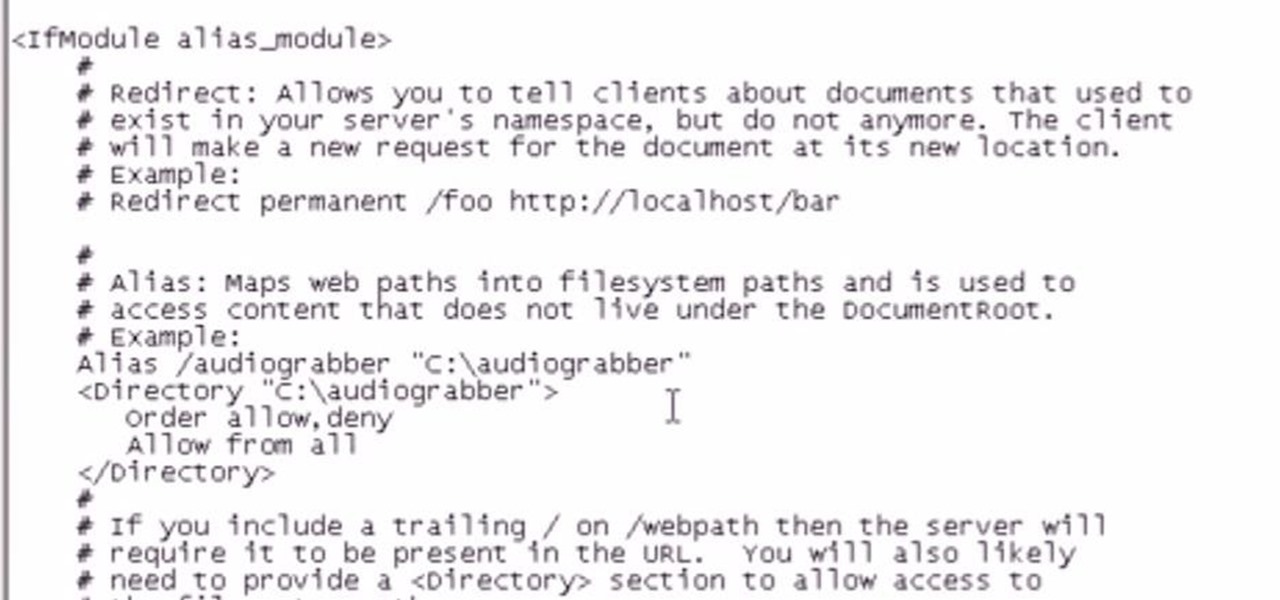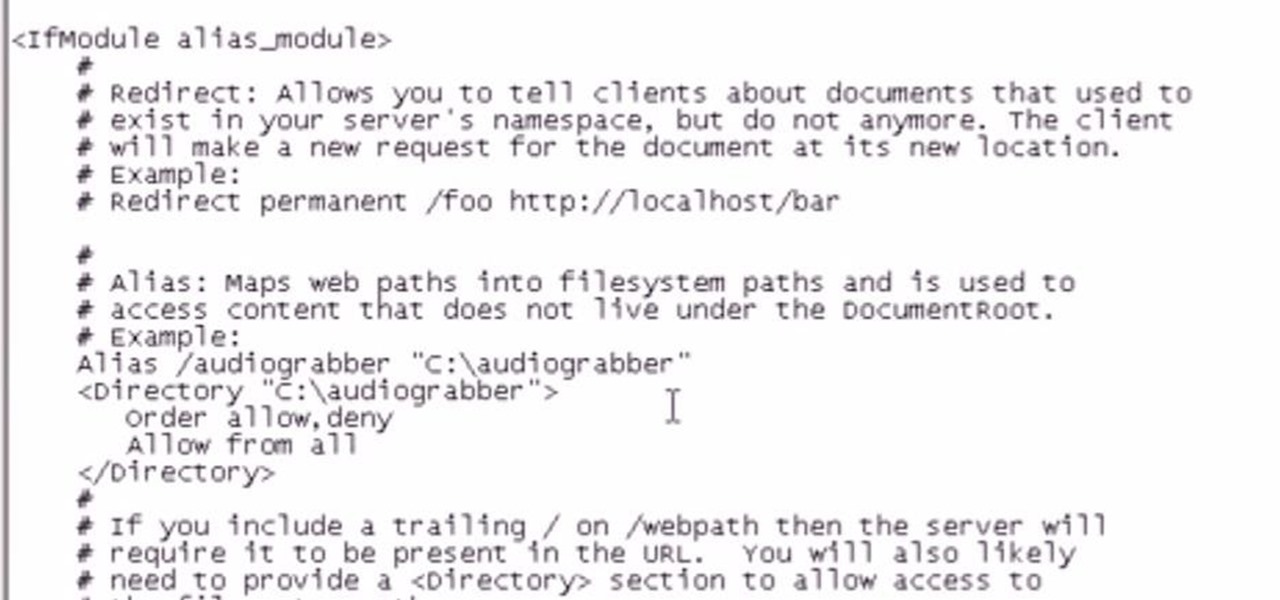
There are several reasons to add an alias to your Apache server. If you want some extra room, add a drive or make the data on an external drive accessible, then setting up an alias will make this possible.
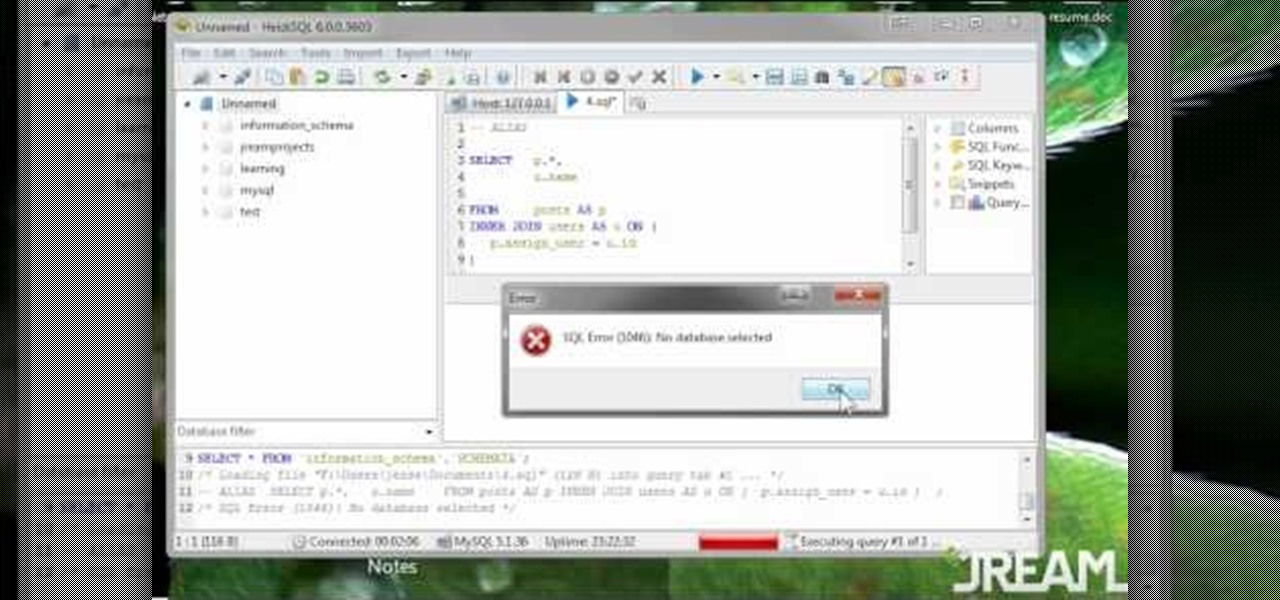
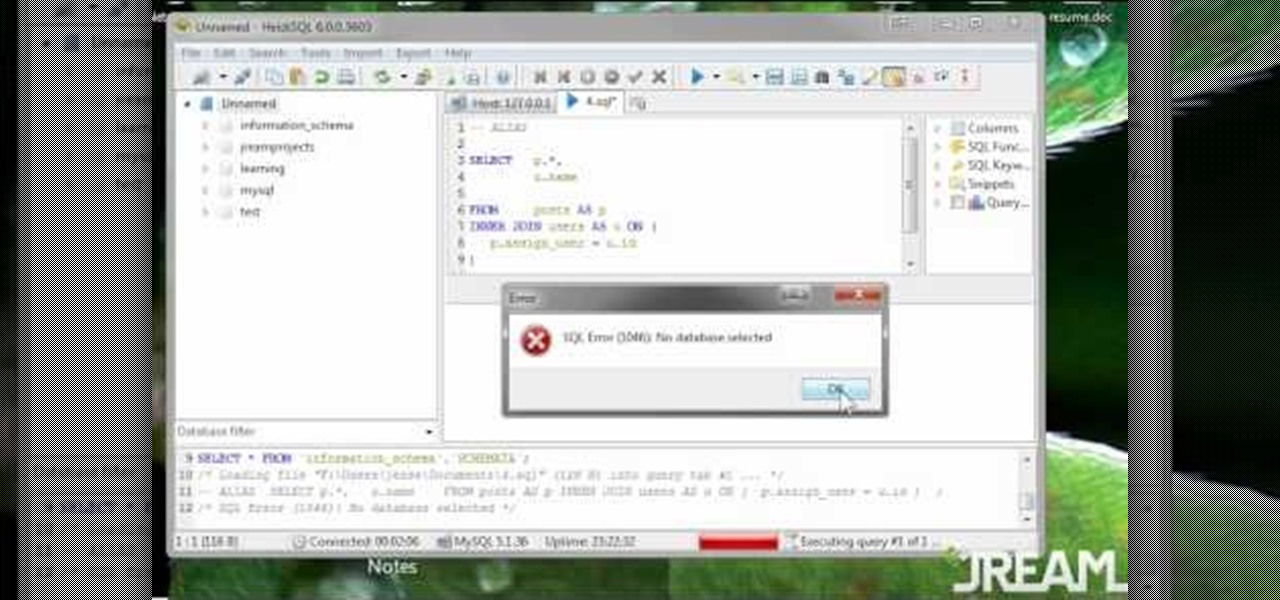
