If you're on the hunt for a profitable side-gig, or even a completely new way to to make money, you'll want to take a look at Upwork, a leading freelancing platform that connects skilled freelancers with clients from all over the world.

BlackBerry has formally unveiled its latest flagship, the KEY2, during an exclusive event in New York. The Android-powered KEY2 retains its distinctive BlackBerry aesthetics with a physical QWERTY keyboard. Here's all the juicy details regarding Blackberry's followup to the venerable KEYone.

Unlike many browsers, Firefox gives a lot of control to the user. By default, Firefox does a great job of balancing security and performance. However, within the app's settings, you can modify options to shift this balance in one direction or another. For those looking to shift it toward security, here are few suggestions.

As of 2016, there are approximately 1.85 billion Android smartphones worldwide. This growing popularity has led to an increasing number hacks and cyber attacks against the OS. Unfortunately, Android users need more protection than what is offered by Google. The good thing is that there are a number of options available.

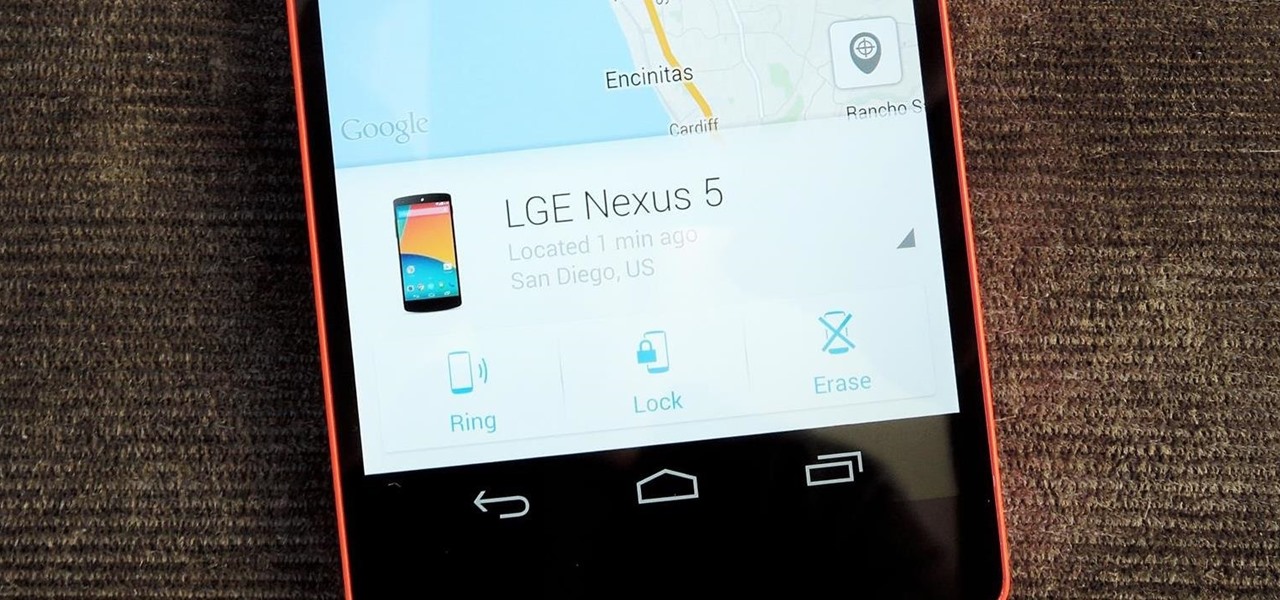
As smartphone users, we live in dangerous times. The value of phones continues to rise, making them prime targets for thieves. In 2015, the FCC estimated that one million phones are stolen each year, and with several devices starting to hit the $1,000 mark now, these numbers are sure to rise. But what do you do if you fall victim to phone theft?

It seems like there's a cyber security scare every day. Consumers are growing increasingly concerned about the safety of their accounts, and they have reason to be. Hackers will maliciously attack you anywhere — and we mean anywhere — they can to get your private information.

The photo-centric Instagram app is a great way to share "evergreen" pictures and videos when compared to Snapchat and Facebook's new Messenger Day feature. But like all social media, keeping the account secure is an essential aspect, as it restricts unwanted viewers from seeing your content and can prevent unauthorized users from accessing your account. Instagram has several methods for locking down the account including a new two-factor authentication (2FA) mechanism.

