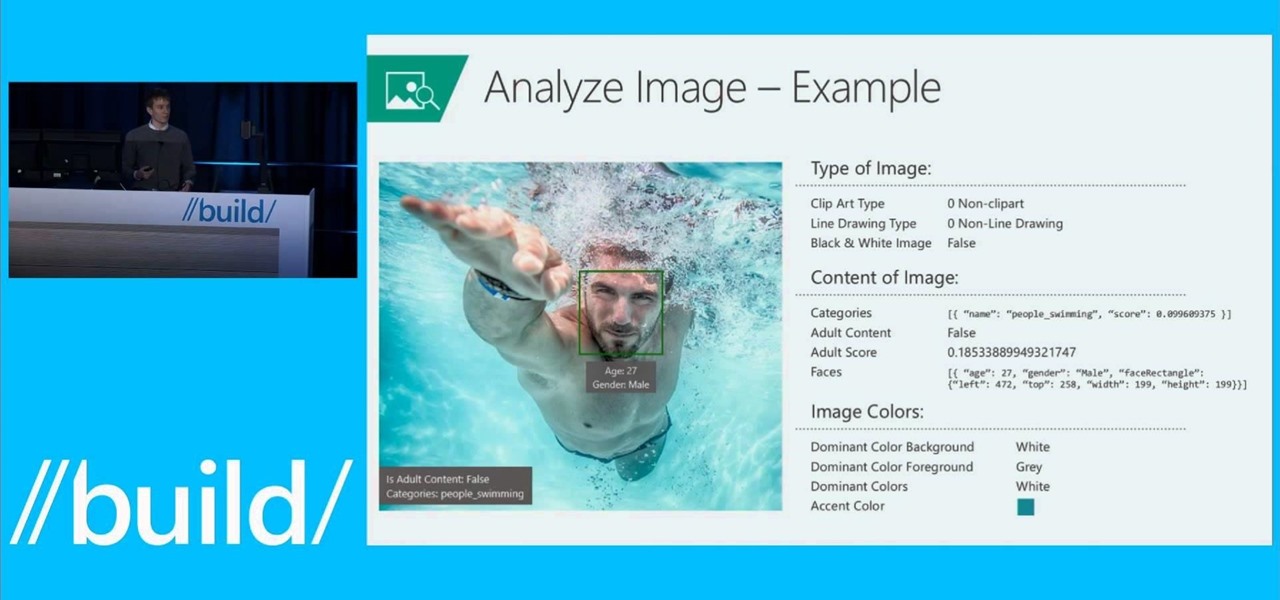
News: Microsoft Project "Oxford"
Microsoft is developing a new API project called poject "Oxford," and it includes face, speech, and more "smart" API technology. Despite being Microsoft, I actually found this to be very useful. ;)

Microsoft is developing a new API project called poject "Oxford," and it includes face, speech, and more "smart" API technology. Despite being Microsoft, I actually found this to be very useful. ;)
Hi all, Pro Hackers/Crackers, Let's see how we can use batch for our own Protection instead of exploiting someone with it.

The Galaxy S6 might just be the best Android phone on the market right now. From a hardware standpoint, Samsung truly knocked this one out of the park with its finely-crafted build quality and amazing screen.

