For 365 days of the year, our mothers show their love for us by driving us places, cooking us food, doing our laundry, and being our number-one cheerleader. But for one day of the year, we all get up early in the morning and show our love for our favorite women. Often, that means cooking breakfast or making brunch, or running to the store to grab a pre-selected bouquet of flowers.
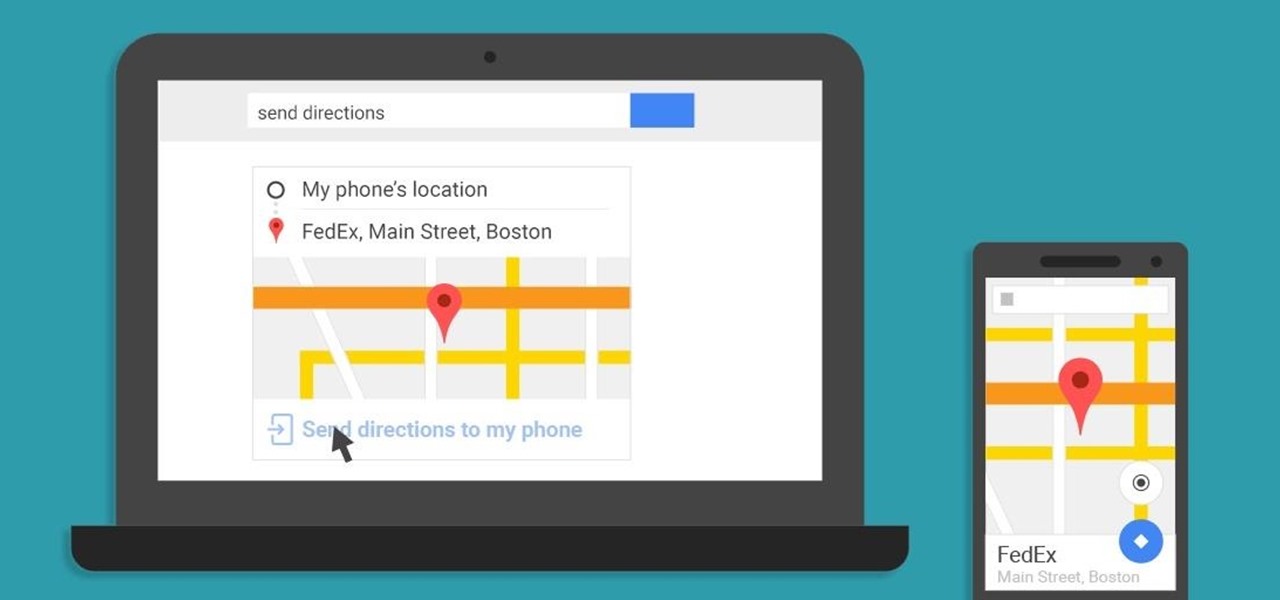
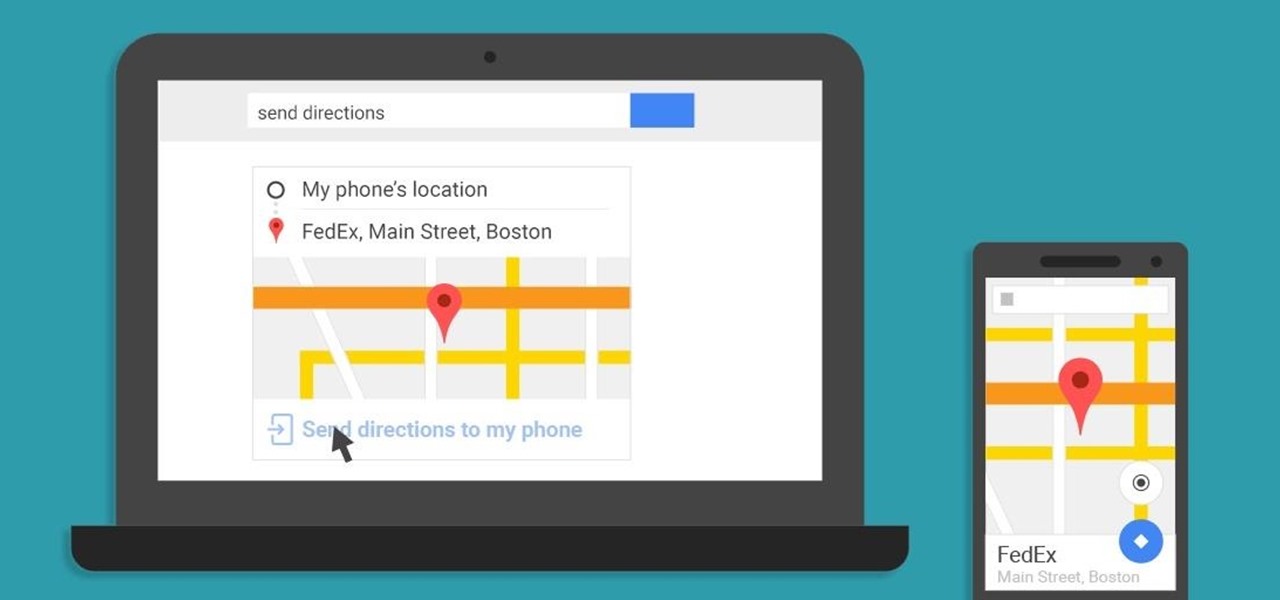
A set of cool new Android-related Google Search functions made their debut this week, which will allow you to locate your phone, send directions to your mobile device, set alarms and reminders, and send notes from any web browser.

