You can learn how to make a cheap green screen in your home for chroma key effect. You will need a wall, a green poster frieze paper, masking tape, and blu-tac. You can use Abobe Premiere to chroma key effects on to the green screen backdrop.

Many operators use elevators to control access to particular floors, whether it be the penthouse at a hotel or a server room in an office building. However, the law requires them all to have a fire service mode, which gives emergency access to restricted floors, and a hacker can use that to bypass security altogether.

Welcome back, my novice hackers! As many of you know, recon is crucial to a successful hack/pentest. In most cases, hackers spend more time doing good reconnaissance than actually hacking. Without proper recon, you are simply guessing at what type of approach or exploit is going to work and, as a result, your time is wasted without any useful outcomes.

Hello my fellow hackers, it's been a while since my last post, I can't get the time now-a-days for the posts but can manage to tend to comments.

Last year, the Washington Post's Ashley Halsey wrote an article on what really happens to your luggage at airports. In it, they unwittingly published a photo of the master keys the TSA uses for TSA-approved baggage locks. Now, thanks to that picture and a French lock-picking enthusiast, anyone with a 3D printer can make their own master keys to unlock any TSA-recognized locks.

One of the biggest gripes I initially had with the LG G3 was the lack of options for the Shortcut keys, which are the volume keys that allow you to launch the camera or the QuickMemo+ app directly from the lock screen. I never use QuickMemo+, so having it as a shortcut was a complete waste of functionality.

Welcome back, my rookie hackers! As hackers, we are often faced with the hurdle of cryptography and encryption. In some cases, we use it to hide our actions and messages. Many applications and protocols use encryption to maintain confidentiality and integrity of data. To be able to crack passwords and encrypted protocols such as SSL and wireless, you need to at least be familiar with the concepts and terminology of cryptography and encryption.

Many of our everyday apps include a menu tab or search bar, like Chrome and Twitter. In fact, a lot of times those are the first things we go for, as search is universal in most apps, and app settings are just about always accessible through the menu.

Piano keytops can become worn or broken. Replacing them with new keytops isn't as difficult a task as some would think. In the demonstration video you can see how the keytops are replaced and the materials needed in order to complete the job. Having the right supplies and information can make this piano repair job achievable.

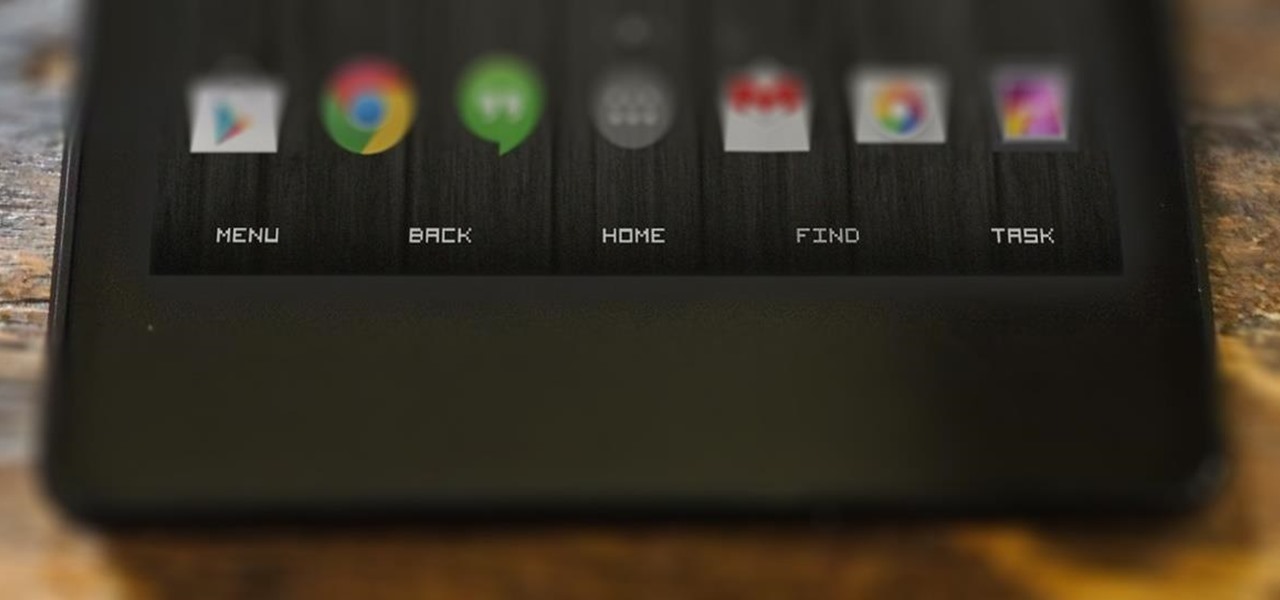
I know all of you softModders love these little modifications, like enabling the hidden battery percentage on the Nexus 7 or getting the exclusive Google Launcher on your Nexus, so here's an easy one that lets you hide the soft-keys from your tablet, which will actually expand your screen to look a little bit longer.

