When performing something such as a mass mailer attack on a company, sending executables usually isn't the best option. That's why, in this tutorial, I'll be teaching you how to code a VBA script macro into a Word document in order to compromise a system. Combined with a little social engineering, this can be a very effective technique.

A lot of people think that TOR services are unhackable because they are on a "secure environment", but the truth is that those services are exactly the same that run on any normal server, and can be hacked with the same tools (metasploit,hydra,sqlmap...), the only thing you have to do is launch a transparent proxy that pass all your packets through the TOR network to the hidden service.

welcome back my masters , teachers and classmates , in this second part of this 0-day series we will learn the basic of fuzzing, and i bought some gift for nullbyte(a 0 day vuln that will be released today exclusively on null-byte) .

Welcome back, my novice hackers! Previously in my "Spy on Anyone" series, we used our hacking skills to turn a target's computer system into a bug to record conversations and found and downloaded confidential documents on someone's computer. In this tutorial, I will show you how to spy on somebody's Internet traffic.

Crochet Weave with Xpression Hair takes some proper care. It is just like having your hair relaxed; the hair is that texture.

Welcome back, my neophyte hackers! In previous tutorials, we learned how to steal system tokens that we could use to access resources, how to use hashdump to pull password hashes from a local system, and how to grab password hashes from a local system and crack them.

While honey is one of the most popular ingredients on kitchen shelves the world over, honeybee pollen is still a relatively rare find in most households. It's not hard to guess why: eating pollen just sounds weird... it would probably sell a lot better if it had a more appetizing name, like honey. Furthermore, it looks unlike any other common ingredient, and the smell can be off-putting to some. But it's good, it's healthy, and it's altogether pretty awesome!

Hi Elite Hackers! Welcome! to my 4th post. This tutorial will explain, how to extend a (hacked) AP's range with a wireless adapter. I made this guide because after hacking an AP it was difficult to connect to it (poor connection) and further exploit it. You can also use this:

In today's world of ordering food from your PC or hailing a cab with an app, it almost seems archaic when we have to actually use our vocal cords to contact a local business. It sure would be nice if we didn't have to use our smartphones as, well, you know...phones.

Video: . How to Make My Famous Spaghetti.

Welcome back, my budding hackers! When we are looking for ways to hack a system, we need a specific exploit to take advantage of a certain vulnerability in the operating system, service, or application. Although I have shown you multiple ways to exploit systems here in Null Byte, there are still many more exploits available that I have not yet shown you.

If you've seen ParaNorman or Fantastic Mr. Fox, then you have some kind of idea of what stop-motion animation is. Basically, these artists make objects, or small figures, appear to be moving on their own by manipulating and repositioning them in the smallest increments, then capturing each frame after doing so. When all the frames are compiled together, the final product is something spectacular like The Nightmare Before Christmas, which took roughly 109,440 frames in all.

Assuming that you're not going to knit a sweater and celebrate New Year's Eve with Ryan Seacrest and Jenny McCarthy on ABC's “New Year's Rockin' Eve," it's a pretty safe bet to say that you're probably going to consume alcohol—a considerable amount of alcohol.

Every Windows system includes command prompt; and while a lot of people on Null Byte and WonderHowTo in general know how to use it, some people don't know anything about it, even how to access it.

If you haven't walked into a department store or seen one of those millions of jewelry commercials airing over the last month, you might not know that February 14th is Valentine's Day.

All of my hacks up to this point have been operating system hacks. In other words, we have exploited a vulnerability usually in an operating system service (SMB, RPC, etc.) that all allow us to install a command shell or other code in the target system.

In general, hacking and information security is not just one discipline, but a number of them, and today we will look into some of the networking concepts.

Have an opinion and want the whole world to know it? You're not alone! There are many online outlets for you to type up your review, whether it be for a restaurant, play, movie, book or anything else you have recently experienced. Check out this video for tips on how and where to post your exciting review.

Privacy is important. Whether its a telemarketer or a crazy ex, sometimes you may need to block someone from contacting you. With this tutorial, learn how to get rid of those pesky callers.

Giardia -- ever hear of it? Probably not, but you'd more than likely be surprised to know that it is the most common nonbacterial cause of diarrhea in the United States. Learn how to care for your pet with help from VetVid. See how to prevent and treat giardia in pets with this video tutorial.