Welcome back, my neophyte hackers! In previous tutorials, we learned how to steal system tokens that we could use to access resources, how to use hashdump to pull password hashes from a local system, and how to grab password hashes from a local system and crack them.

What Is IPython? IPython is a richly featured replacement for the standard python interpreter. It offers a wider range of functionality, that the standard

Today I am going to teach the various ways that you can use social engineering to hack a system. For those of you that have followed my past tutorials, you know that social engineering can unlock a world of possibilities. This is because no matter how many firewalls, no matter how many patches there are on a server, the password is kept in the minds of people...and people, are not as smart as computers.

Hello Elite Hackers! Welcome to my 3rd Post, which explains how to hack any account like G-mail, Facebook, etc.

The Nexus 6 is one of the few devices on the market that sports a 1440p "QHD" display. This means that the amount of pixels displayed is higher than almost any other smartphone, which sounds great on the surface, but is not without its drawbacks.

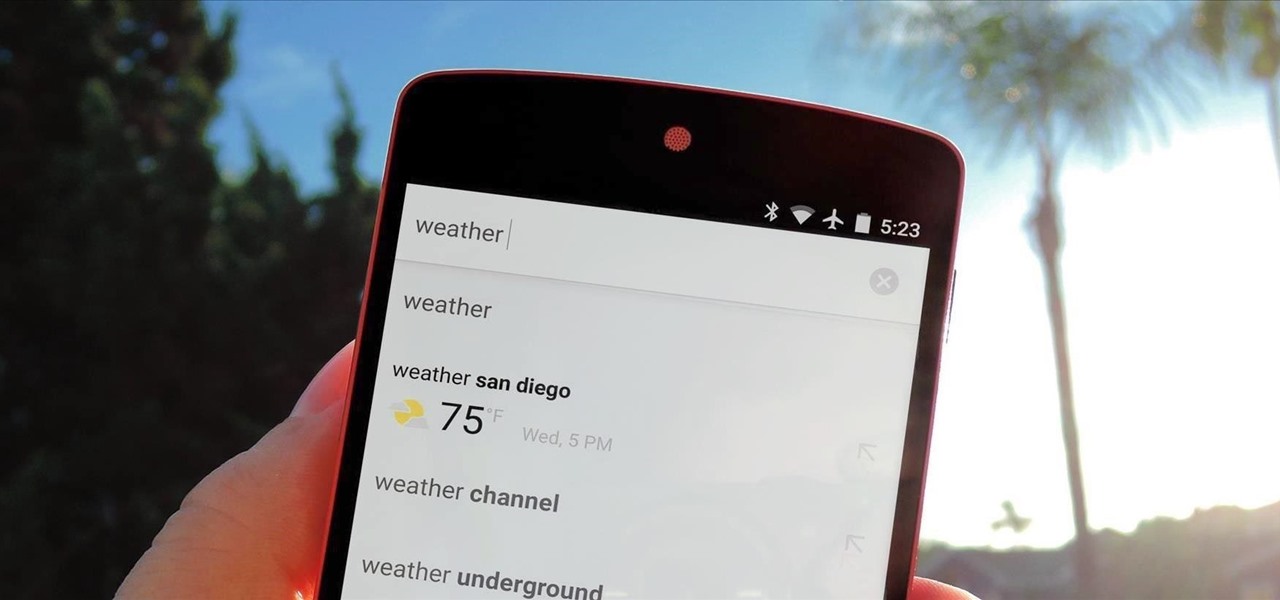
Google continues to be the most commonly-used search engine for a reason. While continuing to stay ahead of the pack with advanced semantic search functions, Google even introduced Knowledge Graph results that offer key information without ever having to click a search result.

