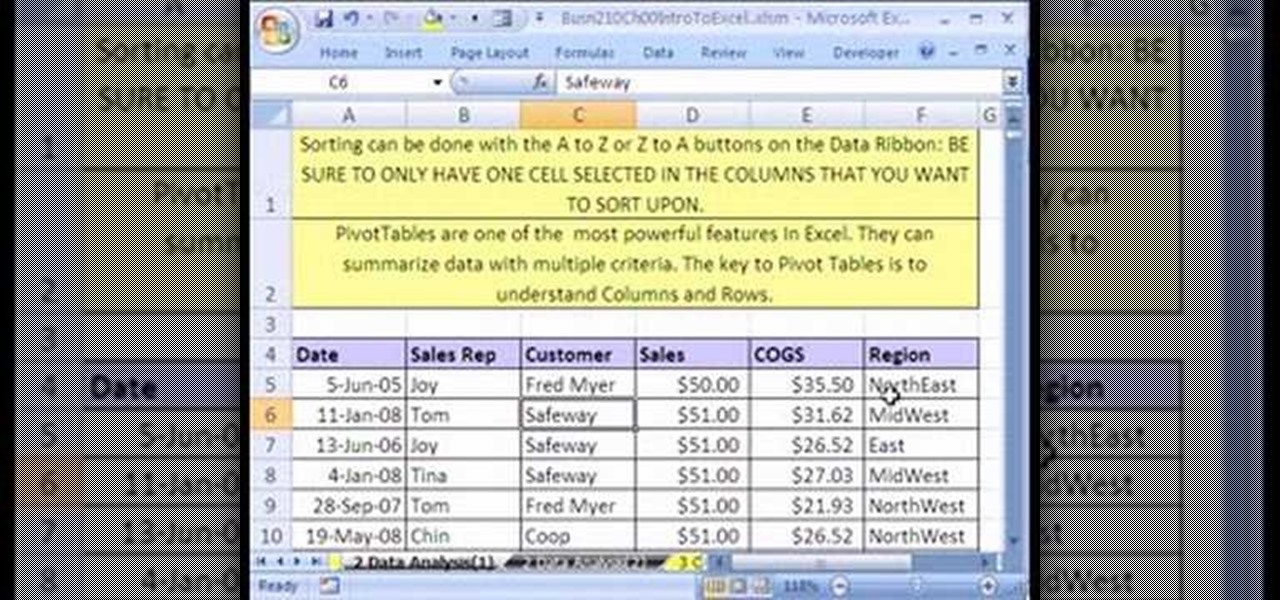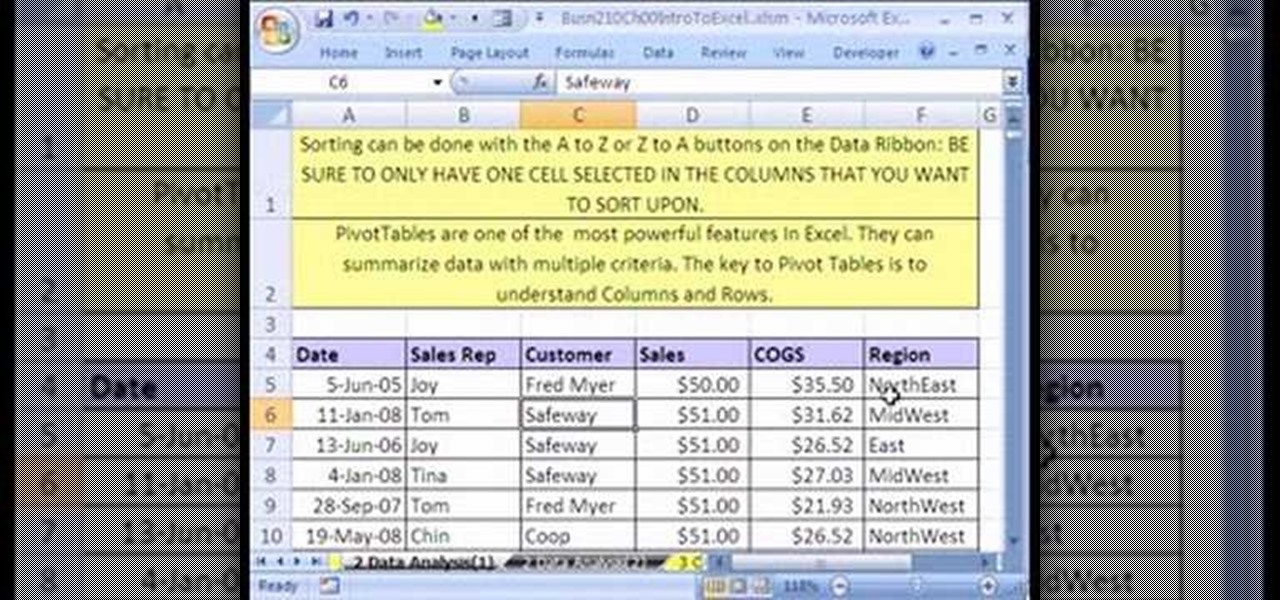
If you use Microsoft Excel on a regular basis, odds are you work with numbers. Put those numbers to work. Statistical analysis allows you to find patterns, trends and probabilities within your data. In this MS Excel tutorial from everyone's favorite Excel guru, YouTube's ExcelsFun, the 3rd installment in his "Excel Statistics" series of free video lessons, you'll learn how to use Excel's sorting and pivot tables (PivotTables) data analysis tools.
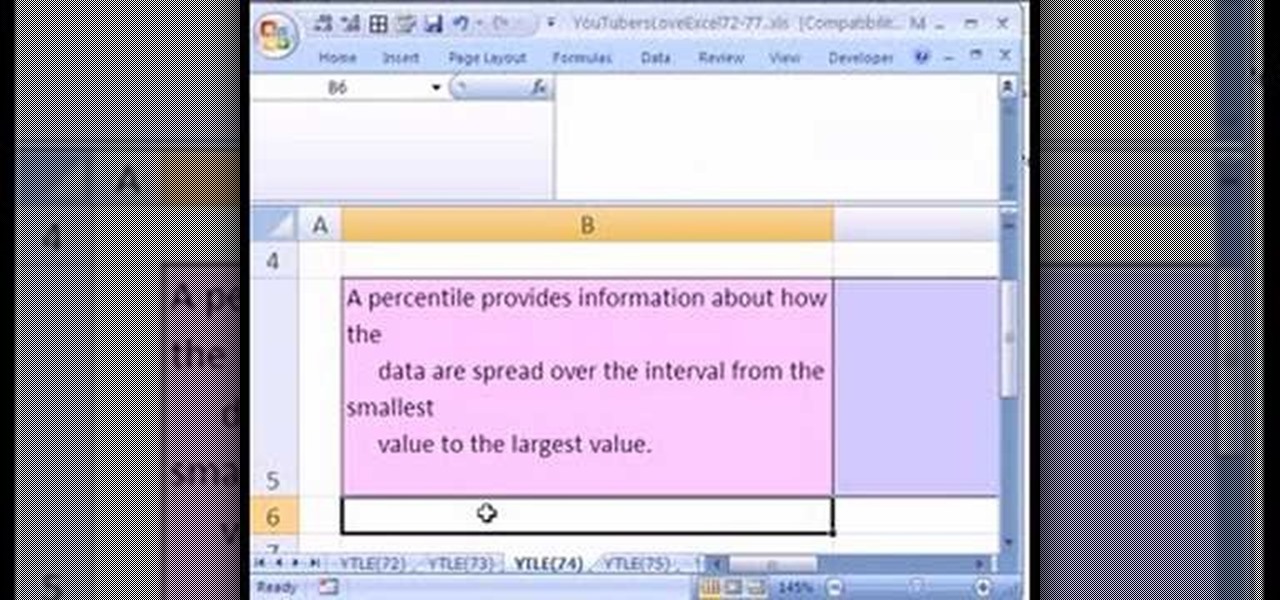
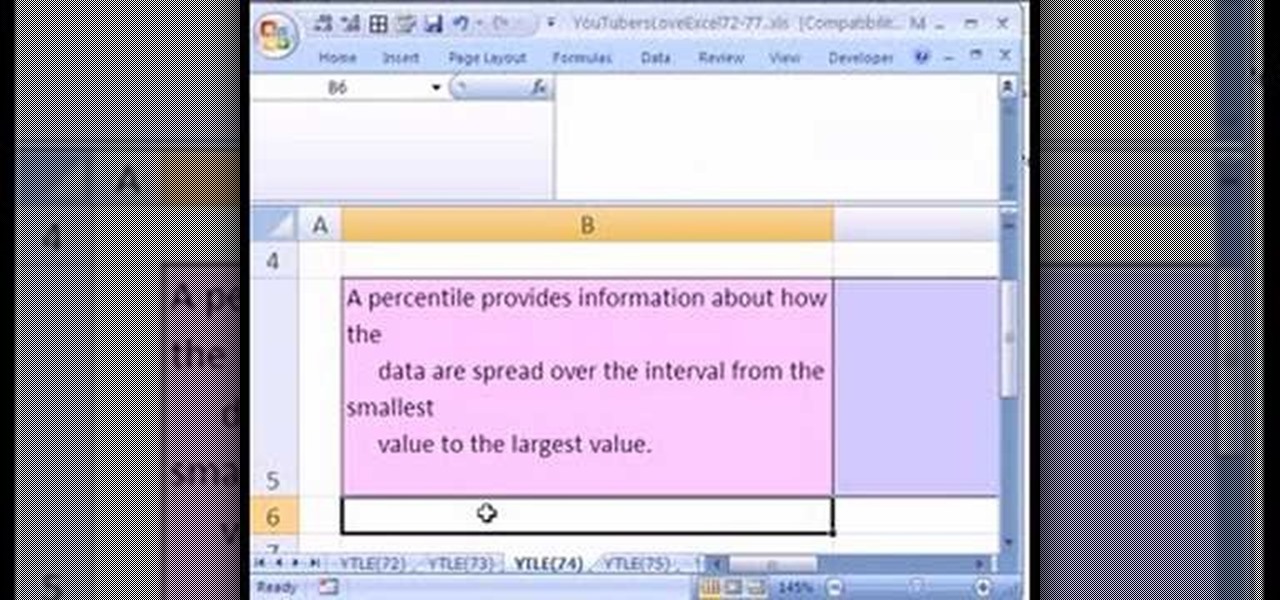
Love Microsoft Excel? This clip contains a tip that just might induce you to. With this free video tutorial from ExcelIsFun, the 74th installment of his "YouTubers Love Excel" or YTLE series of free video MS Excel lessons, you'll learn how to fix bad data with the CLEAN & TRIM functions.
