Many people tend to focus on decorating and tidying up their house, often forgetting to care for their patio. This makes little sense to us because the doorway and patio is the first thing all your guests will see as they enter your house. So spruce your patio up by building a patio and walkway out of flagstone.

Learn a stunning effect by just remembering one card. The key card! Follow along as our British headless magician teaches you how to perform this basic magic trick.
Whenever a new Apple event invite arrives, the entire tech industry begins tearing the invite's graphics apart in a bid to decipher what the company may be planning on releasing in the coming weeks.

Apple's latest updates to its operating systems add another security feature to its Find My service, so you have an even better chance at locating your lost iPhone, iPad, or Mac should it ever happen. As long as you have the option enabled, you can leverage other Apple users' devices to find yours on the map.
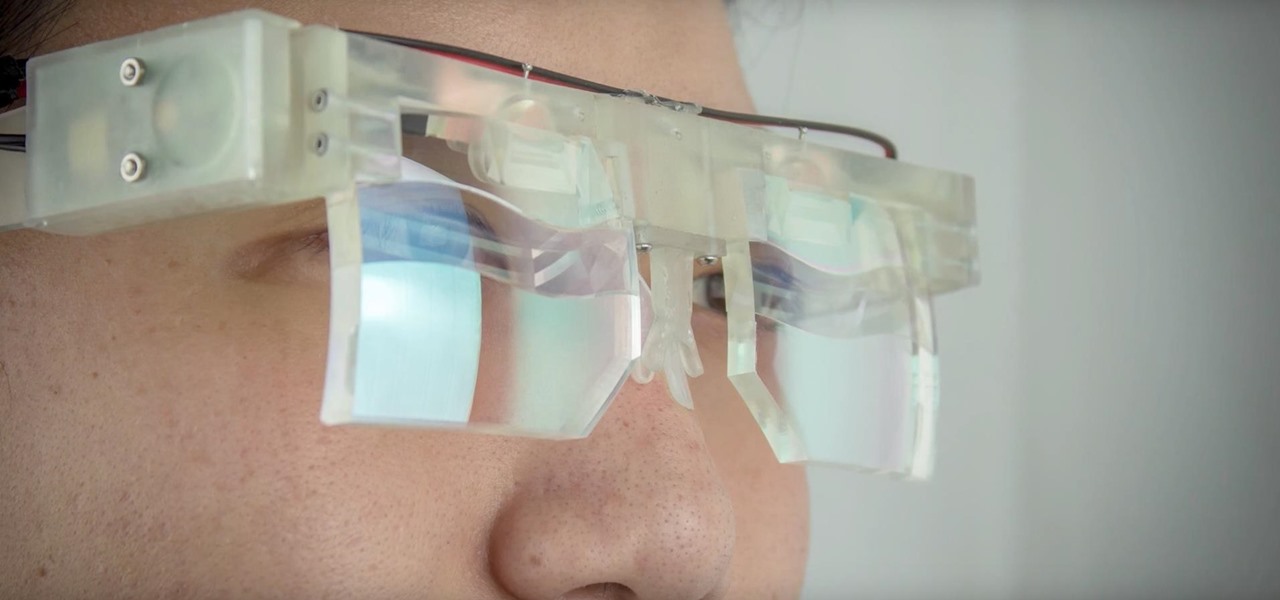
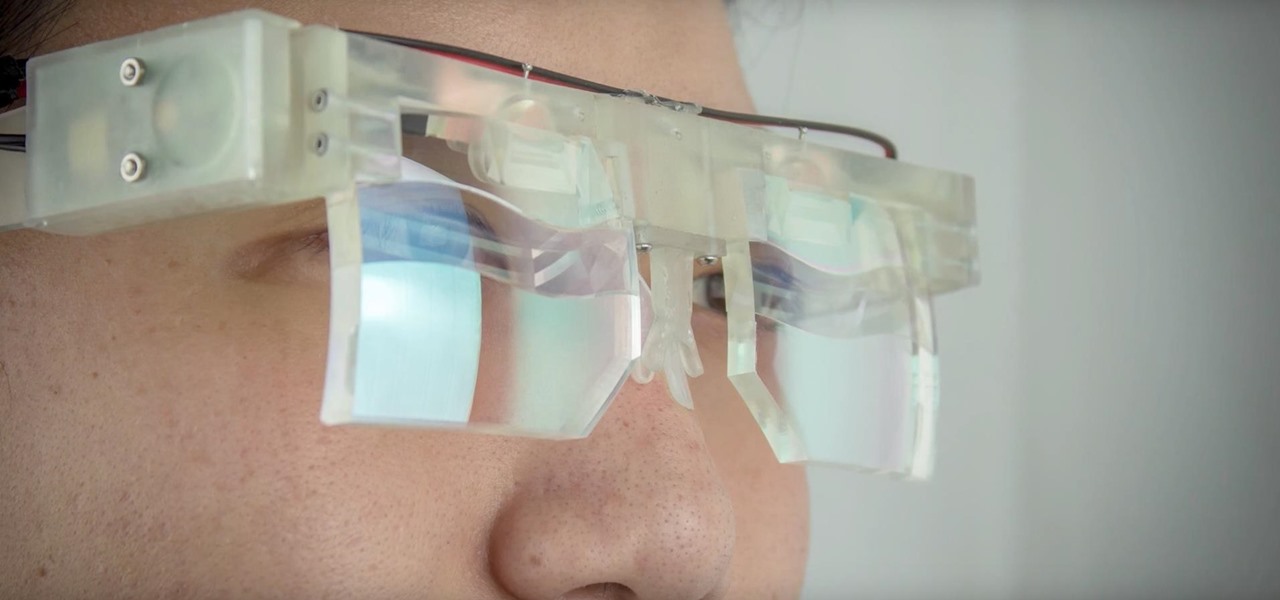
The research team from Nvidia is returning to SIGGRAPH, an annual hotbed of innovation, with two new advancements in augmented reality displays.