When we think of the flu, we think of sick people, but the little guys always get looked over… dogs. Learn how to care for your pet with help from VetVid. See how to diagnose and treat canine influenza (CIV) in dogs with this video tutorial.

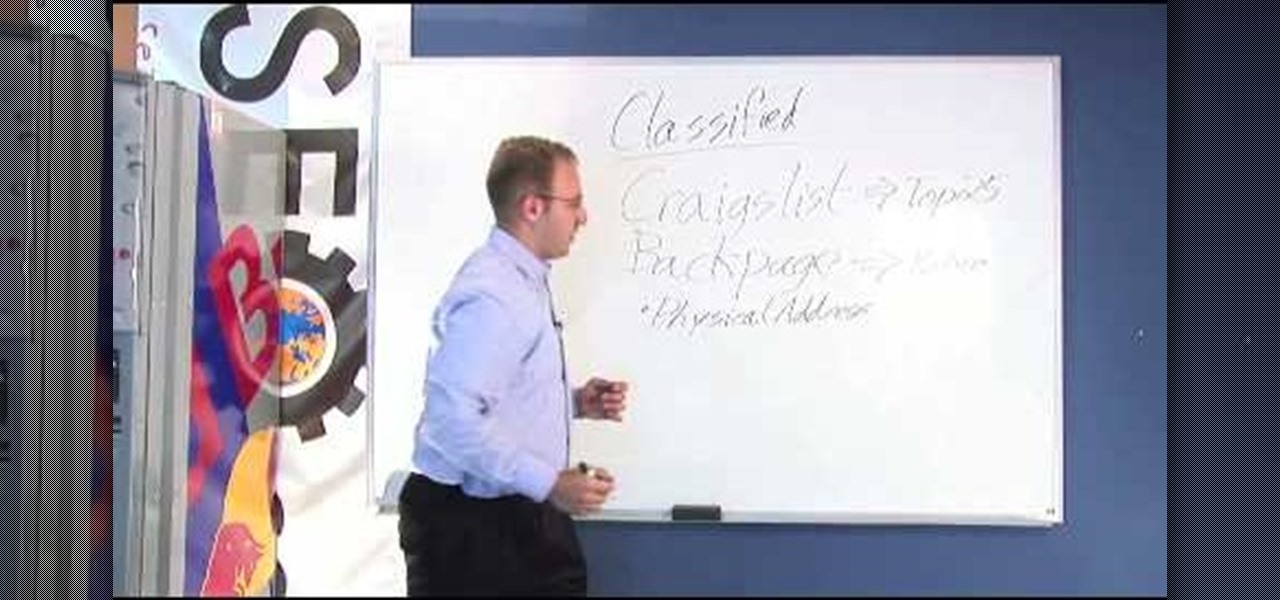
There're plenty of great ways to get traffic, especially this off-site optimization technique using classified ads to point website traffic back into your site itself.

Still got stock? Many factory installed exhaust systems not only sound anemic, they actually are because they scrub power. The designers who are given the task of producing these pipes are often handcuffed by several different requirements that add up to one big compromise. Exhaust engineers are required to build systems that are quiet and that meet certain types of emission standards, but not all of the design concerns are driven by government regulations. Some are based on a perception of w...

The world of CES, the annual technology conference in Las Vegas, usually brings a few surprises, but few expected Samsung to fire off its first real augmented reality salvo at the event.

With big-name tech companies like Apple and Facebook gearing up to push out their own smartglasses in the coming years, engineering conglomerate Bosch has been working on the optical components that could help the competition catch up.

After drawing attention from nostalgic Gen Xers for its Motorola Razr reboot with a foldable screen, Lenovo has a new augmented reality smartglasses concept that the company hopes will also turn some heads.

While the tech industry is hot in pursuit of mainstream smartglasses for consumers, another early maker of enterprise-focused AR hardware has apparently met its end.

In recent days we've covered the marriage of augmented reality and top-tier music artists. This time, though, the music stars are showing off the tech rather than integrating it into their act.

While Modiface, YouCam, and others have been playing in the virtual make-up marketing pool for a while, here comes Google ready to splash down with a cannonball.