Google's monthly Android security updates are generally welcome—at the very least, they provide a feeling of security that our device is now somewhat safer than it was 30 days ago. Vulnerability patches, slight enhancements to performance, and overall bug fixes are generally included in the monthly OTAs, but as it turns out, they're not always for the better.

Smartphones have been around for nearly a decade now, so we've had plenty of time to develop preconceptions and bias. People that have never owned an iPhone will tell you that Apple devices are restrictive and bland, while others might say that stock Android is boring compared to manufacturer skins like HTC's Sense, despite never having owned a Nexus or Pixel.

When Google released the Nexus 5X and Nexus 6P, they added official support for fingerprint scanning to Android's main code base. On the surface, this was done to ensure that the fingerprint scanner in their own devices could be used to its full extent, but because it was added to AOSP, this meant that the new Fingerprint API could be used by any Android manufacturer.

If you keep sensitive data on your phone, you've surely considered a "lockout" app before. There are many such apps that can add an extra layer of security to other apps within Android. For instance, you can require a PIN or password before anyone is able to launch a particular app.

Back in August, Google introduced Android Device Manager. This new service allowed you to locate, lock, or wipe a lost or stolen Android device from either a companion app or a web interface. Effectively, this is the "kill switch" that legislators are clamoring for.

Welcome back, my aspiring hackers! In previous tutorials, I have shown you how to scan the globe for vulnerable servers and write simple scripts in BASH and Perl to perform other reconnaissance tasks. In a very recent guide, I taught how to scan vulnerable servers for Heartbleed.

Welcome back, my hackers novitiates! As you read my various hacking tutorials, you're probably asking yourself, "What are the chances that this hack will be detected and that I'll land behind bars, disappointing my dear mother who already thinks I'm a loser?"

Welcome back, my fledgling hackers! Awhile back, I demonstrated one of my favorite little tools, netcat, which enables us to create a connection between any two machines and transfer files or spawn a command shell for "owning" the system. Despite the beauty and elegance of this little tool, it has one major drawback—the transfers between the computers can be detected by security devices such as firewalls and an intrusion detection system (IDS).

Back in 2010, iOS developer Daniel Amitay developed a camera security app for iPhones that used an unlock screen almost identical to that of the iPhone.

In this Business & Money video tutorial you will learn how to make a successful curriculum vitae or resume. This is the first step in getting your dream job. A well written CV captures the interest of the person who is reading it. Think yourself as a product and the CV is a piece of paper that is going to sell you. Don't be afraid to sell your skills and abilities. If you don't do it, nobody else is going to do it for you. First thing on top is to put your name; centered and bold. Then leave ...

This video explains how to answer one of the five toughest job interview questions, this one being "what are your greatest weaknesses?" In it John Heaney of "The Job Shopper" explains that the most important thing about this question is to realize that answering in a way that really paints a negative picture of yourself will negatively impact your potential employment.

Want to fulfill your dream of becoming an ice cream truck driver? If the idea of rolling around in the sunshine selling ice cream sounds good to you, here's what you need to do.

Many axle bearings must be pressed on, and it's a fairly simple job if you have a press available. But if you don't have a press, try this little trick to get the job done. All you need is a coffee maker. Yep, that's right. Make yourself a pot of hot joe, and when it's done, place the bearing on the heating element. By the time you finish the cup of hot coffee, your bearing should be hot enough to expand. This could work for any vehicle!

One of the coolest jobs on Earth is probably a travel filmmaker, right? You get to go around the world and video tape it for all to see! In this video, learn the best tips for making a professional level video that you can show to all your friends. Never bore your family with a vacation video again with this helpful advice.

According to Outer Banks, cleaning coins found on the beach is an easy job. First of all he doesn't clean pennies as he doesn't think its worth the time. First use a rock tumbler. They're not expensive and cost under $100.00. Toss the coins in a tumbler with small rocks or gravel as this helps clean and separate the coins. Use a couple of squirts of dishwashing liquid and water about 3/4 full. Let it tumble about three to four hours. Using a colander rinse your coins once tumbling is complete...

This video shows how to wrap an ankle with athletic tape. First he sprays a little spray adhesive on the ankle and sticks a couple thin pads on places that are prone to blistering. He then wraps the foot and entire ankle with a prewrap to protect the skin and cover the hair so that the tape won't irritate the skin. Then he begins by taping two anchors around the top of the ankle, and putting a piece of tape down the side from the anchors, under the heel, and up the other side like a stirrup, ...