Many Android utilities use Android Debug Bridge, or ADB for short, to send commands from a computer over to your phone or tablet. This enables such utilities to run terminal commands that, in some cases, wouldn't be possible on Android without root access.
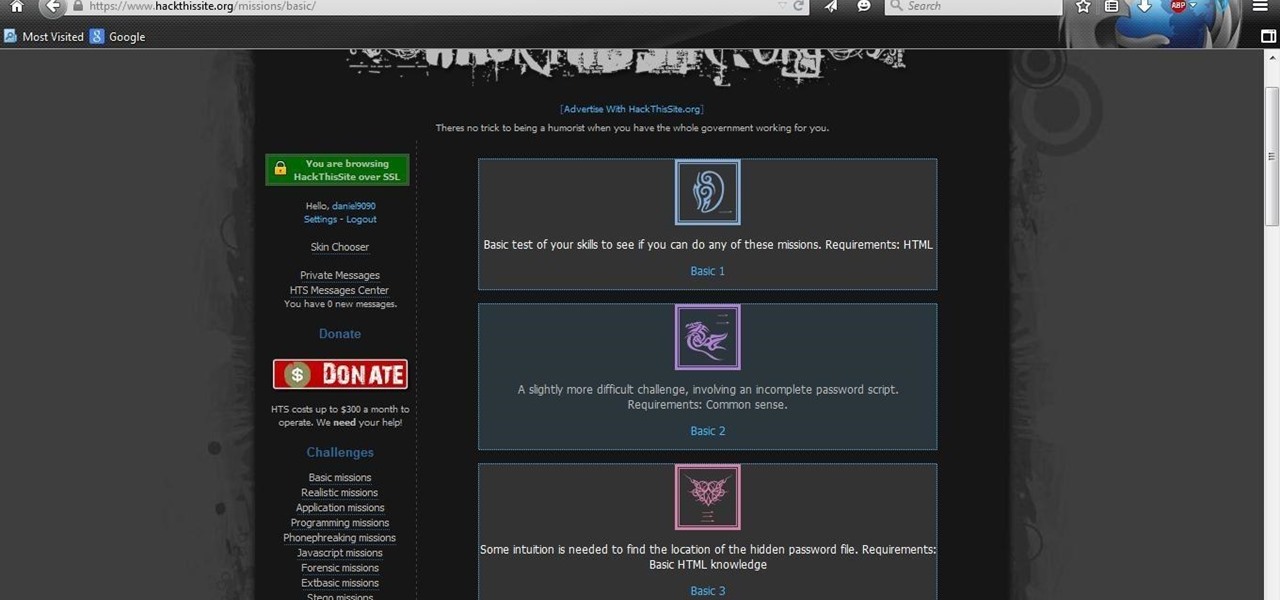
After you have registered to this site,sign in then to start missions. Basic Missions

Many of Google's stock Android apps are some of the best options out there—especially now that they've all been made over with Material Design. But generally, as these are pre-installed system apps, they cannot be used on non-Nexus devices.

Smartphone users often wish for a privacy, where no one is able to poke his/her nose in their personal stuff. Unfortunately, none of the smartphones have been able to guard their privacy in this fashion. Smartphones usually come up with none or almost negligible built-in security to serve your purpose.

Due to their large size and added screen real estate, Apple included a new feature for the iPhone 6 and 6 Plus known as "Reachability." Essentially, this function makes reaching the top part of the display easier by double-tapping the home key to shift the screen down closer to your thumb.
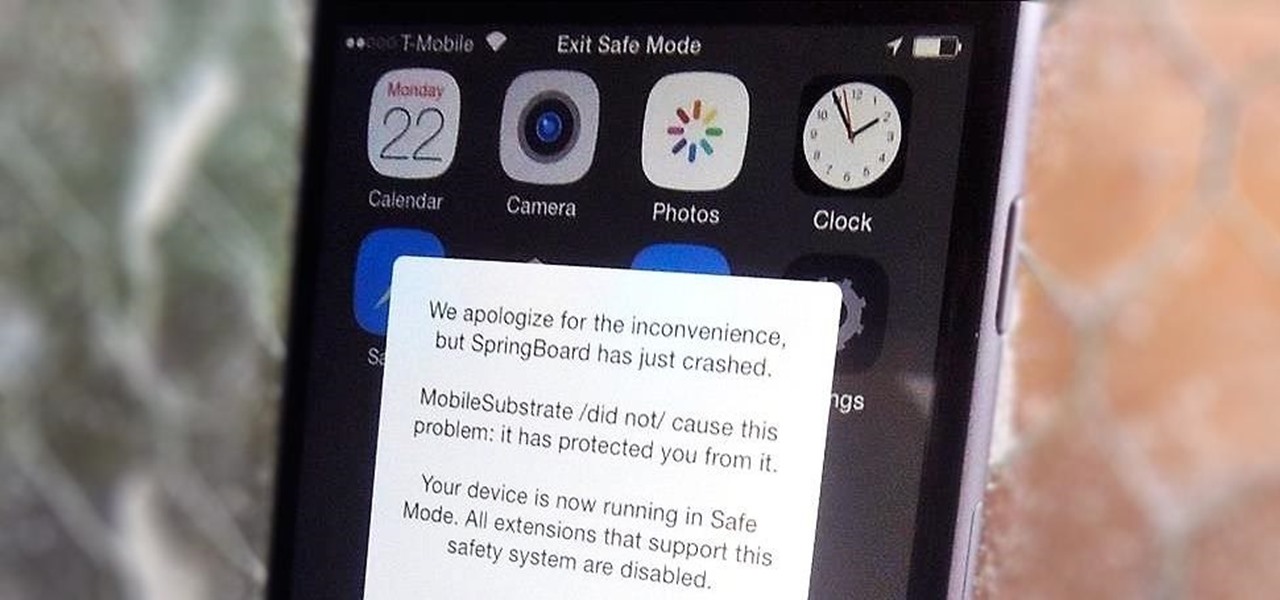
Installing tweaks or themes onto your jailbroken iOS device is a pretty fun and exciting experience, but if you do it for long enough, you're bound to come across a bug that will cause your operating system to crash.