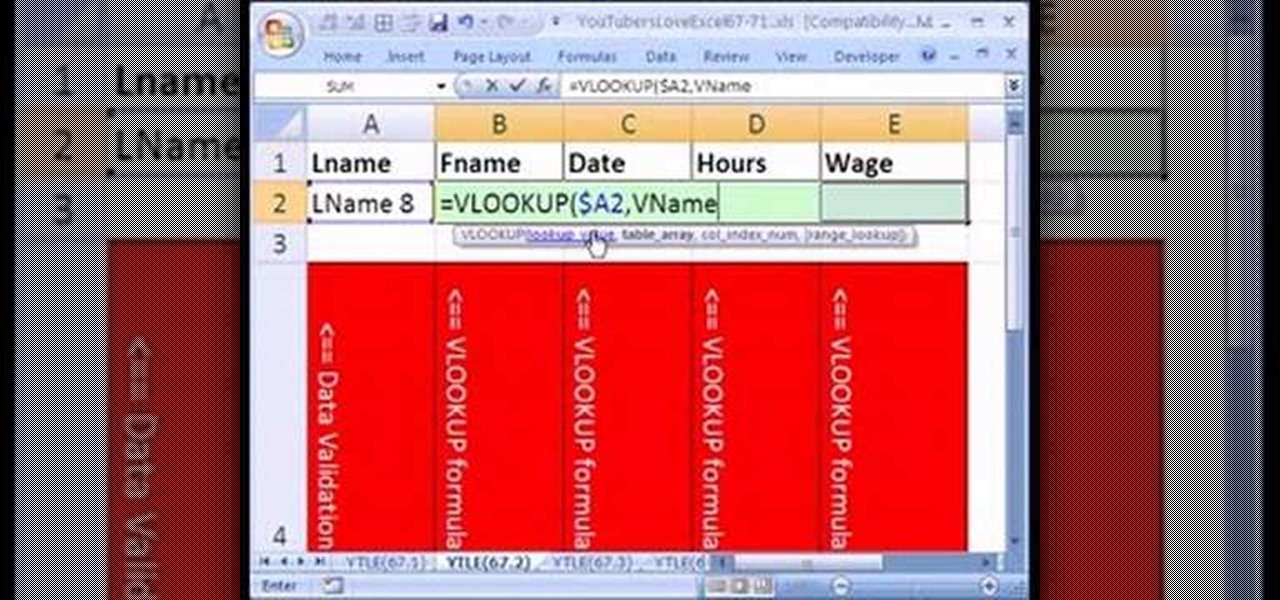
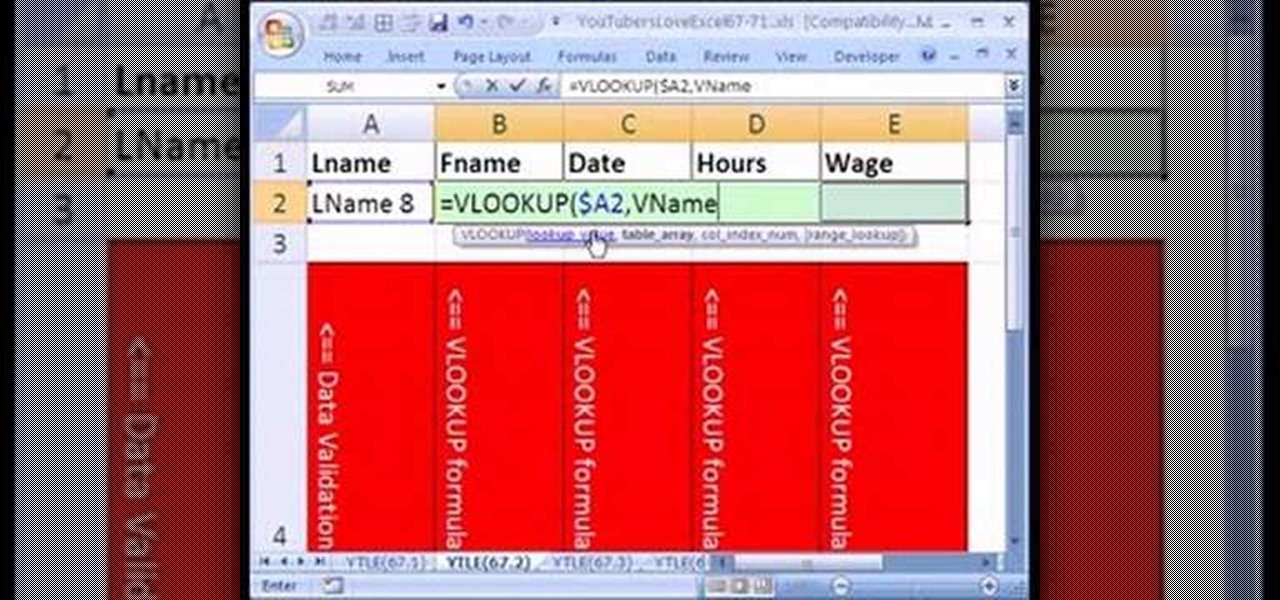
Love Microsoft Excel? This clip contains a tip that just might induce you to. With this free video tutorial from ExcelIsFun, the 66th installment of his "YouTubers Love Excel" or YTLE series of free video MS Excel lessons, you'll learn how to pull data from a table on one worksheet to a second worksheet using the VLOOKUP and DGET functions.
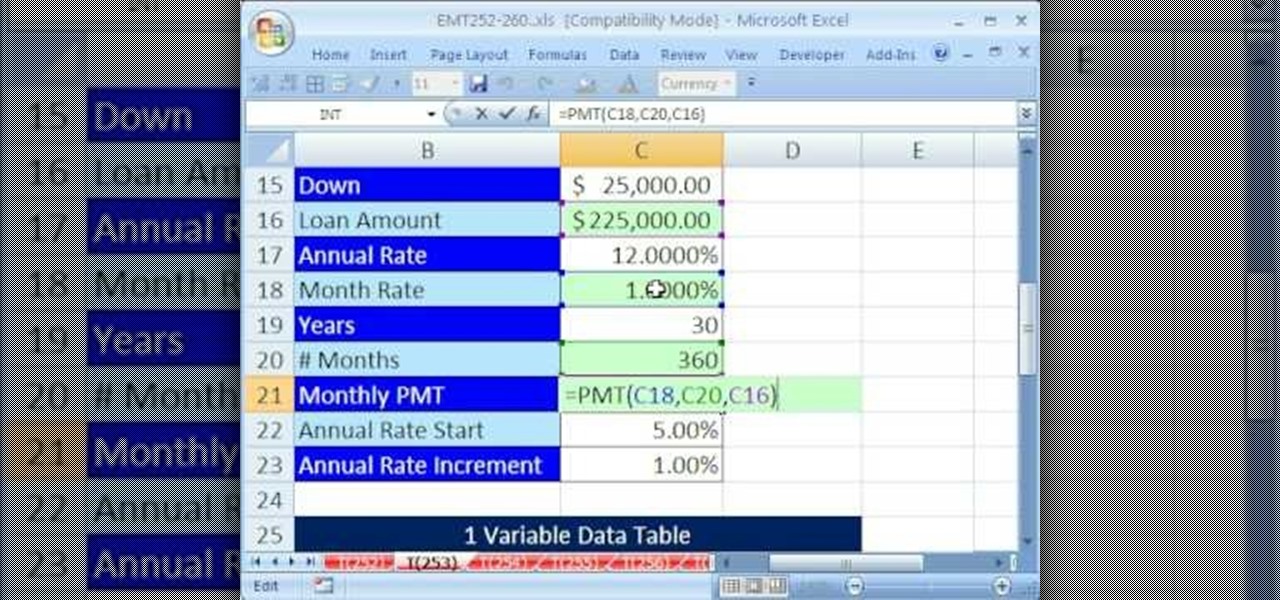
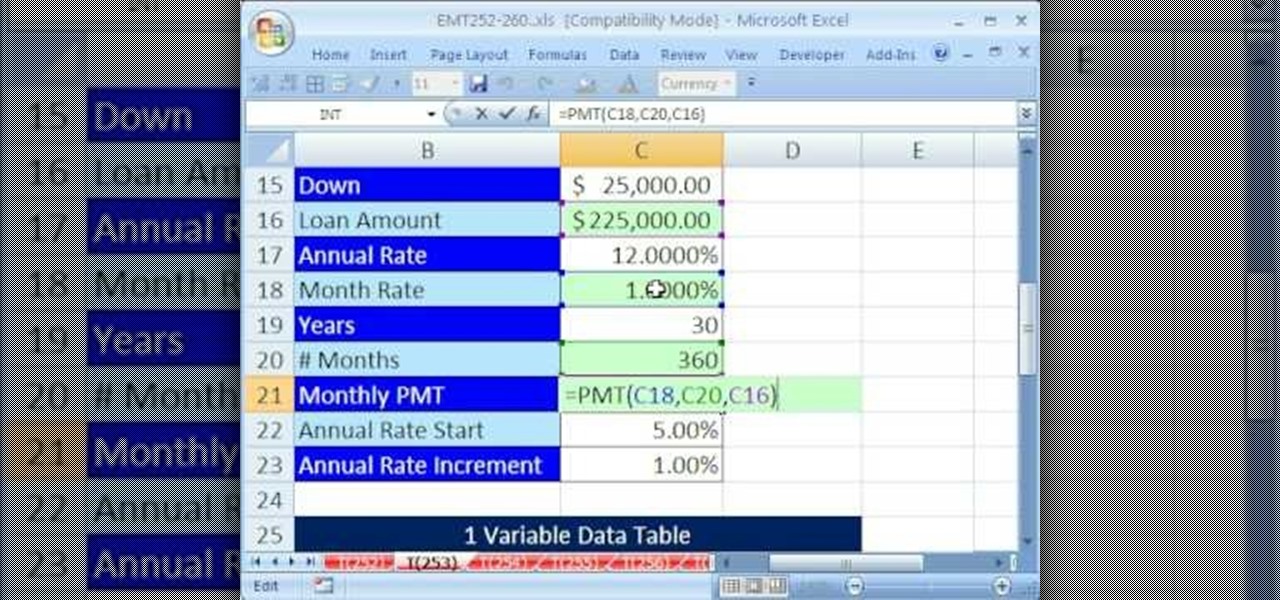
New to Microsoft Excel? Looking for a tip? How about a tip so mind-blowingly useful as to qualify as a magic trick? You're in luck. In this MS Excel tutorial from ExcelIsFun, the 253rd installment in their series of digital spreadsheet magic tricks, you'll learn how to use a data table for what-if analysis. You'll also learn about the PMT and see the formula equivalent to a data table.