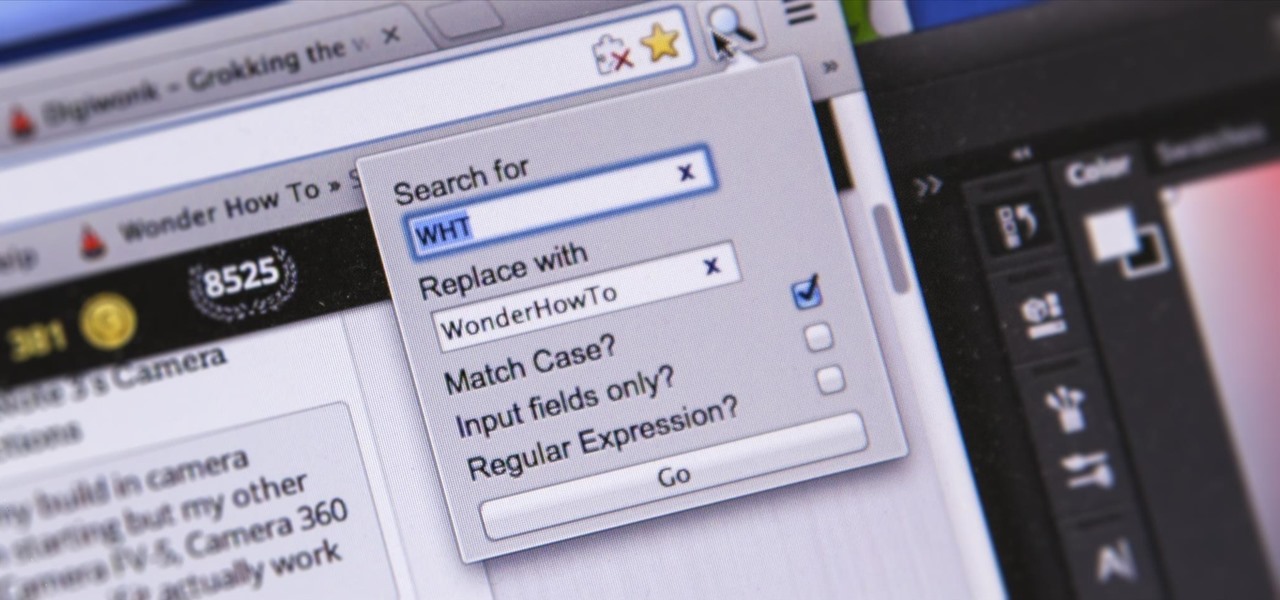
I'm sure you've been there—halfway through typing something out, you realize that one word you've been using more than any other has been misspelled. Perhaps it's a single word, acronym, or line of code that you find yourself typing quite often at work, but this one requires complicated hand gymnastics that you'd simply rather not perform over and over again.

