
How To: Tune vocal tracks in Logic Pro
Correct the pitch of your vocal and instrument tracks with this innovative software program. Learn more about digital pitch correction in this Logic Pro software tutorial from a professional recording engineer.


Correct the pitch of your vocal and instrument tracks with this innovative software program. Learn more about digital pitch correction in this Logic Pro software tutorial from a professional recording engineer.

Correct the pitch of your vocal track with this innovative software program. Learn more about digital pitch correction in this Melodyne software tutorial from a professional recording engineer.

Create funky beats in the same program used by Dr. Dre and Kanye West. Learn how to use Logic Pro 8 software to make music in this free music production tool from a professional audio engineer.

Make your mix sparkle with Logic Pro! Learn how to use Logic Pro 8 software to fine-tune your music mix in this free music production tool from a professional audio engineer.

Borrow a few sounds from other songs to make your mix stand out. Learn how to use samples with Logic Pro 8 software in this free music production tool from a professional audio engineer.

Equalizing (EQing) instruments, vocals and effects is an important part of the mix process. Learn how to use Logic Pro 8 features to mix your recordings in this free music production tool from a professional audio engineer.

In this video series, watch as professional sound engineer Kip Bradford teaches how to make and repair audio cables. Learn the tools needed to repair and make audio cables, learn what kind of solder to use, learn the types of connectors and wires to use, how to solder audio cables, how to remove solder from a solder joint, and how to roll audio cables.
To first get a Skype account you will need to go to Skype and download Skype onto your computer. To download the program click on your operating system and download the proper program. Once it is download you can click on the downloaded file and click on install. It will take a few minutes to install onto your computer. Once it is installed you will be prompted to make an account. To make an account you will have to enter your full name, and your desired username. You will also have to type i...

You love your bike and it was stolen. Although, this is not a good scenario, you still may be able to retrieve it. Sketch the serial number or means of identification into the bike and then when it is stolen you can really get the word out to all the places that it might turn up.

This may very well be the most important video series you will ever watch. You may not think it now but the next time you are pulled over as the officer is asking for your license and registration you will will be thinking of these tips and happy you took the 10 minutes to learn them.
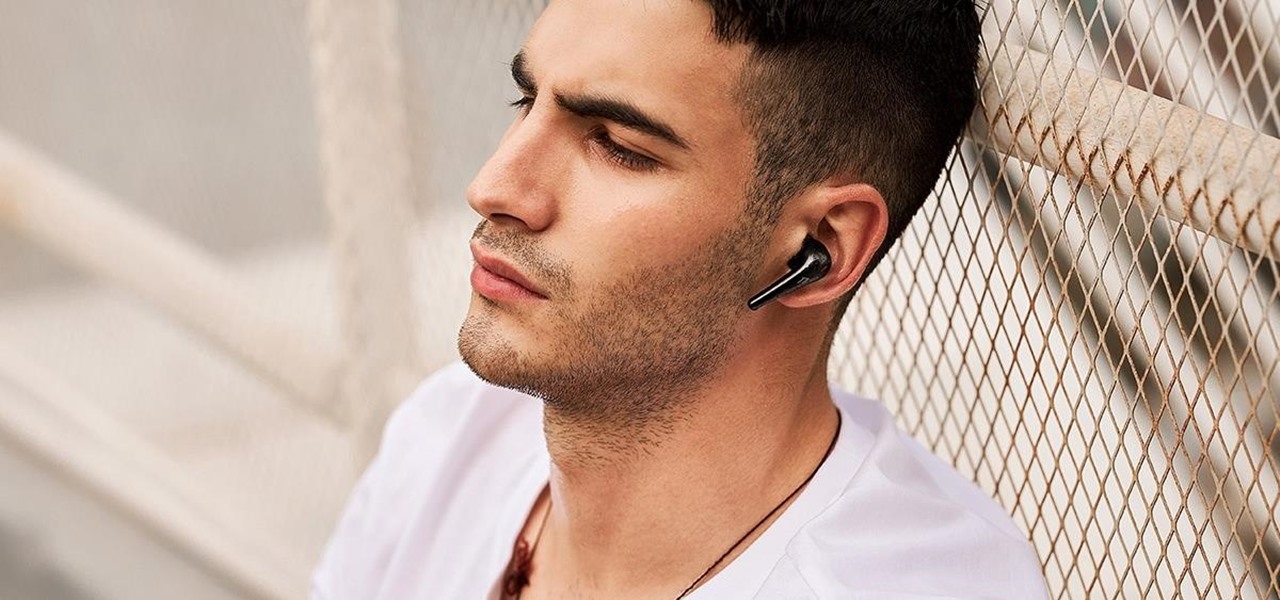
Having earbuds that don't work for you is kind of like having shoes that don't fit. They're never where they're supposed to be, and every second you're using them, you're acutely aware of how much they aren't working for you. And if they fall off, you'll probably step on them. ComfoBuds Pro True Wireless Headphones are the right fit, the right sound, and the right choice if you want to listen to music instead of being distracted by the place your music is supposed to come from.

We're living in the age of Big Data. As the primary force behind everything from targeted marketing campaigns and online search algorithms to self-driving cars and even space exploration, massive sets of complex data stand at the heart of today's most exciting and important innovations.

Many people get into audio and video production out of a passion for making music, films, or documentaries. Yet once they're locked in, they realize the endless possibilities at their fingertips. With more digital content being created every hour, reliable engineers are needed.