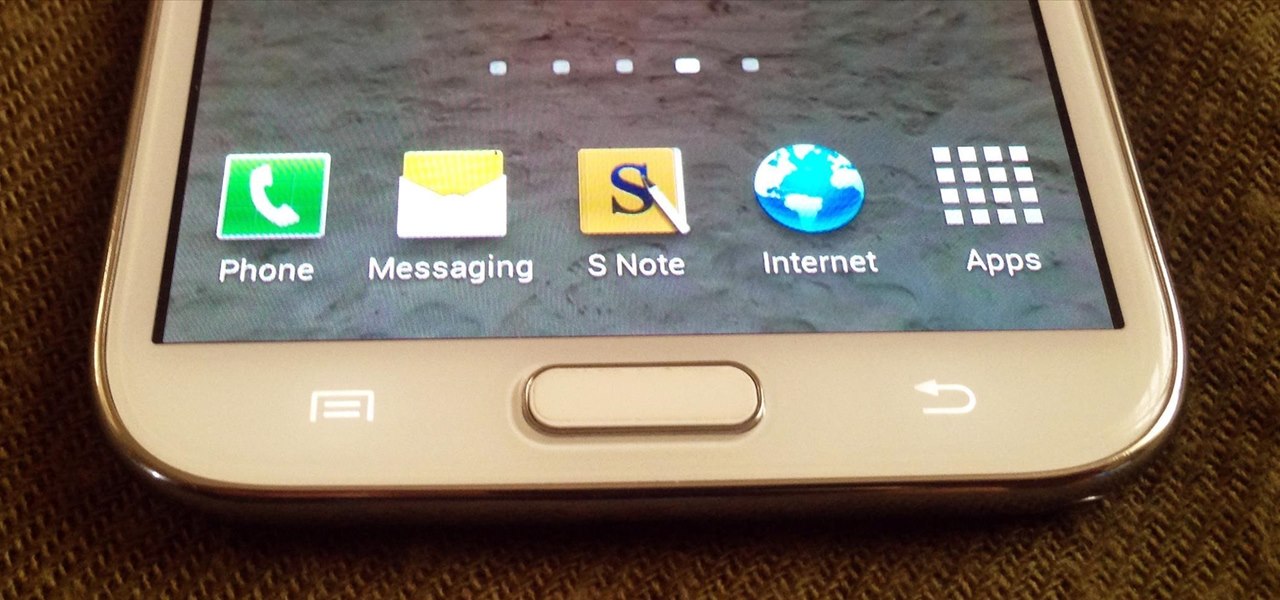
There may only be a few hardware buttons on your Samsung Galaxy Note 2, but when they're not working, your phone might as well be a doorstop. A few years back, I was texting while walking to class and a student on a bicycle crashed into me. My phone was flung thirty feet—straight into a puddle. I picked it up and checked for damage, but everything seemed okay. The biker apologized profusely, but nothing was wrong, so I told him not to worry about it and proceeded to class.

