All fields of study have their own language. For people interested in learning about microbes, the language can sometimes be downright difficult — but it doesn't need to be. From antibiotics to xerophiles, we have you covered in an easy-to-understand glossary.

In this video, I'll be showing you how classic black snakes work and how to make them at home. There are actually two methods covered in the video — one that uses fire and one that does not. So just choose the one that fits best for your situation.

I learned the hard way that boxed dyes just don't work well for me. A few months ago, I tried one that had a pretty name like "soft violet black." Sounds nice, right? What I ended up with was brown hair and hot pink roots. Trust me, it wasn't cute.

How to adjust a sliding door. Sliding doors are great when they are sliding but can be a real pain in the bum when they don't. Today's video will concentrate on adjusting the wheels to help alleviate some of these annoying issues. It doesn't matter if it's a robe sliding door, a closet sliding door, a glass sliding door or a patio sliding door, the principle is still the same. Obviously there can be other factors like the sliding door track or the sliding door wheels being in a state of disre...

Pyromania is definitely nothing new on WonderHowTo. From flamethrowers and hydrogen fireballs, to flame-making pistons and wine corks, to simply burning steel wool fireworks and DIY smoke mix, we've covered it all. But when pyromaniacal mad scientists feel the need to release some tension in the lab, gummy bears and cockroaches become the victims of euphoric oxidation by way of molten potassium chlorate. A recent video by famous YouTube chemist NurdRage shows one of mankind's most despised cr...

Here is an Indian Chinese fusion dish that will really wow your taste buds. This dish combines a plethora of shredded vegetables together plush lots of seasoning and a binding agent to create colorful balls that only need to be fried up and enjoyed.

Champagne is great, rare champagne is even better in The Saboteur for the Xbox 360. Prove yourself and find the bottle in the second mission in Act 1: Bottle Shock. Luc needs antibiotics for his wounds. Luckily, Santos can provide them if you do him a favor. You'll need to steal back a bottle of champagne for him. Leave the new HQ and hop in a car. Now follow the GPS to the location of the champagne bottle. A pair of Gestapo agents will be guarding the front gate of the courtyard the bottle s...

Buying a digital camera doesn't mean your old prints, slides, or negatives are obsolete. You can easily convert them with a scanner to bring them into the 21st century. Watch this video to learn how to convert photos to digital.

If you're an aspiring actor, your headshot is a vital part of your arsenal. It is the first thing that most casting agents will see, so it has to be perfect. This video will give you tips for getting the heashot you want, the one that will get you your big break!

Watch this video tutorial to learn how to book the best hotel room for your money. You've spent all year saving up for your dream vacation. The last thing you want is to end up in a hotel room that ruins the whole trip.

Learn how to solder. Whether you like to tinker with electronics or do your own plumbing repairs, soldering metal is an essential skill. Plus, it's kinda fun.

One of the most common web application vulnerabilities is LFI, which allows unauthorized access to sensitive files on the server. Such a common weakness is often safeguarded against, and low-hanging fruit can be defended quite easily. But there are always creative ways to get around these defenses, and we'll be looking at two methods to beat the system and successfully pull off LFI.

Notaries can make $75-125 an hour for their services. All it takes is one course and a small fee to get a license and you will be on your way to raking in the extra cash. Being a notary is a great boost to your resume and your pocketbook, so why not give it a try?

Determining the antivirus and firewall software installed on a Windows computer is crucial to an attacker preparing to create a targeted stager or payload. With covert deep packet inspection, that information is easily identified.

Augmented reality and drones already go together like turkey and stuffing, but a new iOS app adds some spice to the combination with a new kind of flight path automation.

In the waning days of October, at the Innovation Tokyo 2018 conference, attendees got their hands on some of the new augmented reality experiences that Niantic is working on through its Real World Platform.

Augmented reality gaming developer Niantic has decided to give its players the opportunity to make their mark on Pokémon GO with a PokéStop nomination system.

If you want to follow Null Byte tutorials and try out Kali Linux, the Raspberry Pi is a perfect way to start. In 2018, the Raspberry Pi 3 Model B+ was released featuring a better CPU, Wi-Fi, Bluetooth, and Ethernet built in. Our recommended Kali Pi kit for beginners learning ethical hacking on a budget runs the "Re4son" Kali kernel and includes a compatible wireless network adapter and a USB Rubber Ducky.

Hitman Sniper topped our roundup for the best premium shooting games, and it's easy to see why. Straightforward yet intense story. Awesome visuals. Stealthy action. Strategic gameplay. Hitman Sniper is easily the best sniper game available for your smartphone, and it's currently free on Android for a limited time, as well as discounted for iPhone.

