
How To: Copy and paste on a computer
Why type everything twice? If you don't know how to copy and paste you are missing out on an incredible time saver. Check out this tutorial and learn how to speed up your work.


Why type everything twice? If you don't know how to copy and paste you are missing out on an incredible time saver. Check out this tutorial and learn how to speed up your work.

This masterful drawing session from idrawgirls instructs us how to draw a mysterious girl specifically the facial figure, face, hand and upper body front view. First you will establish, very lightly, the facial shape, direction of the eyes, and the shoulders and upper body. The key here lies in the direction of the eyes, casting the face slightly downwards, creating that ineffaceable mysterious effect. Another important factor specific to the female face is keeping the nose close to the eyes ...

Hello! My name is Nicole Valentine and on behalf of Expert Village, I'm here to talk to you about how to coordinate birthday games for a birthday party. Now we're going to discuss the game can you read my mind. This game has a little bit of mystery flavor to it. You'll see what I mean. In this game, you need to utilize 2 rooms. In the first main room, you have all the guests of your party. Then later we'll instruct the guests we're going to play a game called can you read my mind and the goal...

Your iPhone is fairly secure by default, but Apple's Lockdown Mode takes it to Fort Knox levels of protection. If you're a high-value target for spyware, phishing attempts, and other sophisticated cyberattacks, it's an essential feature. But for almost everyone else, it's an extreme move. If you simply want to verify someone's identity when chatting, Contact Key Verification is a more practical option.

We might never truly know all of the colors behind old and classic black-and-white photos, but thanks to technology, we can get a pretty accurate colorization. Although Photoshop is a popular way to colorize these images, you can now use your iPhone, along with a nifty shortcut, to transform and give new life to vintage photos.

Remember when typing without physical keys seemed ridiculous? Now, touch typing is the smartphone norm. That said, mistakes are inevitable on small screens. So before you start hammering on that delete key or shaking your iPhone like a madman, know that there's a better way to undo text you didn't mean to type — no shaking involved.
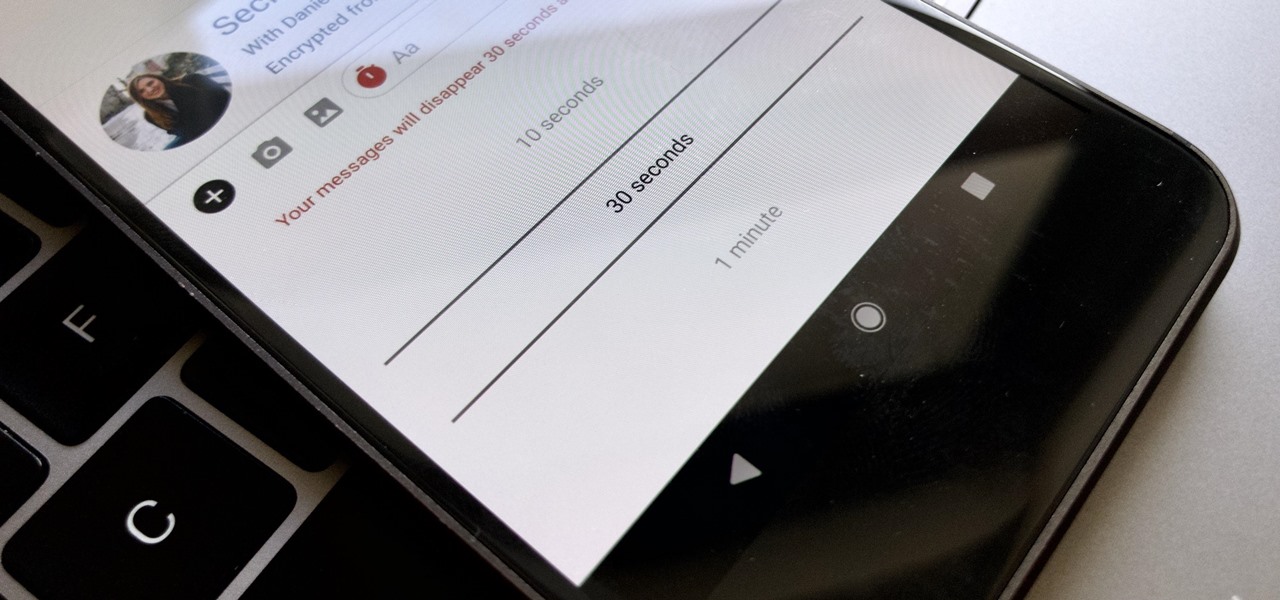
Traditionally, if you were looking for end-to-end encrypted messaging, you'd stick with something like iMessage, WhatsApp, or Signal. However, if you already use Facebook Messenger, you have all you need for truly private chats with its built-in E2E encryption. It's available to all users, on Android and iOS — you just need to know where to look.