If your iPhone XS or XS Max has been suffering from Wi-Fi connectivity and charging issues, Apple just released iOS 12.0.1 on Monday, Oct. 8, as an over-the-air update for all compatible iPhones. The main focus of the update is to give fixes for users going through "Chargegate" and experiencing Wi-Fi issues.

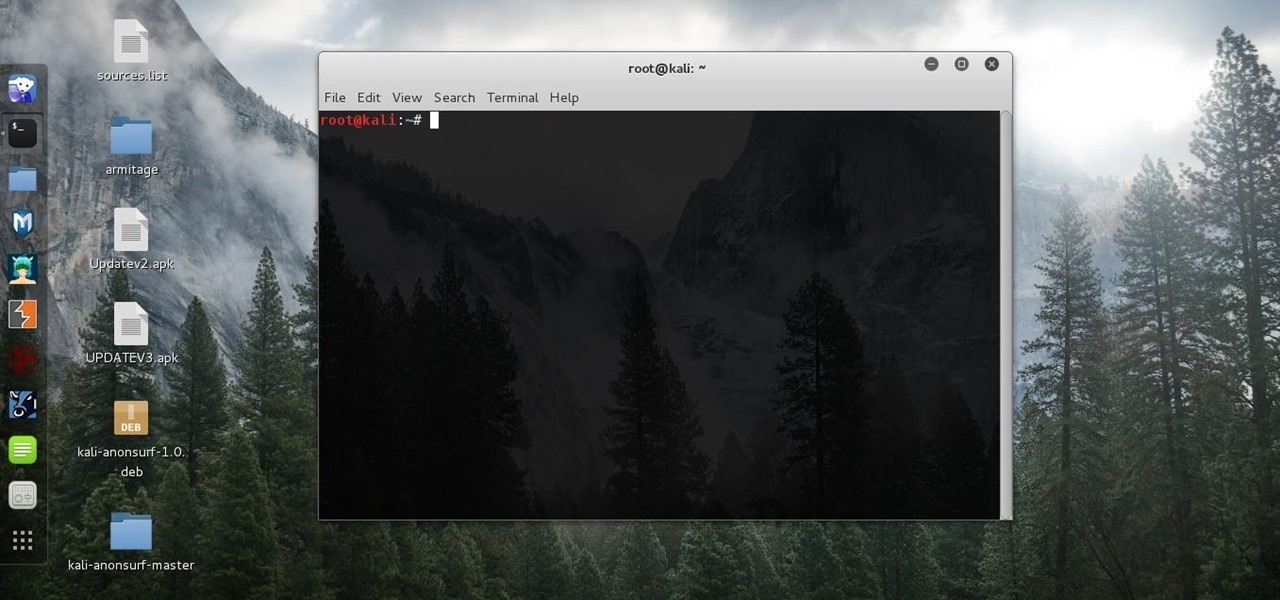
As penetration testers, we sometimes need to securely store customer data for prolonged periods. Bruteforce-resistant, vault-like containers can be created with just a few commands to protect ourselves from physical attacks and unintended data disclosures.