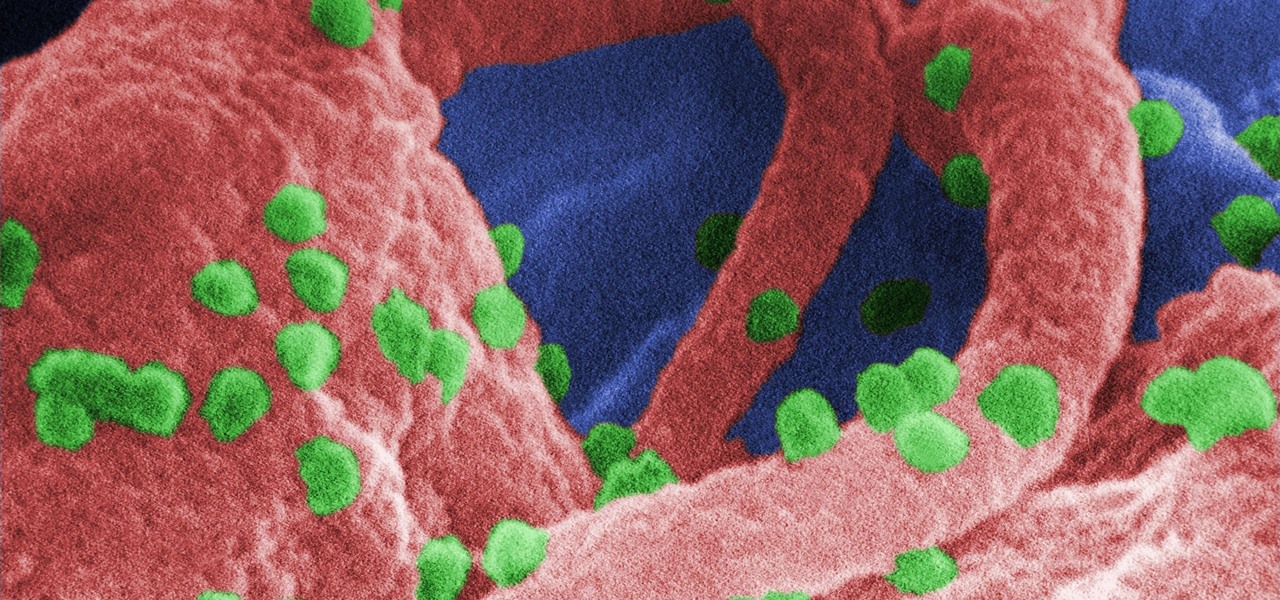
A vaccine against HIV might prevent the disease that we can't seem to cure. Some HIV patients make antibodies that can take down the virus, much the way a vaccine might. But, scientists haven't been able to provoke that type of response in other people. However, in a process that might work in humans, a group of researchers has successfully generated antibodies in cows that neutralize multiple strains of HIV.

As if the swollen, painful joints of rheumatoid arthritis weren't enough, the disease is the result of our immune system turning against cells of our own body. Ever since this realization, scientists have worked to find the trigger that sets the immune system off. Scientists believe that gut bacteria may have a role in initiating the abnormal immune response. Now, a team of researchers from Boston has figured out how that might occur.

The problem with HIV is that it attacks and kills the very cells of the immune system that are supposed to protect us from infections — white blood cells. But a new technique, developed by scientists at The Scripps Research Institute (TSRI) in La Jolla, California, offers a distinct HIV-killing advantage.

An innovative new wound dressing has been developed by a research team at Lodz University of Technology in Poland that uses crustacean shells to create a bandage that packs an antimicrobial punch — and even more potential to help solve a global problem.

Soy sauce is a sushi essential for most Americans and we don't often consider its exact origins whilst chowing down on that tuna roll.

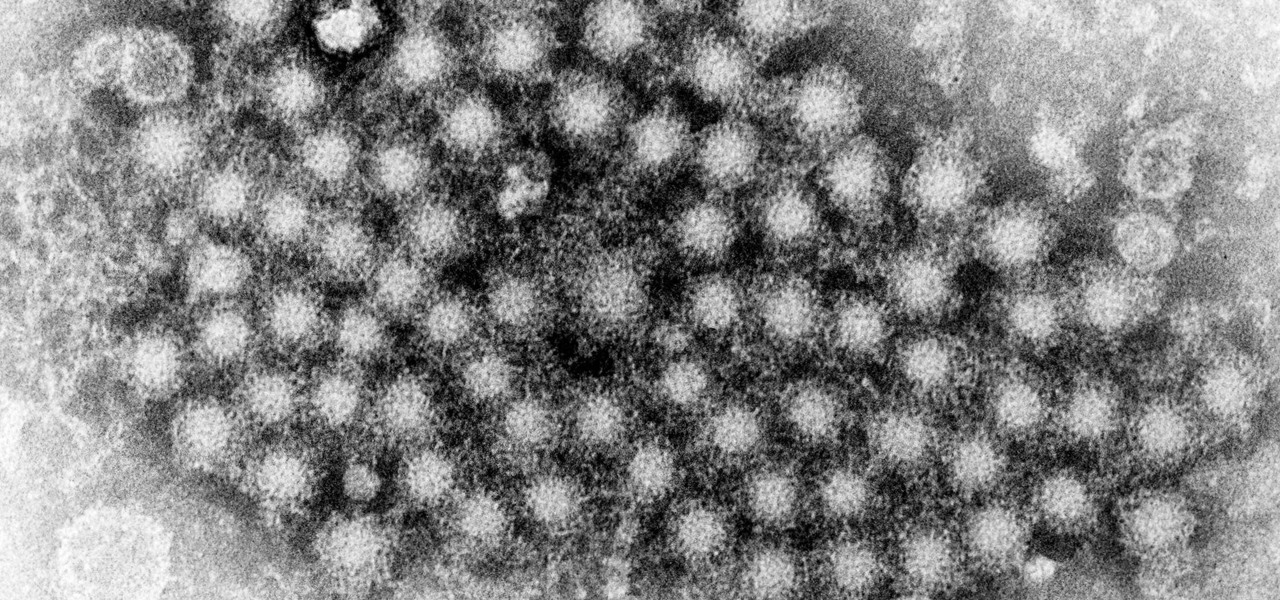
This month, Iowa issued their first hepatitis C virus epidemiological profile and the news was not good. The number of cases of hepatitis C reported in Iowa between 2000 and 2015 rose nearly threefold, from 754 cases in 2000 to 2,235 cases in 2015.

