You might be sitting there thinking that I'm crazy, but the truth is you're only partially right. You can get free text messaging for life, all for a cheap, one-time fee. But, how can that be possible? An exploit in AT&T's prepaid GoPhones is the culprit behind this sweet, oh-so rare opportunity for exploitation. The exploit grants a lifetime of free texting, assuming that the company stays afloat from now until the end of time.

I have to say, the Xbox 360 controller is the best controller ever created. When I first held it back in 2005, I swore that the dudes working at Microsoft came over and took a molding of my hands because of how great it felt. The thing felt like it was born there.

The biggest struggle with flashing DVD drives on Xbox 360s has been the price tag of the probe to extract keys on some drives. The probe and kit is required to extract the DVD key, which is needed to perform a drive repair, flash, or backup of any kind. Who wants to pay big bucks for the "pro" kit and then get added to a huge waiting list behind a million other people looking to buy the same product? We can hack the same thing together at home!

Null Byte is looking for moderators! In today's Null Byte, we're hacking Netflix. As most of you know, Netflix is a subscription service that streams movies and TV shows to your devices over the internet. A common stance amongst my Xbox Live friends is that Netflix isn't worth the cost. The instant movies predominantly consist of old titles, and new movies aren't added often enough.

Here's another Null Byte on hacking our Skyrim game saves. Some of the rarer items in Skyrim are really fun to play with. However, seeing as they are rare, you will probably not see all of the best weapons in the game. Null Byte doesn't take too kindly to games that don't give us the rarest items when we please. Let's beat this game into submission by hacking our game save files via hex editing.

With a lot of Null Byters playing around with Linux because of its excessive use in the hacking world, some of you are bound to run into some trouble with the installation at some point or another. If you make a mistake, or you're intimidated by the wonky-looking installation screen, you may want to just stick with Windows. However, you may notice it can be hard to go back once you've crossed a certain point in the installation. Your Windows installation may be broken or unbootable.

Ever since kernel 2.6.xx in Linux, a lot of the internet kernel modules for wireless interfaces ended up becoming broken when trying to use monitor mode. What happens commonly (to myself included) is a forced channel that your card sits on. No good! For users of airodump and the aircrack-ng software suite, the software has become unusable.

Many users of the virtualization software VirtualBox may have noticed that the USB system has been pretty buggy for quite a long time. I've had my USB randomly duck out on me way too many times to count. This can really be difficult to deal with when you require access to the devices and files from the host system.

Let's face it, CDs and DVDs are a thing of the past. We no longer use them as a storage medium because they are slow, prone to failure in burning, and non-reusable. The future is flash memory. Flash memory is cheap, fast, and efficient. Eventually, flash drives might even replace discs as the preferred prerecorded selling format for movies.

Here's yet another one of those pesky multi-step time sink achievements, but the reward is great. To get the 'Genius' achievement in Batman: Arkham City, you have to rescue all five hostages The Riddler has taken. It should be noted though that you'll need a certain amount of Riddler trophies to activate the hostage rescue missions.

Welcome to Part 3 in my series on protecting your computer from prying eyes (Part 1, Part 2). In today's segment, we will be going over drive encryption using the TrueCrypt program on Windows OS. Drive encryption is a technique that masks your data with a cryptographic function. The encryption header stores the password that you have entered for the archive, which allows the data to be reversed and read from. Encrypted data is safe from anyone who wants to read it, other than people with the ...

Encryped traffic and tunneling is a must when away from home to keep you and your information safe. SSH tunnels can be slow, and are heavily encrypted. VPNs are an all port solution, and proxies are just not what we need in most cases. Then, there is Tor.

Everyone has deleted a file or folder on accident before. Sometimes people even delete stuff on purpose, only to find out that they needed the files after all. If you're experiencing one of these mishaps, don't worry, file recovery is possible in most cases!

