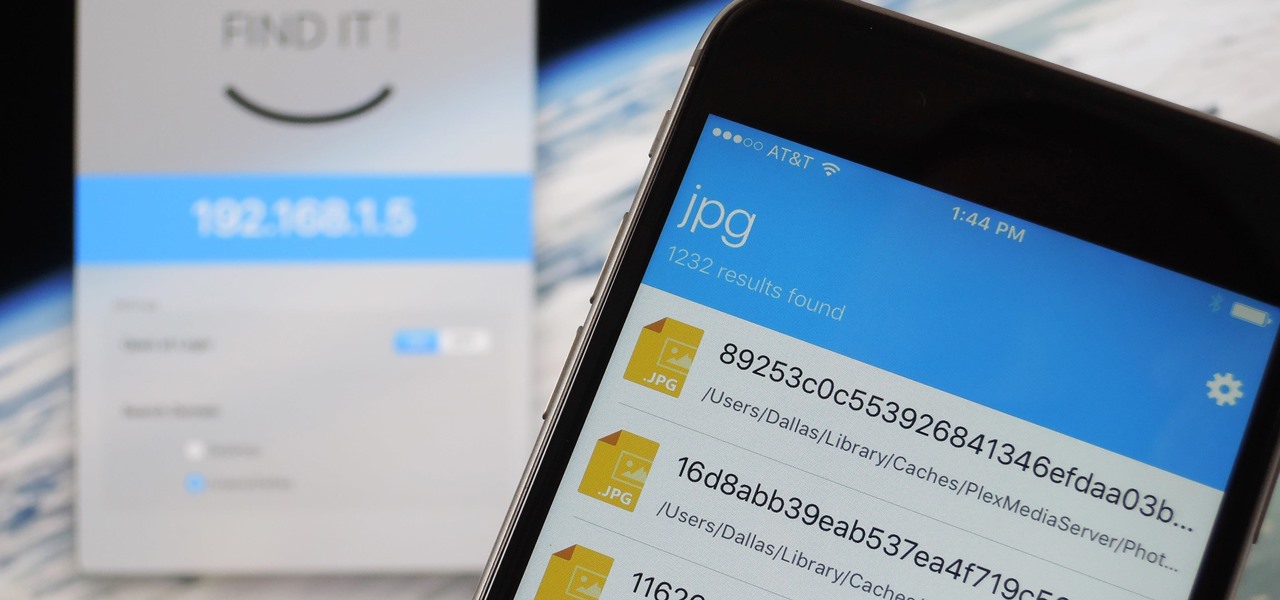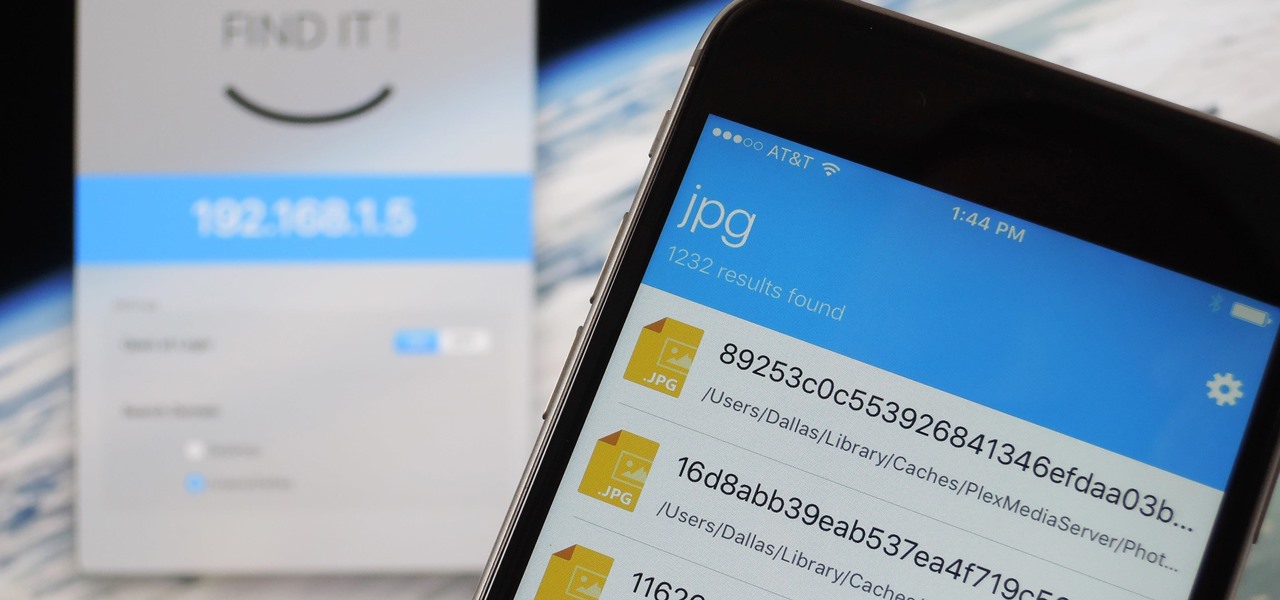
When it comes to sharing files between a smartphone and a computer, there are several solutions available for a Windows and Android pairing. But for those of us with Apple devices, the selection of apps in this category isn't quite as great. You can use AirDrop to quickly share files, but searching for files is not so easy.