After years of struggling, it appears BlackBerry has finally figured out how to update its iconic design for modern times. The BlackBerry KEY2 pays homage to past devices such as the Bold 9000 while adapting to modern times with the Android OS. The result is a device that might be the best BlackBerry to date.

Snapchat has added yet another social feature to its mobile app, and this one makes it possible to use augmented reality with a group of friends over video.

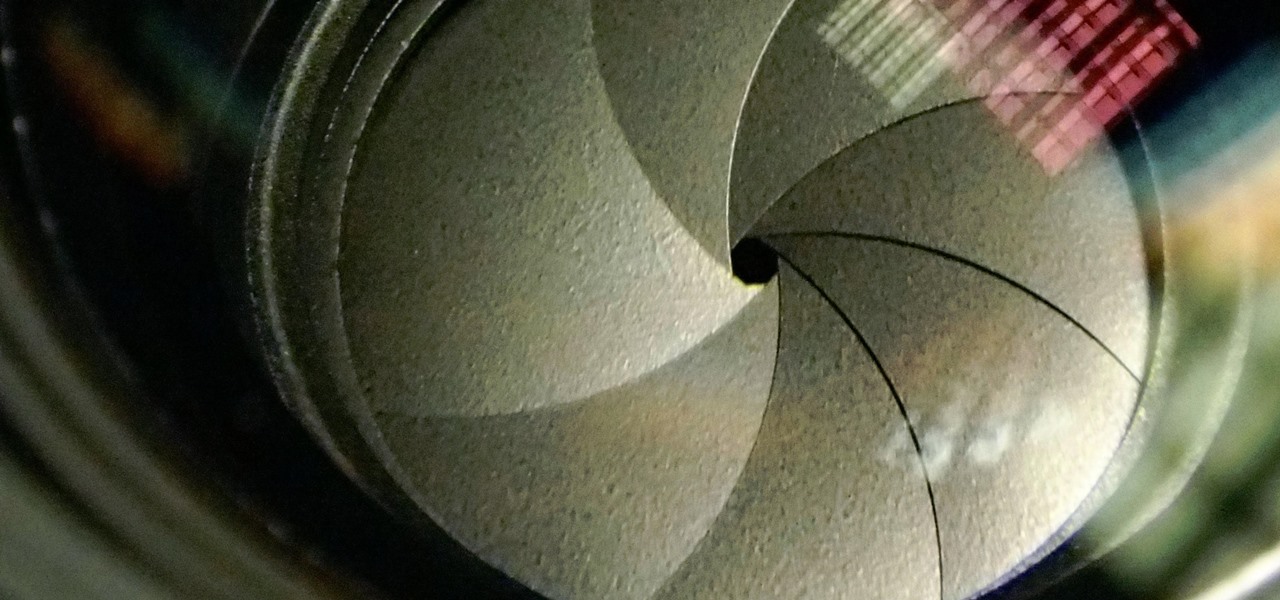
The Galaxy S9 and S9+ have a new camera feature that Samsung is calling "Dual Aperture." On the surface, that may sound like your typical techno-jargon, but it actually has some significant implications for the future of smartphone photography.