OpenVPN is the open-source VPN (Virtual Private Network) client, used over the PPTP (Point to Point Tunneling Protocol). It allows you to connect to a remote network over a secure, encrypted connection and mask your IP addresses over all ports. Since there is only one "hop," the network speeds are barely effected and are far more secure.

Without Japan, video games would not be very fun. Atari's early work was important, but Japanese developers, publishers, and hardware makers were responsible for almost every major advance in video games for the first 25 years of their mainstream existence. In recent years, it has often been said that they have become less relevant than Western developers. In the indie games movement— (our area of greatest interest here at Indie Games Ichiban)—Japan does not have anywhere near the presence th...

What do you do when you desperately need to put a parking garage into the bottom floor of your Victorian apartment building, but the city's Department of Planning says "No". The simple and expensive answer: Create an elaborate secret garage door. If you own a pretty building, it is well within the jurisdiction of the Landmark Commission to inform you that even though you own the piece of property, you cannot remodel it any way you want. Seems un-American. But in San Francisco, specifically th...

Some update notes that you should take notice to are:Celestian Furniture Yes you read that correctly! Celestian Furniture has come to the Spiral, as well as recipes for furniture from our newest underwater world! Keyboard Shortcuts

Progression, isn't it great? It used to be that video games only rewarded you with game scores. The satisfaction was always at the end, and all that mattered was getting there.

We're set to see the actual debut of Google Daydream on October 4, and it'll hopefully serve as a significant step up from Cardboard—their current virtual reality smartphone platform. If you want to get an early taste, you can set up a development kit—you just need two phones to do it.

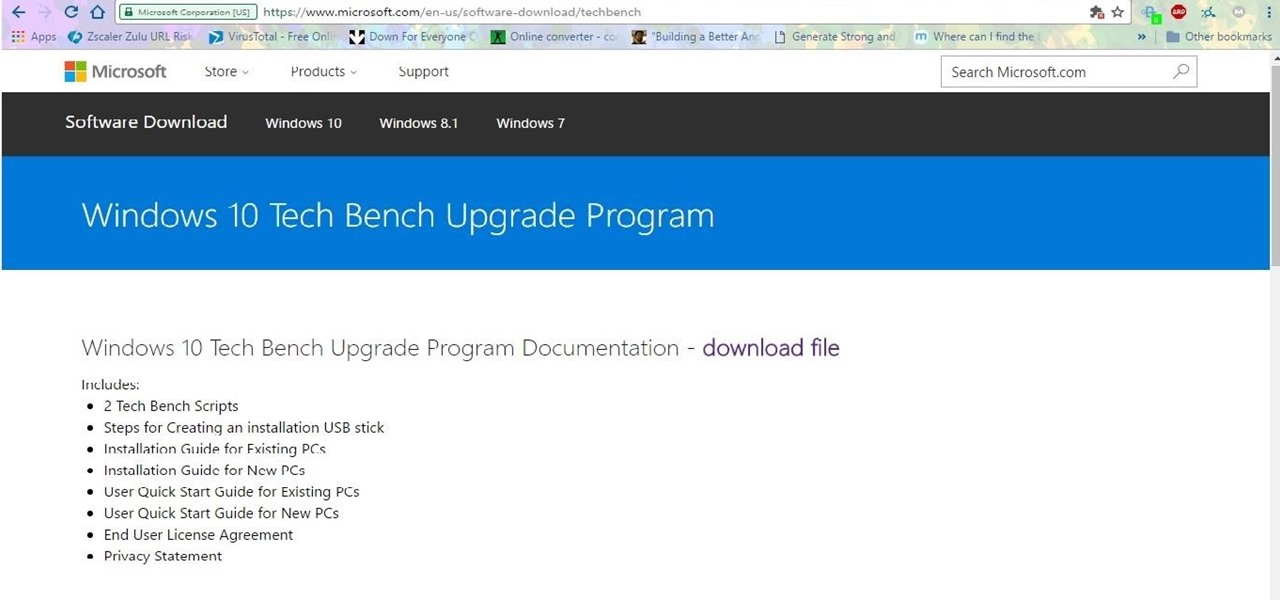
If you want to have windows .iso files for various purpose like you want to have windows 7 in virtualbox, then you need an .iso file. There are many methods of creating an .iso from installed windows. But what if microsoft provided all of them( I mean 7,8 &10) free of cost. The only requirement is that you own a product key for the respective Windows edition (and that's also is not a painful task to get).