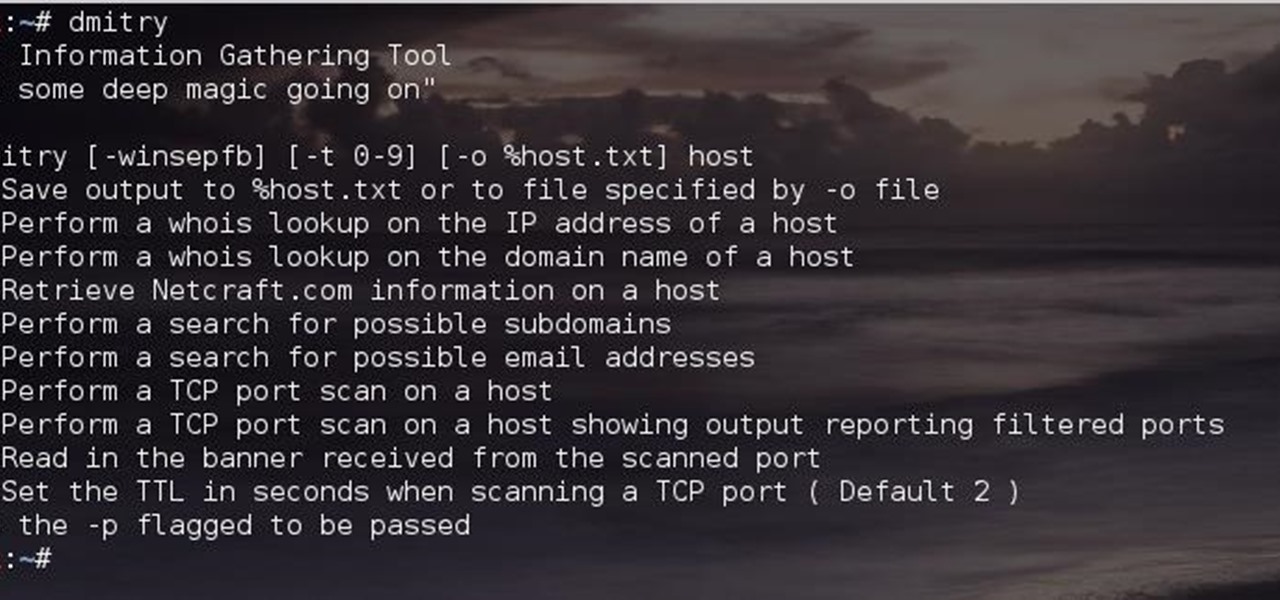
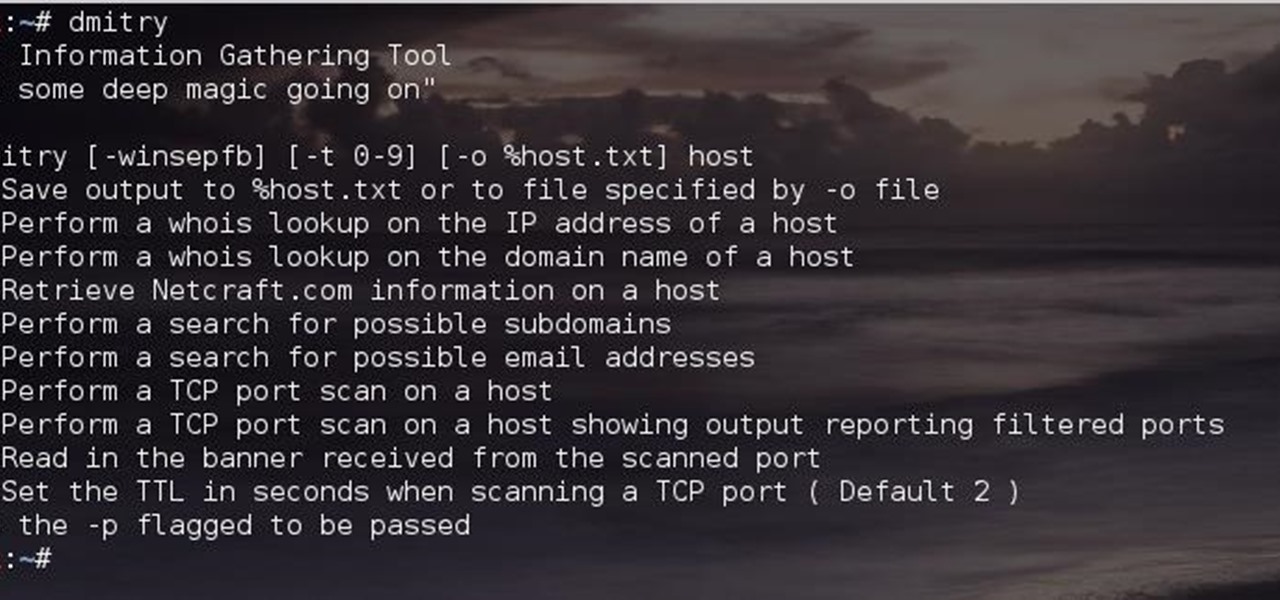
Greetings comrades! Great leader has ordered that we gain intel on a website owned by the opposition. For all general purposes we will be scanning nmap.org because they really don't care if Big Brother decides to perform a whois on their IP. We will be using Dmitry for the scanning.