iCloud Drive is Apple's new solution to file management syncing across iOS and Mac OS X. If you've upgraded to iOS 8 and you have an iCloud account, you can use iCloud Drive to store files for certain apps. While you won't really be able to benefit with file syncing between iOS and Mac apps until you get Yosemite, you can still access your iCloud Drive documents online.

More and more devices are using iOS 8 over iOS 7, and that means more and more developers are adding iOS 8-friendly features to their apps, especially widgets. However, not every widget available for your Notification Center right now is awesome. Take for example the Dropbox widget—it's essentially nothing more than a real-time notification, as the only action it performs is opening a recently updated file within the app.

Accessing your favorite and most recent contacts on your iPhone is now faster than ever before, thanks to the iOS 8 update. Just double-click your Home button, select your contact above the app switcher menu, then choose how you want to contact them.

As soon as third-party keyboard compatibility was announced for iOS 8, Apple loyalists and the newly curious both looked to the popular Android third-party keyboard developer, SwiftKey, to see if they'd be offering their services to iOS.

iPad, iPhone, and iPod touch owners: it's that time again. iOS 8 has been released to the public, and those who have been eager to update since Apple's WWDC announcement won't have to wait any longer. Since iOS 8 promises to pack a bunch of new, really great features, it's time to present your options for getting on the latest and greatest for your Apple device.