Maternal infection with genital herpes, or other pathogens, during early pregnancy could increase risk of autism, or other neurodevelopmental disorders, says a new study.

Google first introduced Google Home, its latest smart product in the works, at the company's I/O conference in May 2016. It will directly compete against Amazon's Echo, which has so far been a success with over 3 million devices sold, and it was even featured as FBI Agent Dom's only real friend in the second season of Mr. Robot. Google may have their work cut out for them, but we're betting Home will knock Echo out of the water. Google Home is a personal assistant with a built-in speaker and ...

Fish is a remarkably useful ingredient, whether you eat it as is or use fish sauce to give your recipes extra depth and flavor. However, if you enjoy a glass of Guinness on occasion, you might be surprised to know that there's most likely fish in that beverage, too.

Welcome back, my tenderfoot hackers! A short while ago, I started a new series called "How to Spy on Anyone." The idea behind this series is that computer hacking is increasingly being used in espionage and cyber warfare, as well as by private detectives and law enforcement to solve cases. I am trying to demonstrate, in this series, ways that hacking is being used in these professions. For those of you who are training for those careers, I dedicate this series.

I think it's safe to assume that most of us appreciate a little privacy and security when it comes to our mobile devices, which is exactly why we have lock screens that require unique passwords, patterns, or PINs. Although someone can discretely peer over your shoulder to see what your password is, it's much more difficult for them to duplicate your face to unlock the device.

With developments from tech giants Apple and Samsung being shared throughout the interwebs, the term smartwatch has become increasingly popular over the last year. That being said, smartwatches have been around for a while.

Most of you probably spread ketchup all over hamburgers and fries. Some of you may even drink it straight. But did you know that tame (and slightly addictive) condiment in your fridge is also a powerful cleaning agent?

Let's just say it's been a pretty bad year for spies and government agencies and an even worse one for the privacy of U.S. citizens. Edward Snowden blew the lid off the NSA's spy program, and the FBI was recently discovered to have the ability to access your webcam any time they want—without triggering the "camera on" light. Yeah, that means those Justin Bieber lip sync videos you recorded weren't just for your private collection.

Did you know you can help protect yourself when traveling with a gun? No, not like that; and not in any way that's going to land you in prison. Simply by packing a gun, you can ensure that not only will your luggage be safer, but that the airline will make certain that it reaches its destination. Photo by Alamy

Featured on MTV's Catfish TV series, in season 7, episode 8, Grabify is a tracking link generator that makes it easy to catch an online catfish in a lie. With the ability to identify the IP address, location, make, and model of any device that opens on a cleverly disguised tracking link, Grabify can even identify information leaked from behind a VPN.

The latest film addition in the American-produced Millennium series, The Girl in the Spider's Web, was just released on Blu-ray a few days ago. As you could expect, the movie has many hacking scenes throughout, just like the previous English and Swedish language movies centered around hacker Lisbeth Salander. Of course, with the quick pace of some scenes, the hacks can be hard to follow.

For anyone using open source information to conduct an investigation, a balance between powerful tools and privacy controls are a must. Buscador is a virtual machine packed full of useful OSINT tools and streamlined for online research. This program can easily be set up in VirtualBox, and once that's done, we'll walk you through some of the most useful tools included in it.

The gig economy is thriving, and if you aren't already making money with your phone, you could be missing out on easy residual income. Some people just want extra cash, and some even manage to completely ditch the 9–5, enabling them to work at their own pace and set their own hours.

With the addition of the OpenSSH client and server in the Windows 10 Fall Creators Update, you no longer have to rely on third-party programs to open an SSH server and connect to a Windows machine. While still a beta feature, this represents a long-overdue update fulfilling a promise made back in 2015.

In the case of rotting food, microbes are not our friends. Now, scientists have developed a new food wrap coated with tiny clay tubes packed with an antibacterial essential oil that can extend the shelf life of perishable food, so we can waste less and eat more.