Chances are, you just point, shoot, and share photos and videos on your iPhone without a second thought about how your privacy is affected. It's fairly easy to do so since the Camera and Photos apps that Apple provides seem so innocent. But there are a few things you need to know when it comes to shooting media, sharing it, and even deleting it.

Whether inappropriate or unimportant, some emails don't need to be viewed at a certain times of the day. For example, you might not want to see any personal emails during work hours. By default, Gmail will notify you of all emails that hit your inbox, but fortunately, there's a feature that can automatically hide certain emails and prevent distracting notifications.
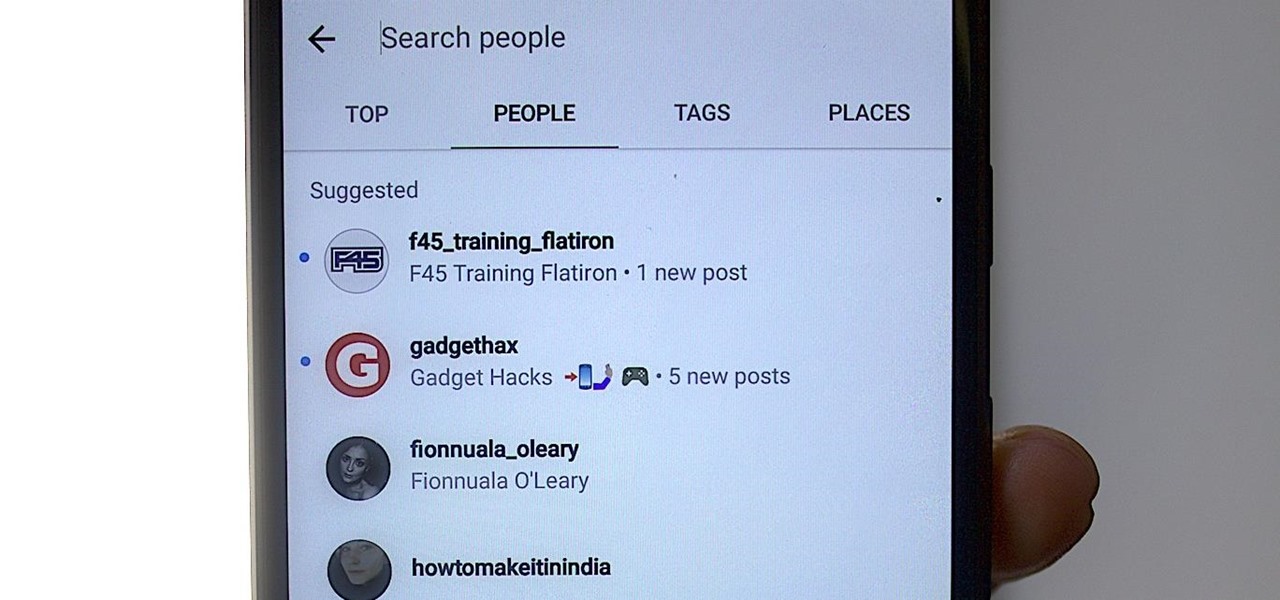
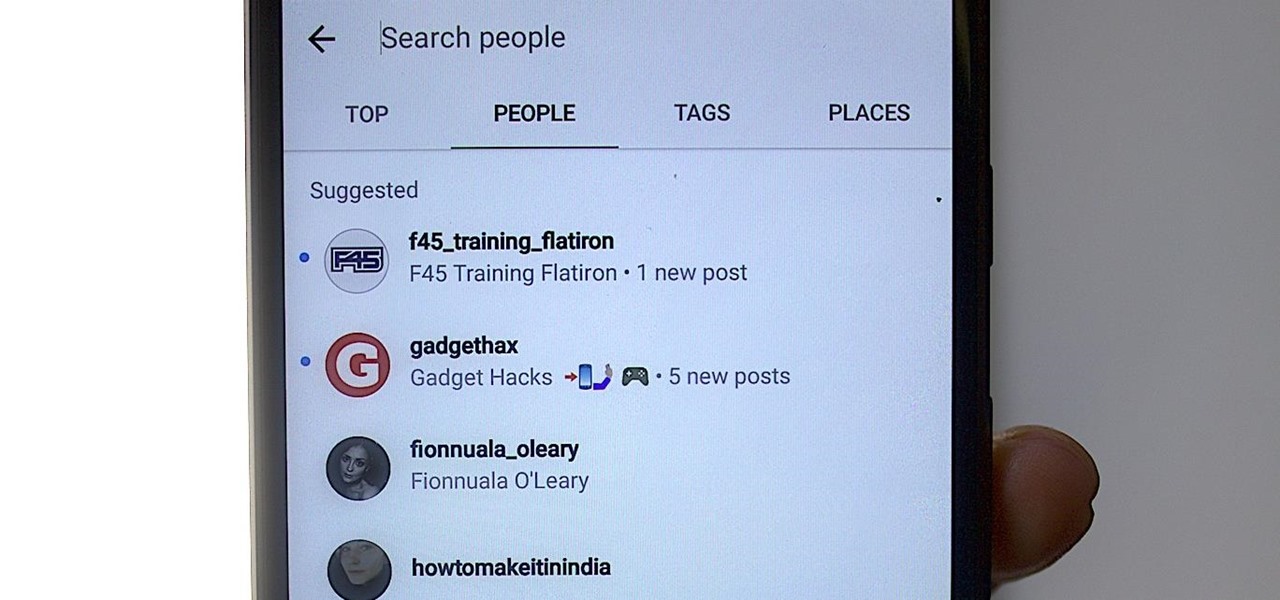
