This is a video tutorial in the Business & Money category where you are going to learn how to how to negotiate your salary without losing the job. You want more salary but, the company wants to pay less. How do you come to an agreement where both sides are happy? George Black, CEO of RSA Corp, gives tips on how to facilitate salary negotiations. The most important tip is he who mentions money first loses. So what you need to do is say "I am very interested in this position and I would serious...
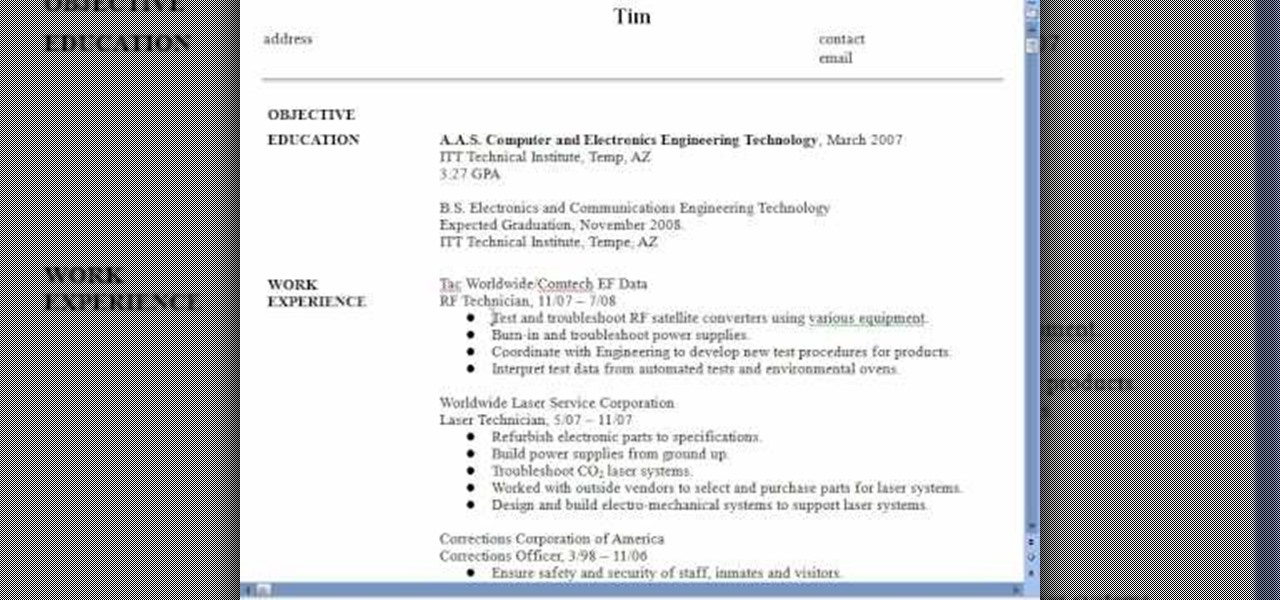
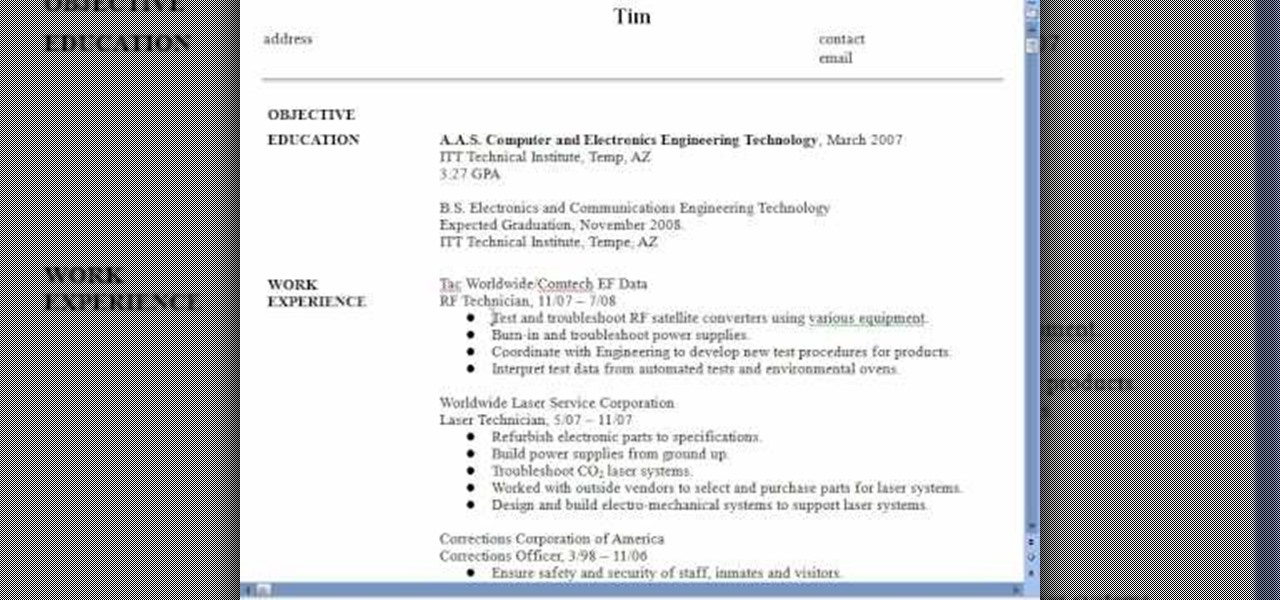
In this video, we learn how to create a compelling resume. When you talk about your prior experience, write down something that you learned from your work background, preferably something that matches the job you're applying for. Employers are looking for something you were taught in your experience. Write down any accomplishments you received while on the job, and how well you did them as well. If you're graduated, let them know when you are available for full time work and when you are grad...