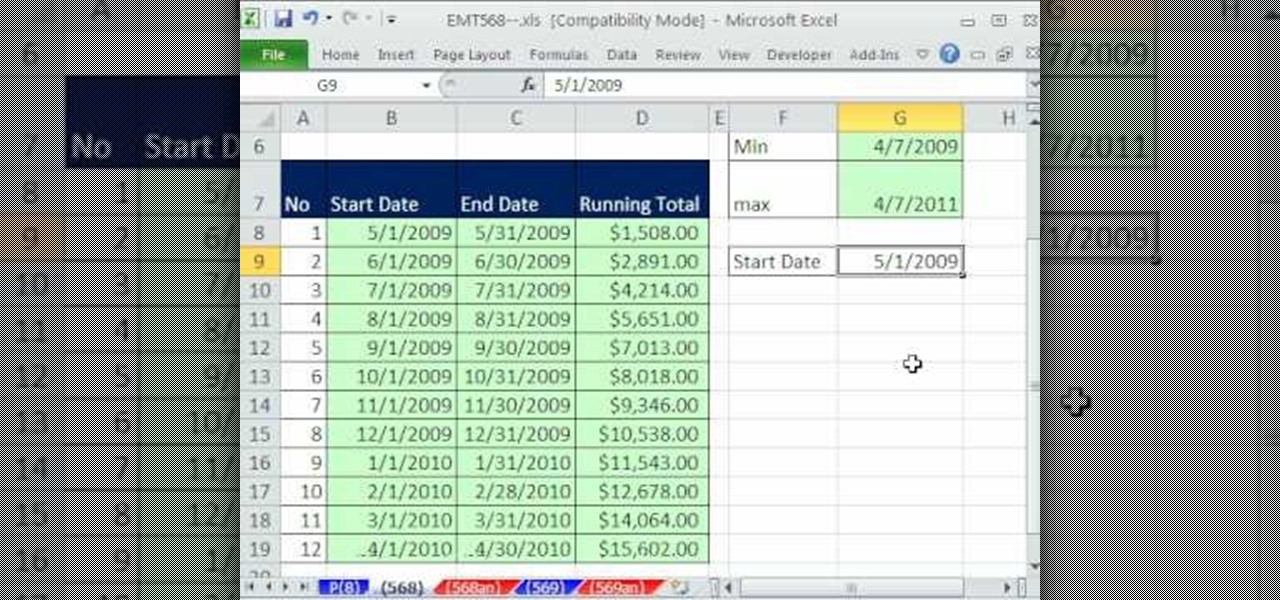
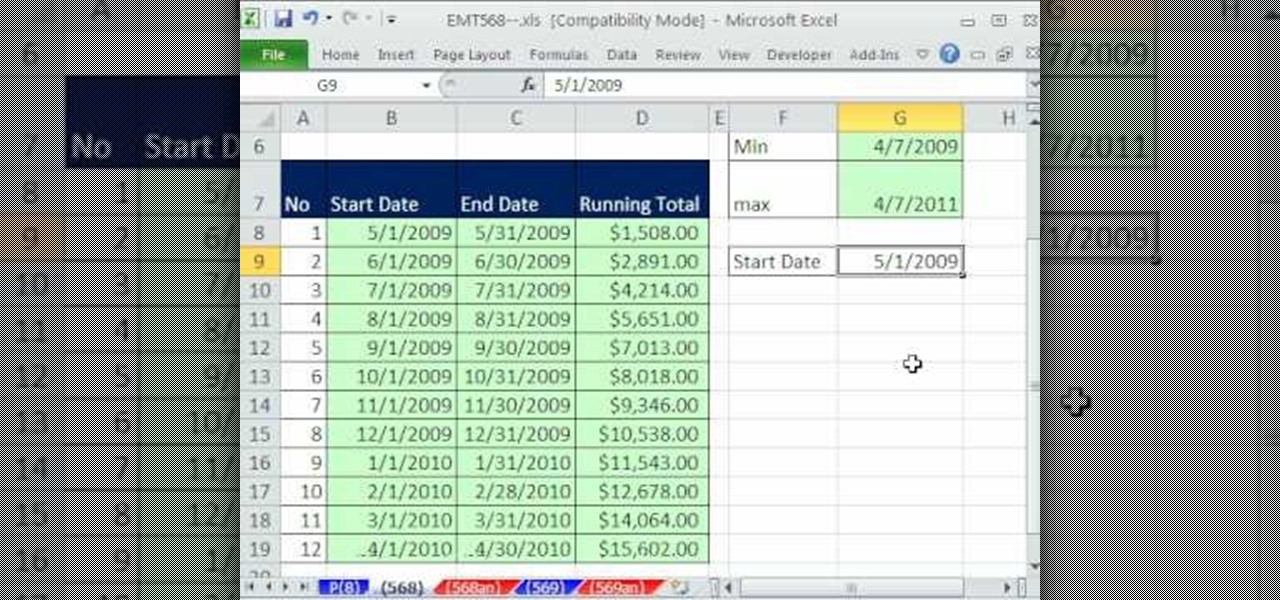
New to Microsoft Excel? Looking for a tip? How about a tip so mind-blowingly useful as to qualify as a magic trick? You're in luck. In this Excel tutorial from ExcelIsFun, the 568th installment in their series of digital spreadsheet magic tricks, you'll learn how to use a SUMIFS function to tabulate a monthly running total from transaction data.
New to Microsoft Excel? Looking for a tip? How about a tip so mind-blowingly useful as to qualify as a magic trick? You're in luck. In this MS Excel tutorial from ExcelIsFun, the 94th installment in their series of digital spreadsheet magic tricks, you'll learn how to use and link a currency web query to a data validation cell drop-down list for money conversion.