I thought eventually that my ex's Instagram account would magically clear from my "Suggested" search history. It's been six months now, and I'm sorry, babe, but enough is enough. It's time to clear out your very cute face. (On Instagram, of course.)
The first public beta of Android O, (most likely to be called "Android 8.0 Oreo") was released on May 17, bringing tons of new features and goodies for Android enthusiasts with supported devices. However, not all of Android O's features were available to try out right off the bat. Possibly the single biggest feature announced during the developer preview of Android O, Picture-in-Picture mode, is nowhere to be seen.
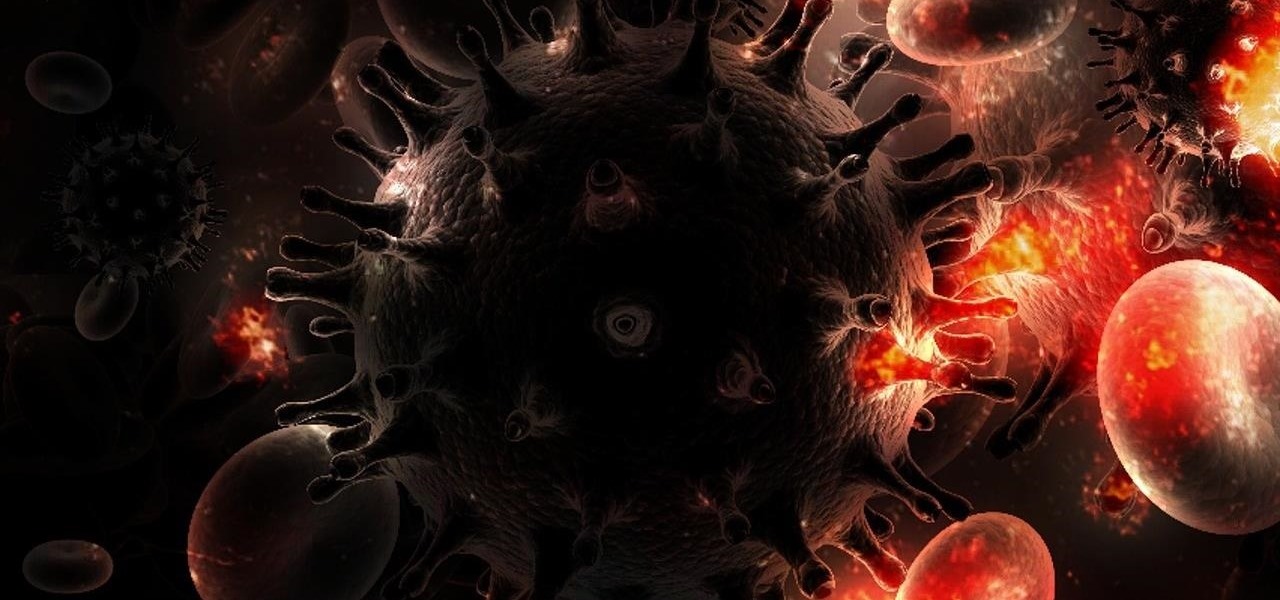
Over 1.2 million people in the US are infected with human immunodeficiency virus (HIV)—and one out of eight of them don't know it. Even after decades of intense research into the virus, there's still no cure for it. One of the big problems is that the virus hides out in certain cells of the body, resisting treatments that kill it.

