One lump or two? That was the age-old question with sugar cubes, which used to be a staple of any tea salon or dignified household this side of Downton Abbey. These days sugar isn't really used in cubes much except in bars and restaurants, and that's a shame. Cubes are a lot less messy than granulated sugar, and you can measure the exact amount you put in your drink no matter what.

Hops have always been known as the driving force behind beer, but now they're starting to grow their own culinary wings. Slowly but surely, this bizarre and bitter plant is showing up on more and more menus across the country as it catches on as a trendy and up-and-coming ingredient. What Are Hops?

Are you a lawyer who's married to a computer programmer? Chances are you might not have even dated if you first met online.

Cooking rice, pasta, and other grains in water is so boring. There is a much better way to guarantee they will have your mouth chewing something seriously tasty: cook them in something that isn't water. Alternative liquids such as stock, milk, juice, or even tea will give bland dishes a fresh new flavor boost. If you're not sure how your dishes might taste, never fear: we tested them out. Before getting started, be sure to read this article first so that you know why it's important to rinse y...

Like most people who cook in a small kitchen, I'm very wary of adding anything to my drawers and cabinets unless I'm sure it's going to be essential to my cooking arsenal or that it can be used in multiple ways.

Having someone send you flowers will almost always lift your spirits. Wilting, dying flowers, on the other hand, aren't so great to look at and smell even worse. While there are time-honored tricks to keep flowers alive longer (change the water regularly, put a penny in the bottom of the vase, and cut stems diagonally are three that come to mind), it turns out that a few items in your kitchen are pretty useful at making sure those blooms stay perky.

There are several reasons why restaurant food tastes so good. One is that the cooks know how to make reductions, which involves cooking down large amounts of liquid until it becomes a pool of thick, glossy sauce. While this technique isn't hard to learn, it can be time-consuming.

Coffee is a topic that everyone has a strong opinion about, especially when it comes to brewing the perfect cup. Even if you buy the best beans and grind them yourself, chances are you're skipping one necessary step to make sure your coffee tastes the best it can: cleaning your coffeemaker the right way.

In February of this year, the Higher Court of Berlin ruled that Facebook must follow strict German data protection laws, which Facebook's terms of services and privacy policies circumvent.

We all know that it's important to drink water regularly throughout the day. After all, it has so many benefits, including flushing toxins out of the body and maintaining kidney health and good bowel movements. Turns out that's only part of the story. While being properly hydrated is key to maintaining overall health, it's also a big component of maintaining and even increasing cognitive ability. Plus, drinking enough water regularly can help you lose weight, if you know when to drink it and ...

There is very little in this world that tastes as good as a glass of fresh-pressed juice. The flavors in fruit and vegetables are more clean and immediate on your palate, while the chlorophyll and nutrients seem to zip right into your bloodstream. A really great glass of fresh juice makes you feel more alive and the pasteurized versions on supermarket shelves just can't compare. However, as much as I love a glass of fresh juice, if I had to do it all over again, I wouldn't buy a juicer. The o...

You've probably seen someone in your family truss the turkey on Thanksgiving before roasting it, even if you don't recognize the word. To truss a bird or roast just means to wrap it up as compactly as possible before placing it in the oven, and it's usually done by tying it with string. Trussing a bird is a tradition that's been around for a long time, and a lot of home cooks do it religiously even if they don't know why. It's a highly debated topic with fierce supporters on both sides, but f...

You know that feeling when your cell phone gets stolen and you figure it is pretty much lost forever. You could've used one of the millions of device managers and trackers, but ya didn't. And the Good Samaritan is not coming to your rescue.

While the legality of secretly recording phone calls varies in each country, sometimes it's useful to have audio documentation of conversations you have on your Samsung Galaxy Note 2.

As we all know, our attention spans are much shorter now that we're accustomed to getting information and news in tiny snippets via text messages, tweets, instagrams, and other constant updates.

If you weren't aware, all music purchased online through iTunes, Amazon, and other digital audio providers have information embedded that can be used to identify the buyer and transaction of the digital music file. This may seem like something you should be disclosed about in their terms of use, but it's not.

We've all had to write an essay or research paper at some point, and undoubtedly the hardest part about it is always the citation, right? If you ask me, it's a huge pain in the arse. Even more so if you're gathering your facts from a huge variety of sources.

For the most part, nobody makes money off of Facebook. Sure, some people make a living by updating pages for businesses and celebrities, but hardly anyone gets a dime from the site itself.