If you've already jailbroken your iPhone, but noticed that you are missing your cellular data network tab, check out this video. You will need Cydia, Winterboard, and be jailbroken on 3.0 of course.

In this ten-step video tutorial, you'll learn how to quickly copy keys using a camera, printer and Dremel tool. With this ten-step process you'll learn the necessary steps to copy almost any key... even if you only have access to it for a brief period of time.

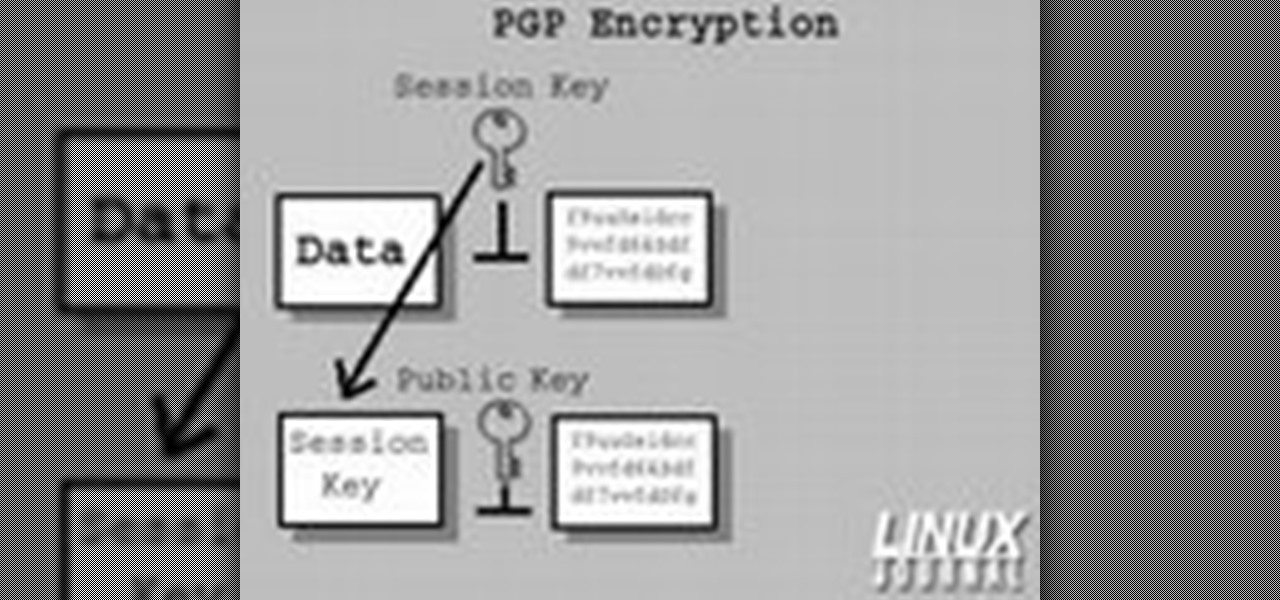
In today's time of rampant IT crimes, including identity theft, security is more important to the average computer user than ever. This tutorial, which was recorded and encoded for the Internet usingly only open source tools, demonstrates how you can use GnuPG to secure and verify data on your GNU/Linux box. Secure your Linux computer with this how-to.