With the official launch of Magic Leap One expected by the end of summer (translation: days from now), Magic Leap's hype machine just took a big hit with the sudden loss of a key marketing executive.

The latest Star Wars movie, Solo: A Star Wars Story, has grossed almost $350 million worldwide during its first month in theaters. This is a good opportunity to discuss how hackers can use media hype (in this case, Hollywood movie hype) to disarm an unsuspecting Windows user into inserting an evil USB stick into their computer.

Now that we finally have vertical plane recognition in ARKit (at least on a developer level until the spring iOS 11.3 release), the real promise of mobile augmented reality is beginning to come into focus on iOS. But a new report indicates that a major near future advancement of ARKit that could change everything has been put on hold by Apple.

Scary movies seem to be a natural fit for augmented reality experiences, with the latest example coming from the Insidious film franchise.

Ransomware is software that encrypts a victim's entire hard drive, blocking access to their files unless they pay a ransom to the attacker to get the decryption key. In this tutorial, you'll learn how easy it is to use the USB Rubber Ducky, which is disguised as an ordinary flash drive, to deploy ransomware on a victim's computer within seconds. With an attack that only takes a moment, you'll need to know how to defend yourself.
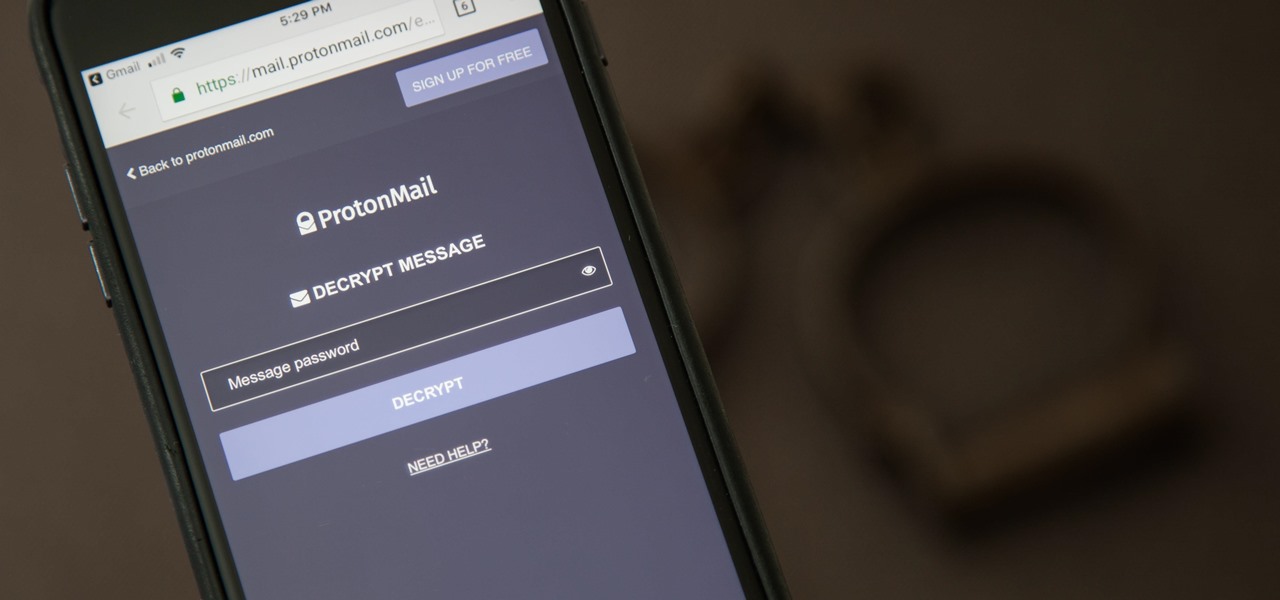
It can be hard to get all of your friends, family, coworkers, and acquaintances to jump on board with the more-secure email system ProtonMail, but that doesn't mean you can't still send them encrypted emails. Best of all, they won't even have to install any other apps or extensions to read or reply to the messages.
As you all journey along with me on my challenge to become some sort of Instagram expert, let me share with you one hack that is currently helping me out a lot. If you've ever wanted to put a line break in your posts, then keep on reading.
With many of the companies working in augmented and mixed reality focused on the Augmented World Expo, the finance side of the industry has been relatively quiet.