The greatest function of the ALIAS command is as a shortcut. Being able to use this properly will make your MySQL database much easier to use, more functional and streamline all your programming. This tutorial shows you everything you'll need to know about using ALIAS in your database programs.
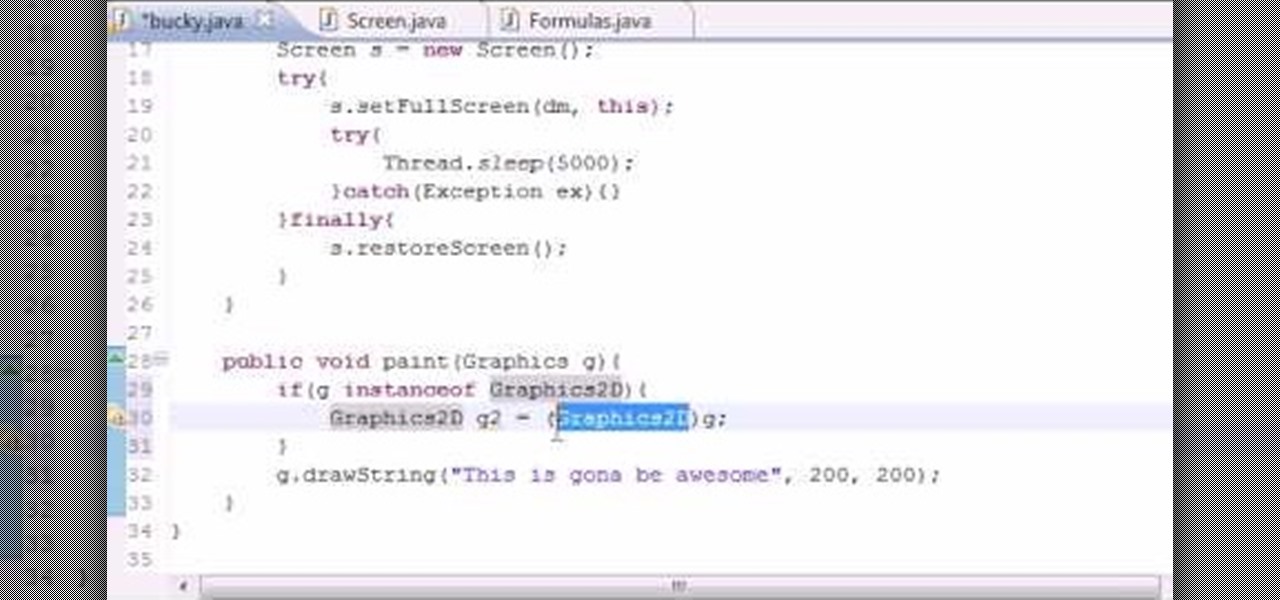
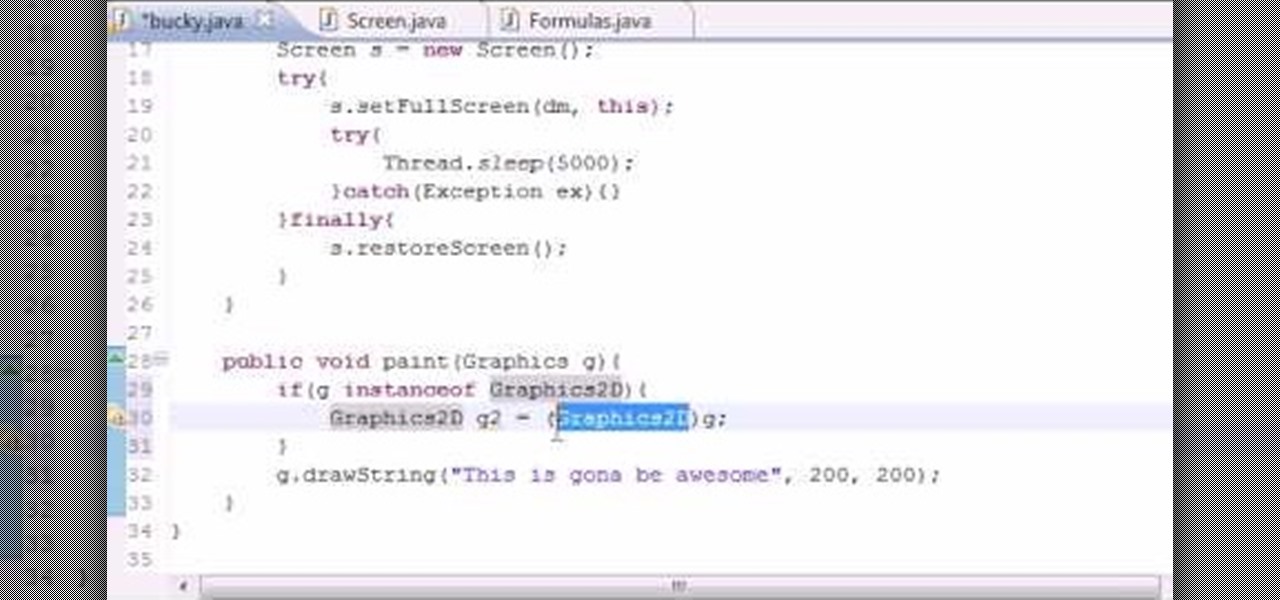
Want to program your own Java games and applications but don't know beans about object-oriented programming? Never you fear. This free video tutorial from TheNewBoston will have you coding your own Java apps in no time flat. Specifically, this lesson discusses how to anti-alias text when writing code in the Java programming language. For more information, including detailed, step-by-step instructions, watch this helpful programmer's guide.