This tutorial follows the same idea as my original tutorial for windows, but I've redone it to work with Mac OS X. Here's how to get a meterpreter session from your victim opening a malicious word document:

Welcome back, my tenderfoot hackers! As you should know from before, Snort is the most widely deployed intrusion detection system (IDS) in the world, and every hacker and IT security professional should be familiar with it. Hackers need to understand it for evasion, and IT security professionals to prevent intrusions. So a basic understanding of this ubiquitous IDS is crucial.
If you're using an up-to-date version of Google Maps on your Android device, there's a little-known feature you can use to apply stickers to saved places, making them visually easier to find while you're looking at the map.

In previous tutorials we have encountered these things called pointers and addresses but we still don't know what they really are. Let's learn a bit more to clear things up.

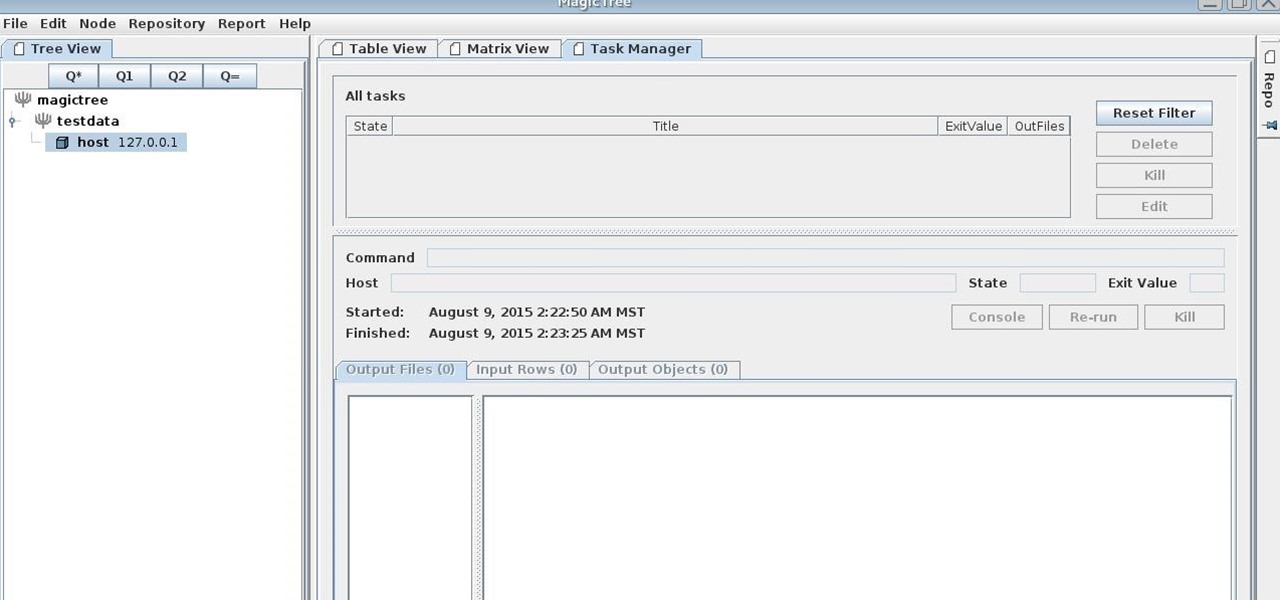
MagicTree is often the go-to tool for data collection and reporting for many pentesters. It organizes data in nodes in a tree-structure which is very efficient at managing host and network data. Reports can be completely customized to meet the user's needs. Also, MagicTree allows you to import XML data and has XSLT transforms for Nessus, Nmap, OpenVas, Burp, Nikto. MagicTree comes pre-installed in Kali.