WhatsApp sneakily made some security changes to iCloud backups without your knowledge, ladies and gents. Not that strengthening security is a bad thing, but still!

Augmented reality could come in very handy for those of us prone to losing things—namely, our wallets. Pixie Technology, a company from Los Altos, California, has developed a way to locate your lost wallet and keys using AR technology and tracking chips, a platform they call the "Location of Things."
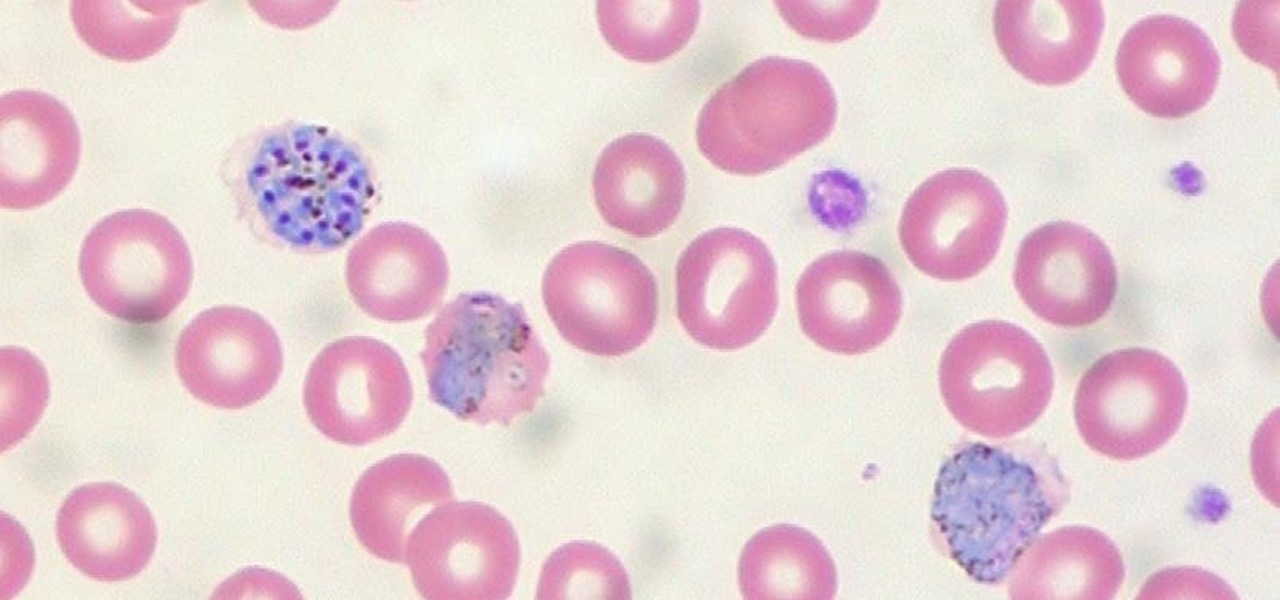
When the mosquito that carries the malaria parasite (Plasmodium falciparum) bites someone, the parasite must travel to the liver where it undergoes part of its lifecycle before infecting red blood cells and spreading to its next host. Until now, the first step of how the parasite gets to the liver hasn't been clear.