When you drag files or folders on your Mac OS X system from one location to another, you expect them to be moved to the new location and not copied. In this video tutorial, you'll learn two things you can do while dragging these files and folders to change the default behavior. Learn to copy and create file aliases using the option and option buttons with this OS X video tutorial.

I mentioned in one of my earlier articles something about ghost hackers, and very shortly stated a thing or two of what they do.

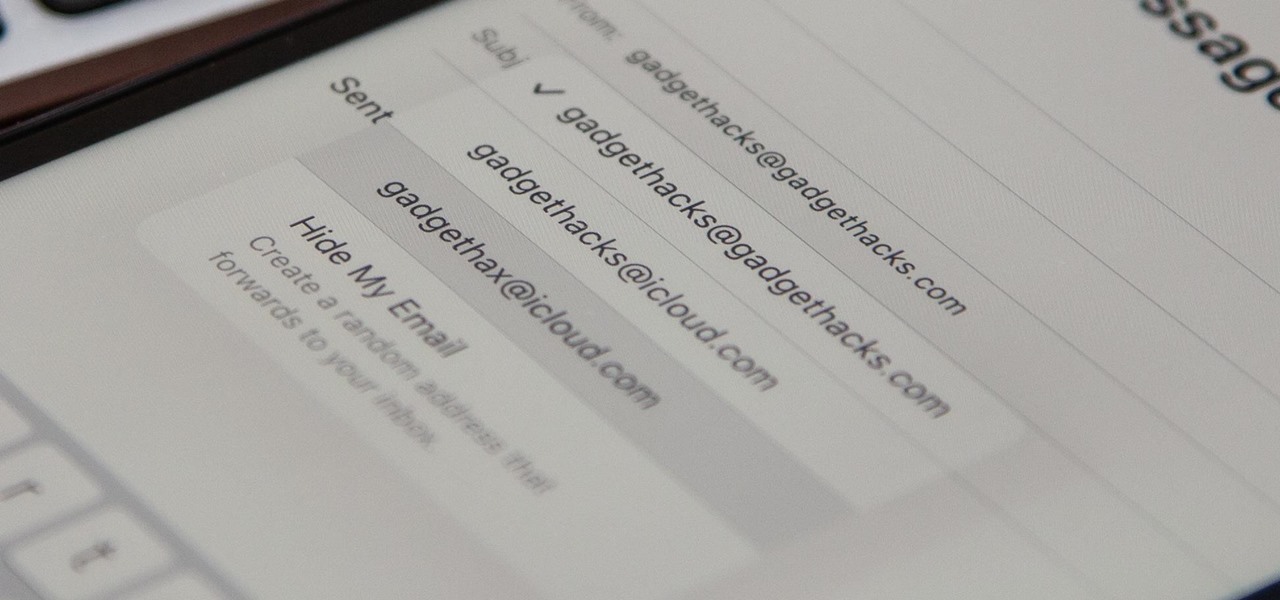
If you use Apple's email services and the "From:" field in your iPhone's Mail app is cluttered with @Mac.com, @Me.com, and @iCloud.com variations of the same address — along with third-party accounts — there's an easy way to declutter things and hide the addresses you don't use anymore.