We live in a time where privacy is rare and our files can be easily accessed by just about anyone. Having your phone protected by a passcode is great, but if someone figures it out, they can easily access anything on your phone.
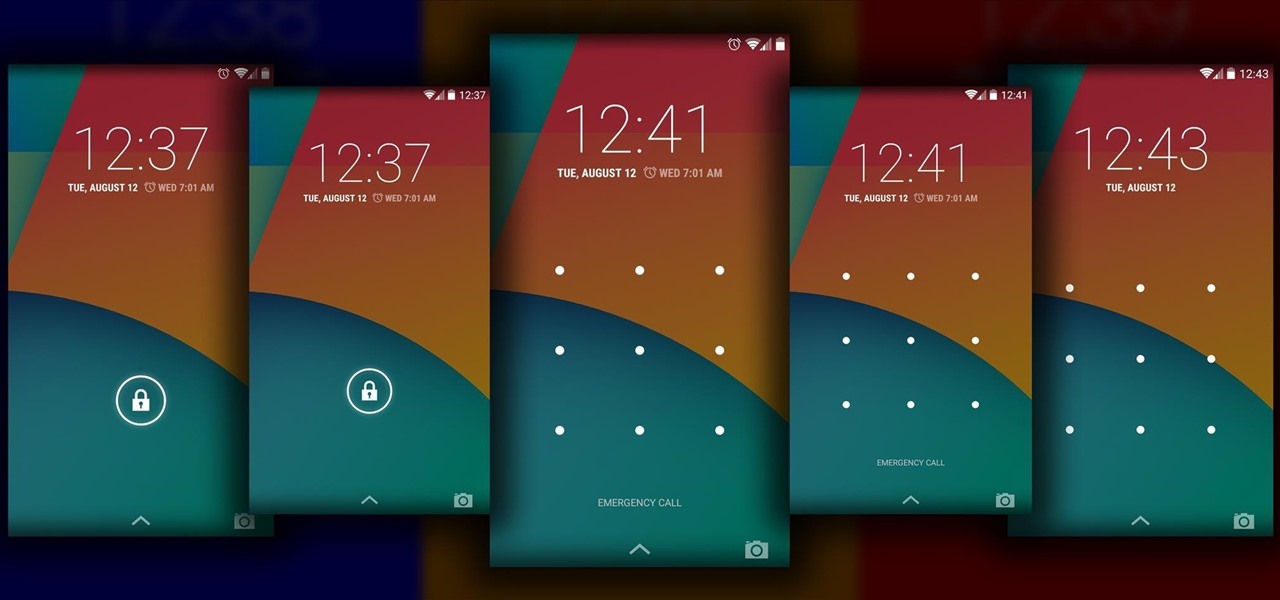
The Android lock screen interface is an integral part of our everyday use. For those of us who use lock screen security, it functions as a barrier between the sensitive data contained within our smartphones and potential outside access. Even if you don't use a pattern or PIN to secure your phone, you still interact with the lock screen every time you go to use it.
Back in the day when computers relied on CRT monitors, having a static image displayed for too long actually resulted in the image being burned into the screen. For this reason, screensavers were developed, which display animated images in constant motion to prevent burning in when you stepped away from your computer.

The weather widget on the main home screen of a fresh-out-of-the-box Galaxy S5 is meant to show off the screen. Super-high contrast and crisp definition on the individual blades of grass in the background let you know that the phone you're holding has one helluva display.