Welcome back, my rookie hackers! I recently began a series on using Metasploit, and my goal with it is to teach you the very basics the incredibly powerful hacking tool has to offer while progressively moving on to the more advanced features.

Certain ingredients that a professional chef might work with in a restaurant-style setting may seem bizarre, dangerous, and even downright scary to a home cook, and for good reason.

Welcome back, my rookie hackers! Most often, the professional hacker is seeking protected information from the target system or network. This might be credit card numbers, personally identifiable information, or intellectual property (formulas, plans, blueprints, designs, etc.). Most of my Null Byte guides have been focused on getting into the system, but this only begs the question—"what do I do when I get there?"

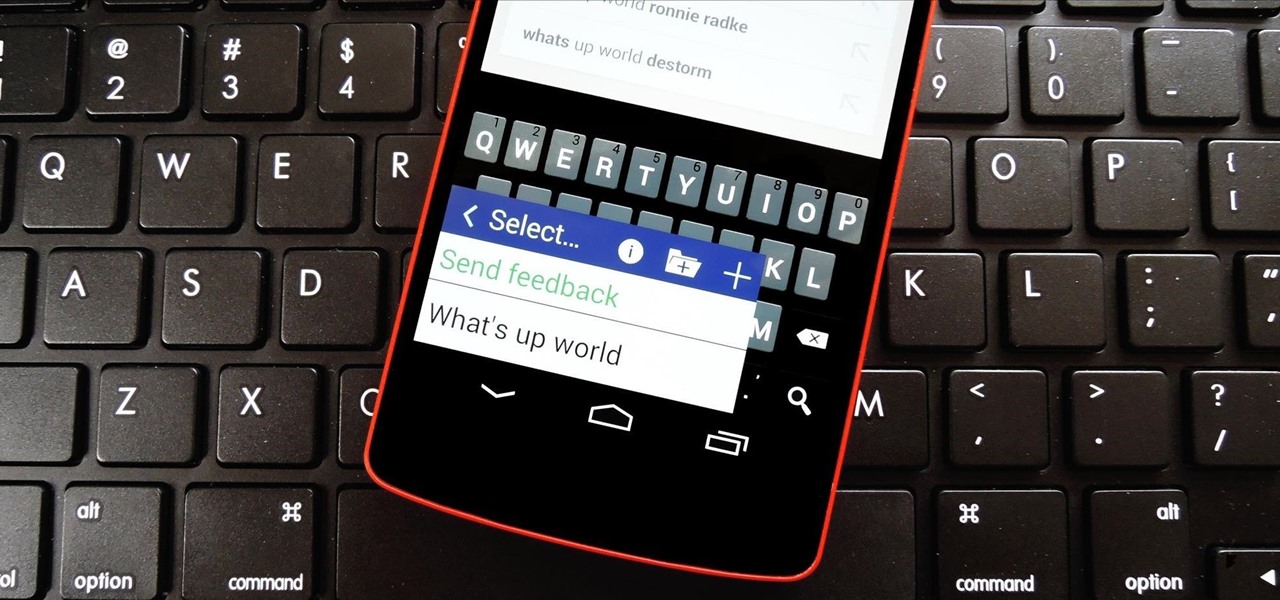
There are a lot of instances where we find ourselves typing virtually the same phrase that we've typed many times before. Whether it's the standard spousal reply of "I'll be home in a few", or a work-related phrase like "I'll have that to you by the end of the day", typing phrases like these can feel very redundant at times.