How to Use Your Mac as a Server: Turn your Mac Mini into a server! Yes, that's right, with a little know-how and a little spunk, you can turn an inexpensive Mac Mini computer into a server to provide services over you network. You won't even need the Mac OS X Server, just the Mac OS X Client, so there is no extra software to buy, just the Mac Mini and it's operating system.

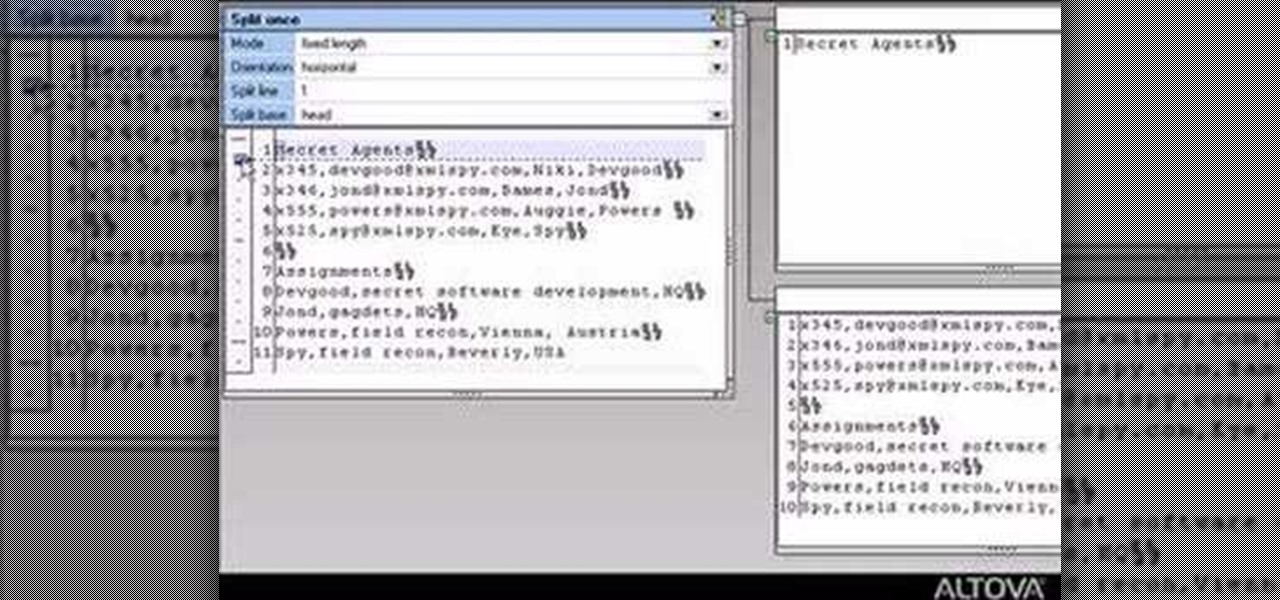
Learn how to use MapForce FlexText to analyze and parse arbitrary text files using an intuitive visual interface in this video. The resulting structured data can be used in any MapForce data mapping.

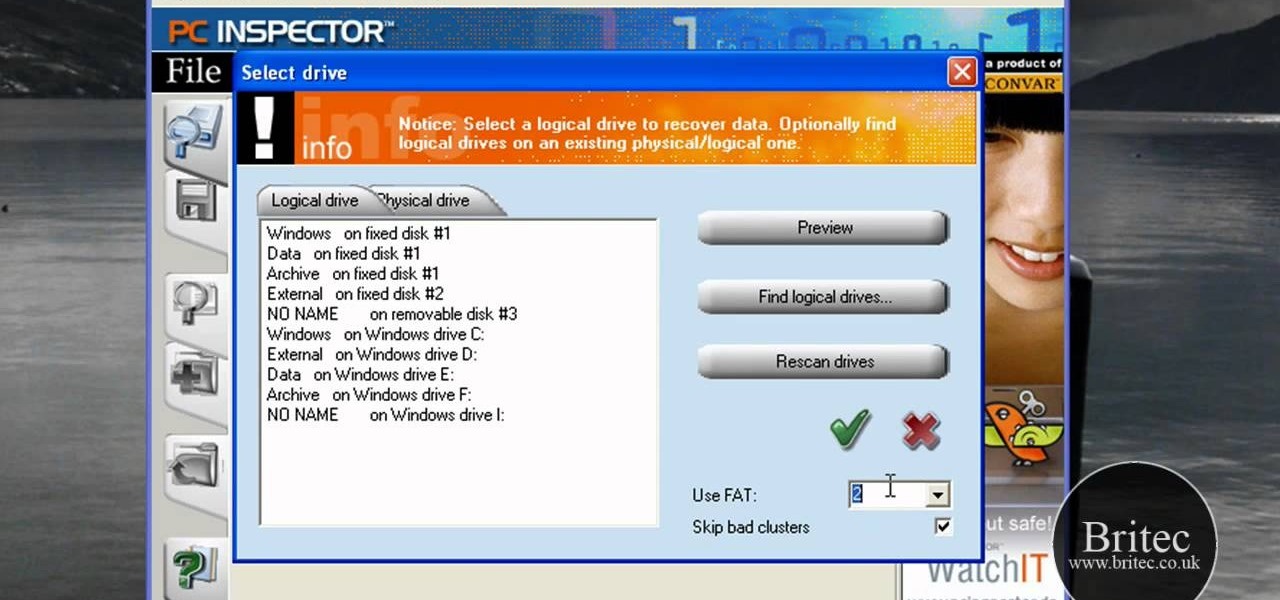
In this data recovery tutorial the instructor shows how to recover deleted files and lost data using a free software called PC Inspector. On your computer you may loose data sometimes due to a corrupted hard drive, or because you deleted it accidentally or some other reason. Now some times you will need to recover that important data and it will cost you hundreds of dollars to get it done outside by the professionals. Now you can avoid this and use a free software called PC inspector and reco...