Humans in general are great at keeping things about themselves private, from feelings to personality traits. While smartphones and social networks are making these secrets more open, narcissists have and always will love being out in the open with everyone's attention on them.
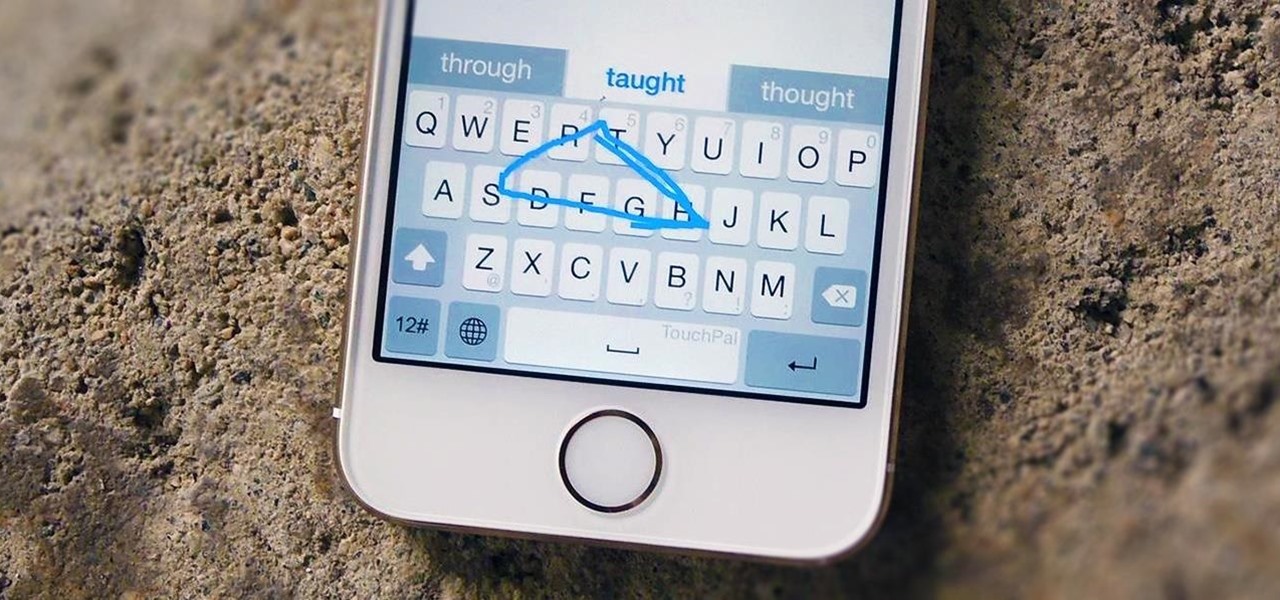
Rather than just use the stock Apple keyboard, iOS 8 now lets you use keyboards from TouchPal, Fleksy, SwiftKey, Swype, and more. I'll be showing you how to set up a third-party keyboard on your iPad, iPhone, or iPod touch, as well as giving you a firsthand look at TouchPal's keyboard for iOS 8.
Still working on mega project builds. This one is going into my own PVP server which (will) contain 4 theme'd biomes inside of a 155m sphere - inside of a 255 meter containment sphere inside a 1000m+ void. The outer sphere acts as both artificial sunlight and a drop-death height of 50m. 4 more outer panels to go (water and lava) and it's ready for interior work and redstone - including command-block powered proximity traps that don't have any triggers marking them as well as hidden walls that...
Facebook is a black hole. The constant stream of baby photos, #hashtags, BuzzFeed quiz results, and unintelligible status updates is mind-numbing. I know too much about too many people I hardly know.