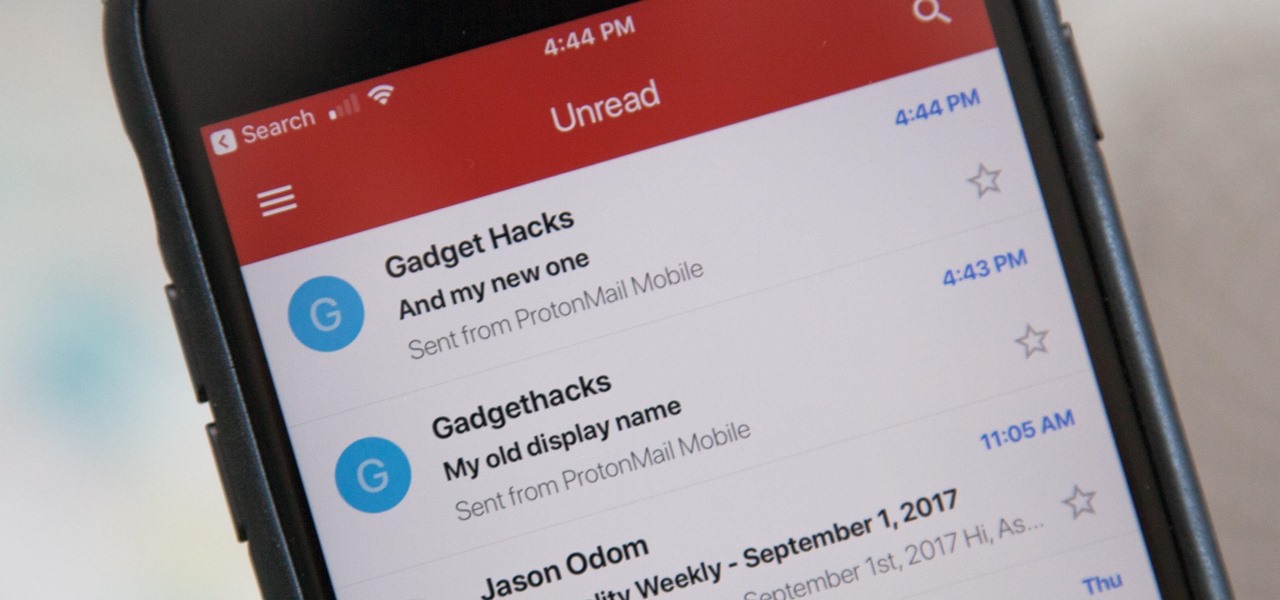
Take better advantage of your Gmail tools -use aliases to organize your mail and forwarding to manage multiple email addresses and locations.