Ask anyone that works on the development of driverless vehicle technology and there is a very good chance that AutonomouStuff will have supplied something to their project.

With the death of Google's Nexus line, the market for phones with top-notch specs at midrange prices is now wide open. OnePlus is apparently ready to fill this void, as they've just announced the OnePlus 3T, an iterative update to their OnePlus 3 flagship only five months after initial release.

As pentesters and hackers, we're going to be working with text frequently — wordlists, configuration files, etc. A lot of this we'll be doing on our machine, where we have access to whatever editor we prefer. The rest of it will be on remote machines, where the tools for editing will be limited. If nano is installed, we have an easy-to-use terminal text editor, but it isn't very powerful.

Samy Kamkar, security researcher and friend of WonderHowTo, just had one of his devices featured in Mr. Robot.

You've likely seen light-up musical keyboards that teach you how to play a song with visual cues, but few of those devices exist and have a limited number of songs you can actually learn. But Karl Baumann and his HoloLens Hackathon team figured out that in mixed reality, you can learn music with visual cues with any piano.
It looks like Apple is finally going to do something to address all of the complaints about their unremovable stock apps clogging up people's home screens. While bloatware is a bigger problem on Android where you have to deal with apps from Google and carriers, an iPhone can still get pretty cluttered with all those stock Apple apps. I mean, just look at all this crap... AppAdvice noticed two new keys in the iTunes metadata that strongly suggest that you'll be able to get rid of stock apps on...
In this Tutorial I will show you how you can use the frequency of letters to decrypt the famous Caesar cipher. I hope it is easy to understand and helpful for getting in touch with basic cryptanalysis. If you find any mistakes or have questions feel free to ask me. Finally I ask you to give me feedback which I will take into account for the next part.

Unless you're in law enforcement, you won't usually have a flashlight on hand for those rare moments when you need to sift through the dark. However, it is very likely that you will have your phone on you, so you'll have fast access to a bright light with just a few easy taps.