HTC's Sense 6 has been out for over a month now with the One M8, and most of you have probably played around with its better known features, like the new Camera app and Harman Kardon audio.

Team Win Recovery Project (TWRP) is a custom recovery for Android devices and the one used by most softModders, mainly because it has touch-based actions, as compared to the more time-consuming button-based approach that ClockworkMod (CWM) uses.
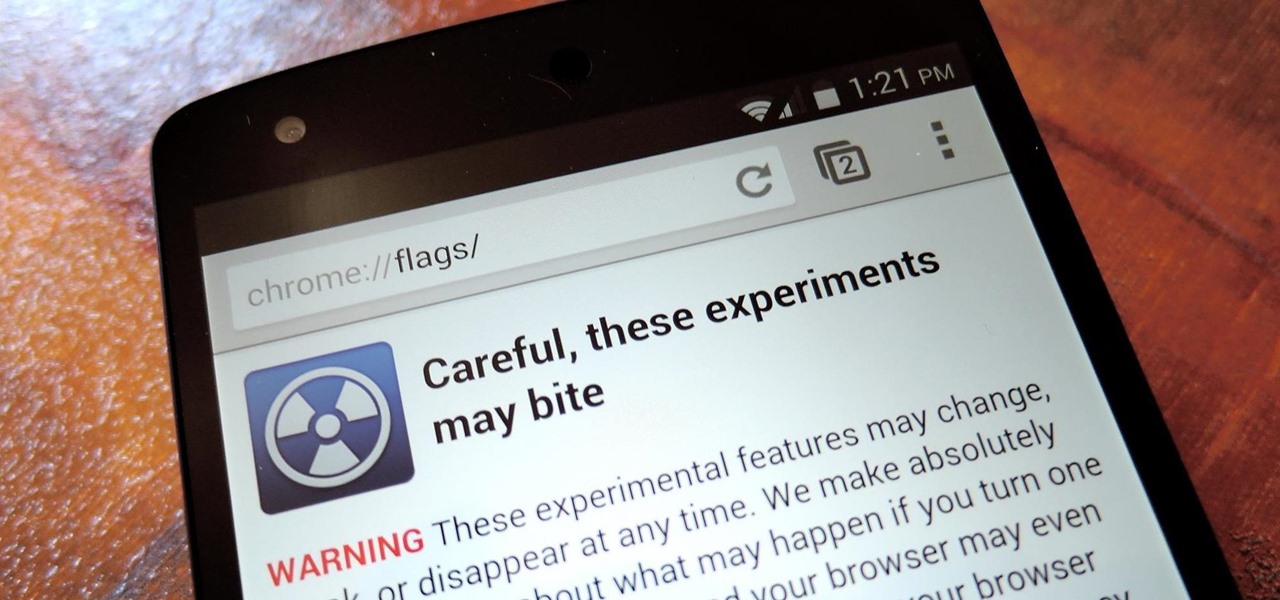
With the release of Jelly Bean, Chrome became the default web browser on Android. The wildly successful desktop browser was now fully entrenched in the world's largest mobile operating system.