In my last how-to, we built a man-in-the-middle tool. The aforementioned script only established a man-in-the-middle. Today we'll be building a tool to utilize it. We'll be building a DNS packet sniffer. In a nutshell, this listens for DNS queries from the victim and shows them to us. This allows us to track the victims activity and perform some useful recon.

Keeping your online data and identity private is an uphill battle, but with the anonymity network Tor, you have a pretty decent line of defense from prying eyes.

In most cases, when the free trial of software is over, that's it—you're left to either pay for it or find an alternative. But what happens if the trial wasn't long enough to sell you on the product? It'd be nice if there was a way to test it out again without having to whip out your credit card.

If you read my last tutorial on using SEToolkit, you probably know that SEToolkit is an effective way to make malicious actions look legitimate. But, that was only the beginning... the truth is, Metasploit and SEToolkit belong together, and help each other very well.

Let's say that we want to see what someone is doing on their computer? In this tutorial, we'll be hijacking cookie sessions to do just that!

First, I want to give credit to the author where I first found how to do this: Astr0baby's Blog. This article was dated, so I took the script on his page and reworked it to make it work today. (I also included the way to make it hide the cmd line popup.) Requirements

If you took a big step back and really looked at the world, you'd see how downright silly our nations look when they put up fences to separate themselves from one another. Creatures big and small roam free while respecting each other's space, but humans create borders and physical barriers to delineate their cultures.

One of the biggest improvements in Mac OS X Yosemite came to the Spotlight search feature, allowing users to not only search through their applications, but also their emails, text messages, iCloud, and the web.

Apps that have no business accessing the internet can share your location, device ID, and other personal information with potentially malicious data snatchers. If you're connected to the internet on your Nexus 7 tablet, you're a potential target for cyber threats.

In my last hack blog on crashing your roommates Win7 system, we started looking at client- side attacks. As promised, we will be looking at some more client-side attacks.

All of my hacks up to this point have been operating system hacks. In other words, we have exploited a vulnerability usually in an operating system service (SMB, RPC, etc.) that all allow us to install a command shell or other code in the target system.

If you're with AT&T and need to change wireless-user information, you can do it easily through the business mobility online customer portal, AT&T Premier. Whether you're needing to change email addresses, phone numbers or physical addresses, this is the place and way to do it.

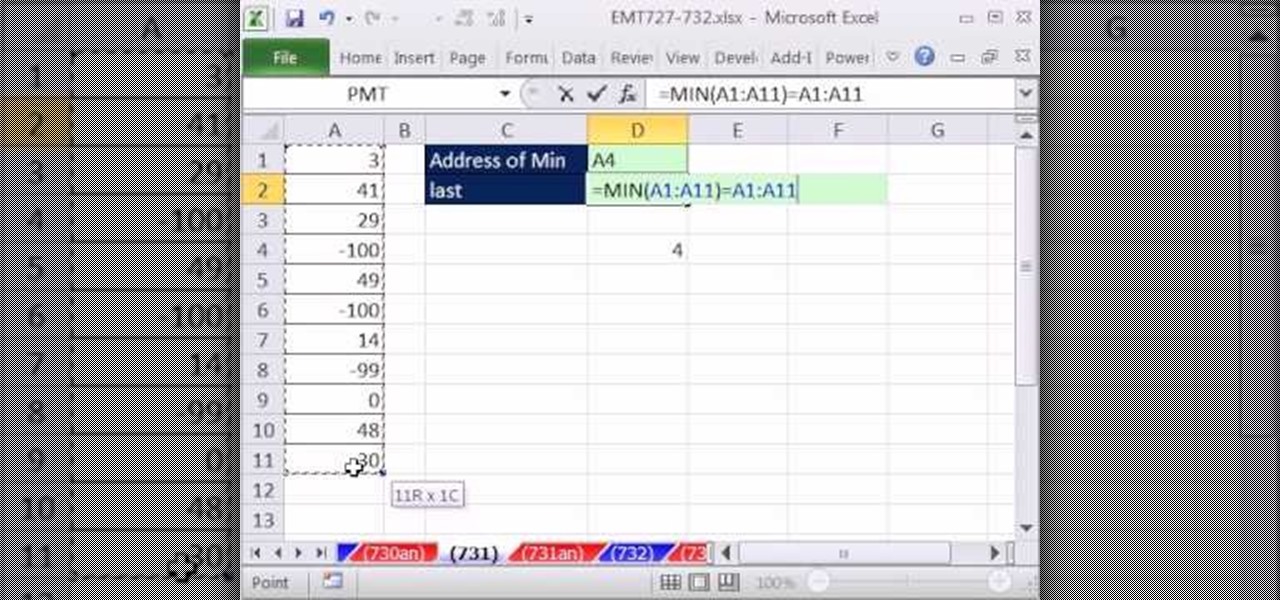
New to Microsoft Excel? Looking for a tip? How about a tip so mind-blowingly useful as to qualify as a magic trick? You're in luck. In this MS Excel tutorial from ExcelIsFun, the 730th installment in their series of digital spreadsheet magic tricks, you'll learn how to create a formula that will retrieve the cell address of the minimum value in column. To accomplish this, you'll use the ADDRESS, MATCH, INDEX, MIN, ROW and LOOKUP functions.

