YouTube's massive user base comprises almost one third of all people on the internet, and collectively, users spend well over 100 million hours on the site watching billions of videos each day. Add it all up, and this means that YouTube is viewed by more people than any U.S. cable network—making it by far the favorite "TV station" of the internet generation.

Welcome back everyone. As many of you know, reconnaissance is extremely important in any successful hack. Without proper reconnaissance, we won't know what we're about to get into, literally.

This is my first How-To on Null-Byte, so I hope it's not too complicated written, because I am not a native english speaker. I don't use pictures, but this Tutorial is a good supplement for my updated Tutorial here.
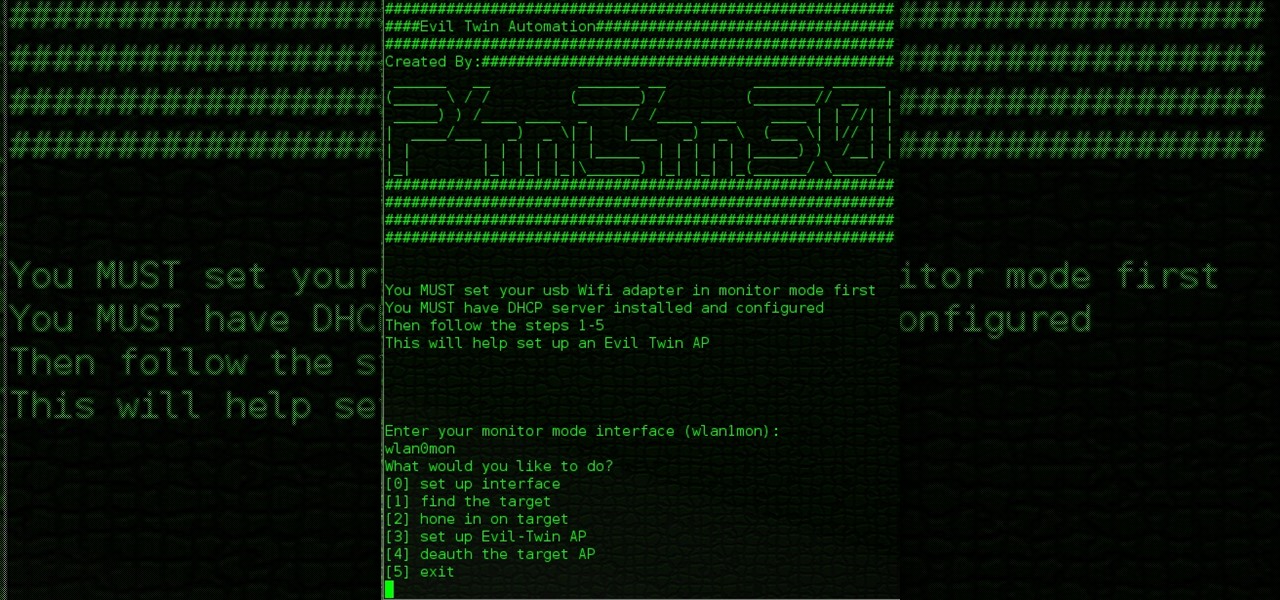
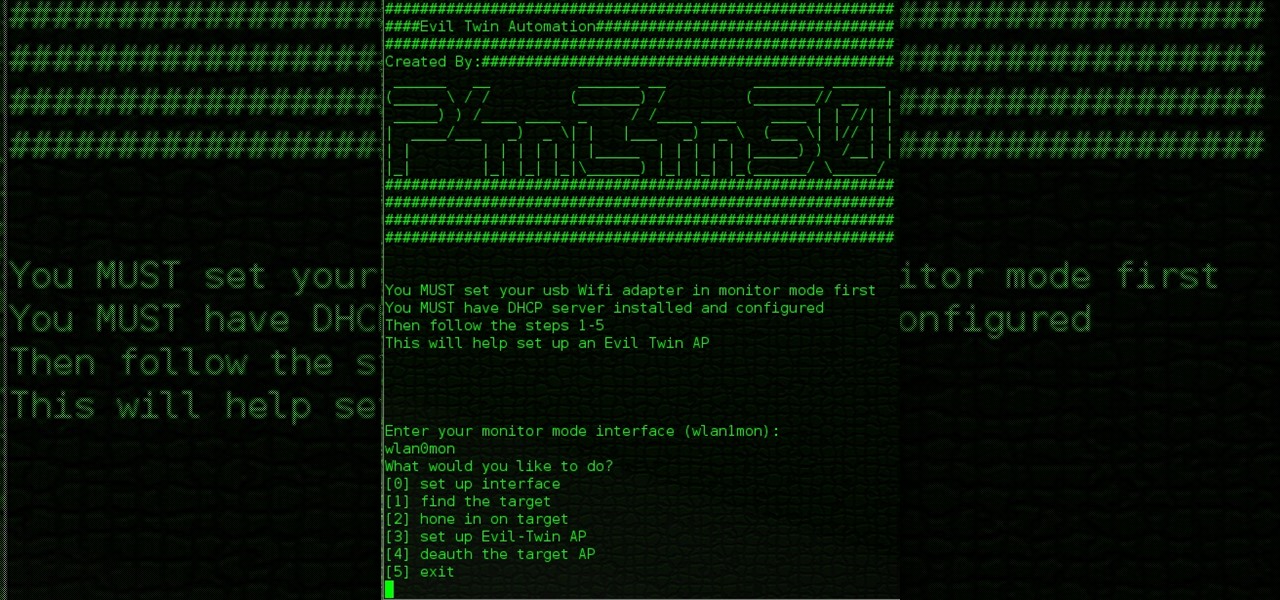
Hello All, So to recap in part 1 I went through setting up the dchp server. Part 2 detailed the bash script. Now in part 3 I will post the entire bash script. I am doing this in its own post because Part 2 is just way to much info on one post IMO.