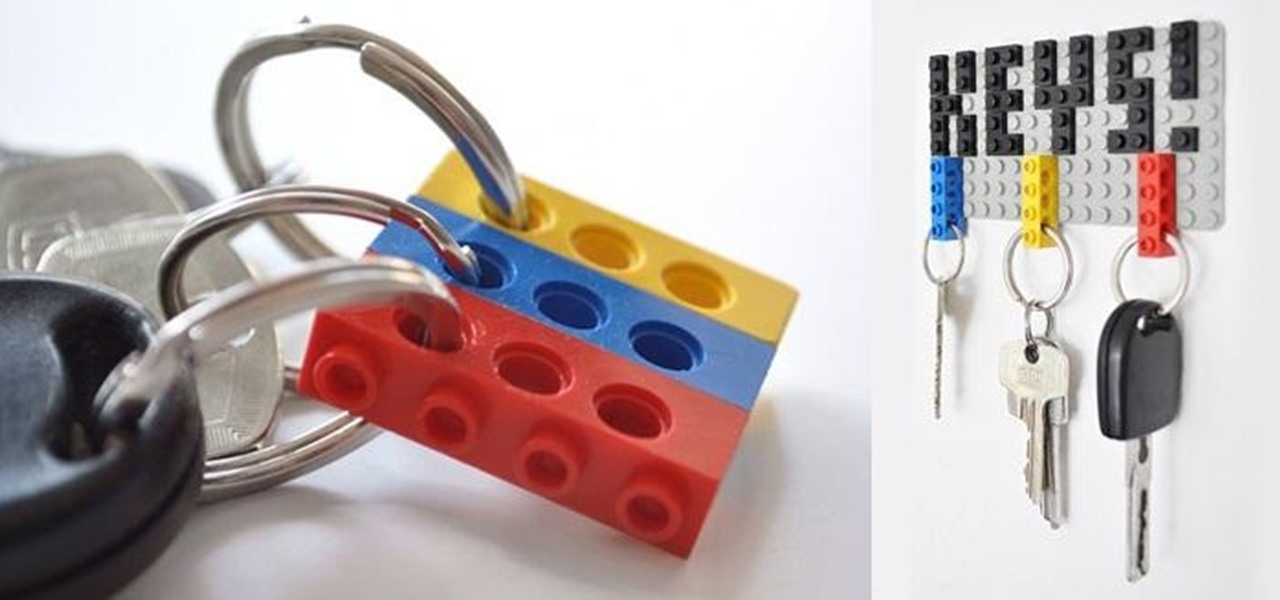
LEGO may no longer be in its heyday, but those colored building blocks of joy can still make some really cool and creative things. I mean, take a look at these pieces from LEGO artist Nathan Sawaya. While making something like that is undoubtedly impressive, it could be just a little too difficult for the common LEGO enthusiast—and expensive (LEGOs aren't cheap these days). So, for the regular LEGO-builders, usefulness is more important that extravagance.

Linux is generally a pretty stable OS, but occasionally things happen. However, as long as your keyboard has a SysRq key, you'll never need to worry about freezes again.

You've done it, I've done it, almost everyone who owns a car has done it: they've gone an locked themselves out. Well, this good how-to shows how to get back into your older model car with nothing more than a coat hanger. It will requre some trial and error to get it done, but this video is a good primer.

Jazz is a complicated style of music that takes a completely different style of thinking and playing to even do it somewhat decently. Soloing in its own right is the toughest, but there's a great way of getting started, and thanks to Jeff Richman from Musician's Institute, you will learn how! In this amazing video lesson, he goes through showing you the various ways of using melodies and key centers to really bring out your solo over any sort of Jazz Changes.

