If the Nexus 7 wasn't your first Android tablet, you may have noticed something different with the user interface when compared to other Jelly Bean tablets. You may not know exactly what it is off the top of your head, but it's there.

As a kid, there was nothing more fulfilling than sinking my teeth deep into the succulent flesh of an orange, savoring every drop of juice that wasn't busy sliding down your chin and onto your clothes. While my adulation for oranges never ceased as I grew older, the way I consumed the precious fruit did evolve with my maturity. Gone were the days of messy eating, and here I was now, peeling my oranges as a teenager, taking my precious time in separating each individual slice for a clean and t...

In a previous how-to, I showed how to send and receive text messages by wirelessly syncing them from your phone to your Nexus 7 tablet. Some eagle-eyed users may have notice that the Nexus 7 with 3G actually has a SIM card slot.
There's a lot going for the Samsung Galaxy Note 2—smart screen rotation, huge HD display, great rear camera—which makes it an awesome device for reading, watching videos, and taking pics. But all of those luxuries will end up hogging up your internal memory, which is one of the few things the Note 2 could use some help in. The device comes with 16 to 64 GB of internal storage, depending on your model, with the option of adding a microSD card for more space. Only problem is, everything automat...

For the most part, keyboard shortcuts are great. They save you some time and make it easier to do everything right from the push of a button. But like most things in life, there is always a caveat, and in this case, for me—it's a huge one.

The Rubik's Cube is probably one of the most well-known puzzles, but if the number of articles about how to solve them is any indication, it's also one of the least understood. How many people do you know who actually know how to solve one?

Firstly, I'd like to say that I have nothing against iPhoto; it's a great application that works wonderfully in Mac OS X. Unfortunately, when you no longer have iPhoto on your MacBook—and you don't want to pay for it—looking for an alternative is a necessary endeavor. I could sit here and try to explain to you how I updated to Lion and then inexplicably dragged the iPhoto application into the trash—and proceeded to empty said trash. I could tell you guys that story, but I fear you might judge...

Send an email prematurely? Forgot to attach a file? Accidentally addressed it to the wrong person? It happens to the best of us. But what can you do to get it back? Hack into the other person's email account and delete the email before they get a chance to see it? Unless you're a hacker extraordinaire, that option is unlikely. So, what can you do? If the email has already been sent, you're probably out of luck. Even if they didn't read it yet, your chances of retrieving it are slim. But some ...

In an effort to appease iPhone fans eager for an NFC-equipped device, an option that is available on many other smartphones, Apple created Passbook, their version of a digital wallet.

If there ever was a day to eat green candy, St. Patrick's Day would be it. But is there something better than the banality of green candy swarming the streets on St. Patty's Day? Yes—glowing green candy, and Instructables user BrittLiv wants us to show you how it's done.