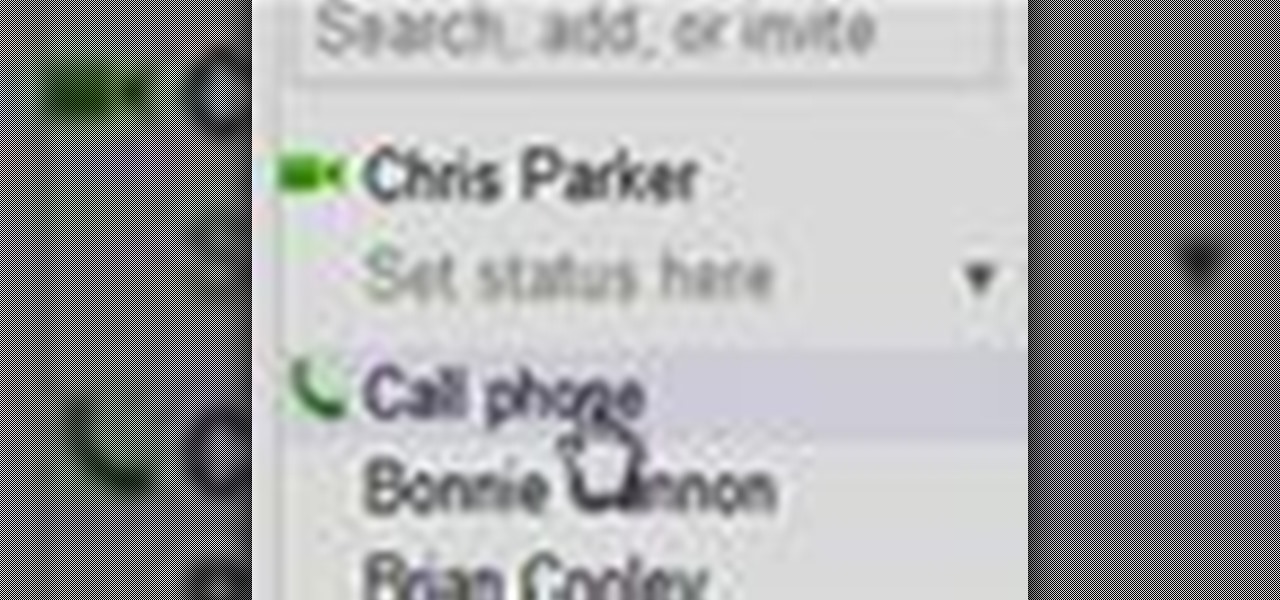
In this clip, you'll learn how to use Google's new VOIP (voice over IP) feature to make domestic and international phone calls from your Gmail inbox. For more information, including a complete demonstration of the process and detailed, step-by-step instructions, and to get started making calls from your own Gmail account, take a look.

In this clip, you'll learn how to make VOIP (or voice over IP) phone calls over your Windows PC. For more information, including a complete demonstration and detailed, step-by-step instructions, and to get started making phone calls over your own Internet connection, watch this handy home-computing how-to from the folks at CNET TV.