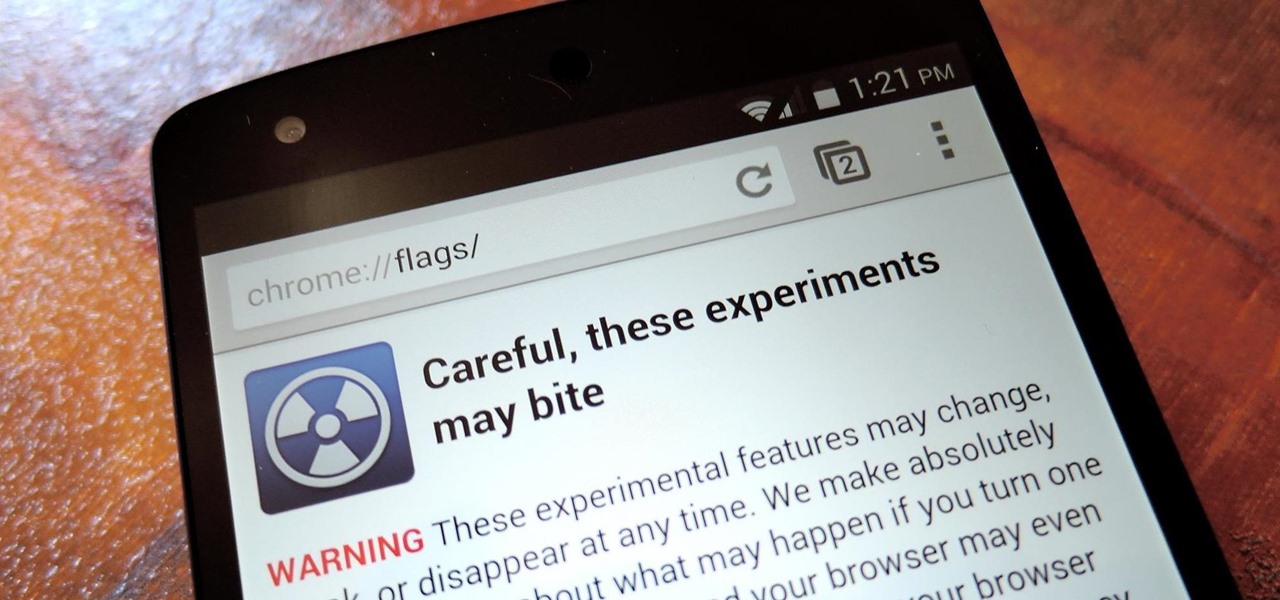
With the release of Jelly Bean, Chrome became the default web browser on Android. The wildly successful desktop browser was now fully entrenched in the world's largest mobile operating system.

The space on your phone is extremely valuable, so getting the most out of your screen real estate can help you out when multitasking or for just making your device feel bigger. One thing that is often overlooked when it comes to saving space on the screen is the keyboard.

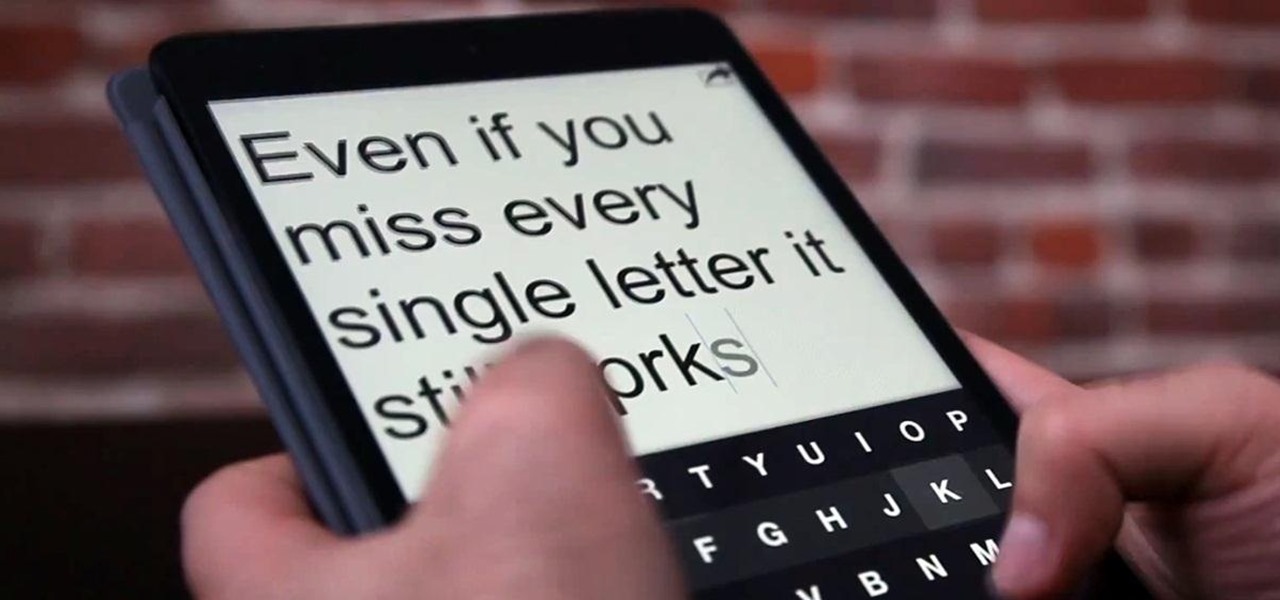
The absence of a physical keyboard is both a gift and a curse. When it was announced in 2007 that the first iPhone would have a touchscreen only, people literally lost their shit. Now, almost 7 years later, you'd be hard-pressed to find a smartphone that still has a physical keyboard.