Welcome back, my nascent hackers! In the conclusion of the Mr. Robot television series, Elliot and fsociety successfully completed their mission of encrypting all of Evil Corp's data with AES-128 encryption and destroying the key.

welcome back my masters , teachers and classmates , in this second part of this 0-day series we will learn the basic of fuzzing, and i bought some gift for nullbyte(a 0 day vuln that will be released today exclusively on null-byte) .

SET is great when you have a short space of time at hand, however sometimes you want to know whats actually going on under the hood or have found a site you can't clone with SET.

Whether it's the start, middle, or end of summer, it's prime-time grilling season. If you find yourself without a grill, however, it may seem as if half your summer plans of swimming by the pool while stuffing hot dogs in your face could be ruined.

NOTICE: Ciuffy will be answering questions related to my articles on my behalf as I am very busy. Hope You Have Fun !!!

Edit: Some of the methods I show you may be difficult, or not work at famous or high quality hotels.

Welcome back, my tenderfoot hackers! Those of you who have been reading my posts here for awhile know how much I emphasize good reconnaissance. Novice hackers often jump into a hack/exploit without doing proper recon and either fail or get caught. Experienced and expert hackers know that 70-80 percent of a good and successful hack is dependent upon successful and accurate reconnaissance.

Welcome back, my greenhorn hackers! In previous Wi-Fi hacking tutorials, I have shown you ways to create an Evil Twin, to DoS a wireless AP, and to crack WEP and WPA2 passwords, but in this tutorial, I will show you something a little bit different.

Welcome back, my greenhorn hackers! In my continuing effort to demonstrate to you how to hack the ubiquitous Windows 7, we will going after that notoriously vulnerable Adobe Flash that is on nearly every client Windows system (you are not likely to find it on servers).

Welcome back, my greenhorn hackers! After the disaster that was Windows Vista and the limited and reluctant adoption of Windows 8 and 8.1, Windows 7 has become the de facto standard operating system on the desktop/client.

Welcome back, my greenhorn hackers! In a previous tutorial on hacking databases, I showed you how to find online databases and then how to enumerate the databases, tables, and columns. In this guide, we'll now exfiltrate, extract, remove—whatever term you prefer—the data from an online database.

Welcome back, my hacker apprentices! In recent weeks, the revelation that the NSA has been spying on all of us has many people up in arms. I guess I take it all in stride as I just assume that the NSA is spying on all of us—all of the time. Don't get me wrong, I don't condone it, but I know the NSA.

BitTorrent—corporations hate it with a passion, but the people love it. The notorious file-sharing protocol was responsible for 36.8% of all upstream Internet traffic last year, as well as 10.3% of all traffic.

When I left off on our last hack, we had hacked into the ubiquitous Windows Server 2003 server by adding ourselves as a user to that system so that we can return undetected at any time. The problem with this approach is that a sysadmin who is on their toes will note that a new user has been added and will begin to take preventative action.

iPodTouchedMaster shows how one can easily SSH into their iPod Touch with all firmware! To SSH is the ability to hack into your iPod Touch's file system. First, your iPod Touch must be jailbroken. Next, you'll have to open Cydia. Click "Featured Packages" or search for the terms "Open SSH" (it will be listed under Console Utilities & Daemons). When you have OpenSSH click on it and click 'Install' and 'Confirm'. After this is finished, click return to 'Cydia'. This may take a lot of battery po...