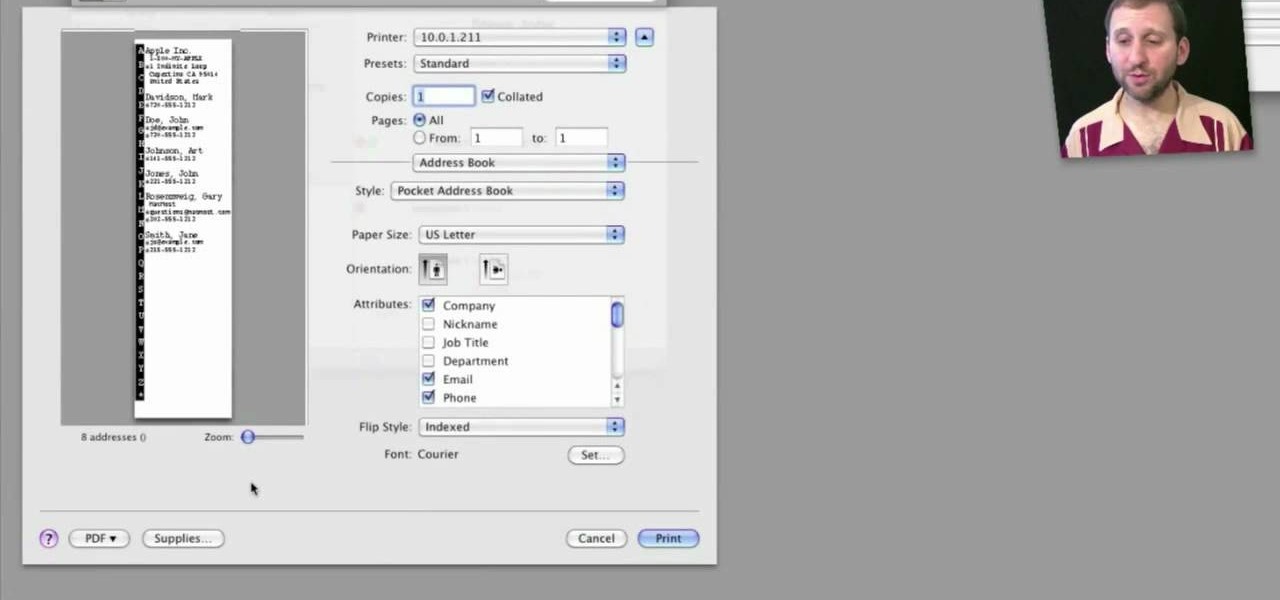
Looking for a quick primer on how to print from Address Book on a Mac OS X computer? It's easy! So easy, in fact, that this home-computing how-to from the folks at MacMost can present a complete overview of the process in just over three. For more information, including step-by-step instructions, take a look.

Want to find a friend on Facebook? Have their email address? Whether you're completely new to the Facebook's popular social networking site or simply require a small amount of clarification on how to perform a particular task on Facebook, you're sure to benefit from this helpful video guide. For more information, including detailed, step-by-step instructions on how to use Facebook's handy email search feature, take a look.

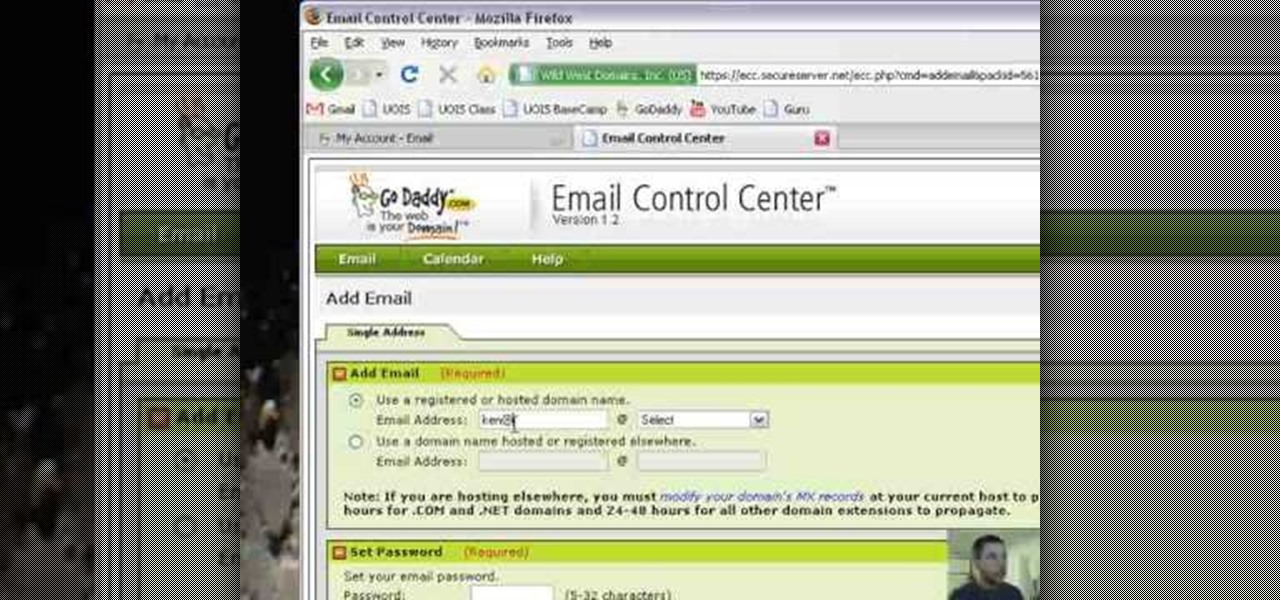
Want to set up a custom email account for a domain hosted by GoDaddy? It's simple. So simple, in fact, that this free video guide can present a complete overview of the email address creation process in just over three and a half minutes' time. For complete instructions, and to start using your own custom email addresses, watch this helpful how-to.