In my first tutorial on Linux basics, I discussed the importance of hackers using Linux and the structure of the directory system. We also looked briefly at the cd command. In this second Linux guide, I'll spend a bit more time with changing directories, listing directories, creating files and directories, and finally, getting help. Let's open up BackTrack and getting started learning more Linux for the aspiring hacker.

Welcome back, my newbie hackers! We've already saved the world from nuclear annihilation and covered our tracks afterwards, but the world is still threatened by a malicious, megalomaniacal dictator with missiles and nuclear weapons.

Who doesn't hate Auto Correct? There's nothing worse than hitting 'Send' only to realize that your phone betrayed you by changing a word so that your message doesn't even mean the same thing anymore—especially when it's going to someone like your boss or parents.

Welcome back, my greenhorn hackers! Several of you have you have emailed me asking whether it's possible to install a keylogger on a victim’s computer using Metasploit. The answer is a resounding "YES"!

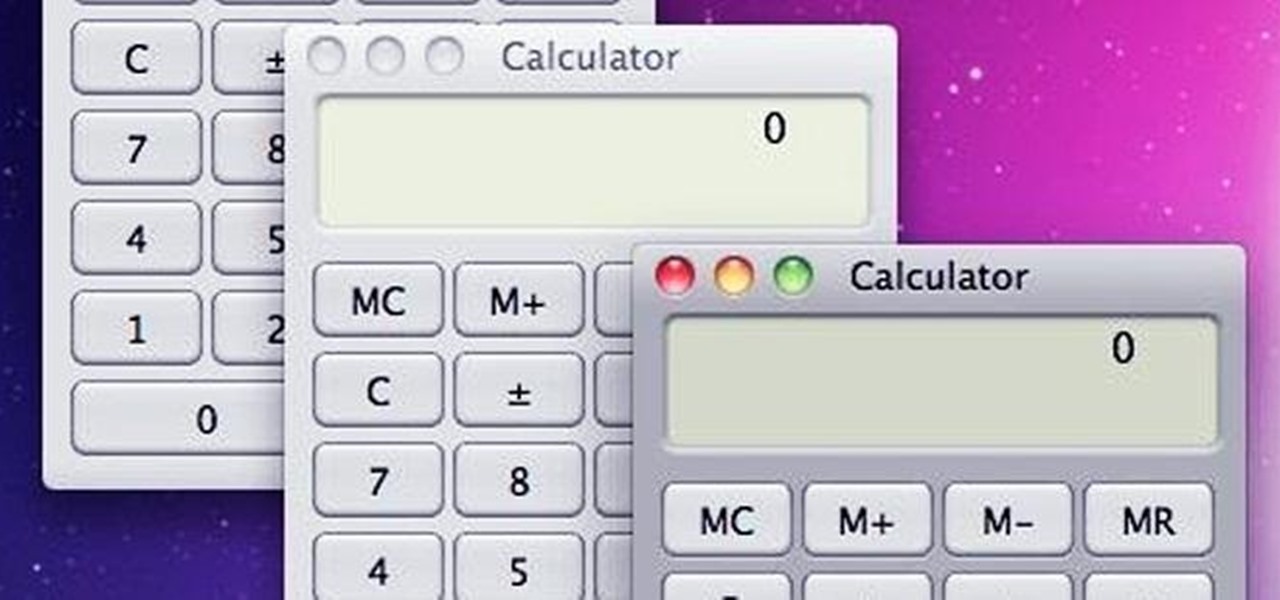
With the use of Terminal, anyone can run multiple instances of the same application on a Mac. When you have multiple windows open in a web browser, the windows are all running under the same Process ID (PID). But, with multiple instances, each has its own unique PID. So why would you want to run multiple instances of the same app? There are several reasons a person may run clones of the same application, but the most popular would be so that the user could multitask. Some applications, like t...

