How To: Twitter's Massive Security Flaw Makes Your Password Easy to Hack
What's your Twitter handle worth? If it's considered "desirable" (aka short and simple), it'll get you around 100 bucks, or, if you prefer, the affections of a teenage girl.

What's your Twitter handle worth? If it's considered "desirable" (aka short and simple), it'll get you around 100 bucks, or, if you prefer, the affections of a teenage girl.

Most newer computers come with a webcam, but if you're using an older system, you may not have one. If you only need to use a webcam occasionally, it may not be worth putting the money into, so why not just use your smartphone? There are a few apps out there that can help you turn your phone into a super-convenient wireless webcam and save some cash.
It's already August, which means school will be back in just a few short weeks. If you're getting ready to start or go back to college, that means you'll probably be dropping a few hundred bucks on textbooks. Here are some of the best places online to buy, sell and rent textbooks so that you can get back to more important things, like making your papers look longer than they really are and getting around your school's website blockers. Plus you can spend your money on more exciting things, li...

There's nothing worse than losing your phone—except losing your phone when the ringer is silent. If you're alone, it can be excruciatingly hard to find your lost device even if the ringer is on, considering most of us don't have landlines anymore. So, the next time you find yourself hunting for your phone, don't tear your house apart until you've tried some of these quick tips.

Getting spammed or too many viruses? This trick will protect your computer from websites trying to access or corrupt it.

This video will take you step by step on how to do some basic memory editing and hacking in Super Mario All Stars: Super Mario Brothers 3.
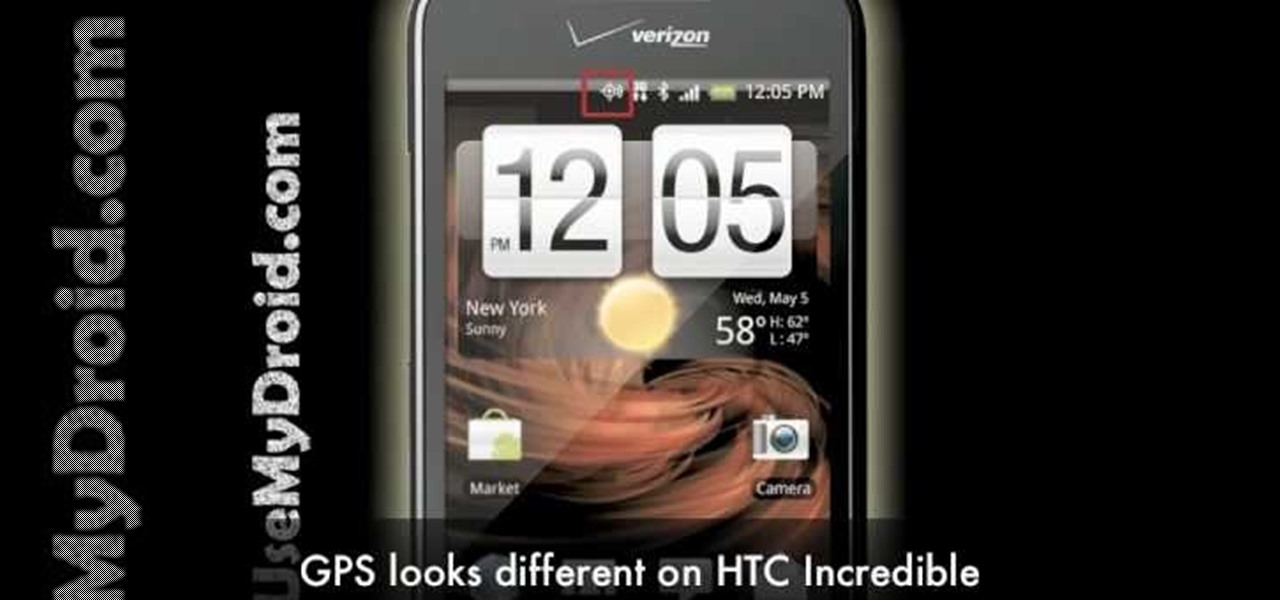
Battery life is a constant problem with cell phones today, and the Droid smartphones running Android software are no exception. If you want to learn how to get the most out of your Droid battery, then check out this helpful video that provides 8 tips on cutting battery-eating apps and features. If you want more battery life and are willing to sacrifice the cool features of the Droid cell phones, then you have to do these things. Don't let you Droid battery get drained!