New to Microsoft Excel? Looking for a tip? How about a tip so mind-blowingly useful as to qualify as a magic trick? You're in luck. In this MS Excel tutorial from ExcelIsFun, the 363rd installment in their series of digital spreadsheet magic tricks, you'll learn how to create an array formula using the ADDRESS, MIN, IF, COLUMN & ROW functions that will return the address of the first non-blank cell in your Excel spreadsheet.

Here you will see how to add a contact to the address book of a Nokia N97. Follow these steps to add a contact to your Nokia M97's address book: From the home screen, tap the "Contacts" icon and then tap "Add New Contact". Enter in the contact information and tap "Done". Tap "Exit" to return to the home screen. To set a contact as one of your favorite contacts, tap "Add to Favorites", and select the contact you wish to add as a favorite. Tap "OK" You can also do things such as add a called ID...

Cashcroppimp teaches you how to open your XBox 360's NAT with Verizon Fios. You first have to find your IP address. For this, you simply point your internet browser to http://findmyip.com to find IP. This is also calling the default gateway. Make sure to write this down somewhere. Now you need to input this number in your internet browser. Enter your username and password and proceed to the next step. Now go to Firewall settings-DMZ Host. Here you will need the IP address from the XBox 360, w...

New to the Ubuntu Linux distribution and interested in setting up an address book for to keep track of your contacts? In this how-to, you'll learn how to make maximum use of the address book built into the Evolution email client. Take a look!

If you're putting your email address online on your own website, or sites like facebook or myspace, you may want to be a bit clever about it. Check out this tutorial and see how to protect your email address from spam.

Check out this video to learn how to search more effectively in the Google Chrome browser. This video will explain how to manually enter keyword searches in Google Chrome and Chromium, which will allow you to search using any engine from the address bar.

Your manuscript is complete, and you have a list of your favorite agents and a strong query letter... but how do you properly address letters to agents? You neither want to be too formal nor too casual - strike the perfect balance.

In this clip, you'll learn how to reinstall an accidentally-deleted system application like TextEdit, Preview, iCal, Address Book or QuickTime without reinstalling OS X. With a little know-how, it's easy. So easy, in fact, that this video guide can offer a complete overview of the process in a matter of a few minutes. For more information, including a complete demonstration and detailed, step-by-step instructions, watch this home-computing how-to from MacMost.

In this clip, you'll learn how to view the list of your previously searched addresses on MapQuest Maps. It's easy. So easy, in fact, that this home-computing how-to can present a complete, step-by-step overview of the process in about two minutes. For more information, including detailed, step-by-step instructions, take a look.

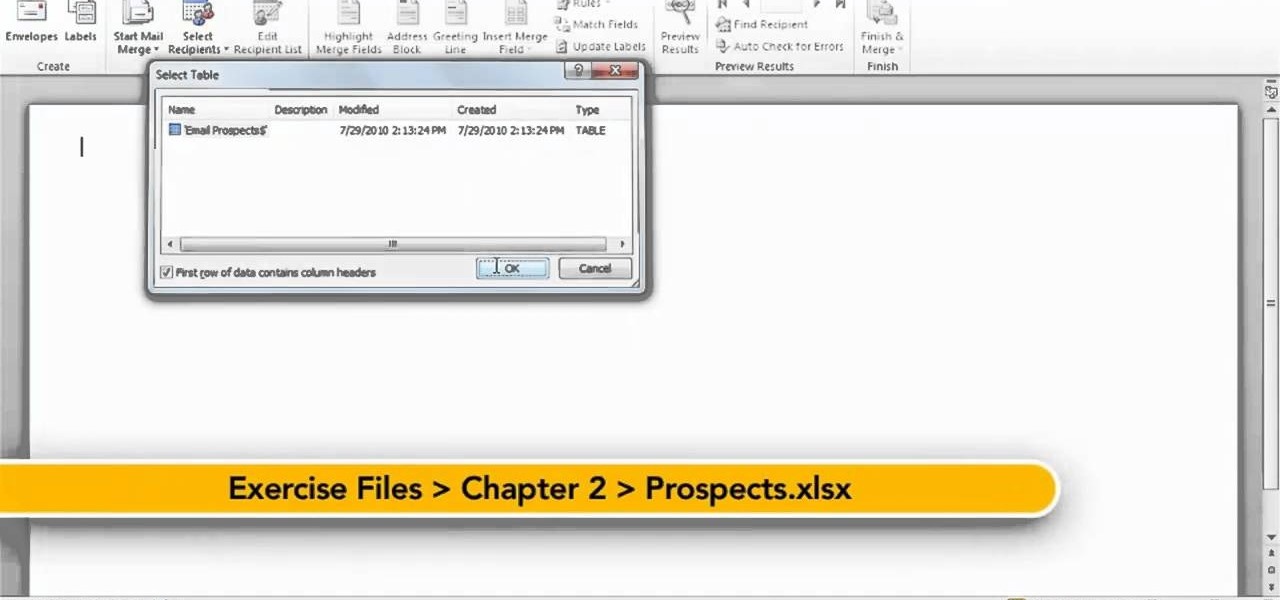
In this quick clip, you'll learn how to insert address blocks and merge fields when using Mail Merge within Microsoft Office Word 2010. Whether you're new to Microsoft's popular word processing application or a seasoned professional merely looking to pick up a few new tips and tricks, you're sure to benefit from this video tutorial. For complete instructions, take a look.