Welcome back, my hacker novitiates! Often, to hack a website, we need to connect to and exploit a particular object within said website. It might be an admin panel or a subdirectory that is vulnerable to attack. The key, of course, is to find these objects, as they may be hidden.

Apple took great strides to enhance Accessibility features on iOS 7 for low-vision users, adding button shapes, dark colors, bold keyboard text, and more. With iOS 8, Apple looks to continue their run at making life easier for the optically impaired.

Sense 6 is great, don't get me wrong, but sometimes I start to miss the vanilla Android experience that comes with Nexus devices. You can always convert your M8 to the Google Play Edition, but then you'd have to ditch all the Sense exclusive features, and we wouldn't want that.

Samsung's TouchWiz skin gets a lot of flak for its appearance, namely the garish colors on the quick settings toggles. The bright green on dark blue scheme is definitely an eyesore compared to the ones in stock Android, and even other manufacturer skins like HTC's Sense.

No matter how careful or decent you are, there will always be pictures or videos that you want to keep private. They say a picture is worth a thousand words, but if someone were to go through my photo gallery, only one word would be coming out of my mouth—"%@&#!!"

Whether it's because you want to make a quick tutorial video or want to show off your gameplay skills, recording the screen your Nexus 7 tablet isn't an easy feat. At least, until now. Hidden inside Android 4.4 KitKat is a built-in screen capturing feature, but it takes a little effort to dig it out.

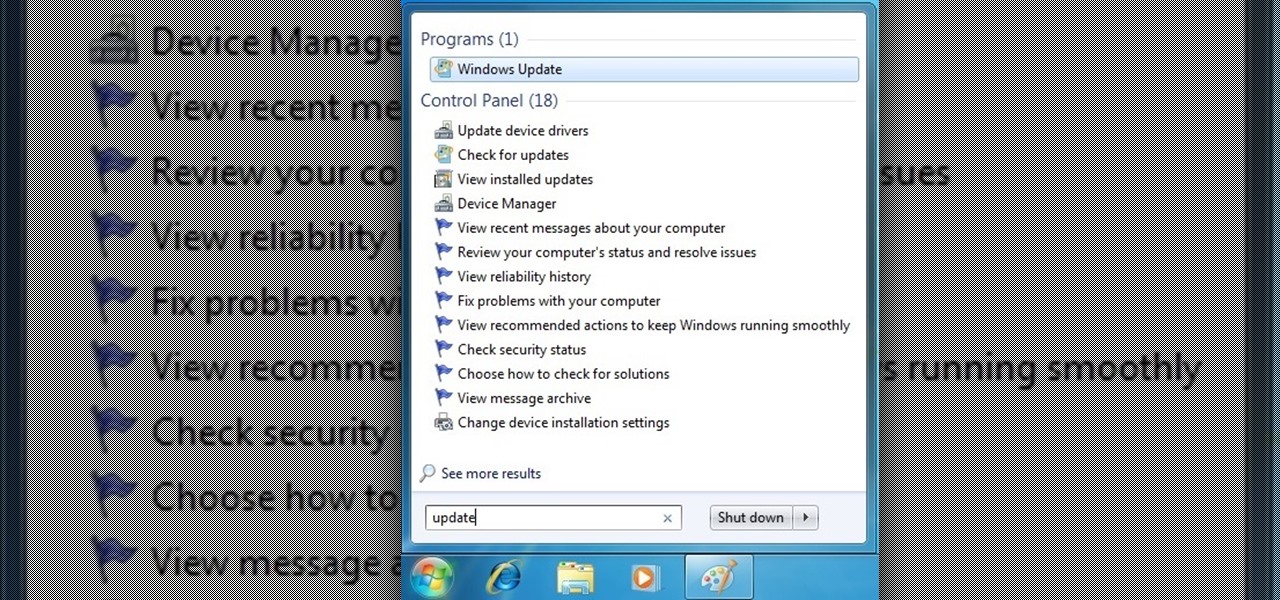
From a fresh home install of Windows 7 (not factory install) this will guide you step by step to updating your Windows 7 and getting it up and running.

There's a lot of cool features rumored to be included in next year's HTC One 2 (M8), the follow up to the flagship HTC One smartphone, including a fingerprint scanner, Android 4.4 KitKat, and Sense 6.0, but it's just too far away to get really excited about yet.

I can definitely say that my MacBook is one of my best friends, but I was still very disappointed when I realized that the only game my laptop came with was chess. For starters, I'm not very good at chess. I haven't even beat the computer once, which really grinds my gears. But, it has come to my attention that chess isn't the only pre-installed game on my Mac—there seems to be some hidden gems that I simply wasn't cool enough to know about. For some of you, this may be old news, but for me, ...