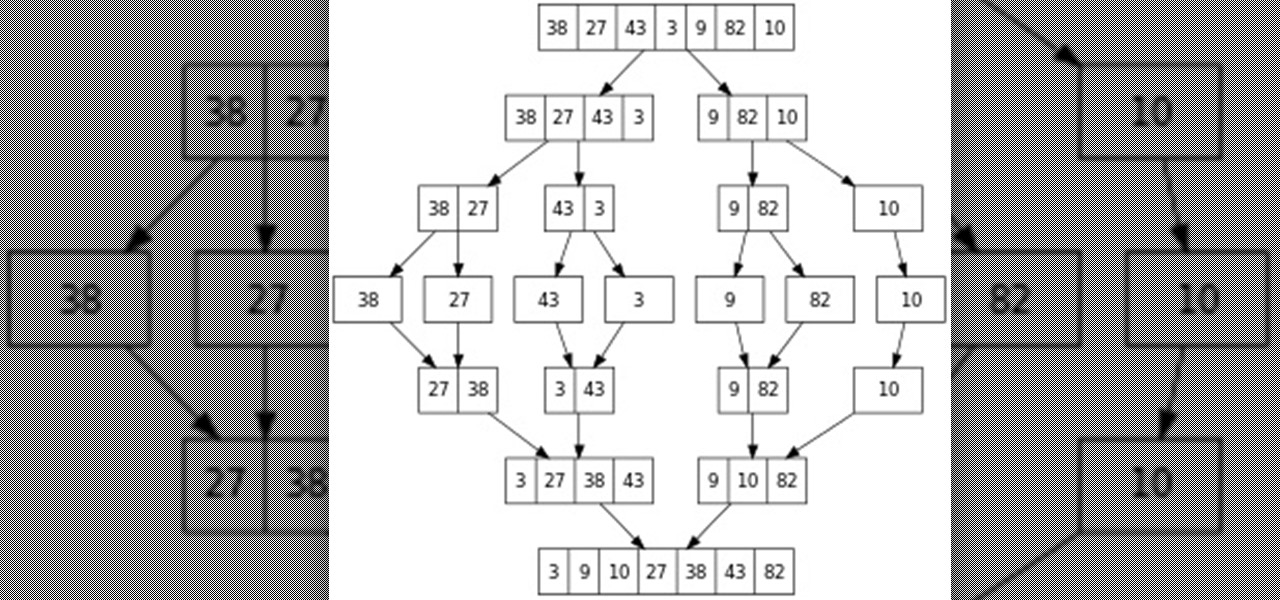
Hello everyone! This is part 7.0 of my Sorting series. I know, I said last time that there would be a 6.1, but not just yet!

Spammers are the bane of every email user. No matter what you do, junk mail always breaks through the spam filters. And some of the best ones seem to come from legit companies, and that's because they aren't legit companies— they're spammers masquerading as legit companies.

tobie91192 teaches you how to take apart an XBox 360 controller to change the cover. First, take out the battery pack on the back. Use a flathead screwdriver to remove all seven of the screws on the back of the controller. It's 2.0 mm. Once you take out the screws, place them in a pile so that you don't lose them. Remove the back of the controller and proceed to take out the grey plastic bottom part. Next, remove the buttons in the back. Then carefully remove the mechanism on the inside and y...

This video teaches the viewer how to multiply fractions with mixed numbers. You would first need to multiply the denominator by the whole number, and then add the product to the numerator. This number is your new numerator and the new denominator is the same as before. For example, 2 1/5 = 11/5. Now you have an equation with fractions and no whole numbers. You may now proceed to multiply straight across. Multiply the numerators together to create a new numerator and do the same for the denomi...

Magic Trick: The Cigarette Through Coin Have you ever heard of the Masked Magician? With the television series Magic's Biggest Secrets Finally Revealed, the so-called Masked Magician (Val Valentino) revealed secret after secret of the magicians repertoire. Valentino creates “the magic” then proceeds to reveal the reality of the illusions before a captivated television audience.