These days, if you're having friends over, they'll probably ask to log into your Wi-Fi network before asking for a drink. But if you've forgotten your password, it can be quite hard to find, since most devices obscure the characters with asterisks.
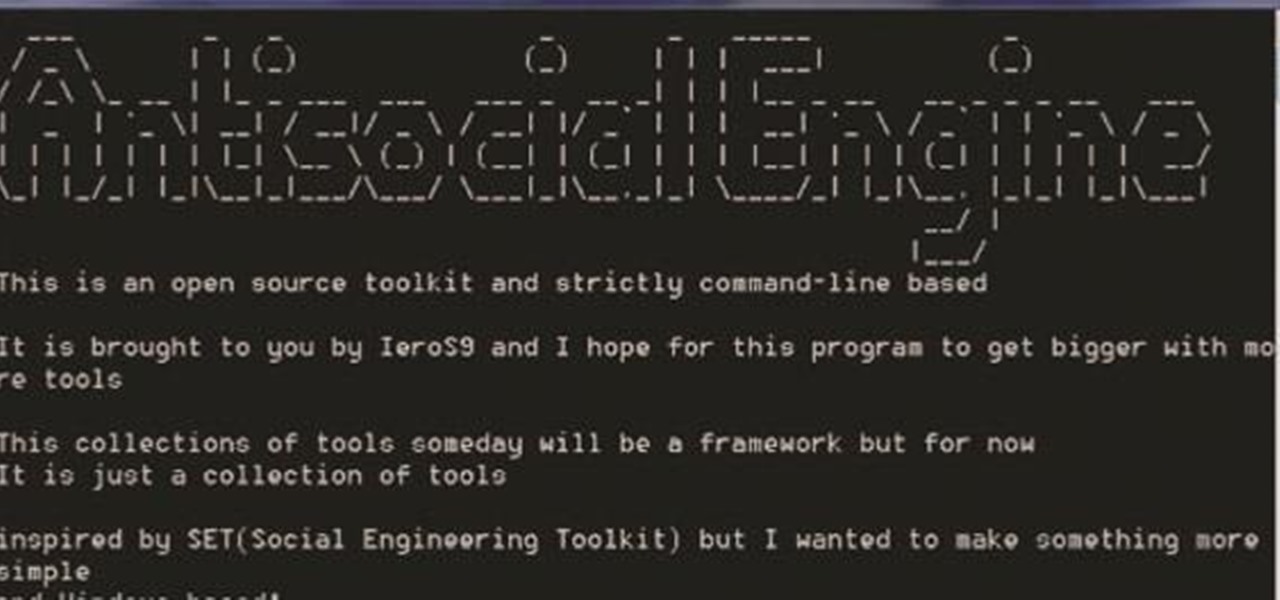
A.E Hi again this is my second post on nullbyte. The first one was on how to make a remote screenshot captor, now I will give you a presentation for a project of mine(I have named It Antisocial Engine) that It is not something extraordinary but will help many guys.
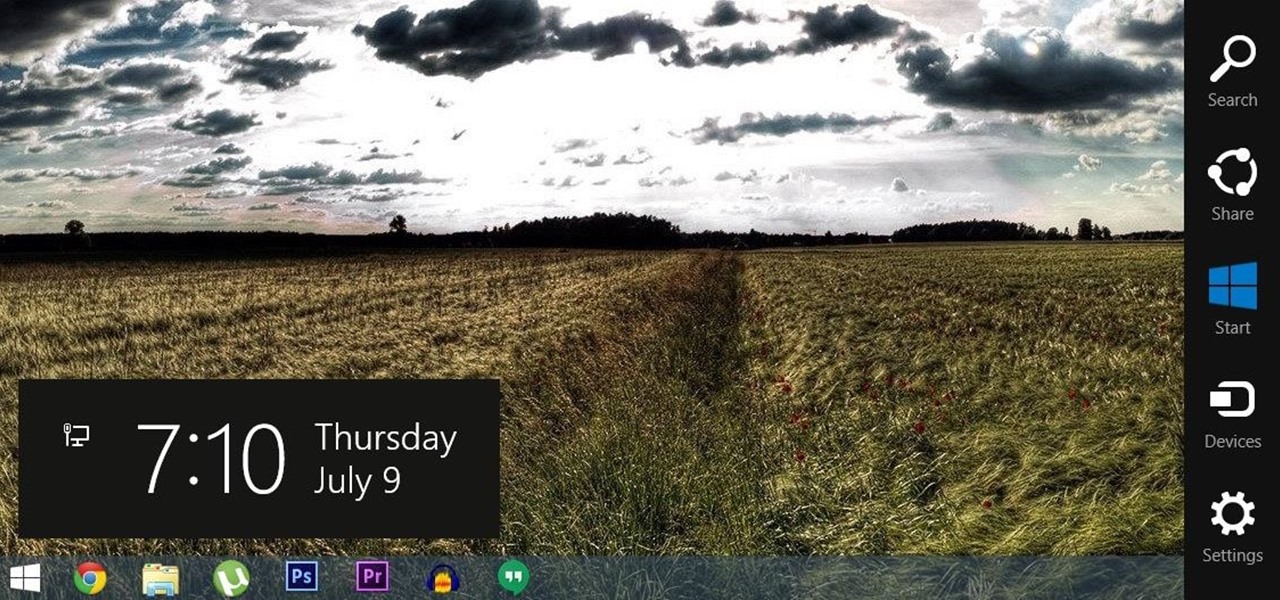
For all of the flak that Windows 8 received from desktop users, it certainly had some interesting and unique features. For instance, the "Charms" bar allowed you to easily access several key menus by simply hovering your mouse pointer in the top- or bottom-right corner of the screen.