Okay, just because the new Verizon Wireless Droid X comes with an HDMI-out port doesn't mean you're limited to just that. Motorola has made it possible for you to play video, music, and pictures to your television without any wires at all. With the Droid X's DLNA media sharing application, you can easily stream to an PS3 or Xbox, send pics to your PC, and stream videos to your TV. Check out this video walkthrough to learn how to use the DLNA services to connect your Droid X to the PlayStation 3!

Washington State has a history of large earthquakes, as does California. More than 1,000 earthquakes are registered in Washington State each year. More than 10,000 are recorded in California each year. In an earthquake, non-structural elements, which is anything that does not actually hold the building up, may become unhooked, dislodged, thrown about, and tipped over. this can cause extensive damage, interruption of operation, injury and even death.

This video tutorial from TruTricks presents how to setup Google customized alerts.Open your internet browser and search for Google Alerts using Google search engine.Click first result that says Google Alerts.You will need to sign in to use this Google feature.Google or Google mail account will work. If you don't have it you should create one.After you signed in Google Alerts welcome screen will open.Here you can create new Google alerts using Create a Google Alert window.Enter Search Term you...

There are a lot of things out there in the design world that people have seen and liked, but didn't know how to make. LIke vector lights. Watch this Illustrator video tutorial to take a look at those cool glowing, color changing, fading, bright, neon-like, fanning spread of glowing colors. Maybe there's no specific name for them, but for now, refer to them as 3D Light Ribs. You can use these in photographs, illustrations, composites, print work, web design, and maybe even a logo or two! You w...

This beauty video demonstrates how to create a St. Patrick's Day makeup look.

This beauty video demonstrates how to do an 88 Palette purple posey makeup look .

Origami plane designed by Joost Langeveld. This bomberjet is pretty easy to fold. This is an origami tutorial brought to you by Joost Langeveld origami, a dutch origami artist. Joost offers some of the prettiest, most creative models. Joost has been doing origami for seven years and about a year and a half a go, started designing models.

XSS Shell is a cross-site scripting backdoor into the victim's browser which enables an attacker to issue commands and receive responses. During a normal XSS attack an attacker only has one chance to control a victim's browser; however, the XSS Shell keeps the connection between the attacker and the victim open to allow the attacker to continuously manipulate the victim's browser. XSS Shell works by setting up an XSS Channel, an AJAX application embedded into the victim's browser, that can ob...

This video tutorial from kobeshoot shows how to create, upload and seed torrents using uTorrent application on your computer.

How to set up an e-mail account in Windows Live Mail.

This video shows you how to add live web content to your website using iWeb. You can embed content from an iGallery, add google maps, widgets and more.

In this video Special Guest Lynn Grillo from Adobe will show us how to create and use GoLive page templates. Templates in GoLive allow you to define the page design and placement of your objects. By using Templates if you ever decide to update/change the design of your site, all you have to do is modify the Template page that your site pages are based on.

Perceiving Reality answers that if you just believe in God, then you can't live a spiritual life. What is spirituality? According to Kabbalah, spirituality can't be defined as a belief or philosophy, but only as a clear perception and sensation of reality.

How to track an email address. Useful if you meet someone who says they are from somewhere e.g. LA as given in the video and you don't believe them. Go to the Rate a Bull site type in their email address and then hit return or 'find them'. The site will give you options to see information about them on the internet, MySpace, Facebook or other site or track the email. The site gives instructions on how to track the email via outlook, outlook express and other mail programs and the video shows ...