In this video, we learn how to make your resume stand out. If you can't hire a professional, use these secrets to stand out of the crowd. Emphasize your unique value and play up keywords that make you stand out. Create a document that will get you interviews. Before you begin, make sure you have your information from school and work ready, so you can reference it in your resume. Also print out target job descriptions to help you write down notes and outlines. Using these tips will help you wr...

In this video tutorial, viewers learn how to answer the question, "What is your biggest failure?" When answering this question, be honest and don't lie. Sharing your feelings will show that you care about work. Your reaction may indicate your response to any future problems. Always indicate if you turned that failure into a success. A strong ending to your answer should express that you learned from your mistake. This video will benefit those viewers who are looking for a job, and would like ...
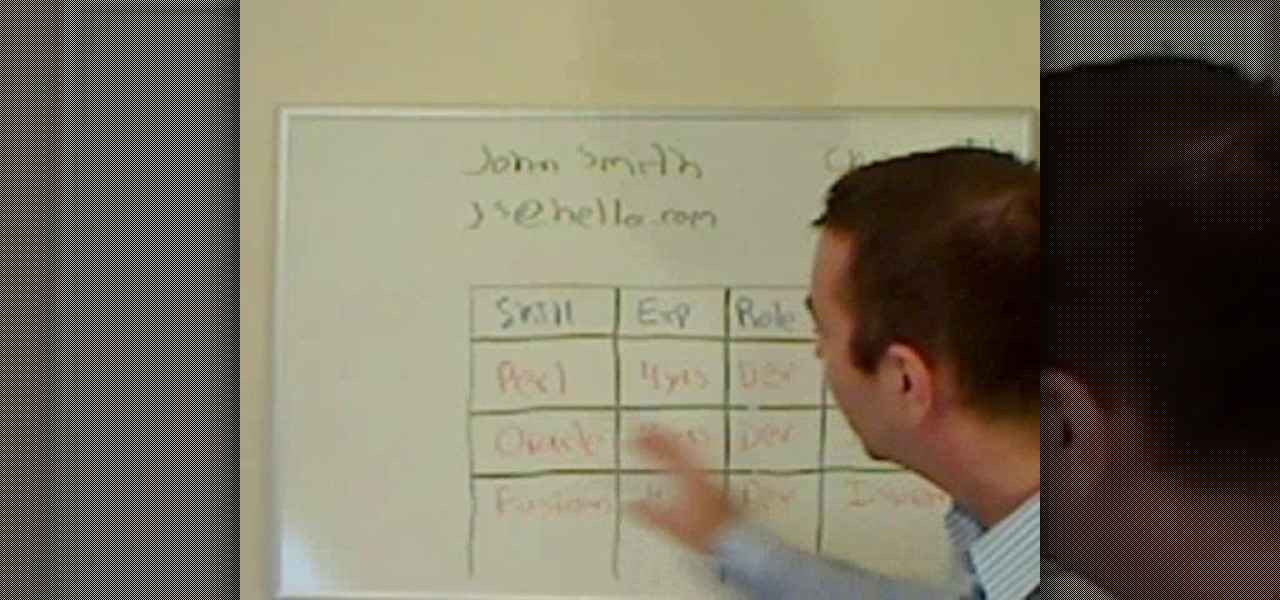
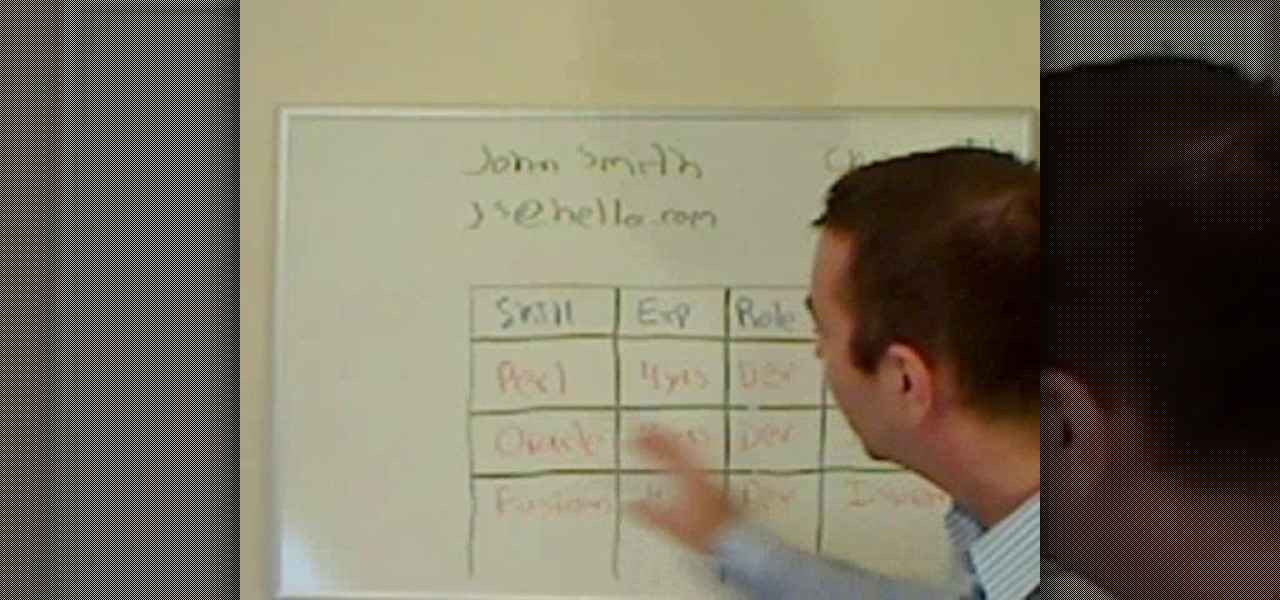
In this video tutorial, viewers learn how write a resume in the table format. A table formatted resume is one of the most effective formats. It highlights metrics in a particular field that potential employers are looking for in a presentable quick overview. At the top of the table, provide your name, contact information and location. In the table, list your skill, experience, role and products from each of your previous jobs and experiences. This video will benefit those viewers who are sear...

In this video from NescoResource we learn how to answer the question in an interview of "Where do you see yourself in 5 years?" This question provides you an opportunity to show your commitment to that job and to demonstrate your knowledge of the company's and the role you could have in achieving that vision. To provide a thoughtful response, you need to do the homework on the company. Do not answer by saying you see yourself in the interviewer's job. This could really backfire on you because...

The video asks the question "What would you do to gain respect?" This is the bad example. It says that you should turn the sound off on your cell phone before you enter the interview. The video suggests that talking on your cell phone during an interview will lower your chances of getting the job. The video also suggests that keeping your potential employer waiting while you take a phone call can also keep you from getting the job for which you are interviewing.