Trying to find your friend's Yahoo! mail address so you can send them a letter or tell them about a cool new website you found? Yahoo! directory makes it easy to find someone you're looking for. All you need is is their name.

Want to get involved with the information superhighway? E-mail is the best technology to stay connected with friends and family. Use these tips to create your own email account in Gmail, MSN or Yahoo! mail. Keep track of addresses, improve your networking and learn the basics of instant messaging.

Thwart would-be spammers by creating temporary, disposable email addresses at GuerillaMail. This clip will show you how it's done. It's simple! So simple, in fact, that this home-computing how-to can present a complete, step-by-step overview of the process in about two minutes. For more information, including complete, step-by-step instructions, take a look.

In this video tutorial, viewers learn how to get more room in a web browser. Users will need to use the Mozilla Firefox web browser. Begin by going to the Firefox add-on website and search for "status address bar". Then click on Add to Firefox to install the add-on. Once installed, any link that is moused over will appear in the address bar. This means that users are able to hide the address bar clicking on View and deselecting Status-bar. This video will benefit hose viewers who use the Mozi...

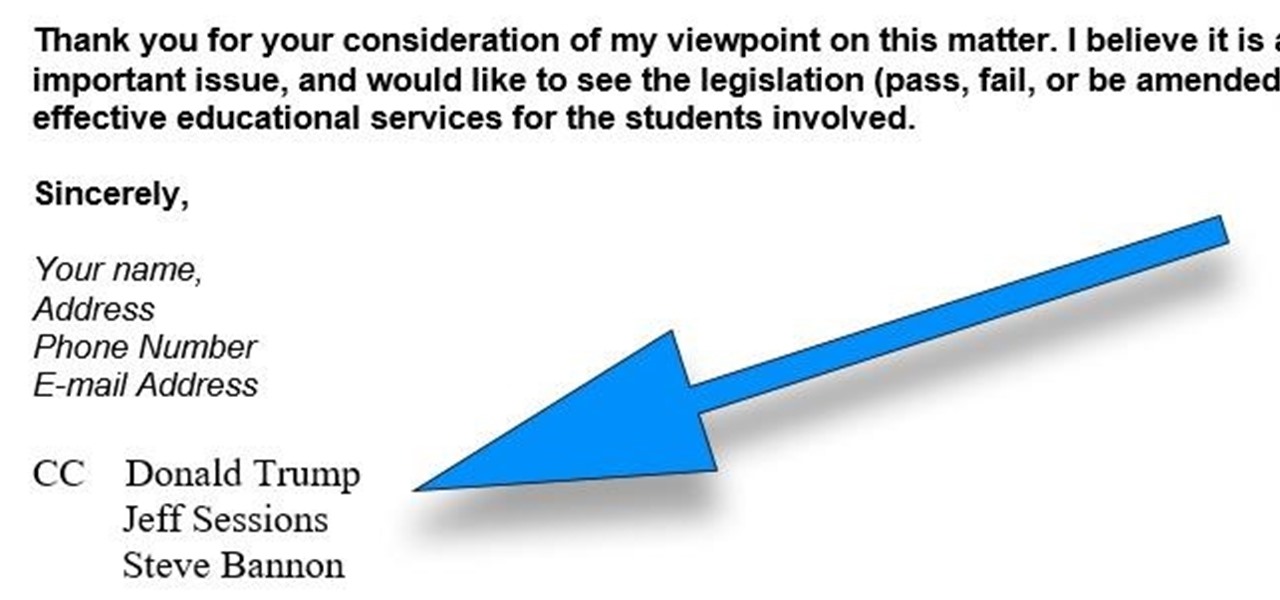
CC, which stands for "carbon copy", is a familiar phrase in email, but can also be used in business letters and legal documents. This can be especially useful for letters you want to spend up a company or organizational chain, letting each recipient know exactly who else received the same document.