Google Drive has been a gamechanger in the business world. First launched in 2006, Google Sheets has become much more than an alternative to Microsoft Excel. The powerful spreadsheet program is a boon for efficiency that's accessible wherever you have an internet connection—or when you have time edit offline.

Since Motorola engineer Bill Smith invented Six Sigma in 1986, corporations around the world have employed it to eliminate costs and process cycle time while increasing profits and customer satisfaction. These techniques and tools for process improvement were invaluable to famed CEO Jack Welch, who used them to redefine General Electric's business strategy in 1995.

It's common knowledge that when it comes to your child being happy and successful in life, giving them access to an excellent education is paramount. Whether your son or daughter grows up to be an engineer or an artist, they should be well-rounded in a wide range of diverse disciplines to take advantage of all the opportunities that will inevitably come their way.
It can seem as though there's a virtually endless number of essential programming languages to choose from these days. And complicating matters even further for aspiring or even established programmers, developers, and hackers is the fact that most languages are a bit esoteric and suited for only a certain number of relatively finite tasks.

Using a strong password is critical to the security of your online accounts. However, according to Dashlane, US users hold an average of 130 different accounts. Memorizing strong passwords for that many accounts is impractical. Fortunately, password managers solve the problem.

In years past, the Consumer Electronics Show (CES) mostly dabbled in the future as far as the long-term vision for augmented reality was concerned. This year, however, objects in the future are much closer than they appear.

It looks like Pokémon GO players may get a surprise gift from the game's developer, Niantic, this holiday season.

Apple's ARKit has built a considerable lead in terms of features over Google's ARCore, but Google's latest update to ARCore adds a capability that makes the platform a bit more competitive with ARKit.

Investment in augmented reality remained robust in 2019. For the third consecutive year, we looked back on the biggest funding deals in the AR industry this week, and a familiar name came out on top.

While its competitors are concentrating on building out AR cloud platforms to give advanced AR capabilities to mobile apps, Ubiquity6 is taking a step in a different direction.

The week in AR business news started out with a bang with two bombshell reports that cast a shadow on the AR industry as a whole.

Augmented reality plays a key role in the evolution of adjacent technologies, such as 5G connectivity and brain-control interfaces (BCI), and the business news of the week serves up proof points for both examples.

There are a lot of songs out there, so it's tough to remember all of the words to every song you like. If you're like me and have a less-than-perfect memory, visual aids will ensure your Apple Music jams aren't interrupted with incorrect or forgotten lyrics. That's why Apple's update with time-synced lyrics is so cool, essentially turning your iPhone into a portable karaoke machine.

Over the past decade, Marvel Studios has been a dominant force at the box office, raking in more than $21 billion dollars. Averaged out over that span of time, the yearly earnings of those movies outweigh the gross domestic product of some countries.

The ability to shift between virtual reality and augmented reality seamlessly on one device is a dream of many AR fanatics, but the execution is usually fairly buggy or underwhelming.

Apple had its Worldwide Developers Conference on June 3, 2019, which showcased big software announcements for all of Apple's hardware, and anyone can watch the keynote as it happened.

Developers in the augmented reality industry got a lot of love this week.

When joining a new network, computers use the Address Resolution Protocol to discover the MAC address of other devices on the same network. A hacker can take advantage of ARP messages to silently discover the MAC and IP address of network devices or actively scan the network with spoofed ARP requests.

To borrow from the canon of Game of Thrones, what is dead may never die. And while the Meta Company that we knew this time last year is no more, the patent infringement lawsuit filed against the company lives on.

As Microsoft continues to bask in the glow of its HoloLens 2 unveiling and begins ramping up the hype to launch, Nreal and Vuzix are carving out their own niches in the AR hardware landscape.

Current-generation mobile augmented reality apps offer users numerous opportunities to punch up photos and videos with 3D content, but there's surprisingly few options for users to express themselves using virtual characters.

Augmented reality and computer vision company Blippar has a new lease on life, as previous investor Candy Ventures has completed a successful bid to acquire the assets of the beleaguered company.
When Google introduced the Pixel 3 on October 9th, one of new additions they briefly mentioned was the Titan M security chip. While they did talk about how it will improve overall security, they didn't expand on the number of changes it brings to the Pixel 3's security. Well, they finally shared more, and it's a pretty big deal.

They're finally here. Apple announced three new iPhone models at their "Gather Round" event in Cupertino, and they're all absolutely gorgeous phones. With bezel-less screens and polished titanium edges, the iPhone XS, XS Max, and XR are truly marvels of engineering — but perhaps the most impressive design feat Apple pulled off is the fact that two of these models are rated IP68 under the IEC standard 60529.

With the rise of website encryption (TLS), sniffing passwords from network activity has become difficult. However, it's still possible to quietly exfiltrate a target's network traffic in real time to extract passwords and sensitive information. Pertaining to macOS, there are two methods for retrieving traffic from a backdoored Mac.

As Magic Leap prepares to ship the Magic Leap One later this year, the company is putting its focus on mentoring developers and creators to build a content ecosystem for the spatial computing platform.

The microphone in a Windows computer is accessible to most applications running on the device at all times and completely without security limitations. Information gathered from recorded audio conversations taking place in the surrounding area of a compromised computer can be used for social engineering, blackmail, or any number of other reasons.