It's easy to have your password stolen. Important people like executives, government workers, journalists, and activists face sophisticated phishing attacks to compromise their online accounts, often targeting Google account credentials. To reduce this risk, Google created the Advanced Protection Program, which uses U2F security keys to control account access and make stolen passwords worthless.

Many guides on Null Byte require using the Secure Shell (SSH) to connect to a remote server. Unfortunately for beginners, learning to use SSH can become a confusing mix of third-party programs and native OS support. For Chrome OS users, using SSH is even more difficult. We'll fix this by using the Chrome Secure Shell to establish an SSH connection from any device that can run a Chrome browser.

If your mechanical home button or capacitive navigation keys are on the fritz, doing something as simple as navigating your phone's interface becomes a tedious chore. In this situation, some users have turned to root mods that enable Android's software navigation bar to solve the problem, but not everyone is willing or able to root their device.

This is the very first article in my series on setting up a Mac for hacking. In this series, I will be operating under the assumption that you have a clean install of macOS (previously OS X). If you aren't starting with a clean installation, there may be a few differences, but nothing we can't help you out with.

Hello again, readers! In our previous crypter tutorial, we looked at how we could obfuscate our malware (or any program) by using a simple one-byte XOR key. In this quick tutorial, we will be looking at how a simple little tweak can create a better means of obfuscation. Let's get right into it!

First of all, before we start, the modules and some of the tutorials belongs to Und3rf10w, not mine!

Making sure you have the best gallery app available for your Android device used to be as easy as just installing QuickPic. But late last year, Android's top photo-viewing app was sold to a company who is notorious for permission spamming, so QuickPic quickly lost everyone's approval.

Welcome back! In the last iteration of how to train your python, we talked about functions, and we even made our own! We're going to move on to more types of data arrays (much like lists) in today's discussion.

If your Android device wasn't manufactured by Samsung, chances are it uses on-screen navigation buttons. Colloquially referred to as "Soft keys," these have become commonplace due to their flexibility, as well as the fact that manufacturers don't have to include extra hardware buttons with a propensity to fail.

At the end of an all-day affair with friends or family, I'll unwind and go through all the pictures I took that day as a sort of recap. All too often, though, I'll come across a few that are almost perfect, except I didn't quite position my phone well enough, leaving someone's face cutoff or too much space to one side of the image. It's a fail of a basic and crucial tenet of photography—framing.

Among the additions that Apple's included in iOS 8 for iPhones are a couple of new features to the Camera app, including a timer and manual control of the exposure setting. Hit up the video to see how these new features work, of scroll down for the written walkthrough.

This video will guide you top 10 windows shortcut key which is very useful in everyday computing. Watch the video and follow the steps to know top 10 windows shortcut key.

Since picking up your first crayon, chances are you've had a favorite, or dominant, hand. That hand gets you through the day, taking care of everything from writing to eating. If you've ever been forced to rely on your "wrong hand", you know how uncomfortable and unwieldy it feels.

After a lengthy video and a series of leaks got us a good look at what we can expect from the new HTC One, codenamed M8, the guys over at GSMArena have brought it full circle.

I love cryptography. It is like a great gigantic puzzle for me to solve. However, it is more important than that. It is also how we keep secrets safe. Not just sorta safe either, but really safe.

Macrame Owl - Decoration for keys / key ring or necklace / How to / DIY Video: .

A few weeks ago, Bluebox Security uncovered a bug that could potentially effect 99% of Android devices. Bug 8219321, dubbed the Master Key bug, works by allowing applications with modified code to pass Android's signature verification system, thereby bypassing security measures that normally wouldn't allow these apps to be installed.

Video: . In this tutorial I show you how to get a perfect Chroma Key using After Effects.

It has happened to everyone at one time or another, but if you work in an environment with cars, it may happen much more often.