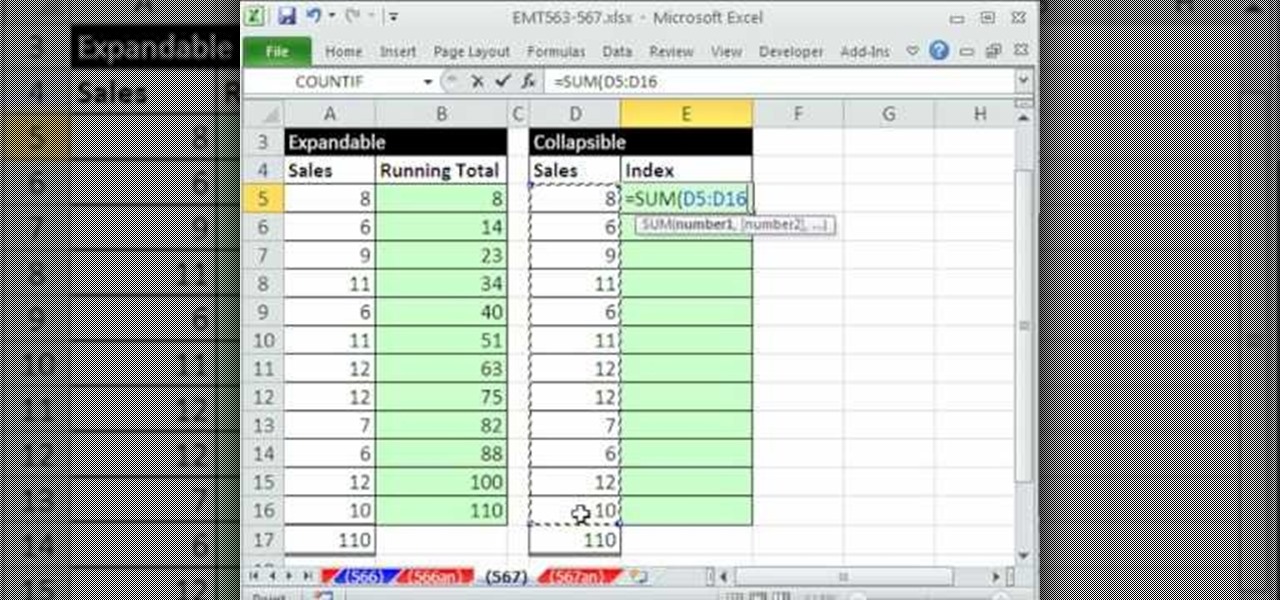
This video demonstrates how to create collapsible and expandable cell ranges in Excel. The first thing that you will have to is to prepare your Excel worksheet that contains the data which you need to be expandable and collapsible. On the first cell under your Running Total column, type in the function, "=SUM". Select the Sales cell corresponding to that cell then type in Shift+Colon. Click on the first value and hit the F4 key to lock your row reference. The result will automatically show. Y...

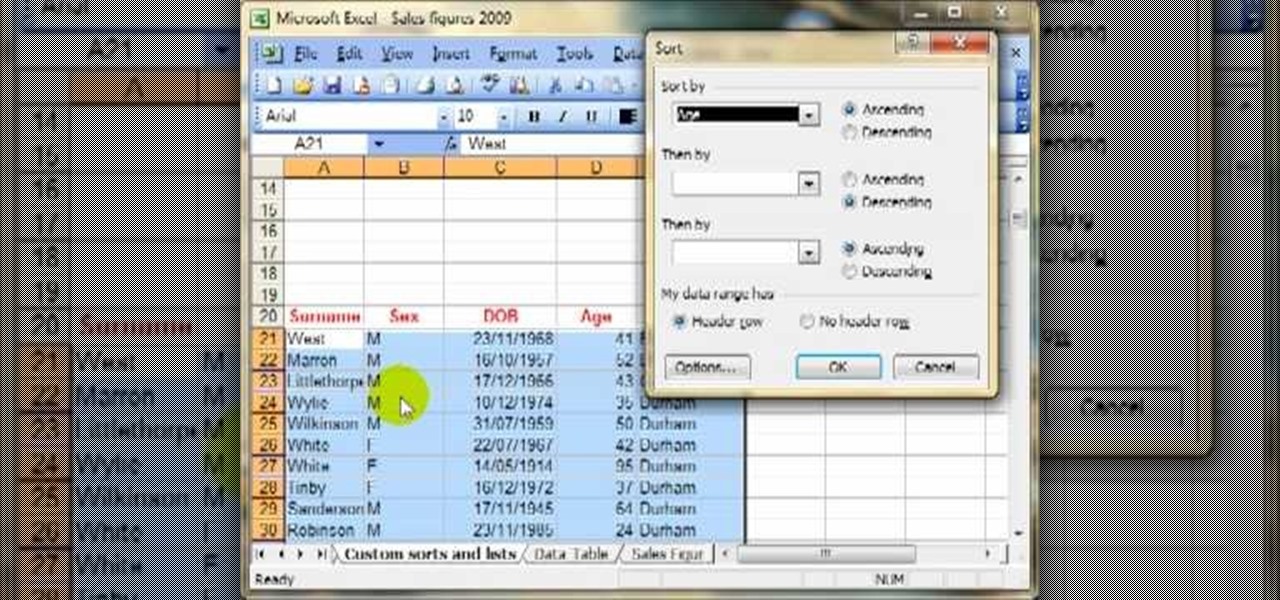
Today we are going to learn how to sort data in a Microsoft Excel 2003 spread sheet. We will go over single column and multiple column sorting. In a single column sort you may high light the data or just click on any cell in the column. Once the data is selected look for the sort icons just under the menu bars. There is a sort ascending and sort descending icon. Click on the icon and Excel will sort the list. When sorting multiple columns the data must be in columns next to each other. If the...