When I left off on our last hack, we had hacked into the ubiquitous Windows Server 2003 server by adding ourselves as a user to that system so that we can return undetected at any time. The problem with this approach is that a sysadmin who is on their toes will note that a new user has been added and will begin to take preventative action.
I've noticed that a few people using the crypto-currency, Bitcoin are having issues importing private keys to their Bitcoin wallet. This is easy to do and doesn't require anything other than your Bitcoin client/daemon (as of ver0.6.0 ) and the command line.

Do-it-yourselfer Kipkay salvaged parts from an old parallel port scanner and made a flexible, super-bright light in this how-to video. The modification is done by extracting the lamp and running it through clear tubing. He mounted the new lamp above his keyboard for night typing. Watch this video tutorial and learn how to turn an old scanner into a keyboard light.

The biggest determent to doing origami, other than time and complexity when you get to harder pieces, is quite simply the origami paper. It doesn't cost much, but like any type of crafting it does require some monetary devotion.

If you recently moved into an apartment with your boyfriend or girlfriend then you know that eating healthy and any type of cooking are generally hard tasks to manage. But it's actually quite simple to prepare healthy meals at home.

Cutting beef for a stir fry is entirely different from cutting a slab of steak to grill. Stir frys are made from a mixture of many bite-sized ingredients, so meat likewise has to come in small chunks.

Card tricks are the best type of tricks. They require little equipment, are easy to understand, and contain nearly limitless potential for trickery. Watch this video to learn how to do a card swipe trick on unsuspecting friends or fellow bar patrons.

This tutorial series shows you how to use Sintra (a type of PVC plastic that bends under heat) to make a piece of Spartan-style leg armor. This focues on making a shin guard, but you can use this method for any piece of armor you want to make.

Not since the days of Royce Gracie have MMA fighters regularly worn a gi during fights, but in jiu jitsu and other types of fighting they definitely still do. Watch this video to learn how to do a gi collar choke from guard, with female BJJ practicioner Hillary Williams demonstrating on Joanne of MMA Girls.

Fishing is a great way of saving you money on having to pay for over priced pre-cleaned fish at the grocery store, it's also a way to relax and enjoy nature. If you're planning on heading on down to your local stream to get some fish, take these tips into consideration. In this video you will get some tips on what sort of physical characteristics of the stream are and also what sort of fish to expect in what types of waters.

Cooking eggs is one of the simplest and most basic kitchen skills you can possess. But what works for one egg may not work for another. In fact, different types of eggs sometimes require different preparation methods.

The Craft Robo is a useful tool for papercrafters, card makers and scrapbookers, which will allow you to cut letters out of any type of paper and using any sort of font you have in your library. Add a professional look to your next paper craft project!

Wallpaper is a big investment. It's one of the most visible pars of your home decor, and you're probably going to be stuck looking at whatever you get for a long time. This video will give you some tips of choosing the right sort of wallpaper (vinyl, paper, prepasted, etc.) and how much you should pay for decent quality product.