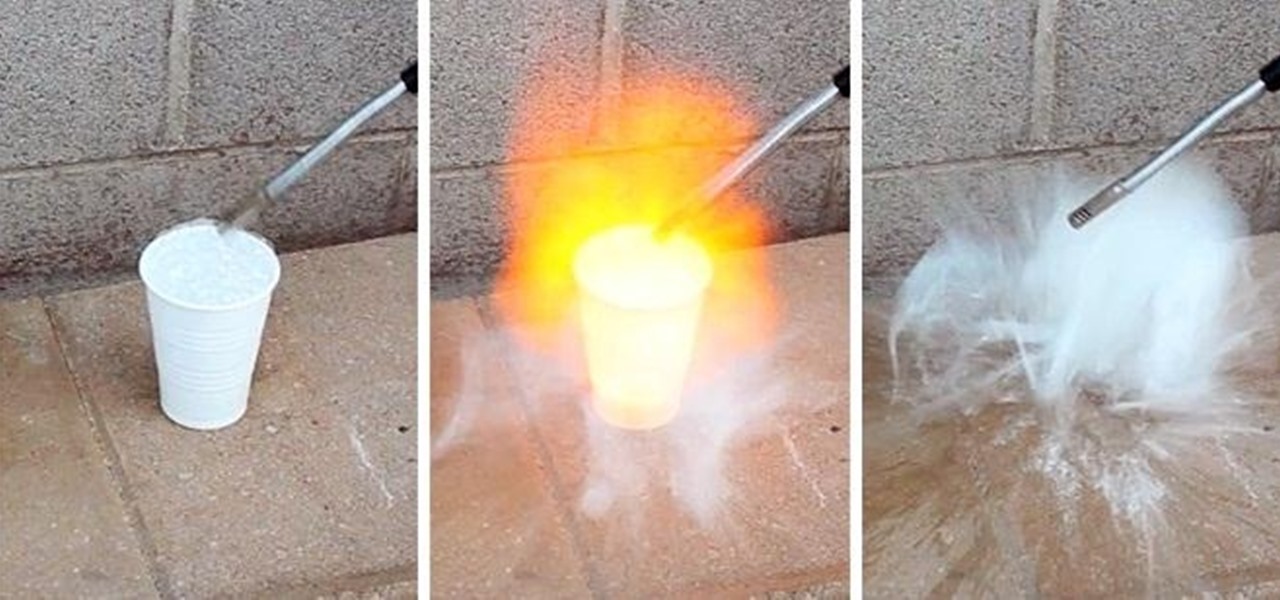
Here's a technique I used to whip up a batch of super cheap and easy to make smoke flares! WARNING: Ignition of an incendiary or explosive material may not be legal in your area, so check local laws before attempting. Use of this video content is at your own risk.

Maybe not water per-se, but with this simple technique you can turn one of the most abundant materials on earth into a highly explosive gas.

In college, I enjoyed eating, sleeping and making my roommate's life a living hell. My most satisfying prank involved 500 red cups stapled together, filled with water, and strewn across his bedroom floor. He was not happy. To clean up, he had to unstaple each cup, carry it to the bathroom, and dump the water. He was furious, but I was okay with sacrificing our friendship in exchange for a fantastic story that I'll probably tell my grandkids one day. If you're not as cruel as me, there are oth...

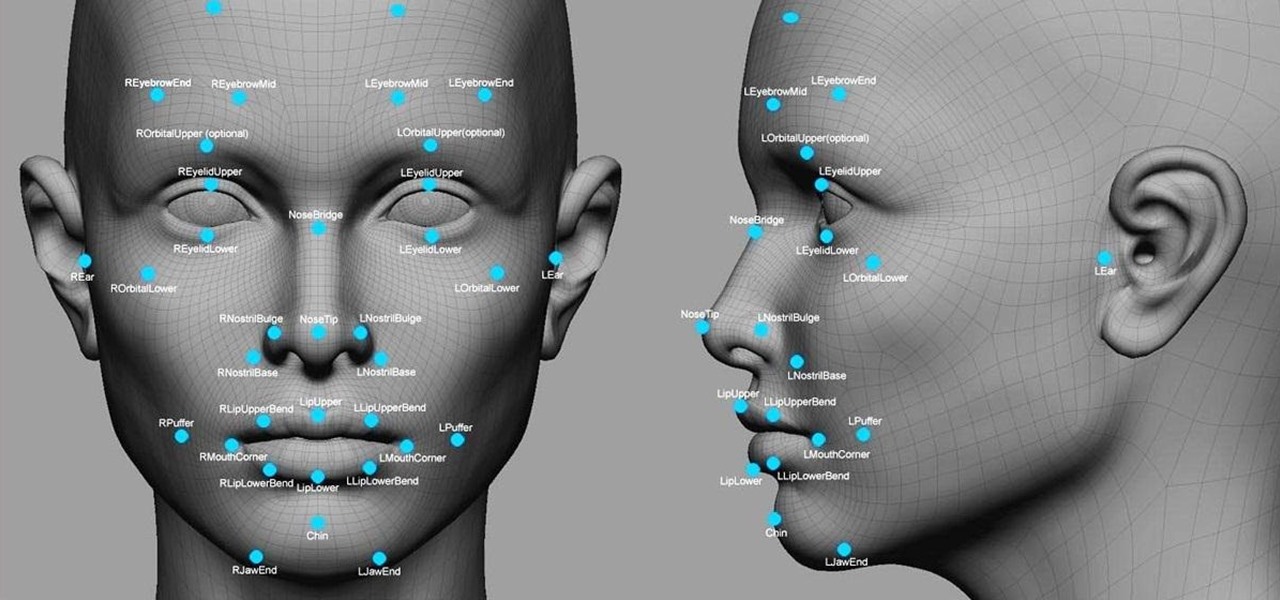
Facial recognition software is being more widely used with every passing day. Your local law enforcement is probably already using it, and it will be even easier for them now that the FBI handed out its own facial recognition software to state authorities. Even the fine folks at Facebook are using this technology. Obviously, this brings up some pretty serious privacy concerns amongst most people, because honestly, who wants to be tracked? Right now, there's not a lot we can do about it being ...