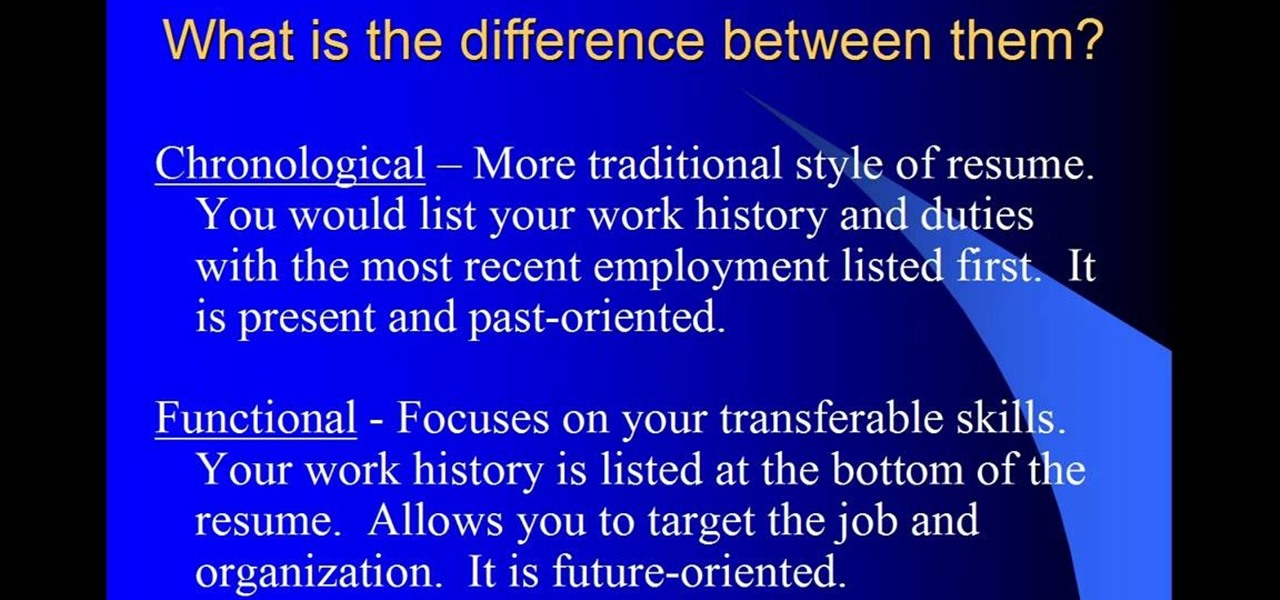
Writing a resume can be a strong asset to any job application, but the process can be stressful and confusing. With this easy to follow guide, even the most novice writer can create a professional resume with just a few short steps. Including phone numbers, education and work experience, this video tutorial takes you through different styles and forms on how to organize the perfect resume for you. It explains what each style is with simple visuals that anyone can easily follow and in no time ...