The latest Android N preview build was released today, April 13th, and included Emoji Unicode 9.0 support, among other things. The highlight is definitely the emojis, and the new designs are intended to look more realistic than the older, blobbier emojis. The update also allows for skin tone variations and adds new emojis like the face palm, selfie, and the juggler, to name just a few. Get These Emojis Right Now

Hello everyone. As many of you know, we've successfully launched the Null Byte Suite for our wonderful community. In addition to the prepackaged tools, there is a dedicated GitHub repository where tools submitted by the community will be pushed to for distribution in the suite. There have only been a couple submissions, and out of them, only one fit the requirements. So, out of anticipation, we've added it to the suite!

Welcome everyone Today i will show you a simple but very useful way to stop your ip leaks . In order to stay anonymous on the web you HAVE to do this.

Take a minute and think about how many times a day you press the home key on your iPhone . . . a lot, right? It is quite literally the most important button on your device. If the home key stops working, you won't be able to multitask or back out of apps to go to your home screen, so preserving its life should be priority, otherwise you're stuck using one of these tips for fixing your home button. Luckily, for 5S users, you can add a tweak that will utilize your touch ID sensor, instead of ha...

Christmas is almost over— all of the presents are unwrapped, all of the prime ribs have been eaten, the whole family's drunk off eggnog— and soon it will be time to forget about Christmas until next year.

Watch this "Grease On Your Hands" video tutorial from the Washington Post to see how to change the engine oil in your car properly.

Call Your State's Nurse Aide Registries for School Inquiries

If you're on a tight budget for food, whether you're in college, or someone just starting out living on their own, you're probably low on money and sick of ramen noodles. Don't get me wrong, ramen can be tasty and filling, and there is almost nothing cheaper.

Today I will show you how to create a simple keylogger in Visual C# Sharp, which will start up hidden from view, and record anything the user types on the keybord, then save it into a text file. Great if you share a PC and want to track what someone else is writing.

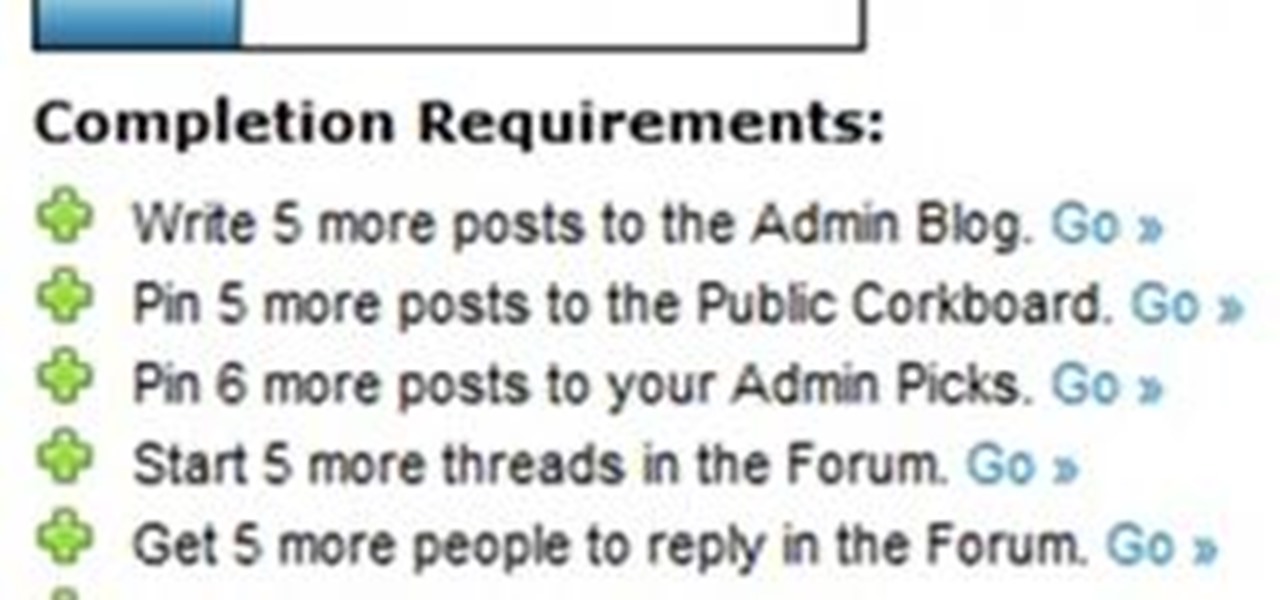
We're officially seeking Null Byters on a weekly basis who would enjoy taking their time to educate the community. Contributors will write tutorials, which will be featured on the Null Byte blog, as well as the front page of WonderHowTo (if up to par, of course). This is a job meant for anyone with the will to share knowledge. There is no need to be intimidated if you fear you lack the writing skills. I will edit your drafts if necessary and get them looking top-notch! You can write tutorials...