There are tons of situations that require you to give out your phone number, and I think just about everyone has regretted doing so at some point. It can be incredibly convenient to have a secondary or temporary number on hand, so if you don't want to provide your real digits, you can still get the call without revealing your true numbers. And that's where Burner comes in. Burner is a mobile app for iPhone and Android that lets you create alias phone numbers that you can take out of service a...

At the recent DefCon conference in Las Vegas, researchers opened many of the top commercially available gun safes with simple tools like a straw or a paper clip, and in one case, just by shaking it a bit. The investigation began after the researchers, Toby Bluzmanis, Marc Tobias and Matt Fiddler, learned that certain Stack-On safes, issued to some law enforcement officials to secure their firearms at home, could be opened simply by jiggling the doorknob.

Assuming everyone knows of the recent "String of attacks" passed between Obama and Romney, I just want to talk about how useless this entire thing is. I'll try to be as un-biased as possible.

There's no shortage of ice cream recipes out there, but one ice cream shop in London has found a unique recipe to sell to its customers, and of course it's controversial—breast milk ice cream.

In this tutorial, we learn how to make sonora hot dogs. You will need: tomatillos, chicken broth, refried beans, queso, dried cilantro, hot dogs, lemon juice, bacon, tomato, garlic, jalapeno, mustard, ketchup, and mayonnaise. First, place the cilantro and jalapeno and place into blender with lime juice. Next add in your chopped onion and chopped tomatillos and start to blend while adding in the garlic and chicken broth. Next heat up a large pan with lard, and once it has melted add the sauce ...

What should you do if the police come to you? Or, most importantly, what should you NOT do if police just want to chat? Check out this educational video that will help you escape the clutches of an officer of the law, without being rude, and without getting caught doing something bad.

Do the cops think you had too much too drink? Not on Playbook's Matt Bean's watch! Find out what to do if you get caught drunk in public from Former NYPD Detective Scott Androvic.

It is well documented that what you say and do online is tracked. Yes, private organizations do their best to protect your data from hackers, but those protections don't extend to themselves, advertisers, and law enforcement.

Apple Card has generated quite the buzz since its March 2019 announcement. The iPhone maker's new credit card pairs with Apple Wallet on your device, is simple to sign up for, includes enhanced security over other cards, has zero fees, and provides daily rewards right to your Apple Cash account. And as good as that sounds, the fine print can complicate things real quick.

For lack of a better word, a missing iPhone sucks. Not only do you lose a physical device that cost you a small fortune, but there's also the probability you'll never see your precious data again. Hackers and thieves might, just not you. To keep this from ever happening, there are preventative measures you should take, and the sooner you do them the better.

The rise and fall of Meta, the Silicon Valley-based augmented reality startup that looked to challenge the likes of Microsoft's HoloLens, and others, took just six years.

| Update: ZTE's issues with the US government have finally been resolved. Check out the details below.

Just days before the release of the first image of the Magic Leap device, the company's CEO, Rony Abovitz, knew that the biggest moment of his life was about to unfold the following week. But instead of hunkering down in the Florida-based confines of the company's skunkworks, he instead decided to deliver a speech to the public about, what else, the future.

Now that Fyre Festival co-founder Billy McFarland is charged with fraud, this is the perfect time to list off those top 15 influencers who promoted tickets to the disastrous event to their loyal followers, right?

There is an Indian story called the Legend of Paal Paysam, and while it doesn't seem like it at first, it has a lot to say about what motivated Paul Travers in the augmented reality space.

Nineteen days ago, several hundred people could have been exposed by a traveler with measles in Nova Scotia, Canada. The next day, someone flying from Minnesota to Nebraska may have spread the measles to other passengers. A couple weeks ago, it's possible that a man and his six-month old child spread the measles in several Seattle-based locations. Authorities are trying to locate persons who may have been in contact with these people. None of the persons with measles were vaccinated. Why?

Many new parents will tell you how hard it is to name a baby. Some have stories of how they knew what the name of their child would be from before conception, only to change their mind when they were born. Sometimes new babies can go weeks without a name since there is an endless selection to choose from.

Good day to everyone, today I will present some basic and advanced concepts that targets sophisticated attacks on the social basis, also I will write about some steps that can prevent this attacks from occuring, basically we will examine Social Engineering from the angle of attacker and victim, some people who are interested in security and work for middle-sized companys can learn and use something interesting from this post.