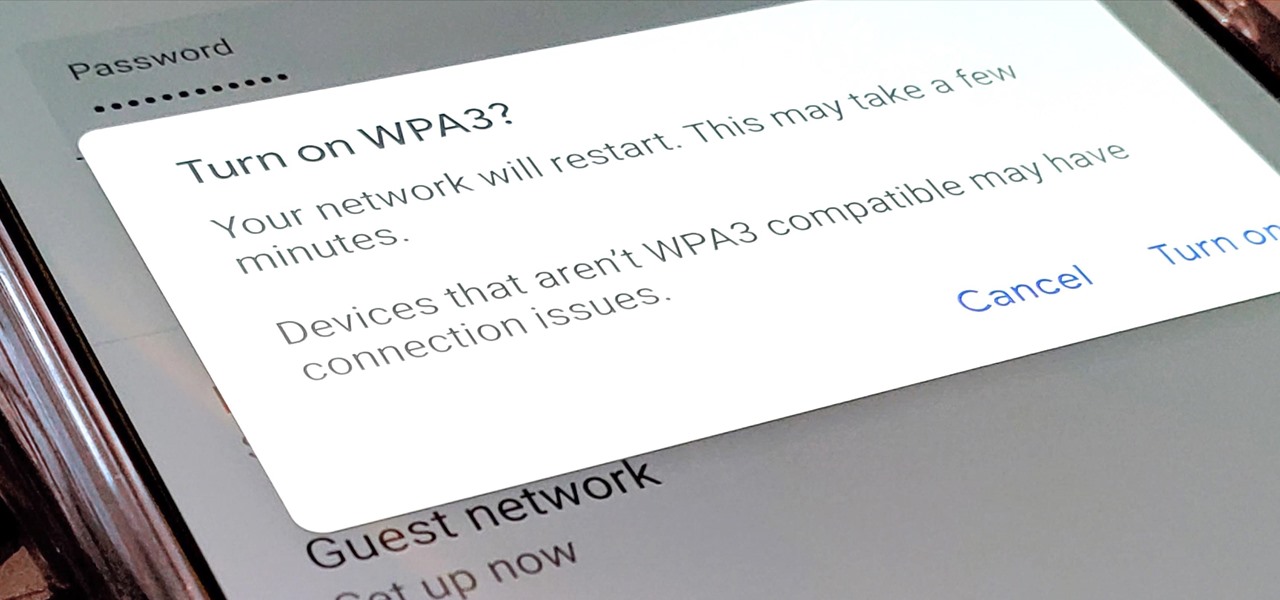
Google recently released a new mesh router known as Nest Wifi. The updated and rebranded Google Wifi brought many improvements, such as faster processing power and an increased level of wireless security called WPA3. But while it's not enabled by default, you can still get the new WPA3 security on your original Google Wifi.

Hundreds of Windows 10, macOS, and Linux vulnerabilities are disclosed every single week, many of which elude mainstream attention. Most users aren't even aware that newly found exploits and vulnerabilities exist, nor that CVEs can be located by anyone in just a few clicks from a selection of websites online.

We need to take our privacy and security much more seriously. Whether it's malware-infected apps or the mishandling of our data by companies like Facebook, there are threats all around us in this digital world. Fortunately, some smartphones are simply designed to protect us better.

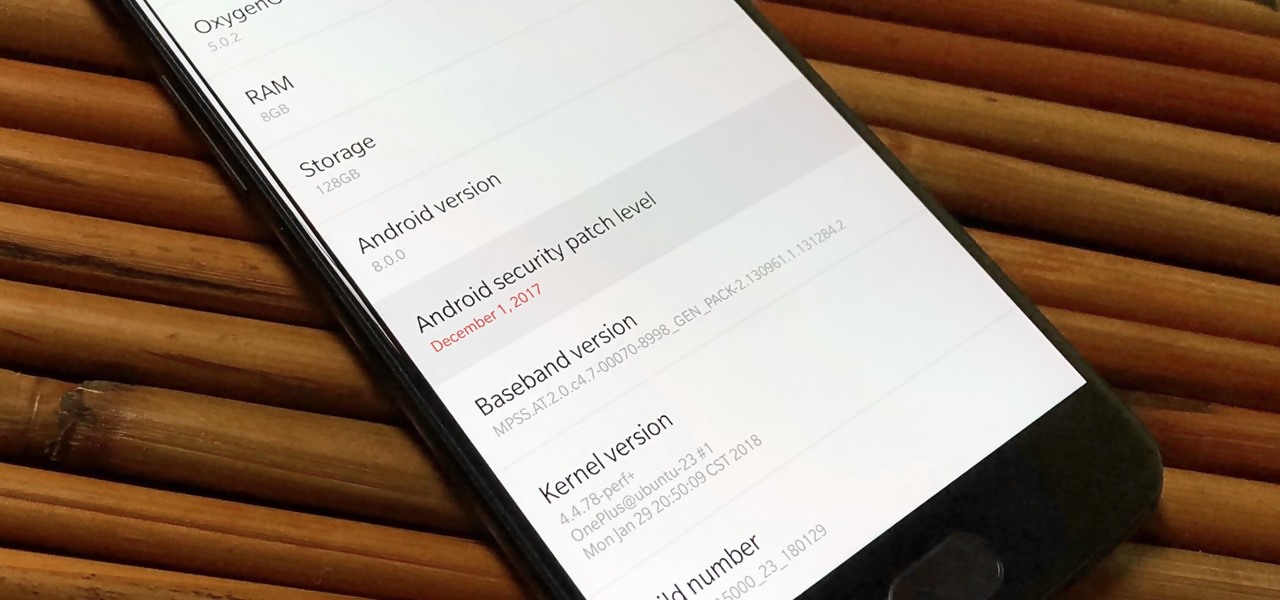
As far as overall security updates are concerned, we all know that iOS reigns supreme over Android. But just how bad do Android devices fare against Apple in general? A recent report will have you second guessing some companies the next time you're in the market for a handset.

