Smartphones are now indispensable when traveling. Domestic and overseas travel alike require food, navigation, translation, and so much more to make work or vacation successful. Gone are the days of lugging multiple tourist books around with you everywhere you go — you need to let your smartphone handle the dirty work.

Your social security number, credit card information, and medical history can fall into the wrong hands if you're not careful about how and where you share your data online. If you really care about your data, there are tools and techniques you can utilize to protect yourself from cyberstalkers, advertisers, and hackers in a time when digital lives are a high commodity.

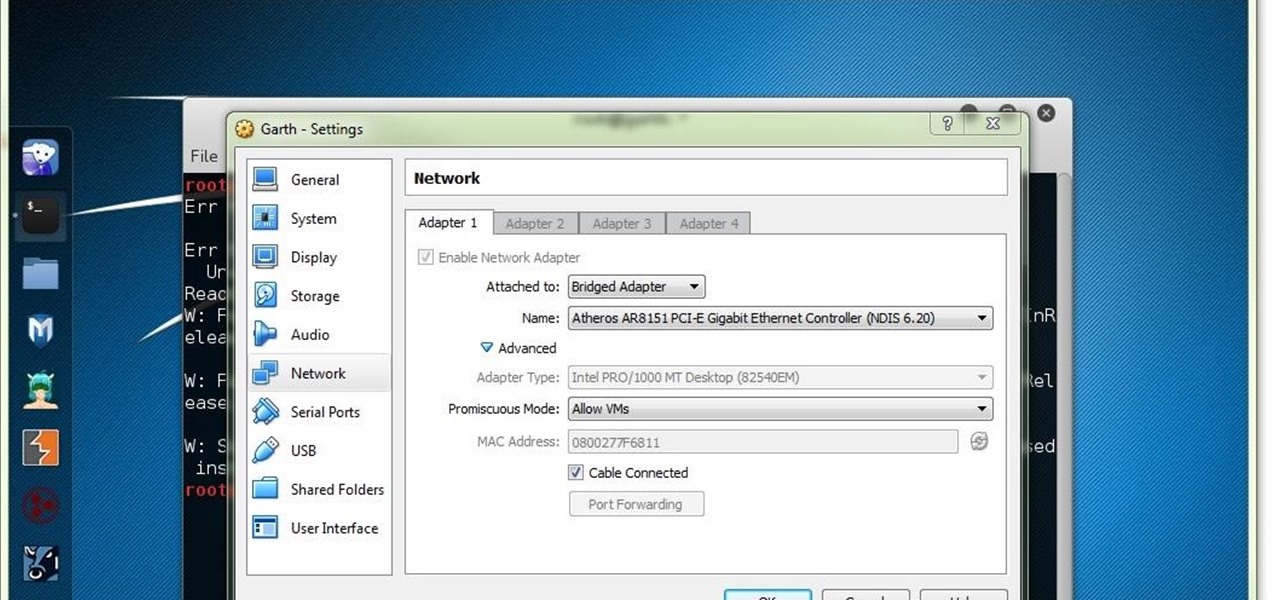
Besside-ng is the hidden gem of the Aircrack-ng suite of Wi-Fi hacking tools. When run with a wireless network adapter capable of packet injection, Besside-ng can harvest WPA handshakes from any network with an active user — and crack WEP passwords outright. Unlike many tools, it requires no special dependencies and can be run via SSH, making it easy to deploy remotely.