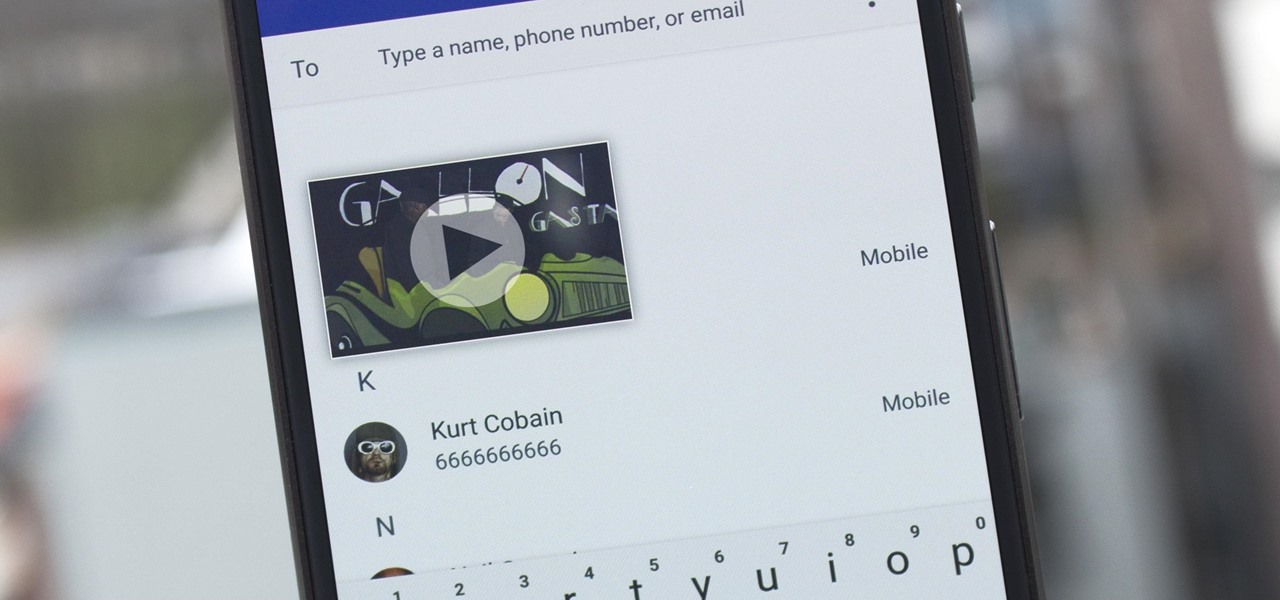
If you want to send someone secret messages you have come to the right place. This is a way in which you can send secret messages to anyone without even making them get a clue that you have sent a secret message.

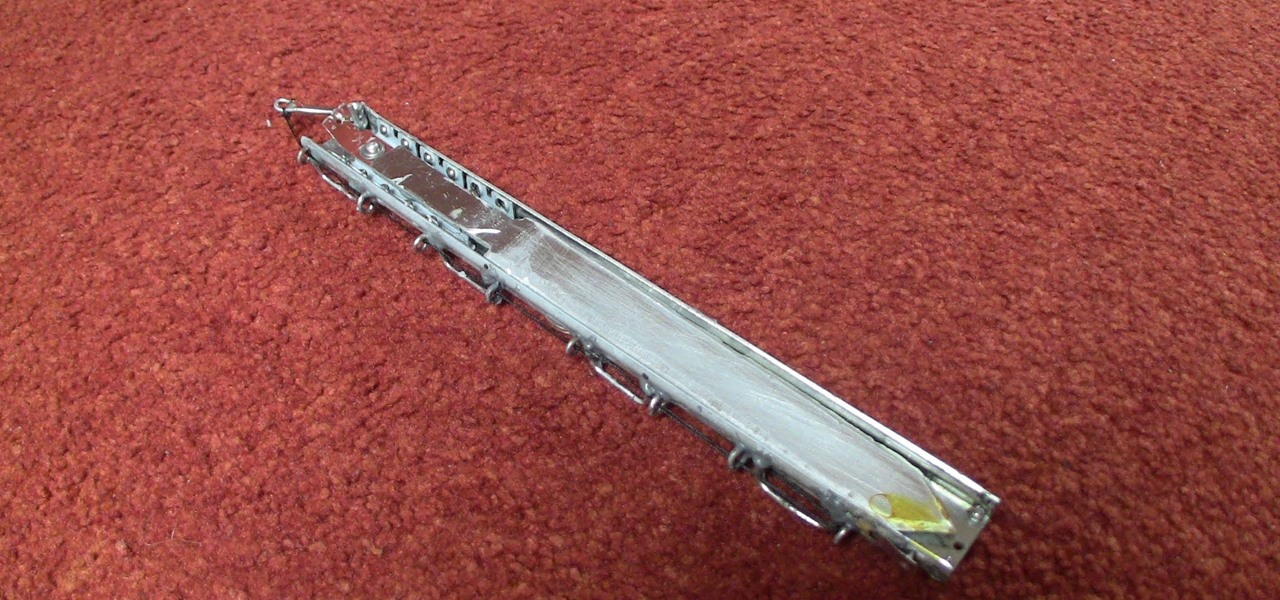
The hidden blade that Altair uses to murder his victims in Assassin's Creed is a great costume piece, and if you don't mind working with metal then you should be able to use the instructions in this video to make a really cool one.