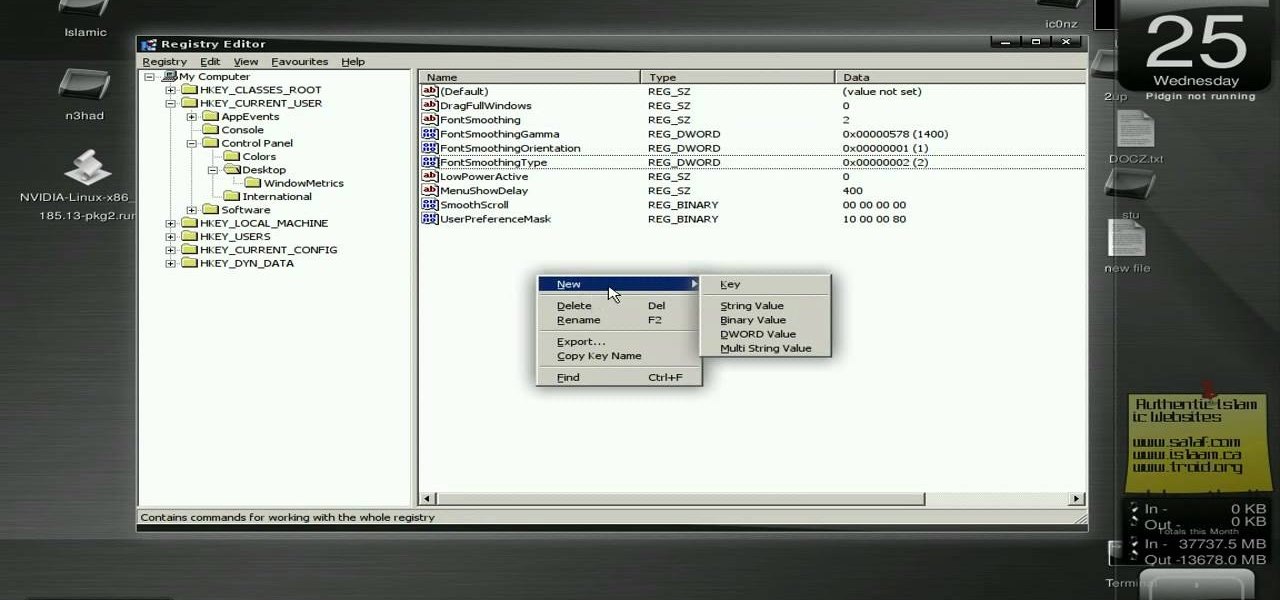
New to Ubuntu Linux? This computer operating system could be a bit tricky for beginners, but fret not, help is here. Check out this video tutorial on how to enable font anti-aliasing on Wine Ubuntu Linux.

Making rounded corners is literally a cornerstone of learning Photoshop. That's because rounded corners are used in many different applications, from harmonizing pictures in a family photo album to create a fun pamphlet for class to setting up an Indie-style vintage picture for your Flikr.

MacOS isn't known as an ideal operating system for hacking without customization, but it includes native tools that allow easy control of the Wi-Fi radio for packet sniffing. Changing channels, scanning for access points, and even capturing packets all can be done from the command line. We'll use aliasing to set some simple commands for easy native packet capture on a macOS system.

Snapchat was created for the sole purpose of removing evidence from your mobile that a photo or video ever existed. That way, snoopers can't find any of these questionable selfies in your photo gallery. Of course, there are plenty of ways around this safeguard, but it's still more private than the standard social networking app.

On your iCloud Mail account, you can easily use subaddressing to create hundreds of new iCloud email addresses to give to companies and other parties, all of which go straight to your primary iCloud email address's inbox. The problem with these types of alternative email addresses is that you can't ever respond to emails with the plus tag intact. But Apple has another alternative for you to start using.