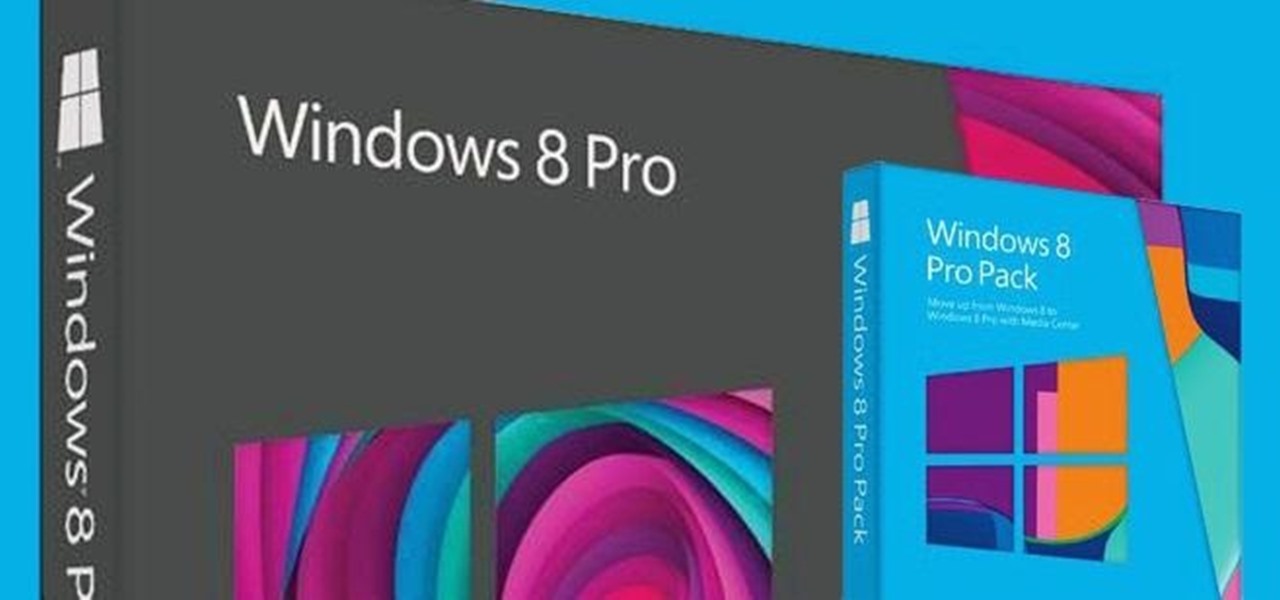
Anything free is cool, but getting a fully upgraded operating system for the great price of nothing is downright awesome. A recent exploit was uncovered that allows users to get a free copy of Windows 8 Pro directly from Microsoft's own website. Seriously.

Anyone who does a lot of photography knows that the right exposure can make all the difference in the world. Taking a picture of something in motion requires a long exposure, so if you've ever wondered why your fireworks photos never quite turn out right, your shutter speed could be the key. Photographer David Johnson decided to put a twist on the classic long-exposure fireworks photo. Normally, when people take photos of fireworks displays, they just set a long exposure for somewhere over 3 ...
The Internet has had a huge influence on many areas of our lives, but, in particular, has resulted in nothing short of a revolution in the way we work. The web has offered the sort of flexibility to the individual that few people would have dreamed of just a couple of decades ago. And where once a global marketplace was available only to a handful of multinational corporations, today thanks to the Internet, we can all access it.
I've noticed that a few people using the crypto-currency, Bitcoin are having issues importing private keys to their Bitcoin wallet. This is easy to do and doesn't require anything other than your Bitcoin client/daemon (as of ver0.6.0 ) and the command line.

If you're new to Google+ and want to know how photos that are uploaded by Google+ users can be browsed or viewed, take a look at this tutorial. You can use the arrow keys to navigate the Google+ photo galleries, or simply click on the photos at the bottom of the lightbox.