In this video magician David Zanthor shares an age old magic trick. You will need a willing human, a deck of cards, a rubber band, two identical coins and skills. The trick? It involves Ing Ping Ching energy and it is quite involved...so you will have to watch the video! Do the Ing Ping Ching magic trick.
In this tutorial we will be go over how we can make use of conditionals. In Perl the main conditional is the if statement. The if statement in
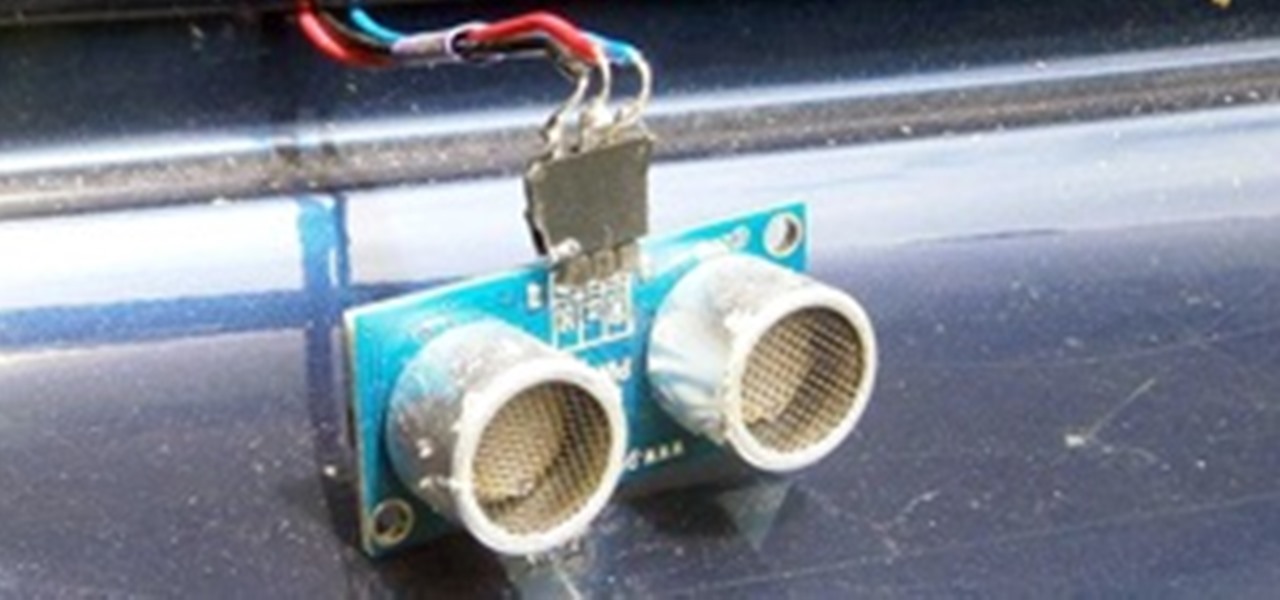
Today's fancy cars come with all sorts of options, from power mirrors to working seat belts. Some of us condemned to live in the reality of capitalist recession have no car, or perhaps a very modest one. But your modest car can still have some cutting edge technology wedged into the trunk and dashboard if you know what you want and where to look for parts. Today, we make a parking sensor using a sonic range finder, just like in the vehicles our owners drive!

Info Summary: Website: EducateTube.com | Your Host: Sipski

Here is the amazingly original social network trailer Here is a parody of that trailer done for ping. Its amazing what a single track of music can do to create the feeling of a trailer.

Hello y'all! I apologize if this question has been solved somewhere else, but I have looked around on Google, Yahoo, and Null Byte and have not been able to find any working solutions.

Office workers beware, or a snarky robot may unleash a barrage of ping pong balls upon you. A somewhat sinister individual from the CKBot group at UPenn’s Modlab concocted the prank.

Even if you live in a big city, chances are you have some wild raccoons or foxes that cannot abide a vertical trash barrel. While apparently omnipresent, these phantasmic critters usually vanish in the night leaving only a shameless trail of refuse you never wanted to see ever again. While I haven't found a way to stop them, I can help you snap some photos of the dastardly creatures.

Arduino fashion (essentially, electronic textiles that can perform a variety of functions) is certainly not a new idea, but the Ping social networking garment brings a fresh and exciting perspective to the concept.

Math is unreasonably effective in describing the natural universe. Anyone who's seen Walt Disney's Donald in Mathmagic Land knows this to be so. Well, the axiom works in reverse, too: The physical stuff of the universe can model math right back. And to great effect.

This instructional video demonstrates how to make a Muppet style puppet. You will need markers, scissors, tape, a hot glue gun, spray paint, spare fabric and foam, and two ping pong balls for the eyes. Make a Muppet.

Giveaway Tuesdays has officially ended! But don't sweat it, WonderHowTo has another World that's taken its place. Every Tuesday, Phone Snap! invites you to show off your cell phone photography skills.

From California is a Place, a portrait of young ping pong Olympic hopefuls at the ICC in Milpitas, California. These kids practice 10 hours a day.

Mad Eye Moody's magical eye from "Harry Potter and the Goblet of Fire" is a character all its own, moving freely and seeing what to others is hidden, especially when it comes to student mischief.

In this article, I'll show you how to make a portable prank stun-baton. Powered by static electricity, simply charge up the baton, and discharge it for a static surprise. The concept behind this device ties in with Leyden jars, and their tendencies to retain static electricity.