Knowing all the information about your car is important for many reasons. Some being for the fact that the government needs it and another being it can help with trying to find parts for the car. So in this very helpful tutorial, you'll find out how to locate the VIN ID numbers on a classic VW Beetle Bug. It's easy to follow and will make life easier for you. So good luck and enjoy!

This photoshop tutorial demonstrated by Howard from tutcast.com, teaches you how to do amazing glow effects for your work and projects. Everything you need to know from the background you choose to use to editing out the leftovers. You can use any image that you choose to. Start out with the pen tool located on the toolbar on the most left of the screen. Create the initial layer for the glow by clicking now on the new layer icon located on the bottom right. Next, define brush by pressing the ...

What if I told you that you could read minds? You'd most likely think I was crazy, and you'd be right. But what I really meant is that you could make people think that you could read minds, something that's not the least bit crazy.

Watch this video tutorial to learn how to calculate your carbon footprint. A carbon footprint is an equation that estimates just how much you, personally, are contributing to global warming—and all you have to do is plug some info into an online calculator. Figuring out how to make your footprint smaller, of course, is another matter.

Stop guessing if you need to take your RV into a service center, answers are here in this tutorial video. Learn how to maintain the water heater on your RV.

Have you ever accidentally dismissed an important notification? Realized you didn't mean to delete an alert after hitting "Clear all?" Instead of pulling out your hair, know you can see the alert again — at least, a portion of it.

Post-exploitation is often not quite as exciting as popping the initial shell, but it's a crucial phase for gathering data and further privilege escalation. Once a target is compromised, there's a lot of information to find and sift through. Luckily, there are tools available that can make the process easy. One such tool is Postenum.

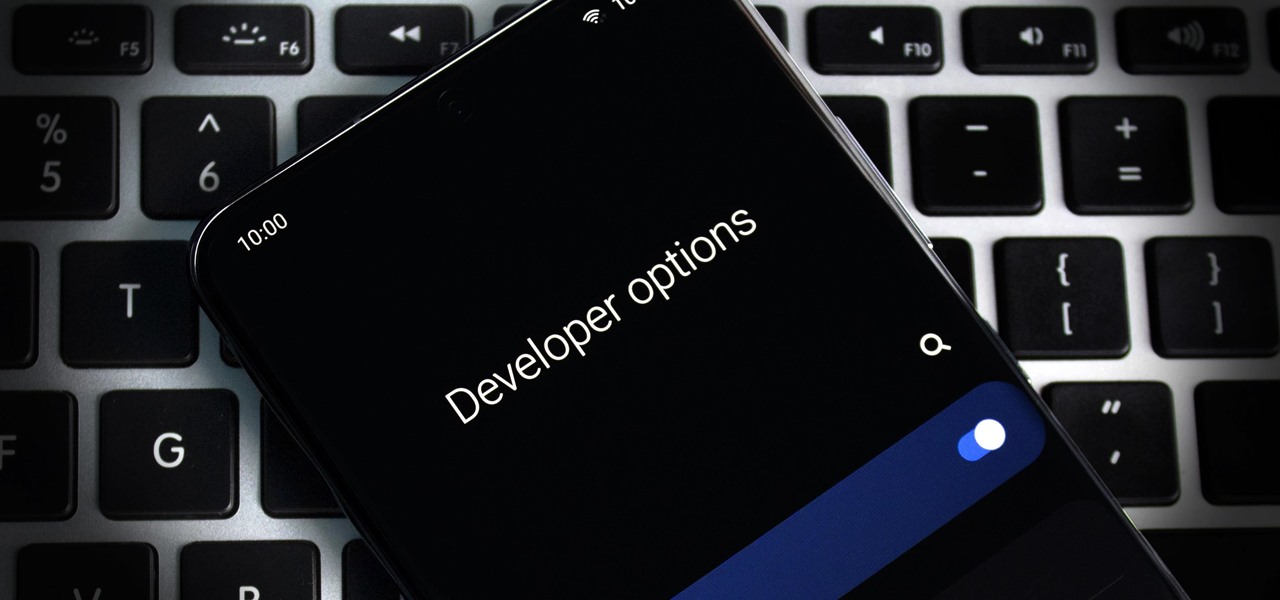
The first thing any Android power user does with their phone is unlocked the Developer options. The hidden menu has many low-level tweaks, such as forcing Dark mode on all apps, speeding up animations, or enabling hidden Quick Setting tiles. And most modifications require nothing more than hitting a toggle.