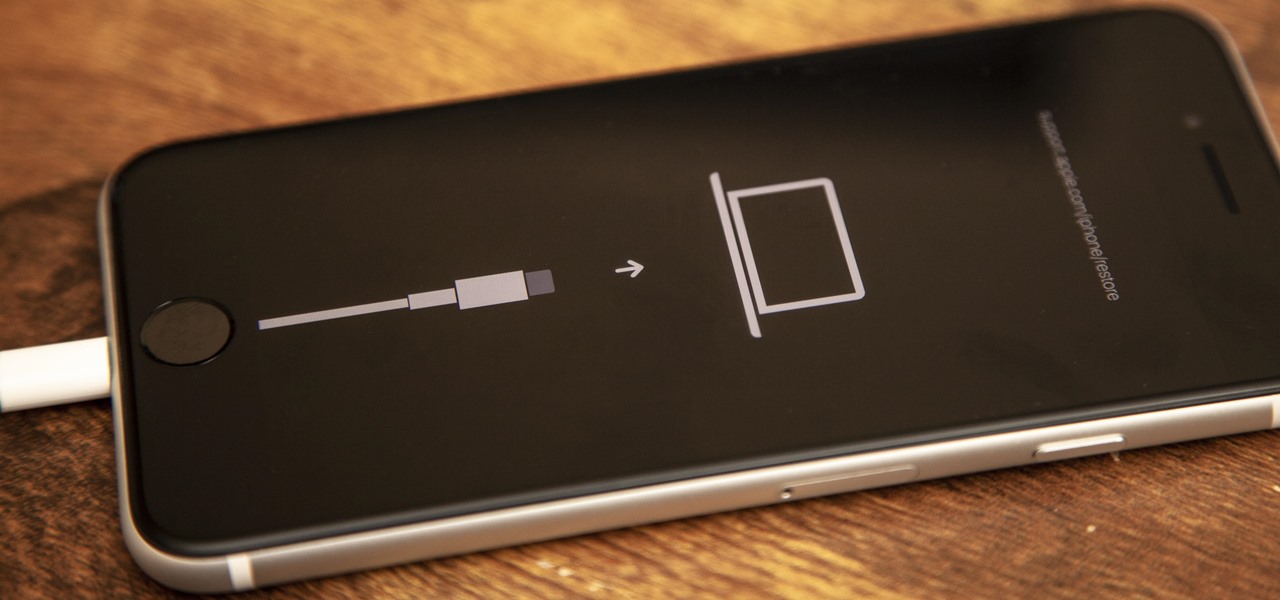
If your new 2020 iPhone SE is frozen, unresponsive, or won't load the system, and a standard power down and up procedure didn't work, there are few more things you can try. Force-restarting the device may do the trick, recovery mode is a last-ditch option, and DFU mode is your fail-safe.

A powered-off MacBook can be compromised in less than three minutes. With just a few commands, it's possible for a hacker to extract a target's password hash and crack it without their knowledge.

It's easy to run Kali Linux from a live USB on nearly any available computer, but many publicly accessible laptops and desktops will be locked down to prevent such use. School, work, or library PCs can be secured with a BIOS password, which is often an easily recovered default password. Once you have access, though, you can use a USB flash drive to run Kali live on any PC you find.

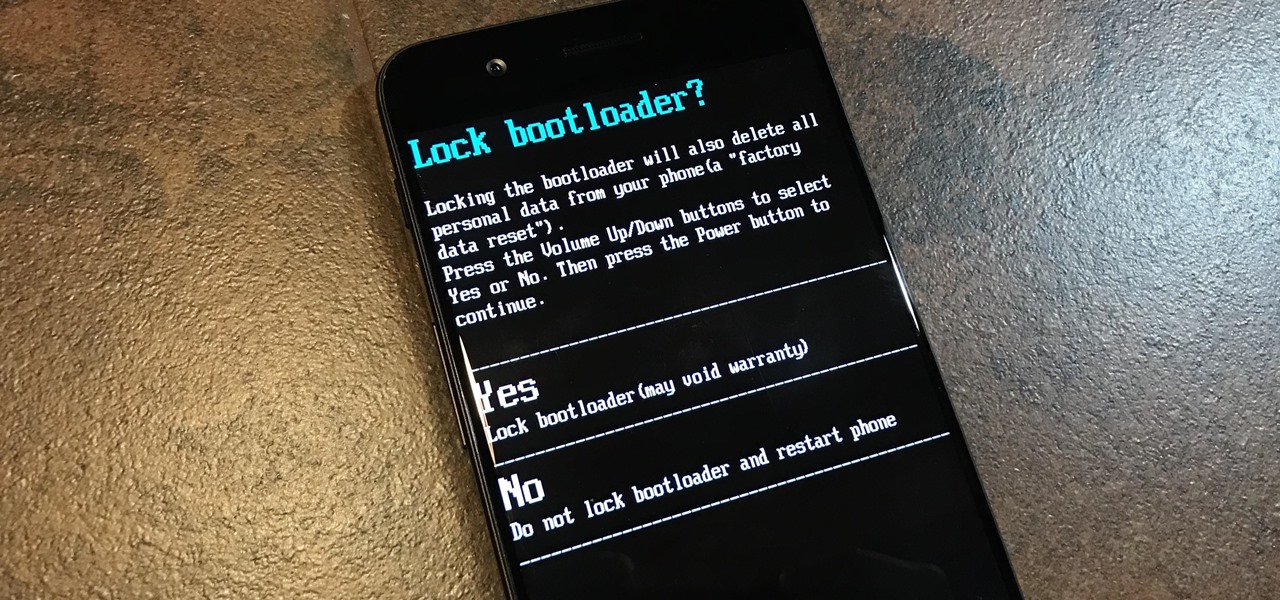
To please those of us who love to mod and root our Androids, OnePlus has made both the OnePlus 5 and 5T relatively easy to customize — so much so that the 5T topped our list for the best phones for rooting. Unfortunately, unlocking the bootloader and using root to modify the firmware on your OnePlus 5 or 5T makes it hard to update to a new firmware such as Oreo when compared to stock.