The lock screen in iOS 7 is great at giving you immediate access to notifications, weather forecasts, date and time, music controls, and even the camera, but for a sports fan like me, there's one critical thing missing—game scores and news highlights.
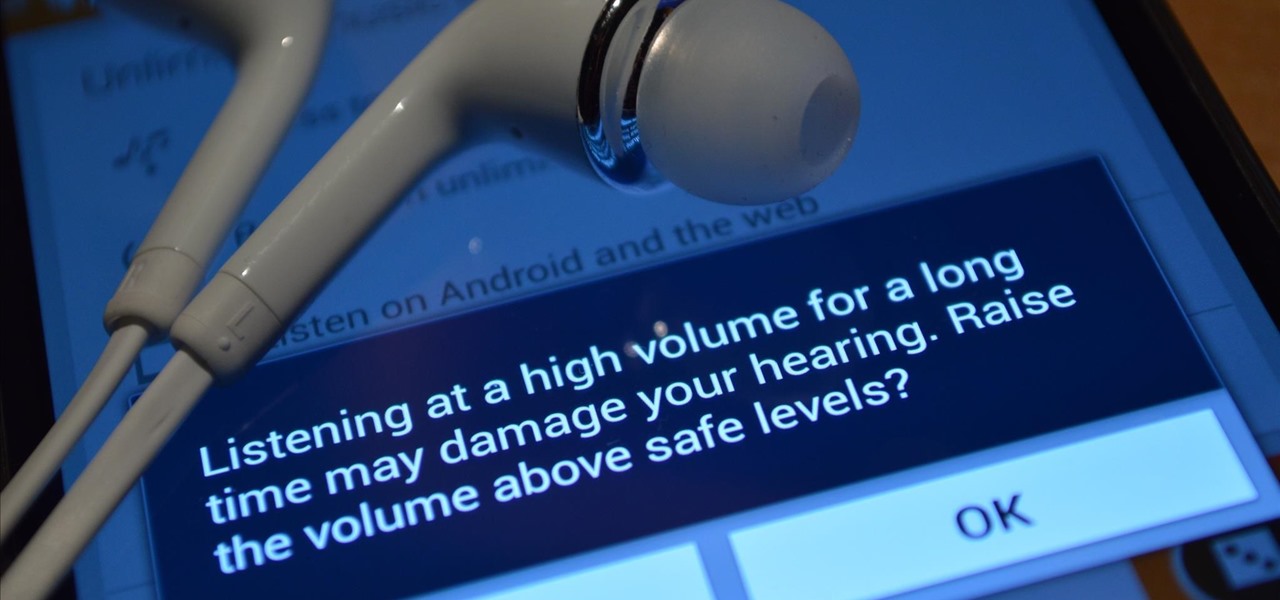
When you were younger, you probably had your parents bugging you not to have your cassette player headphones up too loud. For all you younger readers out there, it was probably a CD player. The even younger readers likely had an iPod or other MP3 player. Either way, your parents didn't want you to mess up your hearing, blasting that Limp Bizkit in your ears (wow, I'm showing my age here).
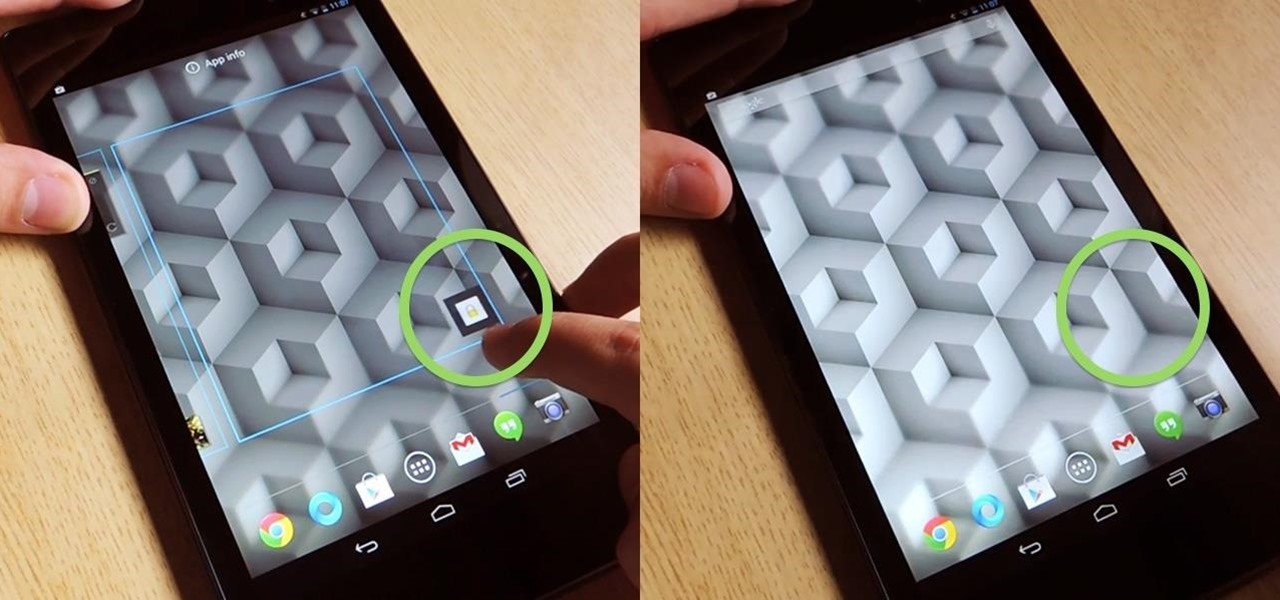
Overall, I love the Nexus 7 tablet, but one thing that I truly dislike about it is having to press the Power/Lock key to lock my screen.

