Welcome back, my greenhorn hackers! Before we attempt to exploit any target, it is wise to do proper reconnaissance. Without doing reconnaissance, you will likely be wasting your time and energy as well as risking your freedom. In previous guides, I have demonstrated multiple ways to perform reconnaissance including passive recon with Netcraft, active recon with Nmap or hping3, recon by exploiting DNS or SNMP, and many others.

Samsung's Galaxy Note 4 is a beautiful device worthy of all the critical acclaim it has received thus far. But aside from the S Pen features, most of the Note's user interface has a great deal of overlap with the Galaxy S5 that we all know and love.

App-locking apps have been around for a while, but none have had quite the panache of developer Fazil Kunhamed's latest offering, Oops! AppLock. While others use a PIN or password to restrict access to apps that are installed on Android, AppLock uses a stealthy volume button combo.

It's pretty logical for your MacBook to sleep when you close its lid, but under certain circumstances, you may not necessarily want this feature to kick in.

With all of the different websites we use in our day-to-day lives, keeping track of our numerous login credentials can start to become a hassle. This has created a market for password managers that aim to centralize these account credentials and generally streamline the process of logging into our favorite sites.

Tired of playing old-school Game Boy Advance, Game Boy Color, Nintendo, and Nintendo DS games on your iPhone? We've got another retro video game system for you to add to your arsenal of emulators—Super Nintendo.

Having someone send you flowers will almost always lift your spirits. Wilting, dying flowers, on the other hand, aren't so great to look at and smell even worse. While there are time-honored tricks to keep flowers alive longer (change the water regularly, put a penny in the bottom of the vase, and cut stems diagonally are three that come to mind), it turns out that a few items in your kitchen are pretty useful at making sure those blooms stay perky.

Google Keyboard, which comes pre-installed on Nexus devices (and is available for all others from the Play Store), is one of the most functional keyboards currently available for Android. With features like gesture-based typing, next-word prediction, and even text expansion macros, it's a very capable form of text input.

Your phone's volume panel is one part of the user interface that usually goes unnoticed to themers and developers. With themes capable of changing the look and feel of the fingerprint scanner, keyboard, and other system apps, this central aspect of the UI seems to get lost in the shuffle.

There are many different reasons that you might want to revert your Samsung Galaxy S5 back to stock. The main one would probably be that you need to return your device to the manufacturer for warranty purposes. And if you've used root to modify system-level files and components, you'll need to undo those changes before you send the phone back.

I don't know of a pain greater than of the one felt after cracking the screen of your phone. After I managed to crack my screen, rendered unusable, I immediately began to panic as to how I was going to recover all of the photos, videos, and documents stored on my device. After a few hours of searching, I came upon a thread by Mohamad Sabra that showed exactly how to alleviate my problem.

It's really amazing how much you can do with root access on an Android device. From various themes to porting exclusive funtionality from other devices, the power of Superuser privileges is truly awesome.

My phablet has incredible battery life, but that doesn't mean I wouldn't like it to last even longer. Unlike the Samsung Galaxy S5, the Note 3 does not come equipped with Ultra Power Saving Mode, which can keep the phone running for another 24 hours with only 10% power remaining.

The Galaxy S5 comes with an awesome feature for those times when you're running low on battery life with no charger in sight. Ultra Power-Saving Mode allows you to cut back on non-vital services and convert your phone's display into a juice-saving grayscale mode to greatly extend that last bit of charge.

Biting into a perfectly ripened piece of fruit is enough to convince you to give up baked goods and plant your own garden. The combination of flavor, juice, and sweetness in a ripe mango, apple, plum, or berry is the stuff of life itself.

There are tons of good reasons that you might want to use Android on your desktop. Perhaps your favorite game is only available on Android, or maybe you use a messaging service that doesn't have a Windows companion app.

You have a cool picture that you want to show someone, but when you hand your phone over, they start swiping through all of your photos. Surely, you've encountered this scenario before. I definitely have.

Most times when you take your smartphone out of your bag, pocket, or purse, you probably know exactly what you're going to do with it. Make a call, send a text, take a selfie, browse viral videos on YouTube, or one of the other many things a smartphone can do nowadays.

Back in the day when computers relied on CRT monitors, having a static image displayed for too long actually resulted in the image being burned into the screen. For this reason, screensavers were developed, which display animated images in constant motion to prevent burning in when you stepped away from your computer.

As Matias Duarte and the team over at Google's Android Design department ready their wares, they've given us a preview version of the upcoming "L" release of Android to try out.

Developing an imperceptible lie is difficult, especially when you're lying right to someone's face. Thanks to smartphones, getting people to trust you is now easier than ever. You can craft a lie in seconds and hit send, all without ever seeing their untrusting faces.

In early-2014, Facebook had the brilliant idea of auto-playing all of those annoying videos in your news feed that you never wanted to see in the first place. Fortunately, they realized their mistake and have provided a way to disable auto-play, which means you can now get rid of some of those plugin-blocking browser settings you have enabled.

One thing I absolutely cannot stand is lag when I'm gaming. Every time I'm about to beat my killstreak record on Call of Duty, my internet connection drops and I'm a goner. It never fails. This usually happens because someone else on my Wi-Fi is streaming a movie or downloading a huge file.

Although lacking in megapixels, the HTC One M8's camera can be considered a top-tier, flagship-level shooter. With the Duo Camera and UltraPixel technology behind it, it can make even the most inexperienced photographer snap pictures like a pro. There seems to be little missing for the average user, but for the more seasoned photographers, some of the standard settings may seem a bit too dumbed down.

It's a modern day nightmare to accidentally reveal too much information on Facebook. I've inadvertently told the world my location more times than I can laugh off, and my friends haven't fared too well either. Just take a look at the requested app permissions next time you're about to click install and you'll quickly realize how much that app can reveal about you.