In this video tutorial, viewers learn how to browse web pages without a mouse. Users will need to use the Mozilla Firefox browser. When you're in the Firefox browser, press F7 or click on Firefox, click on Preferences and select the Advanced tab (Mac OS X). Now check "Always use the cursor key to navigate within pages". This will activate character browsing, allowing the user to use the arrow keys to move up and down the page. Holding Shift will allow users to select a text. This video will b...

Doing piano exercises improves your strength and dexterity in your hands and wrists. It helps you to become more comfortable with the geometry of the keyboard. You should do exercises everyday for at least 5 minutes a day. Practicing everyday sets a routine and a habit of playing.

Start out playing the piano by learning one of the most famous pieces of music in the world. That song would be "Clair de lune" by Claude Debussy. And this video starts you out with playing and learning the clefs, flats, key signatures, and black keys that will help you begin playing this work of art.

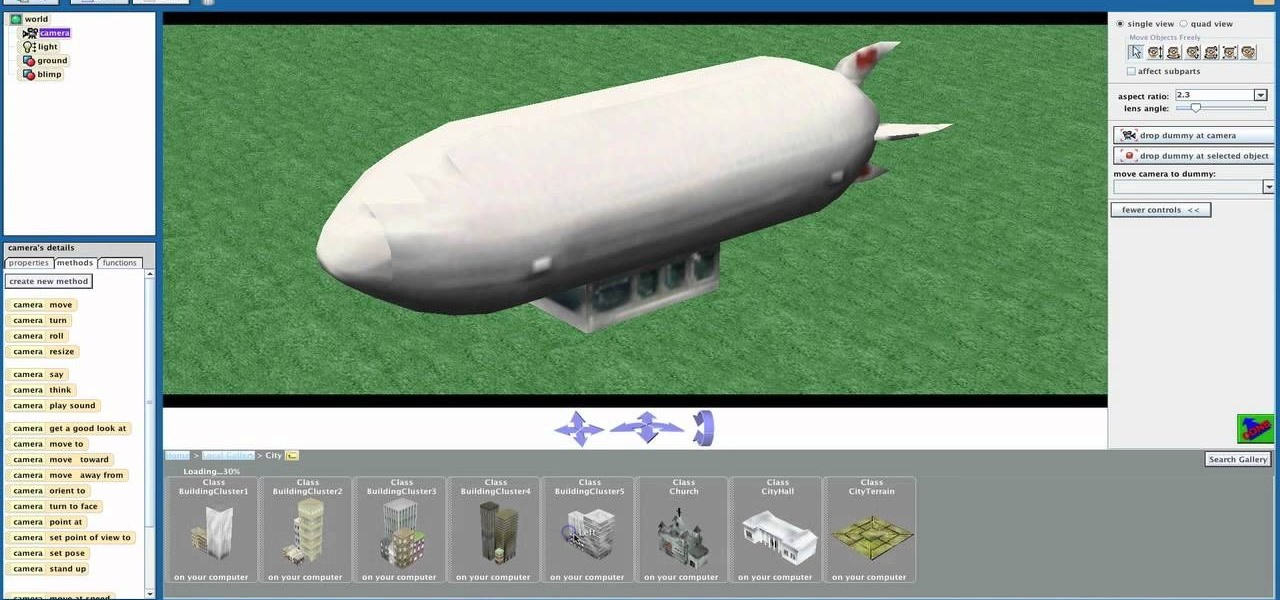
Shaun will teach us how to create a 3D video game compatible with MAC or PC with no prior programming knowledge. First download Alice, a 3D World program that can be turned into a video game. Open Alice, click on "add objects", click on "more controls" and select your choice of aspect ratio such wide screen. Now you can import your own 3D models that Shaun will show you at the end of the tutorial or choose from a wide selection that comes with Alice. In addition, if you click on "home," "web ...