Under the rocket's red glare and the bombs bursting in air, the Statue of Liberty is swaying in celebration this Fourth of July thanks to Snapchat.

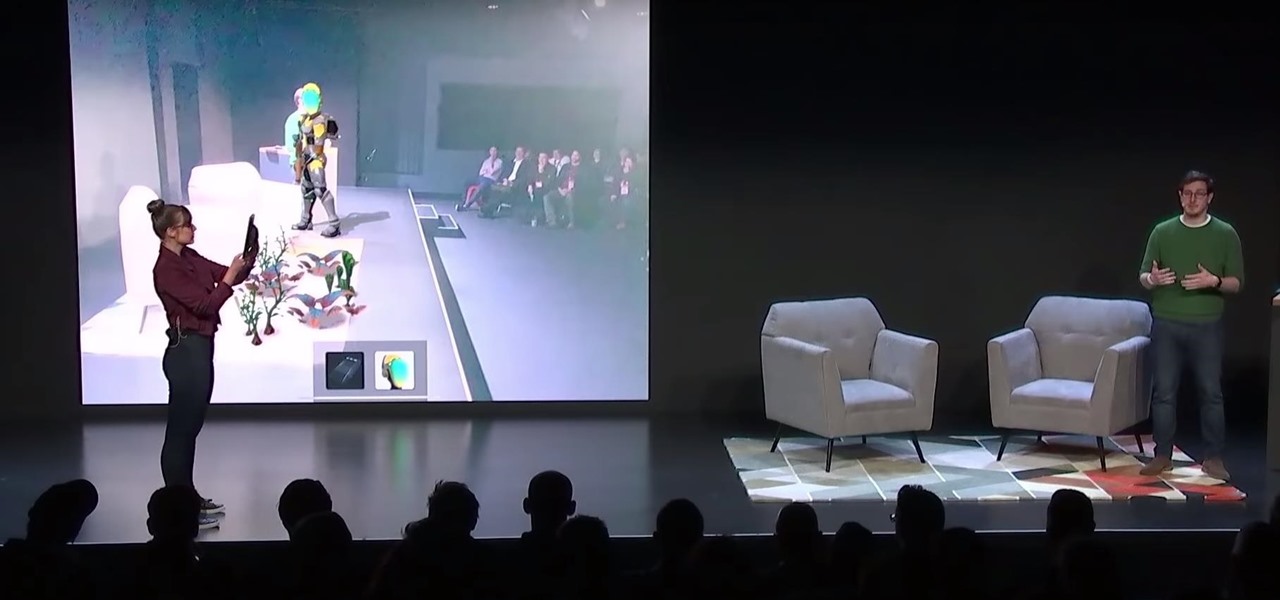
After Apple unveiled ARKit 3 at WWDC on Monday, Unity Technologies wasted little time on ensuring its developers can take advantage of it.

Many tech insiders are waiting for augmented reality to go mainstream, but if you look around hard enough, you'll find that it's already gone as mainstream as possible, thanks to talk show host Ellen Degeneres.

Don't look now, but stock photo mega-site Shutterstock may have the most extensive library of augmented reality content available.

Every year, fans of Irish culture, as well as those looking to celebrate their own culture, come together on St. Patrick's Day, March 17.

While the betting lines on iPhones with depth-sensing, rear-facing cameras in 2019 have already been established, a new report adds some certainty to the notion that the iPhone will get new AR superpowers later this year.

When wearables startup North officially unveiled its Focals smartglasses in October, the stylish frames strongly resembled, in form and function, Intel's canceled Vaunt smartglasses.

Applicants looking to attend Magic Leap's first annual L.E.A.P. conference next month in Los Angeles have begun receiving their confirmation invitations, and now we have more detail about some of what will happen at the event.

Despite the popularity of Pokémon GO, augmented reality gaming hasn't quite caught on yet. The makers of the popular World of Tanks game aren't taking a shot at Niantic's crown yet, but they are looking at giving spectators a new way to watch the game.

To promote Battle of Azeroth, the latest expansion for the World of Warcraft franchise, Blizzard Entertainment has conjured a Shoppable AR Lens that is now available in Snapchat's app carousel.

With the official launch of Magic Leap One expected by the end of summer (translation: days from now), Magic Leap's hype machine just took a big hit with the sudden loss of a key marketing executive.