask Siri to spill your secrets. But there's an extra layer of privacy you can put in place to make sure nobody gains access to any important notes, reminders, and calendar events.

The true crime genre has long been popular on television and more recently on podcasts with shows like Serial.

Without admin privileges, installing additional software, or modifying the Windows 10 firewall, an attacker can alter a router and perform a variety of exploits. It's accomplished by forwarding requests from Kali through a backdoored Windows computer to the router gateway with simple SSH tunnels.
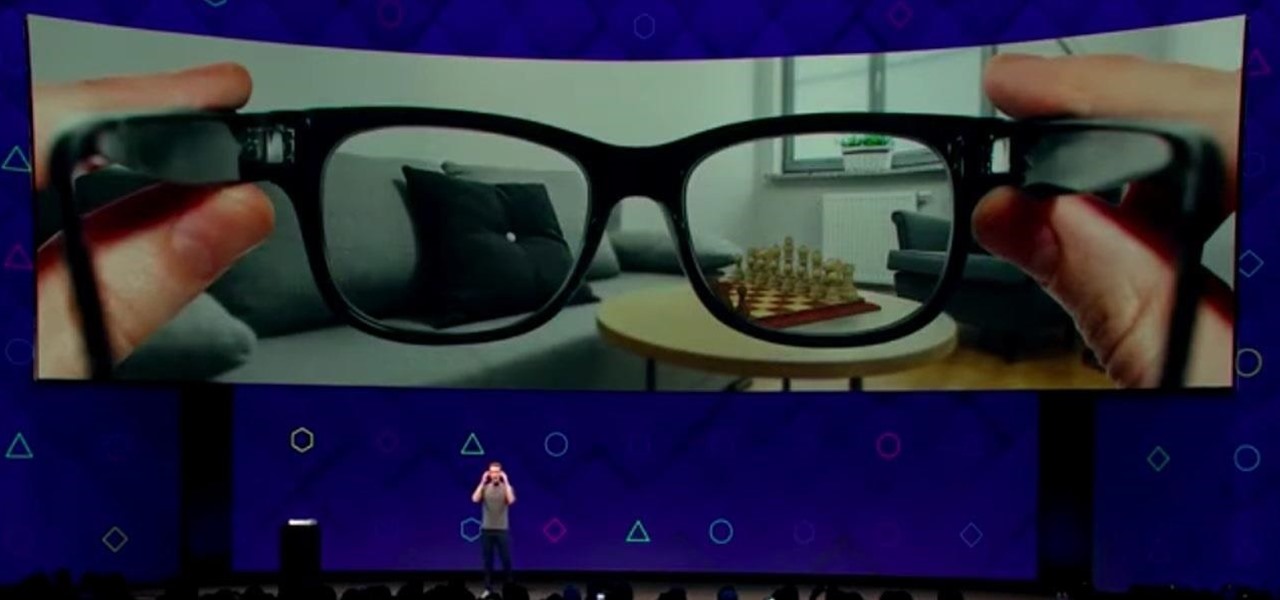
Next to Apple, Snap is currently one of the most important companies on the planet in terms of delivering products that are moving augmented reality into the mainstream. That's why it's no surprise that Facebook, which is also focused on AR and tried to acquire the company for $3 billion several years ago, duplicates many of the smaller company's features.

Gathering information on an online target can be a time-consuming activity, especially if you only need specific pieces of information about a target with a lot of subdomains. We can use a web crawler designed for OSINT called Photon to do the heavy lifting, sifting through URLs on our behalf to retrieve information of value to a hacker.

By far the most significant development for AR in the coming months and years — the development that will drive AR adoption — will be our reliance upon the AR cloud.

Because timing is everything, the latest entry in the location-based augmented reality gaming sweepstakes, Ghostbusters World, has arrived just in time for Halloween.

Web 2.0 technology has provided a convenient way to post videos online, keep up with old friends on social media, and even bank from the comfort of your web browser. But when applications are poorly designed or incorrectly configured, certain flaws can be exploited. One such flaw, known as CSRF, allows an attacker to use a legitimate user's session to execute unauthorized requests to the server.

Command injection is a technique used by hackers to execute system commands on a server, usually via a web application or some kind of GUI. This can happen when an application provides some sort of functionality to the user involving the use of system commands. When the input is not properly sanitized, commands not originally intended to be run are allowed to be executed.

With the announcement of ARKit 2.0 at WWDC 2018, Apple is bringing some powerful new capabilities to mobile augmented reality apps this fall.