SHAITAN n pl. -S an evil spirit 60 points (10 points without the bingo)

Get ready to turn an ordinary flip top garbage into a garbage eating monster! You will need a flip top garbage pail, faux fur, glue, scissors, 2 ping pong balls, a large pompom, 3 colors of felt, a black marker, 2 googly eyes, double stick carpet tape, and cotton stuffing. Follow along with the step-by-step instructions in this video activity tutorial and learn how to make a trash mouth trash can. Make a trash mouth trash can.

In this article I'll show you how to make a simple IP address notifier. The program will text you your new IP address, in the event that it changes. For those of you with dynamic IPs, this is very useful. I'm constantly frustrated when my IP changes, and it's handy to be notified via text when it happens. To use the program, you'll need Python 2.7 or later, urllib2, and a program called "text" (see this article here to get it).

Slow motion isn't just for blockbusters and indie films. Sometimes it's for pure wonderment, like the bullet that seems to melt away at impact, the chemical burning of phosphorus and gelatin on the head of a match, and the distorted skin and disgusting sweat being thrown from a punched face.

This project has been posted on Vimeo for the past two years, and somehow has just entered my radar now. Get this: A robot is manned by a Madagascan hissing cockroach. Each movement the roach makes (perched atop a trackball type ping-pong ball) controls the movement of the robot.

15Do not be feared by the title. It's for a structure i'm building at the moment!

You can try and try, but all the practice in the world can't compete with this robotic hand's pen spinning skills.

The already robust and ingenious Nmap tool has received a whole slew of new scanning scripts that can be used to do all sorts of naughty endeavors. Notably, the SQLi module, since it is a necessary evil that we must cover here at Null Byte. This major update is going to fuel today's lesson.

Welcome to the second Goonight Byte! Our second coding session was kindly hosted by th3m, so props to him for letting this happen.

Our first Community Byte went well! We had around 8 people in the room coding collaboratively and watching to learn. LukeStav did the kind task of hosting it on Gobby for all of us, so big thanks to him!

Dogs are a cartoonist's best friend because it's funny to see them in every day situations. So grab some paper and a pen and get ready to draw your own cartoon dog.You will need a pad of paper, pencil, a marker, colored chalks or colored pencils, and an eraser. Make a shape like a thick boomerang or bent sausage. On the left end, draw a giant oval for a nose, leaving a white space to show shininess. Draw the eyes large and round like 2 ping pong balls, one a little bit behind the other. This ...

About Today's topic Today we will talk about diagnosing and fixing connection problems. Let's face it - the truth is everyone who uses a computer and has an internet connection will have to deal with this at some point. Connection problems often occur at the wrong time and it is a real pain.

Destroy Black Ops Noobs First of all, these tips are great for any consoles that run Black Ops. Whether it be your Sony PS3, Nintendo Wii, XBox 360 or your PC.

Pranks are fun, but finding a way to maximize the affect of a prank can be tricky. Toilet papering the whole campus or repainting all of the parking spaces slightly smaller can take a long time and a lot of resources. A better plan of attack is to booby trap the choke points where your victims are forced to pass through. Think like a guerrilla. A dorm doorway is a good idea.

Giveaway Tuesdays has officially ended! But don't sweat it, WonderHowTo has another World that's taken its place. Every Tuesday, Phone Snap! invites you to show off your cell phone photography skills.

Encryped traffic and tunneling is a must when away from home to keep you and your information safe. SSH tunnels can be slow, and are heavily encrypted. VPNs are an all port solution, and proxies are just not what we need in most cases. Then, there is Tor.

Working from home is already challenging. Add the threat of a cyberattack into the mix, and the situation gets even hairier.

Goooooooooodmorning/day/evening, my favorite minecrafters! I told you to build a ruin, and so you did, so here are the winners of the weekly challenge!

So there have bine added some new stuff into Minecraft. Some new mobs that i will show here and some new blocks.

A phoney word in a game of Scrabble is basically a non-valid word, either played or considered being played. Why? To fool the other player and go from losing to winning. It's perfectly acceptable in Scrabble play, but only if you don't get caught. If the other player challenges your play, then you'll be forced to remove it and your turn will be skipped. That right there—not fun.

Giveaway Tuesdays has officially ended! But don't sweat it, WonderHowTo has another World that's taken its place. Every Tuesday, Phone Snap! invites you to show off your cell phone photography skills.