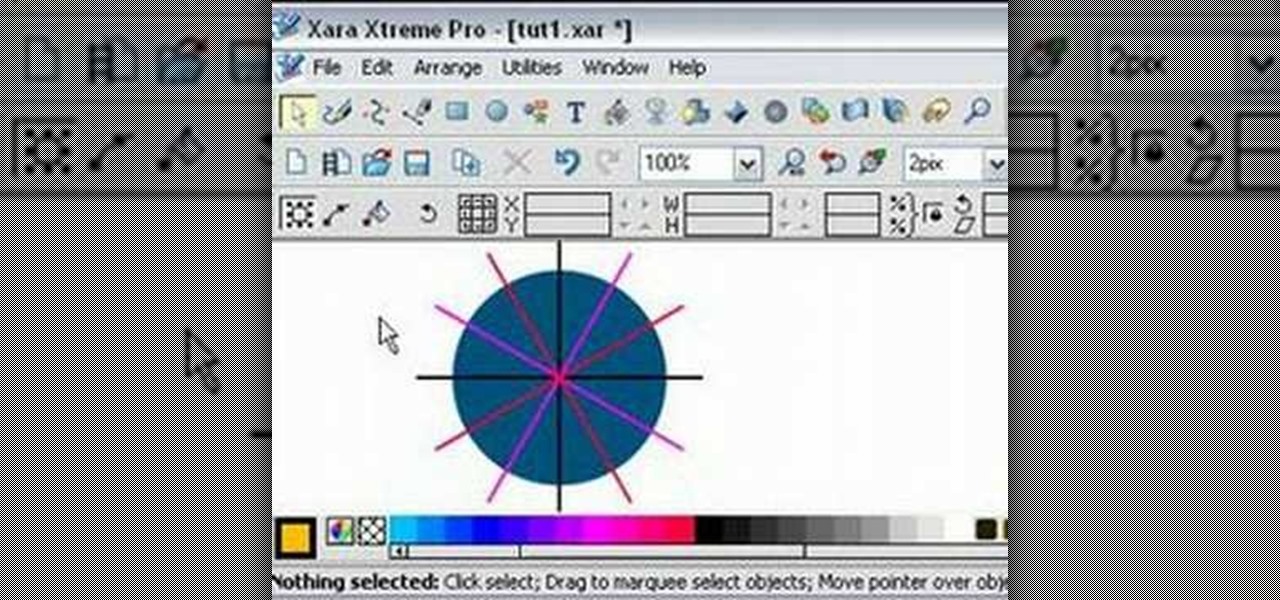
Learn how to split a circle into segments with Xara Xtreme. First select the shape editor tool. Drag the tool to the circle. The dialogue at the bottom communicates what steps to choose next. Holding the Ctrl key drag a straight line within the circle, click on the selector tool (yellow arrow on the left of the middle row) to enable the option of selecting. This saves 1 line on drawing layer 1 also and enables the marquee (flexible box) that you want to manipulate around the circle encasing t...

In this tutorial the author shows how to find out a Cool XP Easter Egg hidden in the XP which comes by downloading the latest update of widows update. The author now opens Internet Explorer and visits the windows site. Now he quits the explorer and holds down both the Control key and alt key and right clicks on the desktop seven times. Now keeping the control key pressed, he releases the alt key and right clicks the desktop and chooses the option 'Create ShortCut'. Now he releases all the key...

For anyone wanting to keep information private, plain text is a format of the past. Instead, cheap, powerful encryption is widely available, but often not easy enough to use to attract widespread adoption. An exception to this rule is EncryptPad, an easy to use application that lets you encrypt text, photos, or archives with strong encryption using a password, keyfile, or both.

Extra hardware buttons have become a trend with smartphones lately. Often, these are unmodifiable buttons designed to launch a voice assistant. That isn't the case with the BlackBerry KEY2. Making a return from the KEYone is the Convenience Key, which also received an upgrade.

When we are building programs that communicate over a network, how can we keep our data private? The last thing we want is some other lousy hacker sniffing our packets, so how do we stop them? The easy answer: encryption. However, this is a very wide-ranging answer. Today we're going to look specifically at how to encrypt data in Python with dynamically generated encryption keys using what is known as the Diffie-Hellman key exchange.