In iOS 13, Apple added an important new feature to its HomeKit smart home ecosystem called HomeKit Secure Video. With it, you have a secure, private way to store and access recordings from your smart home IoT cameras.

Apple's iOS 13 has been available for beta testing since June, and the stable release pushed out to everyone on Thursday, Sept. 19. To help you make the most out of iOS 13 for iPhone, we've rounded up everything you'll want to know, whether a colossal feature, small settings change, interface update, or hidden improvement.

Whether you've celebrated multiple cake days or you're just now getting your feet wet with Reddit, it's a rite of passage to choose your preferred smartphone client. Quick spoiler: Your best option most certainly is not the official Reddit app.

Net neutrality is dead and your internet service providers can collect all the data they want. While VPNs are a great way to protect some of that privacy, they're not perfect. There is another option, though, called Noisy, which was created by Itay Hury. It floods your ISP with so much random HTTP/DNS noise that your data is useless to anyone even if they do get it.

While many of you were off surfing and lounging on some sandy beach or trying to figure out how to balance work with sky-high summer temperatures, I've been talking to all the companies that make augmented reality what it is today.

There's always an iPhone in our list of top phones for privacy and security, due in large part to advanced security measures like Face ID, consistent iOS updates, and easy ways to prevent unwanted access and excessive data sharing. However, some of those options actually do the opposite and hinder security. It all depends on how you use your iPhone, but you should at least know everything available.

Kali Linux is established as the go-to operating system for penetration testing, but in its default configuration, it's less than ideal for regular desktop use. While in many scenarios, a live boot or virtual environment can resolve these issues, in some situations, a full installation is better. A few simple changes can be made to a Kali Linux desktop to make it safer to use in this environment.

As you're surely aware, your phone can be used against you. Thanks to our cameras and microphones, a clever hacker can obtain access to your device and invade your privacy. But spying isn't limited to just these two sensors — gyroscopes, proximity sensors, QR codes, and even ads can be used to paint a very clear picture about who you are and what you're currently doing.

Before you go ahead and delete your Facebook — don't lie, you've been thinking about it — consider this. Facebook offers users a wide variety of privacy options to mess with, which can help you find a little control over your information. We're not saying this solves Facebook's privacy crisis, but it might be a more reasonable option than throwing in the towel entirely.

Imagine for a moment that a VPN is like putting on a disguise for your computer. This disguise works to change your IP address, secure your traffic with encryption, and mask your location to bypass regional restrictions. This makes it a helpful tool for both whistleblowers and journalists. VPNs are also built into the well-known Tor Browser.

The world is full of vulnerable computers. As you learn how to interact with them, it will be both tempting and necessary to test out these newfound skills on a real target. To help you get to that goal, we have a deliberately vulnerable Raspberry Pi image designed for practicing and taking your hacking skills to the next level.

Android has several features built into the platform that improve user experience but require extra attention to prevent a security breach. By modifying these settings, you can drastically reduce the possibility of someone exploiting your device or intercepting information.

At a global security conference in Munich, philanthropist and businessman Bill Gates spoke about the next pandemic and a dire lack of global readiness. Here's how his statement could come true—and how to be ready when it does.

Hello readers, and welcome to Null Byte. Before we start, for those of you who may not know me, my name is ghost_; I'm a relatively active member of our community and have been around for a while.