New to the world of DSLR video and need a hand distinguishing between different lens types? This video offers some pointers for would-be shooters. For details, and to get started using different lenses with your own Canon or Nikon DSLR, watch this video guide.

This video tutorial will show you how to create a fixed loop knot using a piece of amsteel, and the locked brummel splice. This type of knot comes in very useful, especially when you're camping. You've got to be prepared for anything and everything! Just follow along, and you'll be making fixed loops like nobody's business.

Want to know how to set a custom wallpaper or ringtone on a Droid 2? Whether you're a proud owner of the Moto Droid 2 Google Android smartphone or are merely considering picking one up, you're sure to benefit from this video tutorial, which also takes a look at the Swype typing feature. For more information, including detailed, step-by-step instructions, take a look.

In this clip, you'll learn how to create grungy, typographic posters in Adobe Photoshop. Whether you're new to Adobe's popular raster graphics editing software or a seasoned professional just looking to better acquaint yourself with the program and its various features and filters, you're sure to be well served by this video tutorial. For more information, including detailed, step-by-step instructions, watch this free video guide.

When you've mastered the single crochet and have gotten a hang of the double crochet, it's time to really step up your knitting game and start the triple crochet, a more difficult but rewarding type of stitch that creates a very tightly woven fabric.

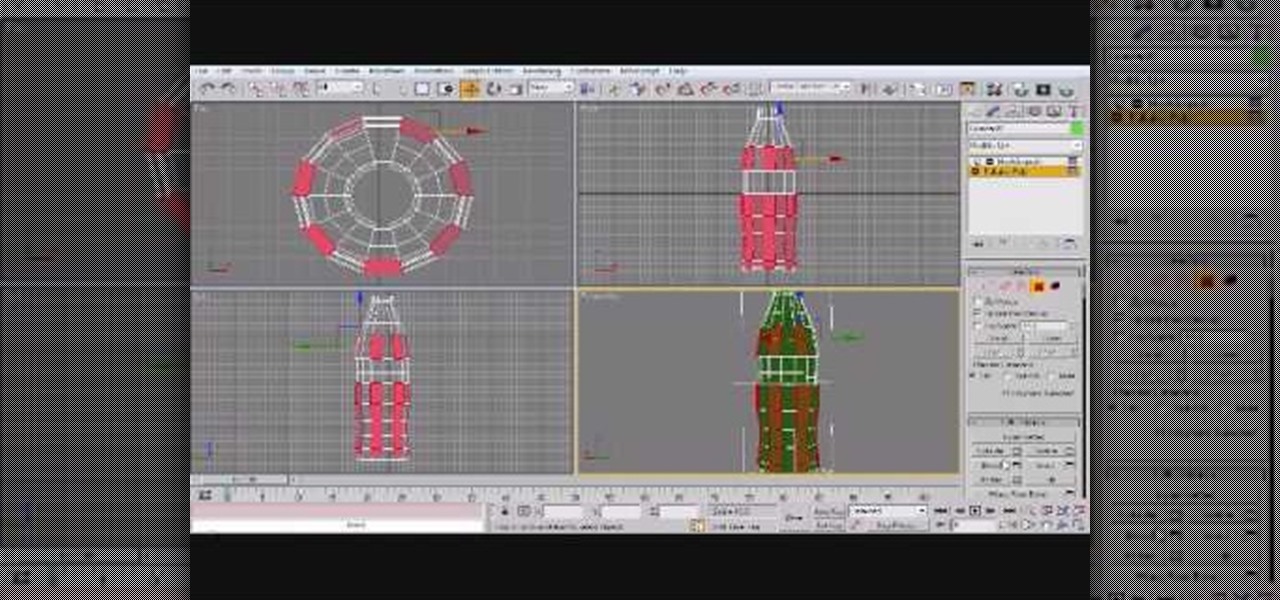
In this 3ds Max software tutorial, you'll learn how to model a glass-type bottle from scratch. Specifically, this deals with creating a Coke bottle from scratch. It will not show you how to texture the bottle, just how to build it. Learn the basic techniques for modeling the Coke bottle.