If the recent "state sponsored" Yahoo hack wasn't enough motivation for users to stop using their services, the latest news about Yahoo should be. Joseph Menn, a reporter at Reuters, just revealed that Yahoo created a custom email wiretap service for the US government.

GIFs are awesome, but GIFing from your keyboard is some next-level stuff, and Apple knows this. That's why they've included a way to find and send GIFs in Messages from the stock iOS 10 keyboard. However, iOS 10 is not out for the public just yet, so if you want to easily send GIFs in your messages, you'll have to settle for a third-party keyboard.

Welcome back, my fledgling hackers! Let's continue to expand our knowledge of digital forensics, to provide you the skills necessary to be a digital forensic analyst or investigator, as well make you a better hacker overall. In your attempts to enter a system or network undetected, it is key to understand what a skilled forensic investigator can learn about you, the alleged hacker.

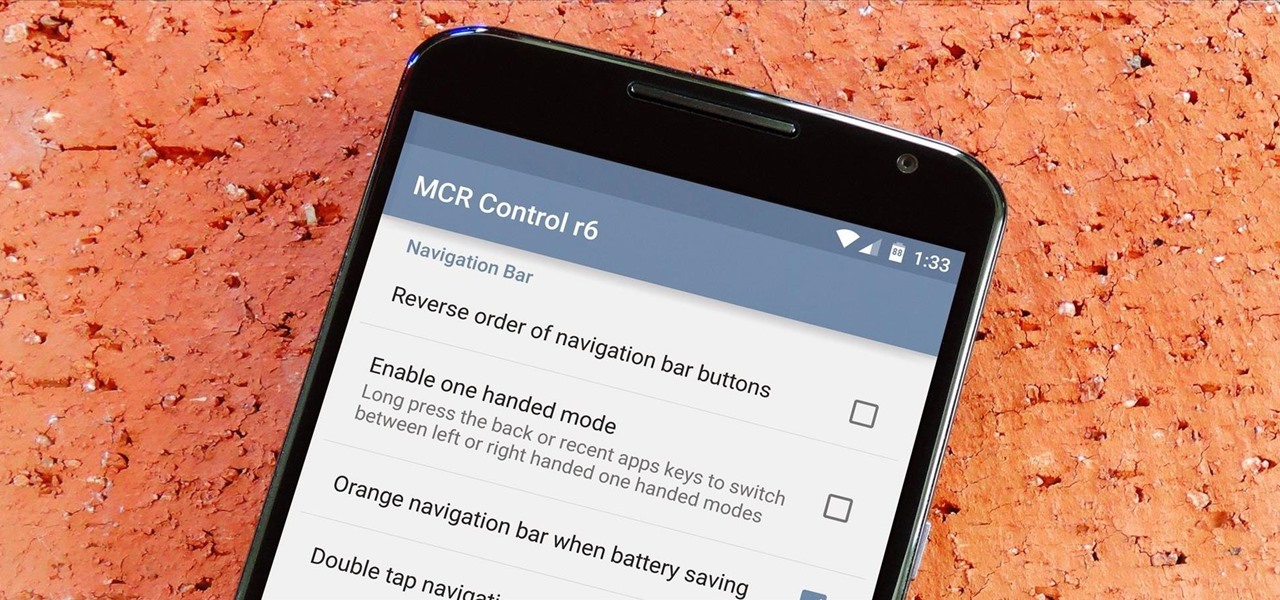
If you've ever flashed a custom ROM on any of your devices, one of your main motivations for doing so was likely the set of neat tweaks and extra options that come with something like CyanogenMod. Another deciding factor was probably the fact that most custom ROMs offer a much cleaner interface than manufacturer skins.