Samsung's 2016 line of smartphones has a new update, at least for the devices on AT&T. The update brings the Galaxy S7 to version G930AUCS4BQL1 and the Galaxy S7 Edge to version G935AUCS4BQL1. Here's what's on the table.

The Play Store hasn't been the most secure place for apps lately. A quick Google search for "Play Store malware" will give you a taste of some of the malicious apps that snuck their way onto Android's official app store. Google is aware of the problem and they're tying to fix it, but their new Play Protect program doesn't have a great track record, so you might want to look elsewhere.

Kali Linux is the obvious first choice of an operating system for most new hackers, coming bundled with a curated collection of tools organized into easy-to-navigate menus and a live boot option that is very newbie-friendly. But Kali isn't the only distribution targeted at pentesters, and many exciting alternatives may better fit your use-case. We've already covered BlackArch Linux, now it's time to talk about Parrot Security OS.

A new Google Search update lets job-seekers streamline their search process. Searches like 'jobs near me' are now designed to show relevant opportunities from multiple sites.

Who likes security? I like security. I lock my doors at night, and so should you! That's why it's exciting to me that Samsung has just announced its May security update. It's like getting a brand new, top-of-the-line lock for free, but for your phone.

These days, our smartphones carry some very sensitive data. From banking app passwords to personal photos, there are many things on your Nexus 5 that you might not want other people to have access to.

Snapchat has had more than its fair share of security failures and mishaps. The photo-sharing company is looking to better address some of these security gaps by adding new features, and today its most recent addition is live: the Captcha. New users will be asked to verify their "humanness" by selecting the infamous Snapchat ghost out of a selection of images. The feature is supposed to help block hacker-made bots from creating fake accounts or accessing existing ones. But rather than using t...

This is a humorous video with tips for young people on how to dress and act to make a good impression in a job interview. Dressing inappropriately for the interview will make the interviewer wonder what you might wear to work. Be well groomed, remove any piercings and be sure any tattoos are covered. A suit is not really necessary; a shirt with a collar and khaki pants are fine. Your appearance shows the interviewer that you are more interested in the job than in expressing your own personal ...

The economy is rough at the moment, and we all need our jobs more than ever. Check out this tutorial, and learn how to make yourself so valuable at your job that no one would ever want to fire you.

The key to a good steampunk paint job is getting the distressted metallic look just right. This tutorial shows you how to add a lot of aesthetic appeal to your next steampunk prop mod, whether it's goggles, binoculars or something entirely different.

There's nothing more tedious, yet exciting, than watching surveillance cameras at work. They prey on the innocent and the unknowing. They protect businesses, workplaces, and homes. They catch criminals in the act, find hilarious anomalies, and are just darn cool when you're not the one that's supposed to be eavesdropping with them.

Learn how to be a stay at home husband. It's not an easy job and as time moves on more and more blokes are making the move to staying at home. It is a hard job as you have to be a psychologist, doctor, nurse, mother, cook, cleaner and teacher to name a few!!!