Selling alt-coins like Stellar (XLM) or Ripple (XRP) in exchange for more widespread coins like Ethereum (ETH) or Bitcoin (BTC) can be a daunting task if you're new to cryptocurrency. Though you'll still need to do your research to avoid potential disasters, Binance takes the hassle out of trading digital currencies on your smartphone.

Using Bitcoin (BTC) or Ethereum (ETH) to buy alt-coins like TRON (TRX), Stellar (XLM), or Ripple (XRP) can seem intimidating if you're new to cryptocurrency. Though you'll still need to do your research to avoid potential disasters, Binance takes the hassle out of trading digital currencies on your smartphone.

Google just bought a huge chunk of HTC for $1.1 billion. They're bringing in around 2,000 employees, mostly from the hardware division, and these folks will presumably work under hardware chief Rick Osterloh. There's a massive patent portfolio involved, too, so stop me if you've heard this before — Motorola, anyone?

Equifax reported on Sept. 7 that it discovered a breach on July 29 which affects roughly half of Americans, many of whom don't realize they have dealings with the company. Hackers got away with social security numbers, addresses, and driver's license numbers, foreshadowing a "nuclear explosion of identity theft." Let's explore what really happened and what you and those around you can do to protect yourselves.

Blowing dust and fungal spores are creating a public health problem that could be just a slice of what's to come with climate change.

OpenVAS is a powerful vulnerability assessment tool. Forked from Nessus after Nessus became a proprietary product, OpenVAS stepped in to fill the niche. OpenVAS really shines for information gathering in large networks where manual scanning to establish a foothold can be time-consuming. OpenVAS is also helpful for administrators who need to identify potential security issues on a network.

Nvidia's decades-long development of graphics processor units (GPU) for PCs has given it a major leg up in the driverless space.

There is an Indian story called the Legend of Paal Paysam, and while it doesn't seem like it at first, it has a lot to say about what motivated Paul Travers in the augmented reality space.

Tell the truth. The bat picture creeps you out. You are not alone. But in reality, bats truly are some of our best friends. They gobble thousands of disease-spreading bugs a night. But they also carry viruses that can be deadly to humans. So, bats — friend or foe?

It feels like someone reached into your chest and squeezed. Your head throbs in unison with your heartbeat. Clammy dread coats your body in sweat. Whether you call 911 or someone does it for you, the ER is your next stop.

We're nearly done getting our Mac set up for hacking. If you haven't checked out previous tutorials, I'd recommend you do so first before diving right into this one.

An average user's smartphone tinkering doesn't go much further than taking their phones out of the box, signing into their account, and installing apps. But some of us want more functionality and customizability than the basic experience provided by Android and iOS.

With T-Day on the horizon and approaching rapidly, you are probably in one of two camps. The one that is eagerly awaiting the holiday feast with barely-contained drool. Or the one that involves breathing heavily into a paper bag while worrying about your lack of oven and stovetop real estate, while also bemoaning the lack of multiples of you to get all the prep work done.

Without a comprehensive root method for all Android phones and tablets, a device-specific approach is needed. And since we always cover new rooting methods for all the popular phones here at Gadget Hacks, we've built this always-updated guide to rooting many mainstream Android devices.

Welcome back, my budding hackers! People often ask me, "Why are you training hackers? Isn't that illegal?" Although I usually give them a short version of this post, there are MANY reasons why YOU should be studying hacking.

Welcome back, my hacker apprentices! Although there is a multitude of different hacker types, the one target they all share is the database. I often refer to the database as the hacker's Holy Grail, or the ultimate prize for an effective hack.

TouchDevelop is a browser-based programming tool that allows anyone to build your own Windows 8 apps directly from any touchscreen device, including iPad, iPhone, Windows Phone, Android, PC and Macs. Once the script is created and the app proves to work, it can be placed in the Windows Store for free or purchase.

To learn how stop worrying involves regular fasting from fear, learning to plan without worrying and to accept the future as it comes. Part of a Yoga class on Rasa Sadhana, the Tantric practice of emotional fasting.

Watch this instructional sewing video to learn about the zip bind tool and how to adjust it for your quilting projects. This video provides a helpful introduction to this quilting tool. The zip bind tool is a sewing tool that makes quilt bindings perfect from end to end. There's no need for straight pinning and there's no measuring involved.

Watch this instructional video to make a mini glass mobile. You will need pliers, pieces of wire, some wire rings, and a fishing loop to attach the different pieces. The earlier processes involved melting wire to pieces of glass, but here we witness the fun part of making a mobile. With a small hand made S hook, the mobile can hang in any doorway or window frame.