In this video, you will learn how to wear a bold flower print skirt in three different ways for going to school, a job interview or going out to a club.

This Diet and Health video tutorial will demonstrate to you how to do an ankle tape job. Take two pads and put them on top and back of the ankle with the toe facing up. Then take the tape and pull it tight. Start about two to three fingers below the calf. Wrap the tape nice and tight around the leg going round and round all the way down to the ankle. Then dive down under the foot and come around under the back of the heel and cut it off. Now you put the first anchor right around the foot. The...

Dominick from AskMeDiy demonstrates what he says is the right way, and the easy way, to clean your tile grout.

A boxer knows that during and after a fight, their bodies will be aching. As a part of the job, they grit their teeth, focus and get past the pain. The most important part of a boxer's body, though, is arguably his hands. A boxer depends on his hands to win fights and to train. The best thing one can do to protect their hands is to wrap them properly. This video will show you exactly how to wrap your hands so that they are cushioned and protected against injury. An ideal wrapping job would pu...

In this follow up video from Lowe's home improvement series, Mike Kraft demonstrates how to install hardwood flooring in your home. If you haven't watched it yet, be sure to check out the video on how to prepare your subfloor for installation of hardwood or laminate flooring, to be sure that your flooring lasts. In this video Mike provides a detailed list of the tools you will need to get this job done right, as well as some great tips on how to prepare your materials to guarantee a job well ...

Anyone can paint a room, but can you do it like a professional? Attention to detail and overall care are the key factors in getting the best paint job for your room. In this video you will learn exactly how to paint a room in your home like a professional.

There are many ways to remove an image from its background in Photoshop and using the filter tool is probably the easiest way to do the job. In this detailed video you will learn to use the Extract Filter in Photoshop to take a portion of an image and remove it from the background.

A cover letter is a quick description as to why this resume is better for a particular job position than all the other resumes, so having specific job position details in it is very important. Write a cover letter specific to each job application by using these tips from a career adviser in this free video on job guidance.

Cutting floor and wall tile with a tile cutter should not be a difficult job. For any successful tile cutting job, the steps are roughly as follows:

String a tennis racket yourself. Take a look at this instructional video and learn how to lace your mains on a one-piece string job for your tennis racket. The number of grommets in the yoke of the tennis racket determines where to start off. After dividing the number by two, if you yield an odd number, you would start from the throat. If you yield an even number, you start from the top of the racket.

String a tennis racket. Take a look at this instructional video and learn how to lace your mains for a two-piece string job for your tennis racket. To find out where you start is by counting how many grommets you have on your racket. By dividing the number by two, you can determine where to start, top or bottom. If the number you yield is odd, you start from the bottom. If the number you yield is even, you start from the top.

A brief video that illustrates parachute packing using the 'psycho method'. Part 1 of 2 shows the steps of; Sorting the 9 cells, slider, stabelisers, wrapping of the tail, flipping the pack job on its back, untwisting d-bag and cocking the pilot chute. Part 2 illustrates the final stages of the pack job called the 'psycho method'. These steps include; Making sure the pilot chute is cocked, roling the left 4 cells left, the other 4 cells right,the9th cell position, slider adjusting or 'pouting...

Before you go out to protest, understand what you are facing. Sometimes these demonstrations become infected with looters and rioters, which could mean interaction with law enforcement and potentially arrest. And if your phone is on you, it can be used as a tool against you.

The term "hacker" often has negative associations attached to it, yet the world is in dire need of professionals with hacking skills. White hat hackers are ethical computer hackers that use their hacking skills to pinpoint network vulnerabilities and patch them up before they can be exploited by the bad guys.

Ever since the iPhone X, Face ID has been the standard way to unlock your iPhone. For the most part, it works remarkably well and adds a layer of security that Touch ID can't match. That said, the tech isn't perfect. If you're finding that Face ID isn't working for you, there might be an iOS setting to blame.

One of Android's biggest strengths relative to iOS is how simple it is to sideload apps that aren't on the official app store. Rather than having to sign IPA files or tell your phone you trust a developer every two weeks, you can just enable a setting and be done with it.

Is Apple trying to set a record for the highest number of updates within a two-week period? You wouldn't be blamed for thinking so. Just eight days ago, Apple publicly released iOS 13.0 for all compatible iPhones. Then, just five days later, Apple seeded iOS 13.1 with 22 new features to boot. Now, just three days into 13.1's tenure, Apple has released yet another update, iOS 13.1.1.