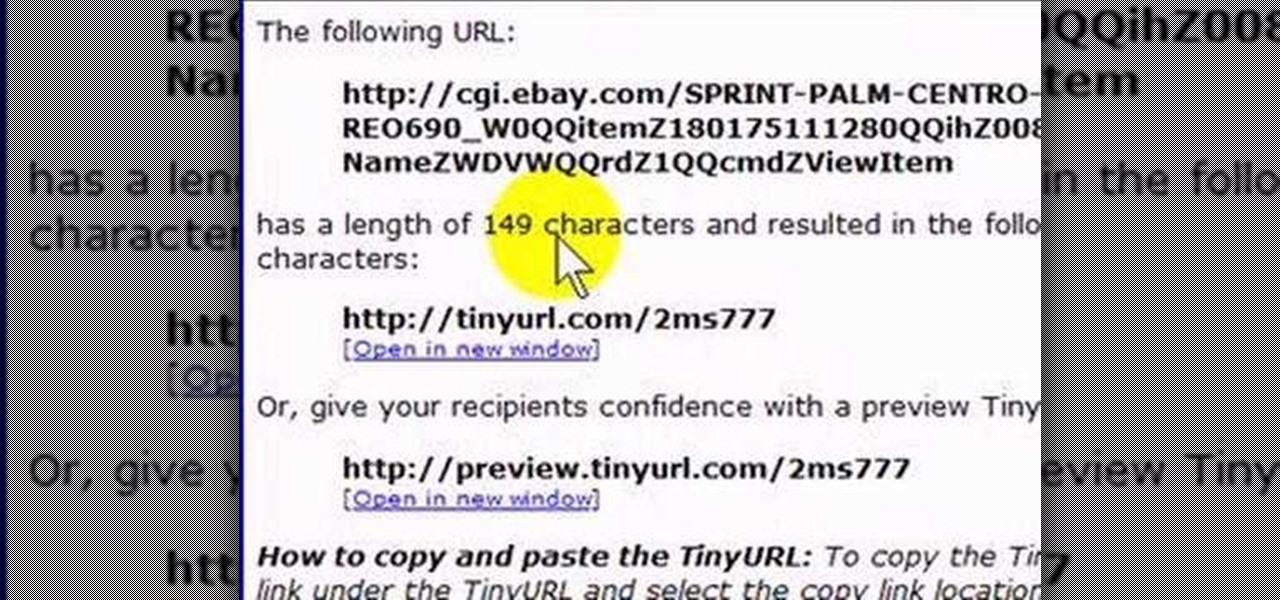
If you like to share websites via email, are a writer who needs to share email in her stories, or just need to make a quick written note of a website address, you need to know how to use web address shorthand. Some URLs can be hundreds of characters long and therefore too tedious to reproduce in writing. To make an easier-to-communicate link, you'll need to use a URL minimizer, like TinyURL. Learn how with this address-minimizing how-to!

One of the most frustrating things on the Internet are sites that make you register just to view content. I'm not talking about paywalls—I mean the sites that make you give them personal information to look at free articles or forum threads. Most people are uncomfortable with this because a lot of these sites either spam you themselves, or sell your information to someone else who will.

This video shows you how to create a new Skype account. Even if you already have one name, you can make another. This is useful for multiple aliases and identities.

With social networking systems, YouTube comments chains, chat rooms, bulletins boards, Twitter updates... It seems as if almost everyone has at one time publicly stated an opinion on the Internet. Nearly half of all prospective employers research job applicants online. Make sure that what you’re posting today doesn’t cost you a dream job tomorrow!

Hi nullbytes! I've been recently reading the whole Linux Basics for the Aspiring Hacker series and felt like it was missing some stuff I know, so I felt like sharing it with anyone who might find it useful too.

Who am I? First let me introduce myself. I am Th3skYf0x, an -well lets call it

Kali Linux, by default, probably doesn't have everything you need to get you through day-to-day penetration testing with ease. With a few tips, tricks, and applications, we can quickly get started using Kali like a professional white hat.

There are tons of situations that require you to give out your phone number, and I think just about everyone has regretted doing so at some point. It can be incredibly convenient to have a secondary or temporary number on hand, so if you don't want to provide your real digits, you can still get the call without revealing your true numbers. And that's where Burner comes in. Burner is a mobile app for iPhone and Android that lets you create alias phone numbers that you can take out of service a...