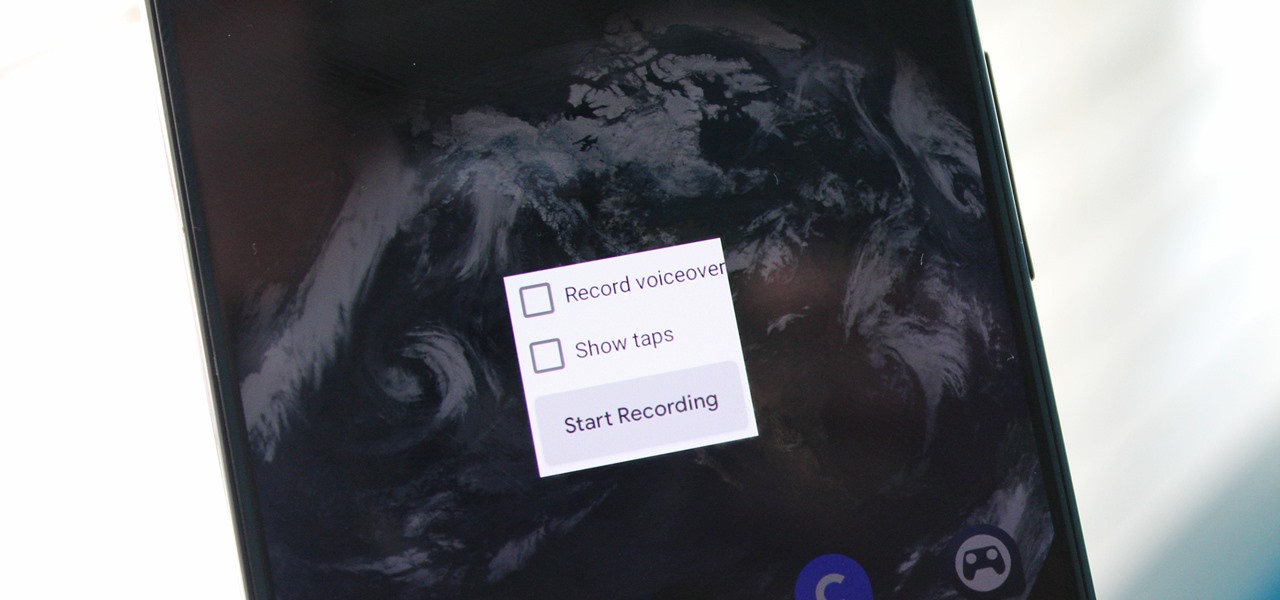
Downloading third-party screen recording apps can be dangerous. The primary function of these apps is being able to record everything on one's display, so it's easy to see how a malicious developer could exploit this for their own gain. That's why the addition of Android 10's built-in screen recording is so impactful.

One of the first steps when pentesting a website should be scanning for hidden directories. It is essential for finding valuable information or potential attack vectors that might otherwise be unseen on the public-facing site. There are many tools out there that will perform the brute-forcing process, but not all are created equally.

Apart from the flashlight, camera, and apps you access via notifications, widgets, location-based alerts, and the Control Center, there's no way to open other apps straight from the lock screen that you use frequently. If you have a jailbroken device, however, you can remedy this and add the home screen's Dock to the lock screen to get into your go-to apps even quicker.

From the first moments of booting up Harry Potter: Wizards Unite to the hours of walking you're bound to experience, one thing is clear — encountering Foundables and defeating their Confoundables is a significant plot point of the AR game. While you receive rewards each time you retrieve a Foundable, the real treasure comes from completing parts of the Registry, called "Families."

The next libSSH or OpenSSH exploit may be just around the corner. Keep your SSH service out of Shodan's database before hackers find new ways to bypass the password protecting the server.

Websites are often misconfigured in ways that allow an attacker to view directories that are not ordinarily meant to be seen. These directories can contain sensitive information such as private credentials or configuration files that can be used to devise an attack against the server. With a tool called Websploit, hackers can scan targets for these hidden directories without difficulty.

Your iPhone is just that — yours. Why should your home screen look like everyone else's? While iOS, and by extension, Apple, famously locks its users into its way of doing things, there's a lot more room for customization than you'd think. Before you make the switch to Android, you might want to see what you can do with the iPhone you already have.

It's important to know who you're dealing with after hacking your target's MacBook. Getting remote access is simple, but covertly gathering information about the user and their system can be a challenge.