There's no getting around it: if you want to get good at playing the ukulele or any other instrument, you'll need to practice. Fortunately, the Internet is awash in free uke lessons, like this one from Ukulele Live, which make the task not only easy but fun. This clip, in particular, demonstrates how to perform old-school jazzy introductions and outros on the uke.
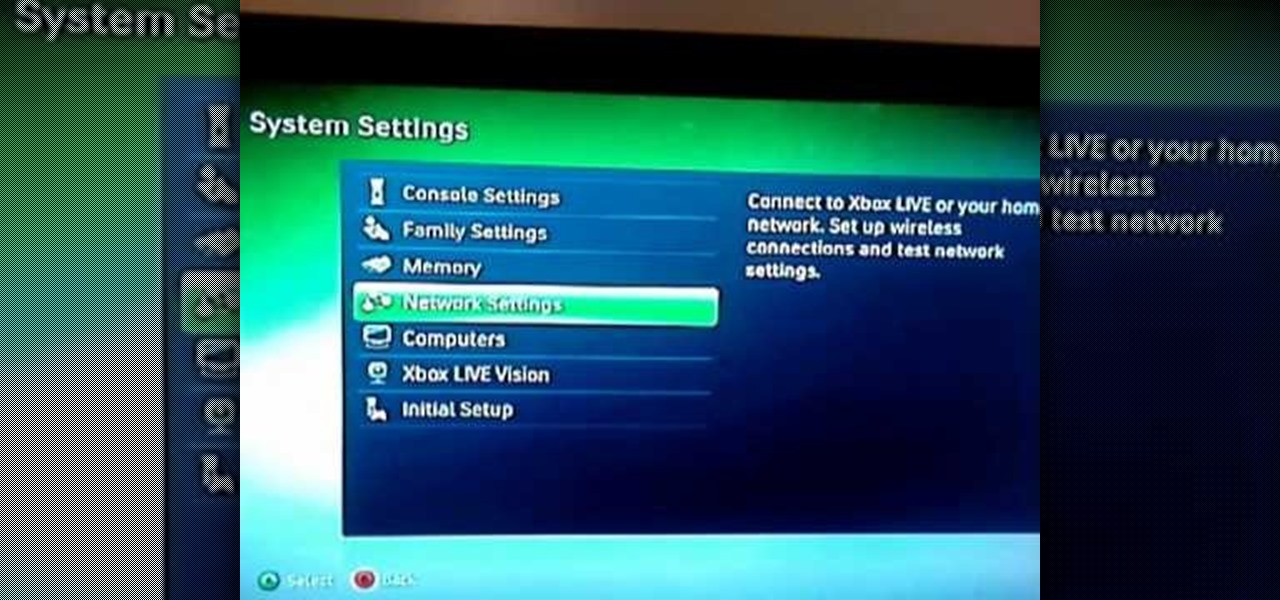
Your router is automatically equipped with firewalls meant to protect your PC from intruders. However, these firewalls often misread information needed to run online video games, and block necessary files from reaching your XBox. In this tutorial, learn how to change the NAT settings of your modem to "Open" and allow these files to get through. By doing so, you will be able to take full advantage of your XBox Live account.

In this video from nmsuaces we learn how to care for the Mexican elder tree. This is a widely used tree but it is not a good windbreak tree. It could have limb breakage. It's native to northern Mexico and southern California and is found in New Mexico. The sprouts on the tree need to be broken off the sides of the tree otherwise they are taking energy away from the rest of the tree. When it goes through its dormancy, you need to keep dead wood out of it. It needs a water source near it but it...

You may not realize it but when you buy music or movies from iTunes, you have to authorize it to be used on a computer and you can only authorize five computers. It's pretty easy to buy and replace computers and if you don't de-authorize the old ones, one day you will download a song and it will tell you that you have reached your five computer limit. At that point, what do you do if you don't have any of those computers anymore? Now Apple has put a fix in iTunes itself. Go to the iTunes stor...

The presenter, Ms. Jennifer explains how compound words are formed from phrasal verbs. With examples she explains how the meaning and pronunciation differs when compound words are formed from phrasal verbs. She explains the difference between 'show' and 'show off' by showing her collection of fans, and showing off with one of her beautiful fan from Japan. Then she explains the difference between 'show off' and 'show-off', giving examples and makes the listeners clear about compound nouns also...