You know how annoyed you get when you put a quarter into the vending or washing machine and it gets stuck? There's a quiet rage that boils inside you. Now, imagine that quarter is a sixty dollar video game, and it's stuck inside your brand new, four hundred dollar PlayStation 4 system.
In this Windows 8 Tutorial you will learn how to search for application in the Windows 8 store. I know it can be a bit confusing for those who have just moved to the Windows 8 store on how to search for store applications in fact it took me like an hour to figure out how to search because all the visual cues were hidden away. However when you finish watching this Windows 8 tutorial you will see it is as easy as being able type on your keyboard to find applications in the Windows 8 store.

Like in the original Black Ops, there are a bunch of funny and cool Easter eggs built into Call of Duty: Black Ops 2. Most have been discovered, like the Atari arcade invincibility on Nuketown 2025, but perhaps you didn't know about Thor's hammer?

Tripwires are a new mechanic released in Minecraft 1.3, and people are still trying to figure out how best to use them. Minecart returns are a great idea, but what about traps?

Every once in a while, Minecrafters want to create a simple hidden piston door to secretly hide all their valuable items. Now, it's possible with only 18 redstone, 2 repeaters, 12 sticky pistons, and ONLY 20 blocks of any kind!
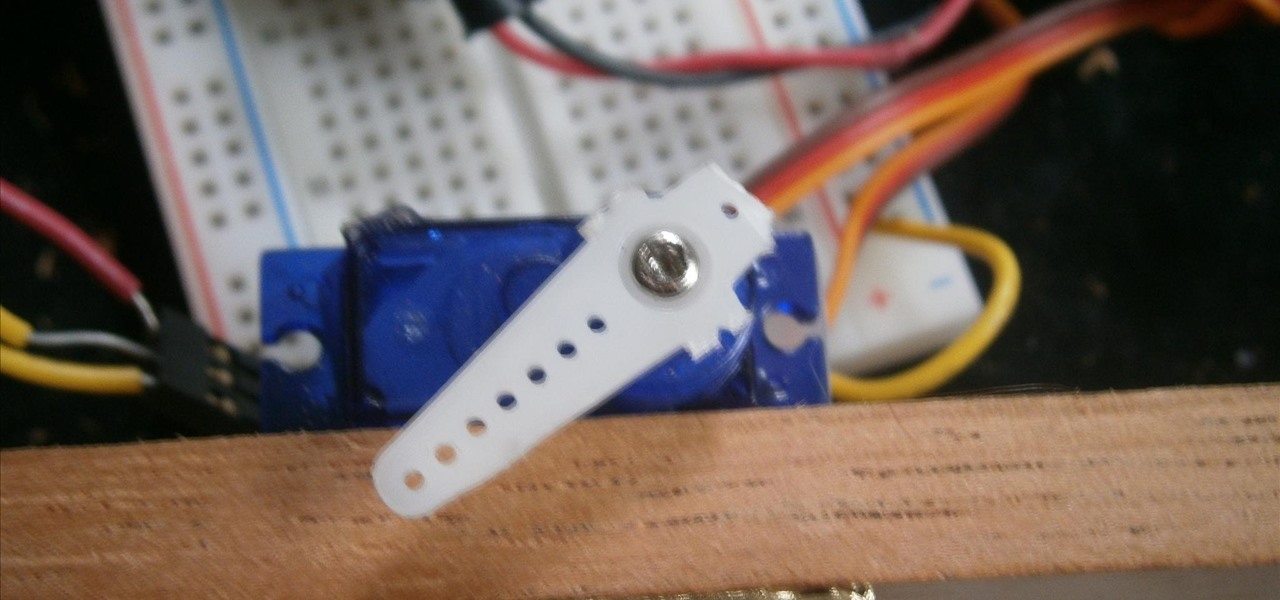
There is something special about a secret knock. It gets you into secret super villain meetings and is a surefire way to test for rotating bookcase passages. Secret knocks usually work with an intimidating drug lord and for policeman listening at the door for the correct pattern of raps.

In this tutorial, we learn how to find your computer's IP address. An IP address is used to know the exact location of someone using a computer with internet access is located at. First, turn your computer on and go to your main desktop. Then, click on "start", (which is located on the lower left hand side of the tool bar at the bottom), then click "run" and once that opens up, type "cmd" into the white empty space. Hit "ok" and when this comes up, type in "IPConfig" and hit "enter". Your com...

To do that just follow these simple and quick steps: Open your browser and go to Facebook. Now login with your details and click the Friends tab located on the top of the page. Now select All Friends and a list with all of your friends will appear. Now go to the person that you want to remove from the list and click on the X button located in the right of his name. Now just click Yes to the question that will pop-up and you're done.

Learn how to turn an old computer into an awesome hiding place. First, unbolt the fan and remove it. Pop open the side metal casing to get inside. Remove the fan and any wiring, then unbolt and remove the motherboard. Once you've removed everything, clean out the dust. Now you have a place to hide your stash!

Check out this computer hacking video tutorial from Unorthodox Hacking. The subject of today... hidden Windows passwords. This is a short episode with a fast pace is intended to expose a few of the areas where Windows hides stored authentication credentials. Be very cautious the next time you use a public kiosk!

Windows 7 has a new feature called Device Stage. It's a powerful and handy hub for all of your electronic gadgets that connect to your PC. It's device management for the power user! Microsoft shows you the layout real quick, so watch and learn.

Libraries is a cool new feature in Windows 7 that helps you find and manage all of your documents, music, pictures and videos in one location, no matter what location there in. This video from Microsoft outlines the usage of this new feature.