This is my first contribution in an ongoing series on detailing the best free, open source hacking and penetration tools available. My goal is to show you some of the quality tools that IT security experts are using every day in their jobs as network security and pen-testing professionals. There are hundreds of tools out there, but I will focus and those that meet four key criteria:

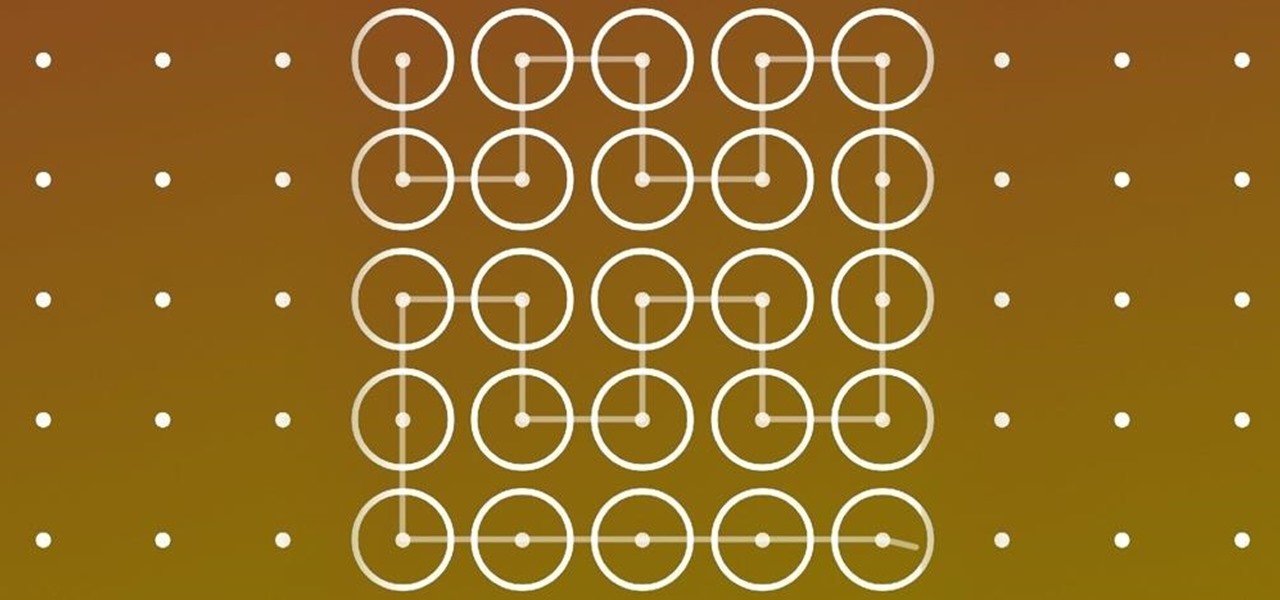
For an extra level of security, you can download an app onto your iPhone or iPod that will let you create a customized security key, which you unlock by using the touch screen to draw a simple graphic. This tutorial shows you where to get the app and how to set it up.

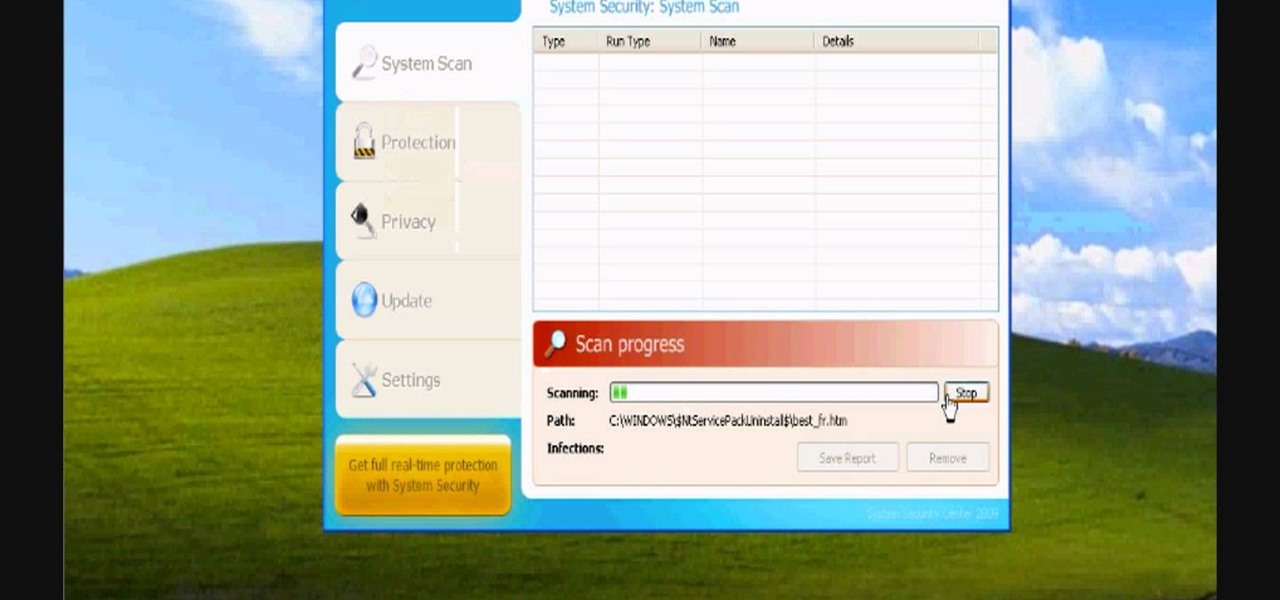
In this video, we learn how to avoid getting infected by "system security". Make sure you avoid the website that show the System Security Anti-Virus. Once you install this onto your computer it will pretend like it is doing a scan, but in reality is hurting your computer. It will pop up showing you that you have problems on your computer, but the alert will never go away. If you delete this, it will just re-install on your computer instead. To do this the correct way, you need to go to your m...