With Geohot's Towelroot allowing us to root our Nexus devices in under a minute without ever leaving Android, many of you are probably enjoying all of the Gadget Hacks that root access has unlocked.

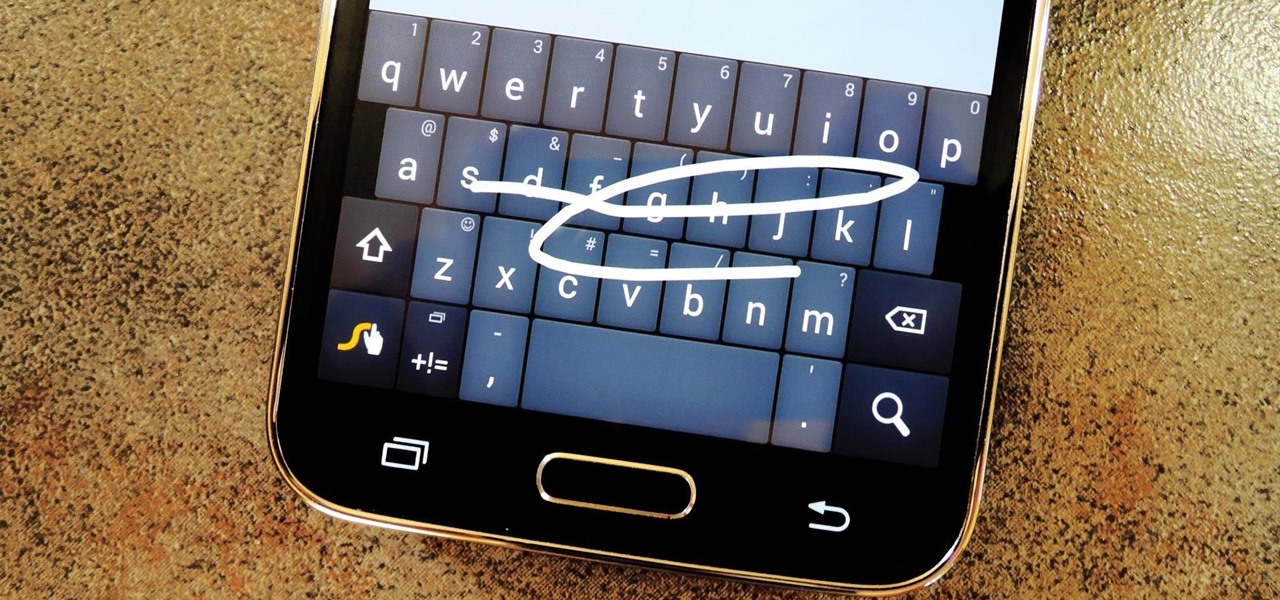
Most variants of the Galaxy S5 come with the gesture-based Swype keyboard preinstalled. If you're into gesture typing, you probably already switched to this input method from the default Samsung keyboard (whose gesture service is nice, but it's no Swype).

Let's be real, browser histories are virtually useless. Trying to find something you passed up a week ago is like, pardon the cliché, finding a needle in a haystack.

Last year, The New York Times wrote that certain restaurants in Manhattan and Brooklyn banned patrons from taking photos of their meals. That means no flash photography, no standing on chairs for a better angle, not even a quick pic for your Instagram followers before the first bite. Little do these restaurants know, this ban can actually make their customers' food taste worse, so to speak.

With a root bounty of over $18,000 up for the taking, developers were highly motivated to get the AT&T and Verizon Wireless variants of the Samsung Galaxy S5 rooted. Legendary hacker George Hotz, aka Geohot, has won the race and can now step up to claim his prize.

A friend of mine has a crazy amount of Reddit karma and gold, and yesterday he let me in on his secret. This person, who will remain unnamed for obvious reasons, created a Python script called Reddit Karma Crawler that finds rising posts before they get too popular.

Remember the feeling you had the moment you removed your shiny new Nexus device from its packaging and booted it up for the first time? You swiped through the app drawer at lightning speed and thought to yourself, "This is the last Android phone I will ever need, they just aren't going to get any better than this."

Koushik Dutta, the developer behind the Android app AllCast, has made the leap over to the realm of personal computers with his latest offering.

When we look back on it, 2014 may be remembered as the Summer of Android Wear. With two new flagship smartwatches due out soon, Google's been readying its mobile OS for the wearables sector.

Multitasking has traditionally been one of Android's strengths. As the first mobile operating system to introduce true multi-process management, it even took things a step further after version 4.0 by dedicating a button to your recently-used apps.

Welcome back, my greenhorn hackers! Lately, much of the discussion here on Null Byte has revolved around evading detection and not getting caught hacking. Several of you have written me asking for a series on evading detection and forensics, and while I began a series 5 months ago on just that, we have changed hacking platforms from BackTrack to Kali, which has a much more highly developed forensic toolset.

Google's new camera app has a highly innovative and unique feature dubbed Lens Blur, and the most interesting thing about it is not necessarily what it does, so much as how it does it.

Downgrading your iPhone from iOS 8 beta back to iOS 7.1.1 is a really simple process, and a very necessary one if you're experiencing frozen screens and apps that either unexpectedly quit or don't even work at all.

Facebook rolled out a new feature that lets your friends ask you about your current relationship status. This is great feature if you use Facebook for finding hookups, but if you use it mostly to connect with family and friends, a bunch of questions about your dating status can get annoying real quick.

Normally, when you open applications on your Samsung Galaxy device, you do so from one of three places—your home screen, the app drawer, or from the list of recently used apps—but it never seems fast enough when it comes to opening your favorite and/or most-used apps.