With tools such as Reaver becoming less viable options for pen-testers as ISPs replace vulnerable routers, there become fewer certainties about which tools will work against a particular target. If you don't have time to crack the WPA password or it's unusually strong, it can be hard to figure out your next step. Luckily, nearly all systems have one common vulnerability you can count on — users!

It's been little over a month since the official release of LG's latest flagship phone, the LG V20. Despite a few minor hiccups, the V20 has been attracting attention from all over for being an amazing phone. But like with most Android phones, there's no better feeling than rooting and taking complete ownership of it.

Jailbreaking gives you root access to the iOS file system, allowing you to install third-party apps and tweaks on your iPhone that aren't available in the App Store. It opens up a whole new realm for what your device can do, but it can also cause instability across the system and can dissuade you from getting future updates from Apple that have important features, bug fixes, and security enhancements.

Apple released the new Mac OS X 10.10 Yosemite in the Mac App Store for everyone to download and install for free on October 16th, 2014, but downloading a 5+ GB file for each of your computers will take some serious time. The best thing to do is download it once and create a bootable install USB drive from the file for all of your Macs.

Cashcroppimp teaches you how to open your XBox 360's NAT with Verizon Fios. You first have to find your IP address. For this, you simply point your internet browser to http://findmyip.com to find IP. This is also calling the default gateway. Make sure to write this down somewhere. Now you need to input this number in your internet browser. Enter your username and password and proceed to the next step. Now go to Firewall settings-DMZ Host. Here you will need the IP address from the XBox 360, w...

Imagine a scenario where you're nowhere near your iPhone, but it's on loud, and you really need to silence it. An alarm may be blaring, notifications could be spitting out sounds left and right, and calls may be ringing. Things can get annoying real quick for whoever's around it. Plus, all that attention makes it easy for someone to find and possibly steal your iPhone. Luckily, you can quiet it down.

When it comes to shooting games, battle royale titles like PUBG and Fortnite have come to dominate the scene, leaving other sub-genres like top-down and third-person shooters living in the shadows. They're far from irrelevant, though, as evidenced by all the great games released just in 2019 alone.

When your iPhone goes missing, it's serious business. Depending on your usage, your whole life might be connected to your iPhone, not the least of which includes debit cards, credit cards, and Apple Pay Cash stored in Apple Pay. While it's nearly impossible for someone to use your money with Apple Pay, it's still a good idea to disable it until you find your iPhone, just in case.

Almost every phone comes with biometric security of some sort these days, but the same can't be said of Windows computers. While fingerprint scanners are becoming increasingly common with laptops and desktops, they're nowhere near ubiquitous. Thankfully, your phone's scanner can be used as a sort-of remote authentication point for your PC.

The OnePlus 6T is easily one of 2018's best value phones for many reasons, especially when it comes to rooting and modding. But like many new phones, it's plagued with the single bottom-firing speaker that left us wanting more in the sound department. The speaker is decent on its own, but it appears to have some hidden potential at the same time.