Yes, that's right: Instagram has a sneaky, inconspicuous, cryptic, hush-hush way to change its iconic, colorful icon on your Android's or iPhone's home screen and anywhere else it shows up throughout iOS. The app really outdid itself too, with 12 alternative icon designs from its classic look to new themes, all located in an impossible-to-find preferences menu — unless you know the trick.

My first ever post on here was 'Keeping your hacking identity secret' and it did very well, and its not something I see here on null byte. So read along.

Thanks to the Freedom of Information and Privacy acts, we’re all entitled to see what the FBI has on us. Learn how to get your hands on your FBI file.

Your display name in ProtonMail is what email recipients will see when they first receive your message in ProtonMail, Gmail, or another email provider. You can choose this name when you first set up your ProtonMail account, but it can also be set up after the fact if you skipped that step.

Jem and the Holograms was one of the hottest cartoon series on TV back in the mid-'80s (though only for a brief time), and was recently given the big screen treatment with the feature film of the same name. While the film bombed at the box office (with good reason), your Halloween costume doesn't have to.

If you're a fan of the Metal Gear video game series, an obvious Halloween costume choice would be Solid Snake, the protagonist of nearly all of the games. However, an even better option would be Big Boss, aka John, Ishmael, Vic Boss, The Man Who Sold the World, and Naked Snake, among many other aliases. He's was once a good man, but better known as the nemesis to Solid Snake. The below costume by YouTube user Erick Zeros showcases Naked Snake in his good era, in Metal Gear Solid 3: Snake Eate...

Welcome back! Sorry for the dry spell, but I've been rather busy setting up some side projects! If you remember back to a few training sessions ago, we covered basic file I/O. This is a very important step in making our scripts applicable in a real life scenario, and today we're going to further these concepts.

Welcome back! In the last training session we covered how to write and execute scripts. But today we'll be getting back to the code!

I rarely receive spam mail, but every now and then I’ll get an email from Cat Fancy Magazine. I’ve never read an issue of Cat Fancy Magazine or been to their website. Actually, I’m allergic to cats. So how did they manage to get my information?

Welcome back, my budding hackers! As you know, I firmly believe that to be a true professional hacker, you need to be proficient in Linux. This is for a number of good reasons.

A group ironically called the "Guardians of Peace" hacked into Sony Pictures' computer systems and released a mountain of internal information such as medical records, leaked scripts, work complaints, and even celebrity aliases.

Shopping online can be as easy as buying cigars in Mexico. You find what you like, ask for the price, and walk away. "My friend! Come back! I give you 10% off. Just for you."

Glitches can be extremely annoying when playing some of your favorite games, but sometimes, only sometimes, there are glitches in the game that give you an unprecedented advantage against the computer or other players online.

Check out this three-part series on how to play Super Smash Bros. Melee (advanced). This is not a beginning tutorial for all you newbie gamers, it's more detailed and advanced for pros, or semi-pros.

Are you still eating MSG? Dr. Gloria Gilbere lists how MSG can still be in our food and what names it can be called on food labels.

Privacy is a growing concern in the tech industry, but Apple has fallen behind many of its peers when it comes to email security. Fortunately, iOS 15 changes that. Your email address is the key to a vast amount of personal information, not to mention a stepping stone into your other online accounts, so it's great to see new features for iPhones that protect email accounts and their contents.

This video is about a particular pool or snooker game shot technique called "Shooting or Going around the Angles." The presenter, with a alias name of 'Forcefollow', first describes a particular 9-ball pool game situation that would require this technique, using a computer generated picture image to show an overhead view of the pool table, with the pool balls in question placed at certain locations within the table and showing the various angle trajectories paths of the desired ball to be str...

Apple has changed how home screen shortcuts work on iOS, which makes one of the most enjoyable customization features even better than before.

With a simple social engineering trick, sudo passwords can be captured in seconds without the target's knowledge. The passwords can then be saved to a file or exfiltrated to another computer on the network.

It might be difficult to admit, but a lot of us are probably guilty of lurking on Instagram profiles, whether it be an ex you've been keeping tabs on or someone cute you literally just met.