In just a few simple steps, you'll have your piano keys sparkling like new. You Will Need

These days, you can FaceTime with family and friends whether you're at home connected to Wi-Fi or on-the-go with mobile data. You may have noticed, however, that your iPhone will sometimes drop Wi-Fi and rely on cellular instead — whether you're placing or receiving a FaceTime call. While that's not an expected result, there is a workaround to get your FaceTime calls back on track.

With the Wigle WiFi app running on an Android phone, a hacker can discover and map any nearby network, including those created by printers and other insecure devices. The default tools to analyze the resulting data can fall short of what a hacker needs, but by importing wardriving data into Jupyter Notebook, we can map all Wi-Fi devices we encounter and slice through the data with ease.

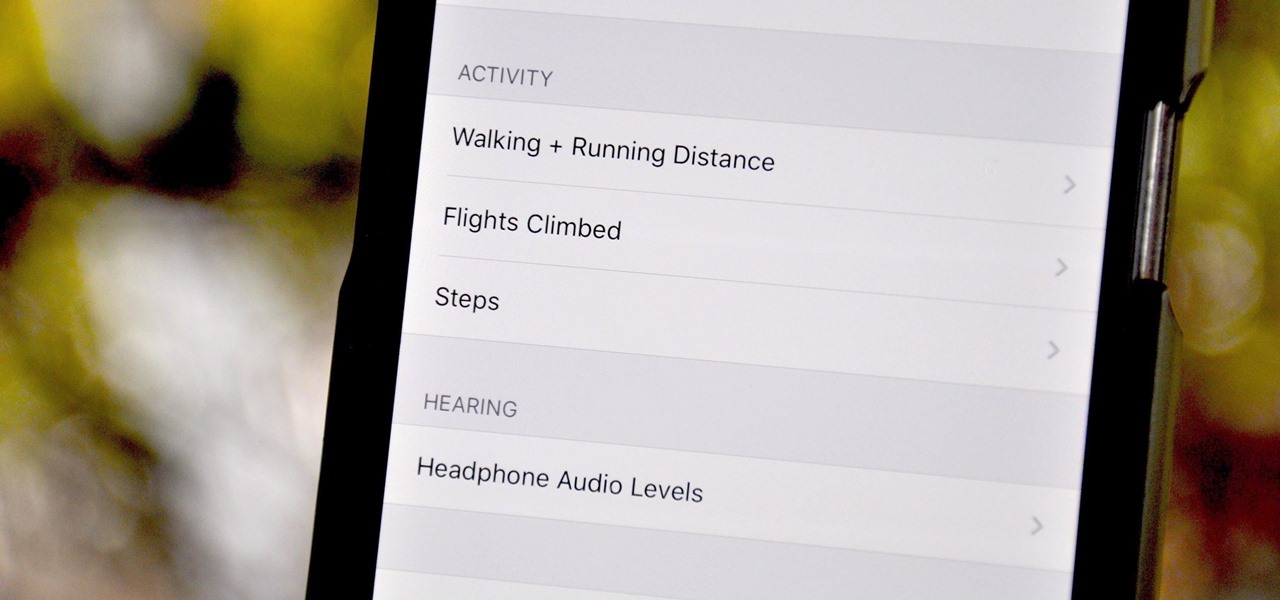
Your iPhone tracks how many steps you take, how far you walk, and how many stairs you climb each day. That may seem a bit frightening, but it's all for a good reason: the Health app stores this data so you can view your progress in one place. But interestingly, opening the Health app isn't the easiest way to view this info.

After reviewing the international plans for major US wireless carriers, it became obvious they're all pretty bad. Your data is heavily restricted, requiring a daily fee which can cost an extra $100+ on a seven-day vacation. That's when I learned about Google Fi, and how for most travelers, it's the best option.

Data breaches are all too common now, and the latest one you need to know about involves Timehop, a mobile app that makes it easy to reminisce over old photos. The breach, which took place on July 4, was revealed on Sunday, July 8. At the time, Timehop disclosed that 21 million users had been affected by the breach, but it now appears that all users were impacted in some way.

If you can't afford an unlimited plan, you're limited to a certain amount of data each month on your iPhone. Even some unlimited data plans have carrier-imposed mobile data caps that throttle the user if they exceed them. Keeping track of your exact usage each day will help make sure you don't get billed more or throttled like a chump near the end of the month.

Using a keylogger to intercept keys pressed on an infected computer can circumvent encryption used by email and secure chat clients. The collected data can often reveal usernames, passwords, and potentially compromising and private information which hackers abuse for financial gain.

When it comes to security, Apple is usually at the top of the pack when it comes to your personal data, minus a few embarrassing flaws here and there. However, a new iOS security concern has been discovered that protects your data less than it did before — and Apple designed it like that.

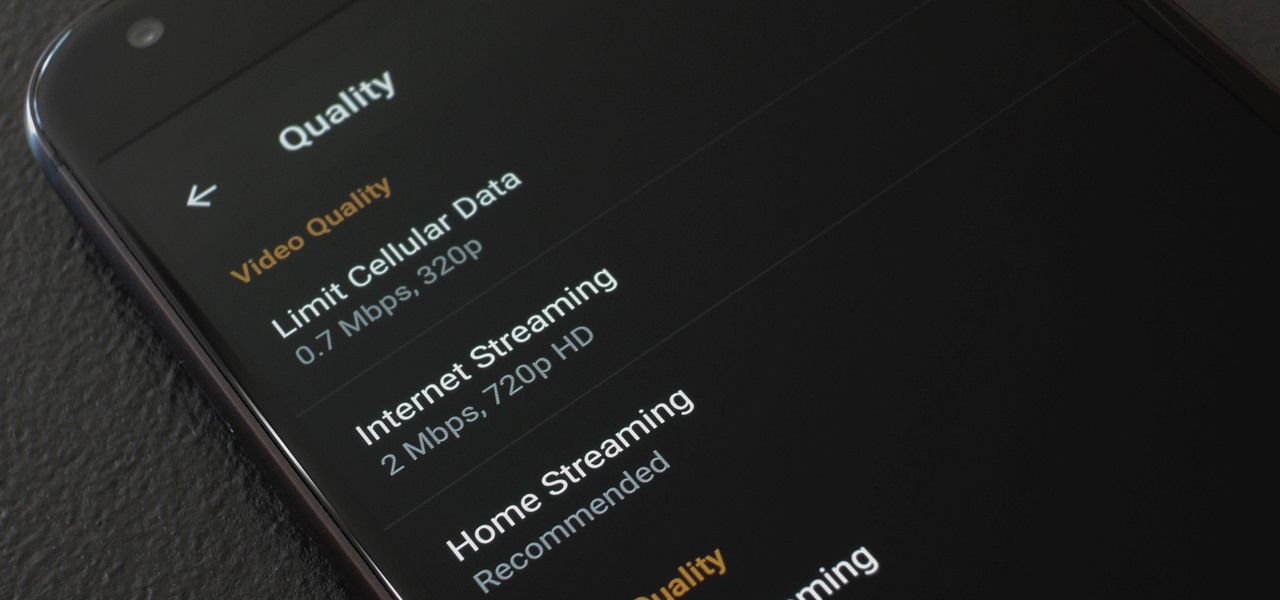
When you're on the go, Plex makes sure your media always stays with you. Just install the server app for Mac or PC and enable remote access, then you can stream movies and TV shows from your computer to your phone over the internet.