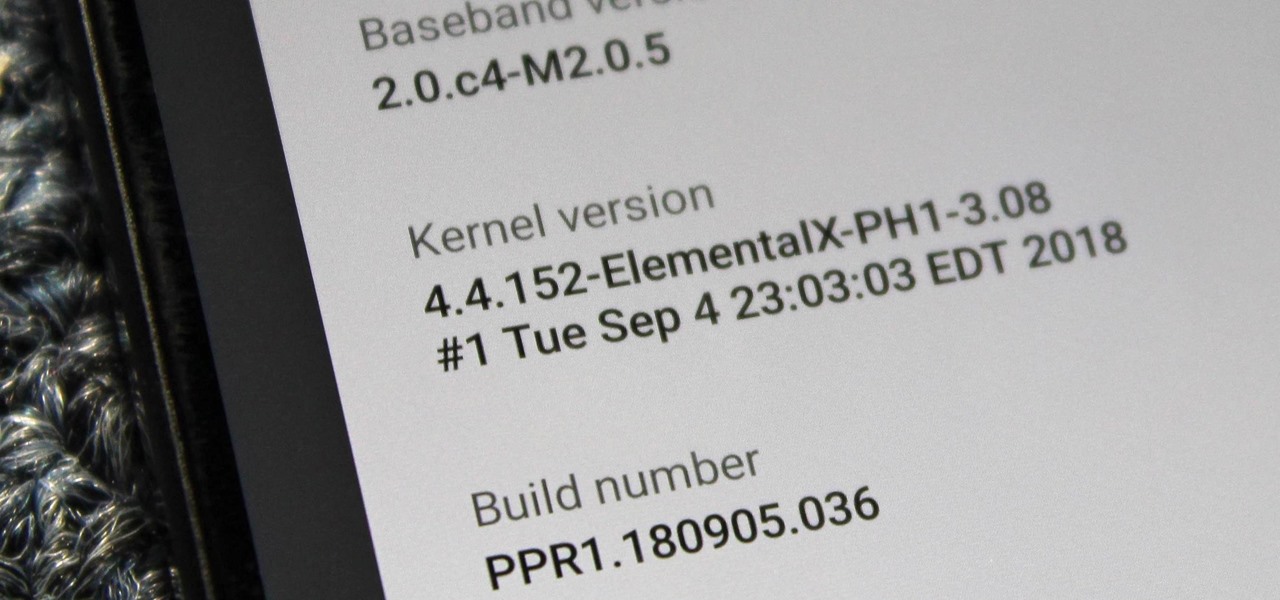
When you unlock the bootloader on your Essential PH-1, you open your device to a host of new possible tweaks. One popular modification is a custom kernel, which can not only speed up your phone, but give you new features that wouldn't be possible otherwise.

If you want to use your iPhone with another carrier, all you have to do is contact the original carrier to request an unlock, which is usually granted in a few days. Unfortunately, you need to meet specific criteria to officially carrier-unlock your iPhone, like paying off the device in full and completing any contracts. But that doesn't mean there isn't a workaround you can use beforehand.

Passwords and data stored in web browsers are extremely valuable to hackers. If not for financial gain, black hat hackers may still leak your passwords and personal information for amusement. Never undervalue what you're worth to a hacker.

Once a hacker has created a PowerShell payload to evade antivirus software and set up msfconsole on their attack system, they can then move onto disguising their executable to make it appear as a regular text file. This is how they will get a Windows 10 users to actually open the payload without knowing they are doing so.

While Wi-Fi networks can be set up by smart IT people, that doesn't mean the users of the system are similarly tech-savvy. We'll demonstrate how an evil twin attack can steal Wi-Fi passwords by kicking a user off their trusted network while creating a nearly identical fake one. This forces the victim to connect to the fake network and supply the Wi-Fi password to regain internet access.