XSS stands for cross-site scripting, which is a form of web-based exploitation that uses client-side vulnerabilities in a web page to execute malicious JavaScript codes. JavaScript is referred to as "cross-site" because it usually involves an external website containing the malicious code. That code is most commonly used to steal cookies with a website that the attacker created and hosted on another server. The cookies can then be used to escalate privileges and gain root access to someone's ...

Bingo! No, this isn't the game where balls fly around in machines and players dab their cards with daubers. In a game of Scrabble, bingo refers to the bonus a player receives when emptying their rack in one turn, which gets them an extra 50 points on top of whatever their play was. Even if you had two blanks on your rack and didn't utilize any premium squares on the board, you'd still have an impressive 56-point turn (at least) by using all 7 of your letters.

This Null Byte is a doozey.

One of the coolest things about Twitter is the fact that you can get direct access to some of your favorite celebrities, and have one-on-one conversations with them in less than 140 characters. With Google+, you can have the same advantage, but you don't need to feel constricted by the 140 character limit. Although Google+ has been weeding out fake accounts, they do not currently have a system for celebrities to verify whether their accounts are legitimate or not.

+Randall Munroe, the man behind the web's most popular web comic, XKCD, has always had a knack for getting to the heart of the larger social issues on the web. During the 1st 48 hours after Google+ started letting non-Googlers in, one of the most shared posts within its private walls was his latest comic about Google+:

There is no fan experience in professional sports quite like watching an NBA game live. Partly, this can be attributed to the combination of fluid teamwork and jaw-dropping athleticism the players exude in the form of size, speed, jumping ability, grace, and strength. What truly differentiates the NBA from the spectators' perspective, though, is the figurative nakedness of the players. While the NFL buries its athletes beneath pads and masks, the NBA presents its talent in shorts and a tank top.

Dual booting Ubuntu 10.10 Maverick Meerkat and Windows 7 is fairly easy. If you don't believe me, just read on!
Tips If you are taking a relatively uncomplicated flight to post, it may be to your advantage to take your pet along as excess baggage. Ask the travel agent to provide you with a cost comparison of excess baggage versus air freight shipment.(Remember also to save your receipts for shipment as a legitimate "moving expense" for the IRS.)

Let's face it, the world we live in is far from the fairy-tale land we want it to be, where violence doesn't exist and weapons are not needed. Our foremost goal in life out there in the scary world is simply to survive. And if we need a few tools to accomplish this, we should use them, right?