Data for mapping and other applications is the lifeblood of machine-driven cars, and so far, Tesla has taken a definitive lead in information it has gathered ahead of other driverless players, including Waymo.

Open-source data scraping is an essential reconnaissance tool for government agencies and hackers alike, with big data turning our digital fingerprints into giant neon signs. The problem is no longer whether the right data exists, it's filtering it down to the exact answer you want. TheHarvester is a Python email scraper which does just that by searching open-source data for target email addresses.

Theorem Solutions, a company that helps engineering and manufacturing companies reduce their costs, has taken the next step with their mixed reality technology. The company has now added their own app, called Visualization Experience, to the Windows Store for the Microsoft HoloLens

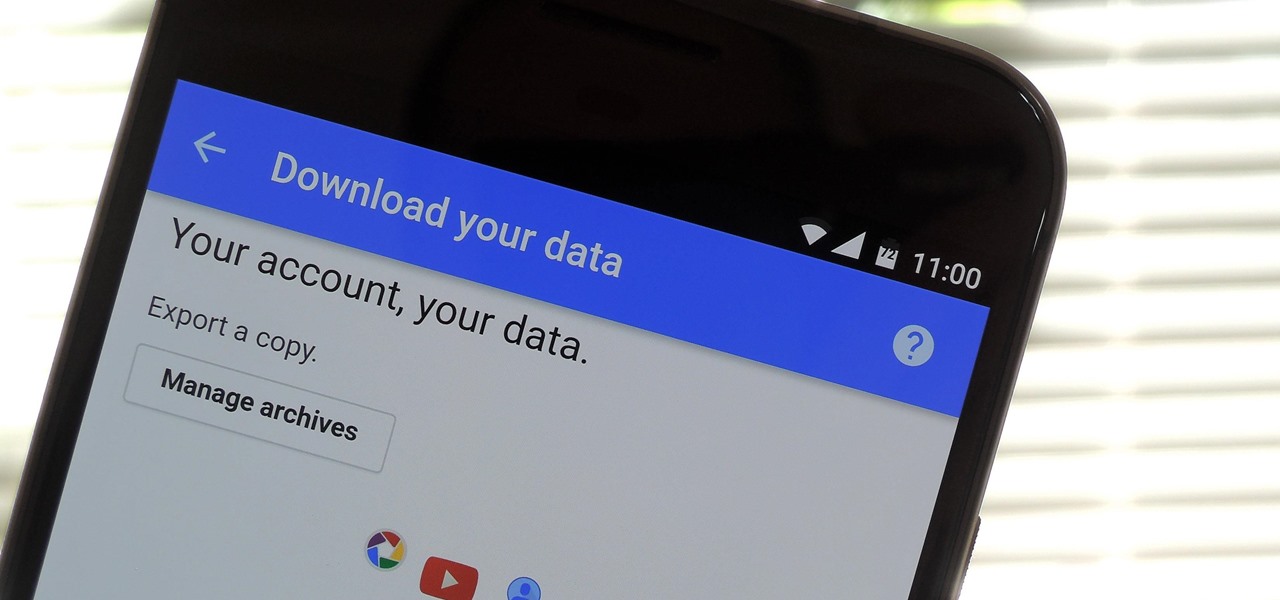
If you're an Android user, Google probably has almost your entire digital life stored on its servers. Family pictures are backed up on Google Photos, your e-book library resides with Google Play Books, videos are on YouTube, chat logs in Gmail and Hangouts, starred places and location history in Google Maps, and so much more.

Data visualization has many applications in virtual and mixed reality, since a third dimension literally adds important depth to the represented information. A new app called HoloFlight is a good example of this, combining flight-tracking data and the Microsoft HoloLens to surround you with a look at every plane in the sky.

Welcome back, my budding hackers! One of the most basic skills the forensic investigator must master is the acquisition of data in a forensically sound manner. If data is not captured in a forensically sound manner, it may not be admissible in court. In my Kali Forensics series, I showed you how to acquire a forensically sound, bit-by-bit image of a storage device such as a hard drive or flash drive, but now let's dive into live memory.

Hello World ! Well, welcome in my post. This will be in series, and this is first part. Throughout the series, I will share my research and findings with you. And that will be on topic, Encryption Is Not Enough. We will see, how Encryption is broken & what countermeasures should be implemented to secure it. Let's begin, Why do we encrypt ?

Welcome back, my neophyte hackers! Digital forensics is one of the fields often overlooked by aspiring hackers. In a rush to exploit every and any system they can, they often ignore learning digital forensics—the field that may lead to them being traced.

As mobile devices become more and more popular, service providers have unfortunately resorted to capping data. What this means is that, depending on the plan you have with your ISP, you could have limits placed on how much data you can use for a set period of time. Once you've hit the limit, your ISP could drastically slow down or throttle your internet speed or charge you outrageous overage fees.

As smartphones become increasingly integral parts of our lives, so does data throttling. Personally, I try to save data any way that I can, so to stave off unnecessary usage, I use the GoogleOfflineVoice to limit the amount of data consumed by voice typing.

If you have a limited or restricted data plan, monitoring your usage can be the difference between escaping the month without overage fees or emptying out your wallet.

One of the biggest problems in data security is authentication of data and its source. How can Alice be certain that the executable in her inbox is from the venerable Bob, and not from the not-so-venerable Oscar? Clearly Alice wants to know because if this file is actually sent to her by Oscar, the file might not be a game, but a trojan that can do anything on her computer such as sift through her email and passwords, upload her honeymoon pictures, or even turn on microphones and webcams. Thi...

If you use apps on your smartphone, chances are you have no idea what those apps are doing with your information. Just this year, there have been several scandals involving apps transmitting user data, like Path uploading users' entire address books onto its servers, HTC's Security Flaw, and Brewster exposing users' personal information (even Ashton Kutcher's). A new service called Mobilescope wants to make sure you always know where—and to whom—your data is going. Lots of apps copy your cont...

Here is a helpful tip for the next time you go on a trip. Don't lose your way, or your money, watch this video and learn how to download Google Maps data onto your Android so you can use it offline.

If you're a certified computer nerd along the lines of NASA scientist Howard from "The Big Bang Theory," then you know how frustrating it can be transferring large amounts of data between an external hard drive or other drive and your main computer, especially when you're in a rush to get experiment data in. Usually this requires mounting the drive into a system or external case first.

Don't be suckered into buying two separate data plans! In this clip, you'll learn how to share your rooted Motorola Droid Android smartphone's 3G data connection with a Samsung Galaxy Tab over WiFi! For more information, including detailed, step-by-step instructions, take a look.