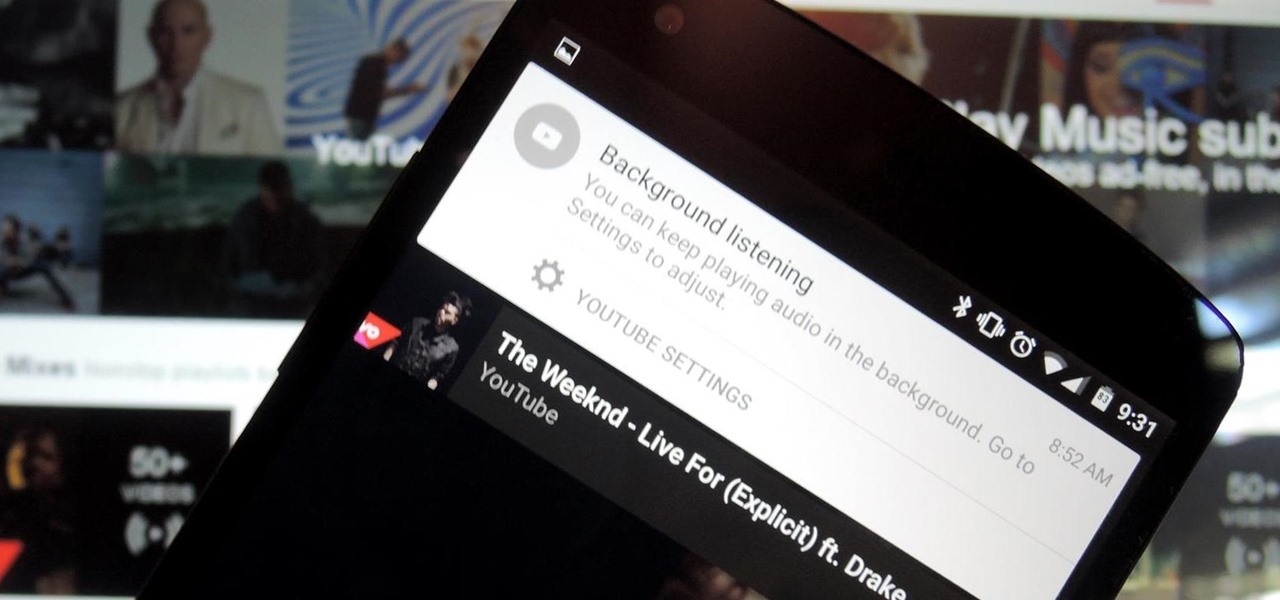
We recently showed you YouTube's new music streaming service, YouTube Music Key, with it's promise of ad-free music complete with background listening and offline play. Well, if you check your YouTube app, there's a good chance that Google flipped on the service for you. Activate the Service

Unlike other Android devices with soft keys, the LG G3 actually comes stocked with a few different styles, as well as the ability to adjust the button layout and combination. But while the customization options are great, the styles you can switch between don't add much flair or personality to your device.

How many times have you heard someone utter the phrase, "Now, let's break into groups"? From classroom discussions to workplace think tanks, gathering into groups to generate ideas is common practice. These forced get-togethers are intended to encourage creativity and unique thought, but they can actually do the opposite. More often than not, group brainstorming is annoying rather than encouraging, and these group sessions can actually be detrimental to your productivity. Getting together har...