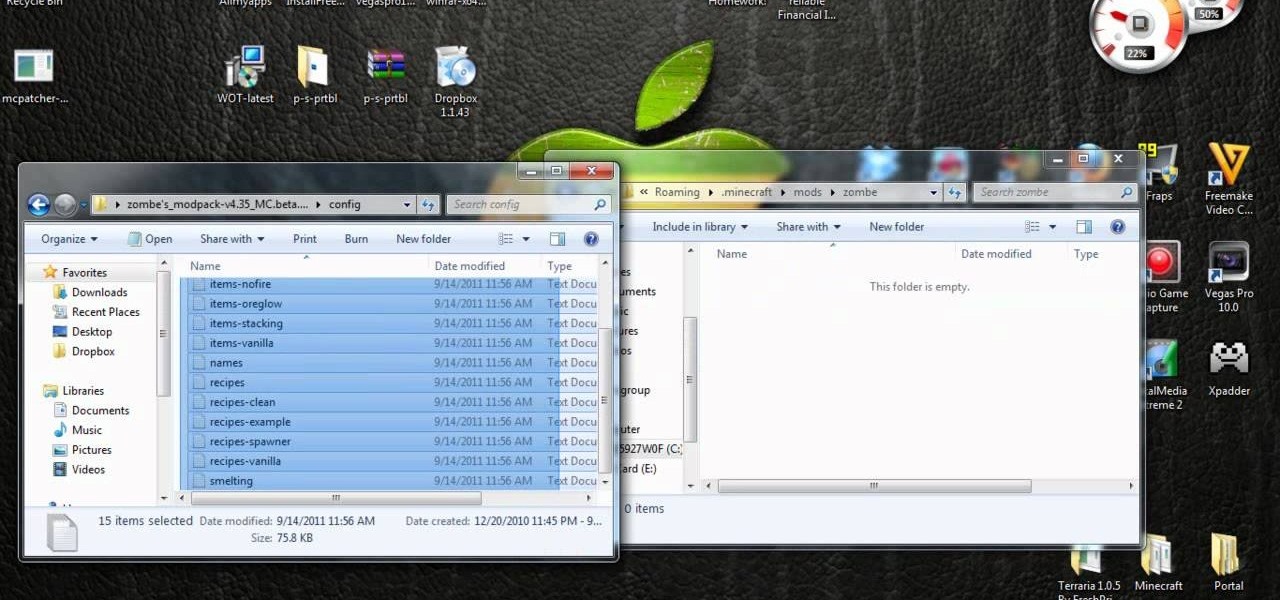
What better way to enjoy the beauty of the blocky world of Minecraft than by flying across the land? If you want to fly in the new release of Minecraft 1.8, take a look at this tutorial on how to download and install the Fly Mod, a part of Zombe's mod pack, with the help of MC Patcher HD. The guide will also inform you on how to bind keys to the different flying controls.

Marvel vs. Capcom 3 is a frenetic modern fighting game, and learning how the combo system works and being able to apply that knowledge on the fly is the key to arcade success in the game. This video will teach you how the combo mechanics in MvC3 work and how you can use them to come up with new combos on the fly and beat any character, as any character, any time.

The Recon character class in Battlefield Bad Company 2: Vietnam is a thinly veiled sniper, and utilizing their target-spotting functionality is key to effective sniping in this game. This video is a complete guide to effective Recon play, teaching you about all your abilities, guns, and how you can spot targets to make yourself much more effective from much further away.

Measure twice cut once applies to filmmaking as well as construction or any other complex process really, and that's why preproduction is they key to actually finishing your film on time and budget. This video will help you with several preproduction tasks, including storyboarding, making a shot list, lining / timing your script, and scheduling the actual production of the film.

Nuketown has emerged as one of the most popular multiplayer maps in Call of Duty Black Ops, so knowing it is key to ranking up fast in the game. Watch this video for an inside-and-out guide to the map and way to get more kill in it while playing Deathmatch.

Once you've unlocked Dead Ops Arcade in Call of Duty: Black Ops on the Xbox 360 (and PC), you can start earning some more achievements, and this video will show you how to get the "Easy Rhino" achievement. The key to earning this one is to NOT kill any of the zombies until they're in a large group, then point at them and press the Right Trigger (RT) to burst and that's it.