With ultra competitive games like Fortnite Battle Royale and PUBG taking the mobile world by storm, gamers are looking for ways to get a leg up on the competition. One of the biggest advantages you can give yourself is the ability to aim and shoot while on the move, but that's not exactly easy with a touchscreen.

It's no secret that you can protect notes on your iPhone with a password, but one thing that most people don't know is that you can actually set unique passwords for each note instead of a blanket password for all of them. It's not obvious at all in the Notes app, but it's easy to do once you've got the hang of it.

As cheesy as it sounds, #HODL became a thing for a reason. A lack of discipline when dealing with cryptocurrencies can lead to impulse buys and panic selling, and ultimately, depleted funds. Luckily, Coinbase has a way to safeguard your cryptocurrency savings to not only protect them against thieves, but to also help you resist the urge to sell off your investments.

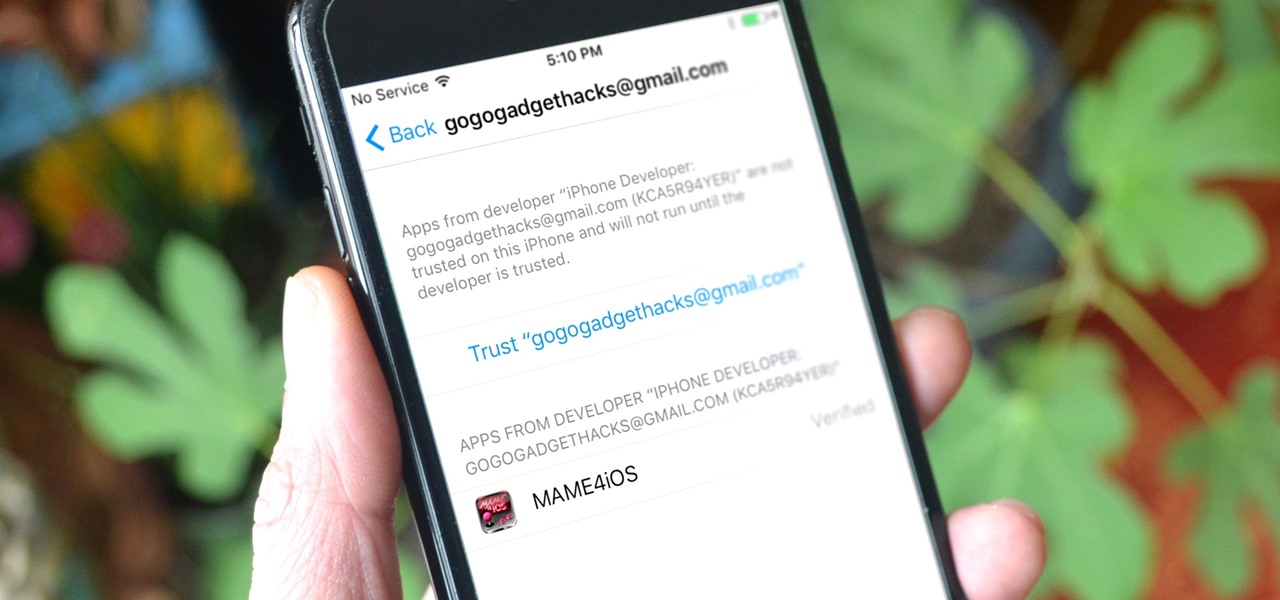
Jailbreaking gives iPhone users almost unfettered access to their devices, offering a slew of customizations, new features, and improved apps that you just can't get elsewise. Unfortunately, Apple has clamped down hard on the latest iterations of iOS, making jailbreaking extremely unstable at best. Hope is not lost, however, as there's still a way to install modded and unofficial apps on your iPhone, iPad, or iPod touch without any jailbreak.

Welcome to a tutorial explaining functions. This article will help clarify some things we have already been exposed to such as function prototypes, function calls, return values, etc.

Yes, screen savers are fun to look at for a few seconds, but those animations actually used to serve a purpose beyond simple entertainment.