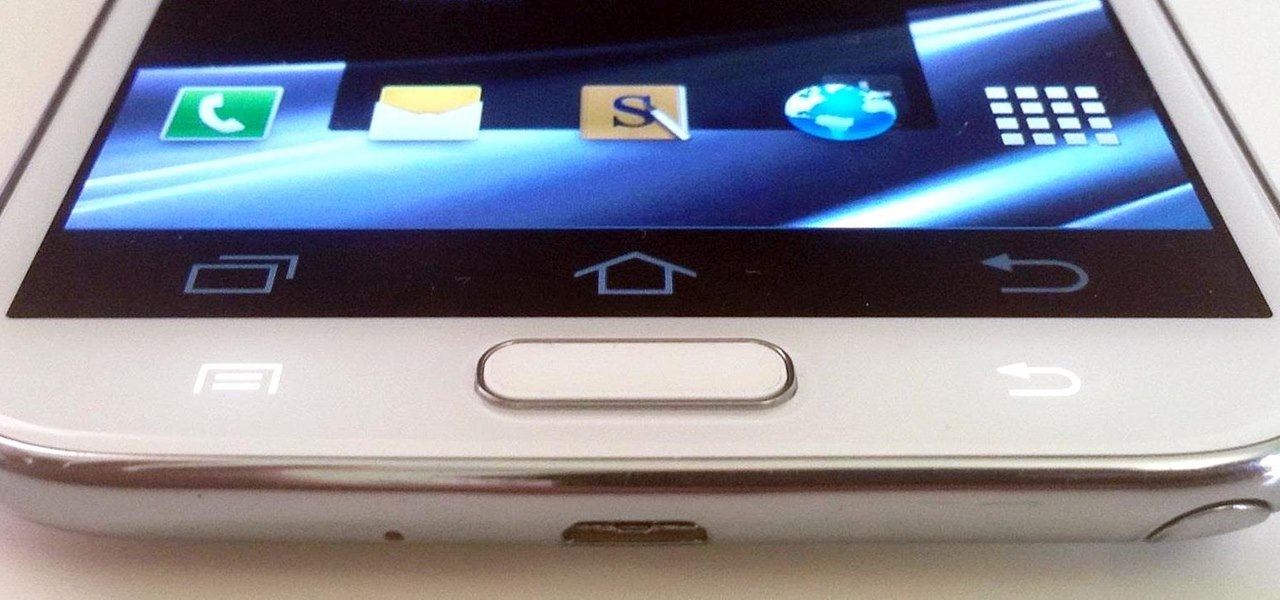
Ever since Android 3.0 Honeycomb, Google has been trying to push phone manufacturers to do away with physical menu buttons. Samsung has been one of the lone holdouts, retaining the menu key up until the Galaxy S5, where they finally replaced it with a "recent apps" multitasking button.

How to make a Lego key holder with note board. Tired of loosing your keys? Well keep them safe and in one place with this fun Lego key holder.

Throughout history, almost every superstition dealing with evil has had something to do with left hands. In the seventeenth century, it was thought that the Devil himself baptised his followers using his left hand. Today, studies show that left-handed people are more likely to be schizophrenic, alcoholic, delinquent, dyslexic, have Crohn's disease and ulcerative colitis, and a slew of other medical problems. To top it all off, left-handed people have an average lifespan that is 9 years shorte...

Opening doors with keys is boring and for the lockpicking illiterate. Inject some mischief into your life by watching this video on how to open a lock and break into a house using everyday objects you have lying around.

Three point lighting is the key to MAKING videos look professional. Tom Skowronski, the associate editor of Videomaker, guides us through the process of three point lighting. Three point lighting involves the use of three types of light to create a professional appearance when video taping. First, a key light is used to provide bright illumination of the subject. Then, a fill light cleans up the dark areas on the face. Lastly, a backlight fills serves to separate the subject from the background.

Do you have coworkers who use the hunt-and-peck method of typing? This trick is guaranteed to drive them completely bonkers.

Everyone remarks upon the hands of the skilled pianist, but even the most dexterous keyboard artist couldn't pull off Schubert without using some fancy footwork.

The key to a successful indoor hydroponic garden is in both irrigation and lighting. This video can't help much with the irrigation, but if you want to decide what the best lighting systems are, this video is for you! There are a wide variety of bulbs and power sources that you can choose from when constructing your own hydroponic grow operation. The key is wattage, and the more wattage you can get out of your bulbs, the better your garden will be.

This tutorial shows you how you can make your own do it yourself green screen out of a bed frame, some hardware (a staple gun is key) and a green blanket (or any large length of appropriately colored green gabric).