As your Galaxy S6 lies on your desk while you're hard at work, it's difficult to resist from periodically pressing the wake/lock button to check the weather or glance over any notifications you may have on your lock screen. While pressing the hard key is easy enough, there's an even easier method where you simply hover your hand over the device to wake the screen.

If you don't like watching YouTube videos on your computer with your hand glued to your mouse, the next best thing is using keyboard shortcuts. They may not seem any easier than clicking, but once you get them down it's a whole other story. Plus, there are some features you might not otherwise use (I'm looking at you, speed control) unless the shortcuts existed.

The new Nexus 6 and Nexus 9 models will be shipping with Android 5.0 Lollipop preinstalled, and the Nexus 4, 5, 7, and 10 will be getting the new OS update from Google very soon. But where does that leave the rest of us?

The "Smart Keyboard" on the LG G3 has received a lot of praise for its ability to adequately analyze user keystrokes, provide adjustable sizes, and customize key placements, among other things. These features, combined with predictive text, swipe gestures, and autocorrect make the Smart Keyboard one of the most powerful typing tools available for Android. Now, it's easy to get it installed on your Samsung Galaxy Note 3.

Pie controls are navigation soft keys that can be displayed by swiping up or from the side of your screen, allowing you to navigate, search, call up the power menu, take screenshots, and a lot more. Not only are pie controls functional, they make using Immersive Mode a breeze since the regular nav bar was no longer required.

A couple months ago, I attended a Pokémon-themed party. Everyone dressed as their favorite Pokémon or trainer, Poké balls flew around the backyard, and more importantly, there was a lot of Poké booze. My friend who created the colorful drinks you see below informed me that they were infused with Skittles. This, my humble readers, was a defining moment in my life.

Update, November 12, 2014: Android 5.0 Lollipop is officially out now. If you haven't gotten the OTA yet, check out our new guide on installing the official Lollipop builds on any Nexus for download links and instructions, for Mac or Windows.
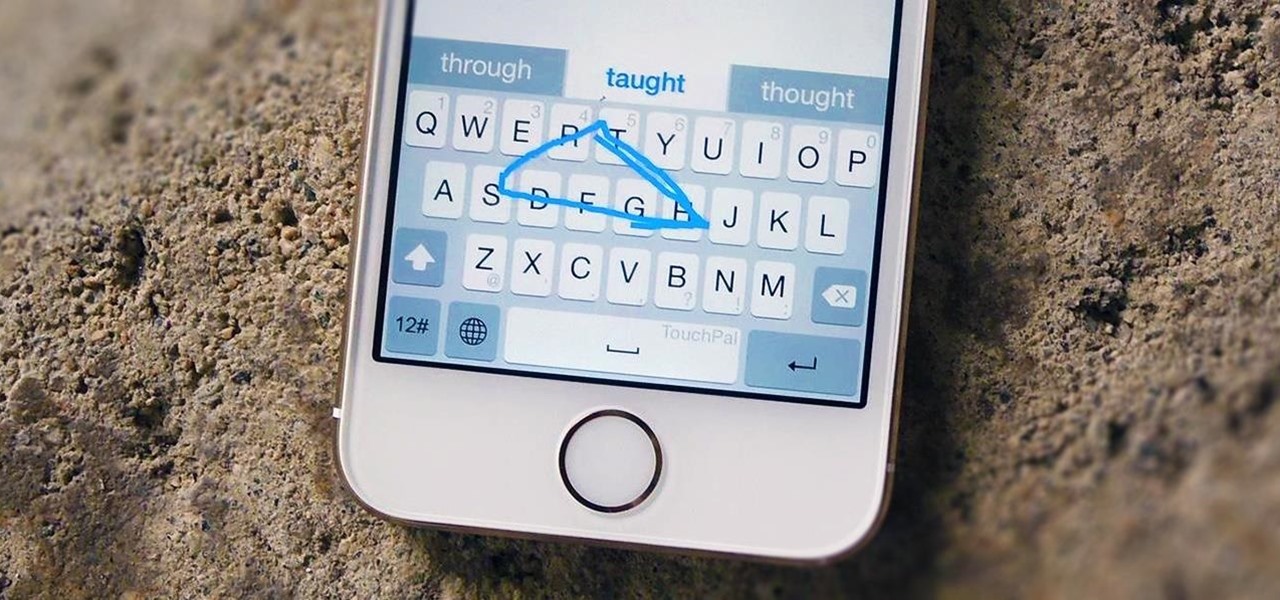
Rather than just use the stock Apple keyboard, iOS 8 now lets you use keyboards from TouchPal, Fleksy, SwiftKey, Swype, and more. I'll be showing you how to set up a third-party keyboard on your iPad, iPhone, or iPod touch, as well as giving you a firsthand look at TouchPal's keyboard for iOS 8.