Once a hacker has created a PowerShell payload to evade antivirus software and set up msfconsole on their attack system, they can then move onto disguising their executable to make it appear as a regular text file. This is how they will get a Windows 10 users to actually open the payload without knowing they are doing so.

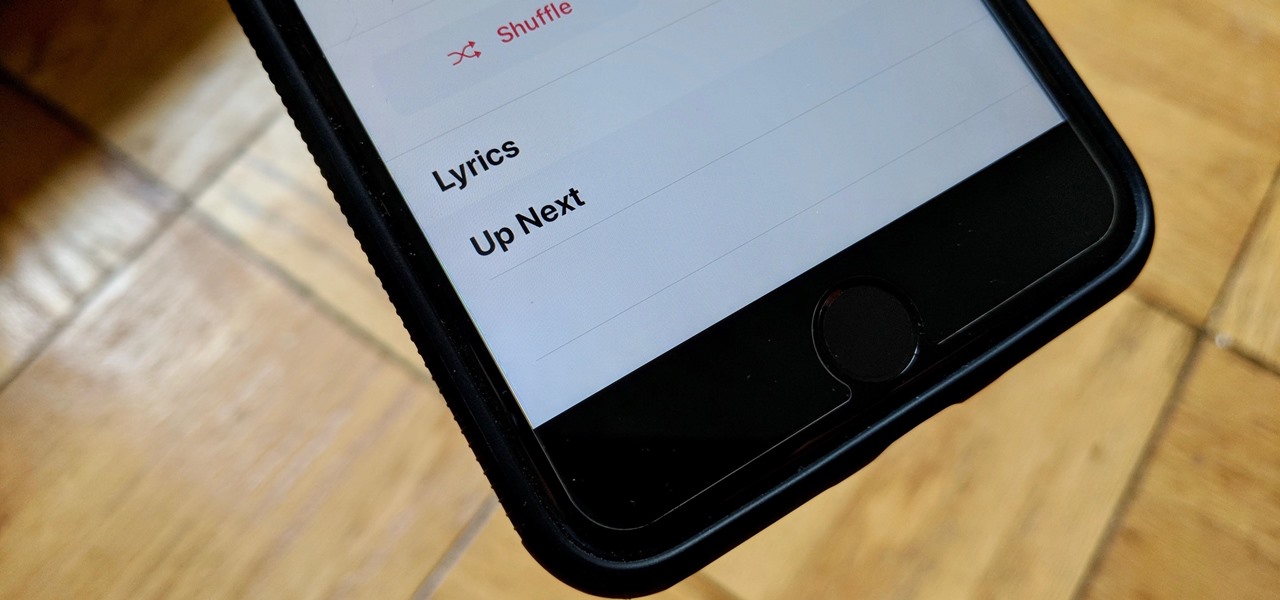
The "Up Next" feature in Apple Music helps you control which songs you want to listen in the order that you want. However, this list can become messy fast, quickly becoming a collection of songs you never wanted to listen to in the first place. Luckily, Apple has built a way for you to clear Up Next, it's just not very obvious.

Magic Leap loves to stoke mystery around its still unreleased product, the Magic Leap One: Creator Edition, and now we've found yet another piece of the puzzle in the form of an Easter egg on the company's website.

Nova Launcher is one of the most popular apps on the Play Store thanks to its rich features and fluid navigation. But one downside that comes with this abundance of features is that much of Nova's functionality is lost on the masses. Fortunately, I've used Nova for several years and learned a few tricks along the way.

As smartphone users, we live in dangerous times. The value of phones continues to rise, making them prime targets for thieves. In 2015, the FCC estimated that one million phones are stolen each year, and with several devices starting to hit the $1,000 mark now, these numbers are sure to rise. But what do you do if you fall victim to phone theft?