This video shows you how to easily remove the Security Tool virus. The first thing you have to do is restart you computer. Once restarted, immediately hold down CTRL+ALT+DEL. In the Task Manager you should see: Security Tool. Quickly end it now. The virus is temporarily disabled. Now go to: Download and install Spyware Doctor. Scan your computer and click Fix All. It will ask you for an account...

Learn how to install Aircrack on your iPhone to hack into almost any WiFi network. First download Aircrack from iHackMyi, then follow these steps:

You have a webcam, right? Nowadays, who doesn't? But just because you all have webcams doesn't mean you're using them the same way. And a great way to take full advantage of your peripheral or built-in webcam is by turning it into a security camera. This video will show you how to turn it into a security cam by accessing the video feed remotely over the internet. And it's a really simple solution—you just need to sign up for a USTREAM account, which allows you to stream webcam footage live!

Smartphones are inherently bad for privacy. You've basically got a tracking device in your pocket, pinging off cell towers and locking onto GPS satellites. All the while, tracking cookies, advertising IDs, and usage stats follow you around the internet.

If you've ever received an email from a sketchy address purporting to be Uber, asking you to sign in with your credentials, you might be a phishing target. Hackers use a fake login page from real-looking domains to trick you into giving up your account information, and while it's been an issue in the past, Uber is making it more difficult on cyber thieves with the addition of two-step verification.

When Google introduced the Pixel 3 on October 9th, one of new additions they briefly mentioned was the Titan M security chip. While they did talk about how it will improve overall security, they didn't expand on the number of changes it brings to the Pixel 3's security. Well, they finally shared more, and it's a pretty big deal.

One downside to iOS 11's awesome built-in QR code scanner in the Camera app is its only been live for a short while. In its short life, there has already been a security vulnerability discovered that was an issue for at least the last 4.5 months, but Apple has finally patched this weakness with its iOS 11.3.1 update.

You may have seen news reports over the last two days detailing a major security flaw in virtually all smartphones. The devices that are at risk are not limited to either iPhone or Android — all of us are affected. If you want to make sure your smartphone and its data stay secure, there are a few steps you can take.

Many people think antivirus apps are useless — why pay a subscription fee when most malware can be avoided with common sense? But the thing is, there were an estimated 3.5 million malicious Android apps discovered last year, with many of them making their way onto the Play Store. As this number continues to rise, can you truly depend on common sense to protect you?

WhatsApp sneakily made some security changes to iCloud backups without your knowledge, ladies and gents. Not that strengthening security is a bad thing, but still!

Don't ignore the update sitting in your Settings app; you'd be leaving your iPhone's security vulnerable.
According to security firm Kaspersky Lab, CoinVault and Bitcryptor ransomware are officially dead.

CEO's of IT companies doesn't know this because they are not a hacker. Only a true hacker can become a successful Security head officer.