There are two types of tablet users in the world—those who like their quick settings up top, and those who want them on the bottom. I fall into the latter category, and there are a couple of reasons for it.

The new HTC One M8 has only been out for a few hours, but it's apparent that some people had their hands on the device before the announcement. And well, one them decided to drop the thing in water.
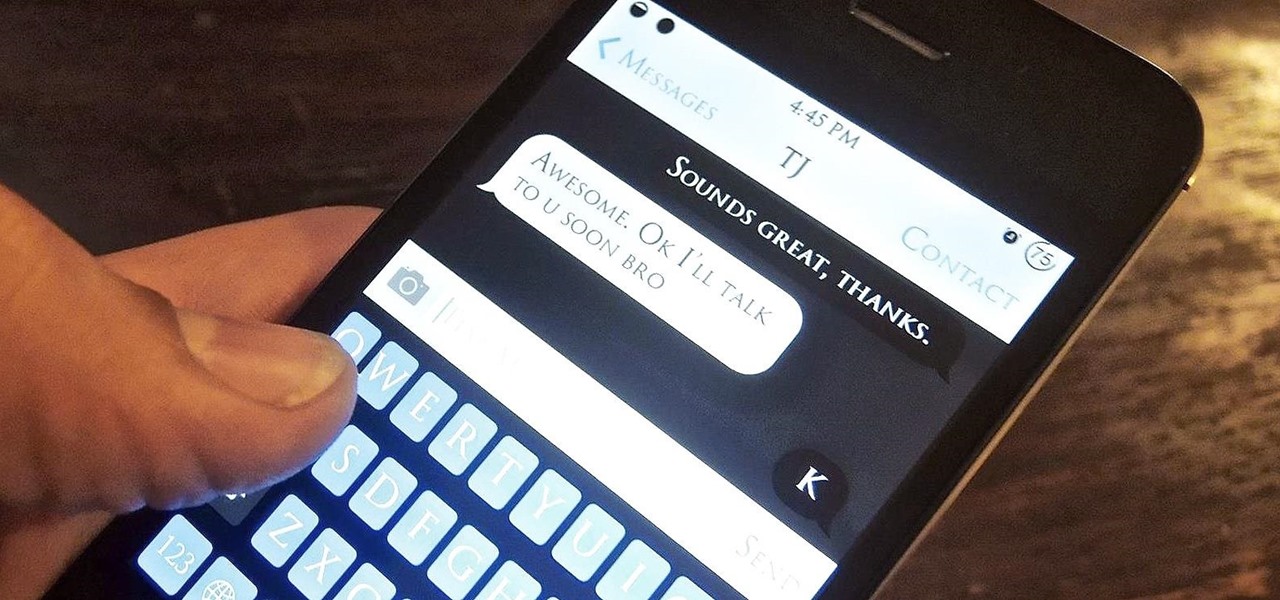
WhatsApp may be one of the most popular mobile messaging services around since it's multi-platform, but if most of your family and friends use iPads and iPhones, there's no need to go beyond the stock Messages app.