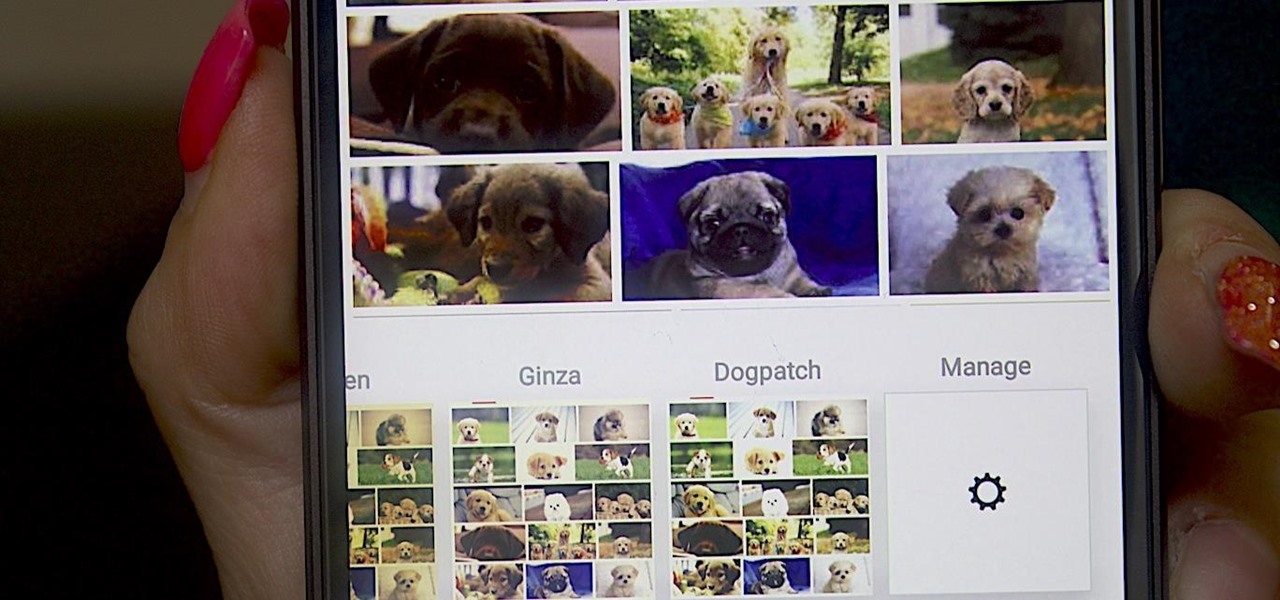
I've possibly been really out of it for a long time not to have realized that Instagram has a bunch of hidden filters. Clarendon seems to be by number one filter for pics and videos, but maybe that's exactly what I've been doing wrong.

While Leap Motion and Microsoft are looking to capture natural human motion with cameras, Enflux figured out how to do it with a shirt and pants that feel completely natural.

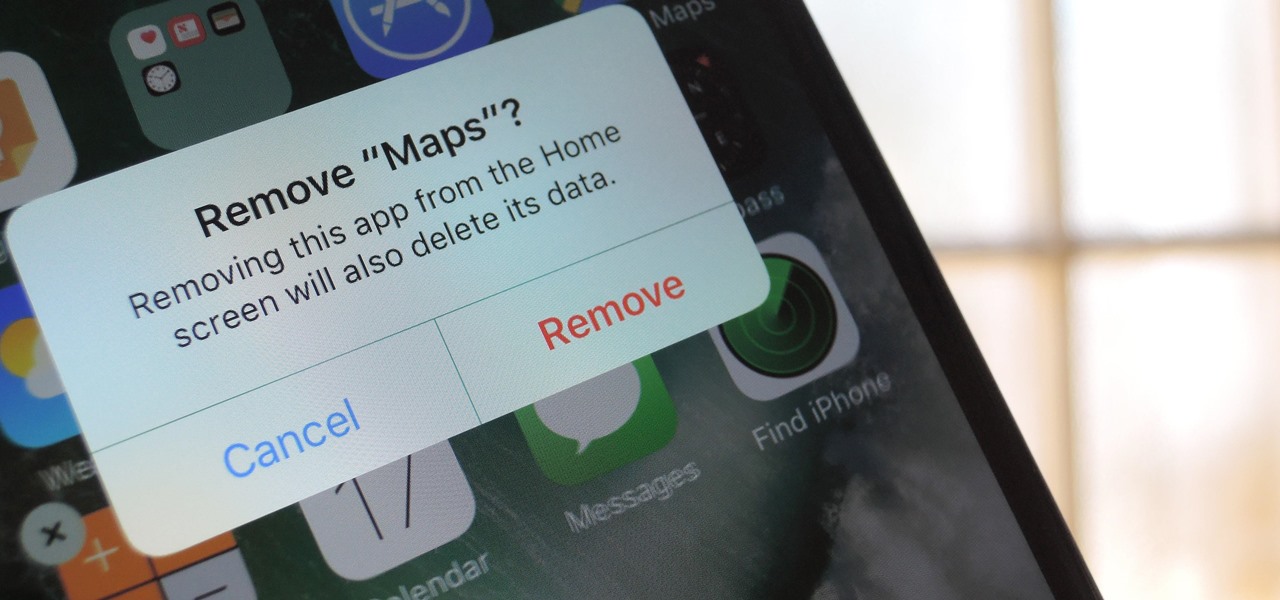
One of the best new features in iOS 10 is the ability to delete all of those stock bloatware apps that you never use. Instead of hiding them in a folder somewhere to get them out of your way, you can finally remove them—or at least, that's what we wanted to believe.