Is your BFF getting married? Looks like you have a bridal shower to plan! Organize a bridal bash that people will actually want to attend using these innovative ideas.

Eagle Lake Woodworking, hosted by John Nixon, offers great do-it-yourself guides for building your own furniture, especially in the American Arts and Crafts style, and turning your garage into an amateur woodshop. Search Eagle Lake on WonderHowTo for more carpentry tutorial videos. From Eagle Lake Woodworking on this specific lesson:

Watch this video tutorial to learn how to book the best hotel room for your money. You've spent all year saving up for your dream vacation. The last thing you want is to end up in a hotel room that ruins the whole trip.

Work the butt, thighs, and hips with this quick resistance band exercise. Watch this how to video as our host demonstrates how to positions the band to get a lower body workout. Tone every inch of the inner and outer thighs with resistance bands.

The town of Westville hosts a blacksmith conference in this video metalworking tutorial. One of the smithies demonstrates how to put an edge on a tool and how to twist steel. Watch this instructional video and learn how to craft metal tools and how to twist steel.

Learn how to a fold napkin into an atrium lily with this tutorial. This is a perfect way to decorate your table when hosting a fancy dinner party. Impress your guests with your napkin folding skills with this easy and beautiful atrium lily.

Learn how to fold a napkin into a rosebud with this tutorial. This is a perfect way to decorate your table when hosting a fancy dinner party. Impress your guests with your napkin folding skills with this easy and beautiful rosebud.

Learn how to fold napkin into a candle with this tutorial. This is a perfect way to decorate your table when hosting a fancy dinner party. Impress your guests with your napkin folding skills with this easy and beautiful candle.

Learn how to fold napkin into a goblet fan with this tutorial. This is a perfect way to decorate your table when hosting a fancy dinner party. Impress your guests with your napkin folding skills with this easy and beautiful goblet fan.

Learn how to fold napkin into a fan with this tutorial. This is a perfect way to decorate your table when hosting a fancy dinner party. Impress your guests with your napkin folding skills with this easy and beautiful fan.

Learn how to fold napkin into a rose with this tutorial. This is a perfect way to decorate your table when hosting a fancy dinner party. Impress your guests with your napkin folding skills with this easy and beautiful rose.

Learn how to fold napkin into a bird of paradise with this tutorial. This is a perfect way to decorate your table when hosting a fancy dinner party. Impress your guests with your napkin folding skills with this easy and beautiful bird of paradise.

Learn how to fold napkin into a pyramid with this tutorial. This is a perfect way to decorate your table when hosting a fancy dinner party. Impress your guests with your napkin folding skills with this easy and beautiful pyramid.

Forget the take out tonight. Watch this how to video and learn to cook some Korean style food. In this particular video our host shows you how to make Korean style stir fried squid.

Learn how to combat the stresses of modern life and get better sleep through meditation with this tutorial. In this how to video, Roni Proter, host of Simply Beautiful on Veria TV, explains the benefits of meditation. Follow the tips in this video and you will be sleeping better in no time

Learn how you can combat the stresses of modern life through meditation with this how to video. Roni Proter, host of Simply Beautiful, explains the benefits of meditation. Watch this tutorial and you can reduce stress and improve your health with meditation.

Shed those dead skin cells with homemade lip exfoliant. Using safe and natural ingredients, Roni Proter, host of Simply Beautiful, makes a gentle lip exfoliant. All you need is sugar and olive oil. Watch this how to video and you will have smoother, softer lips in no time.

Learn how to ease the discomfort from menopause with this tutorial. Amanda McQuade Crawford, medicinal herbalist and host of What a Relief!, offers safe, herbal treatments for menopause. Watch this how to video and you will know what foods to avoid and what foods to take in during menopause.

You can prevent joint pain with vitamins and supplements. Amanda McQuade Crawford, medicinal herbalist and host of What a Relief, discusses natural remedies such as fish oil, SAM-e and garlic for joint pain. Watch this how to video and you will soothe your aching joints in no time.

Learn how you can alleviate the symptoms of menopause through meditation with this how to video. Kurt Johnsen, host of Yoga For Life, shares how using this technique can alleviate hot flashes and improve your overall well-being. Watch this video and you can have a more comfortable menopause.