It's very easy to get your hands on a good cake. These days, a store-bought cake or even one made from boxed cake mix will usually be pretty good. Heck, make the first simple recipe you find on the internet, and it's likely to taste fine.
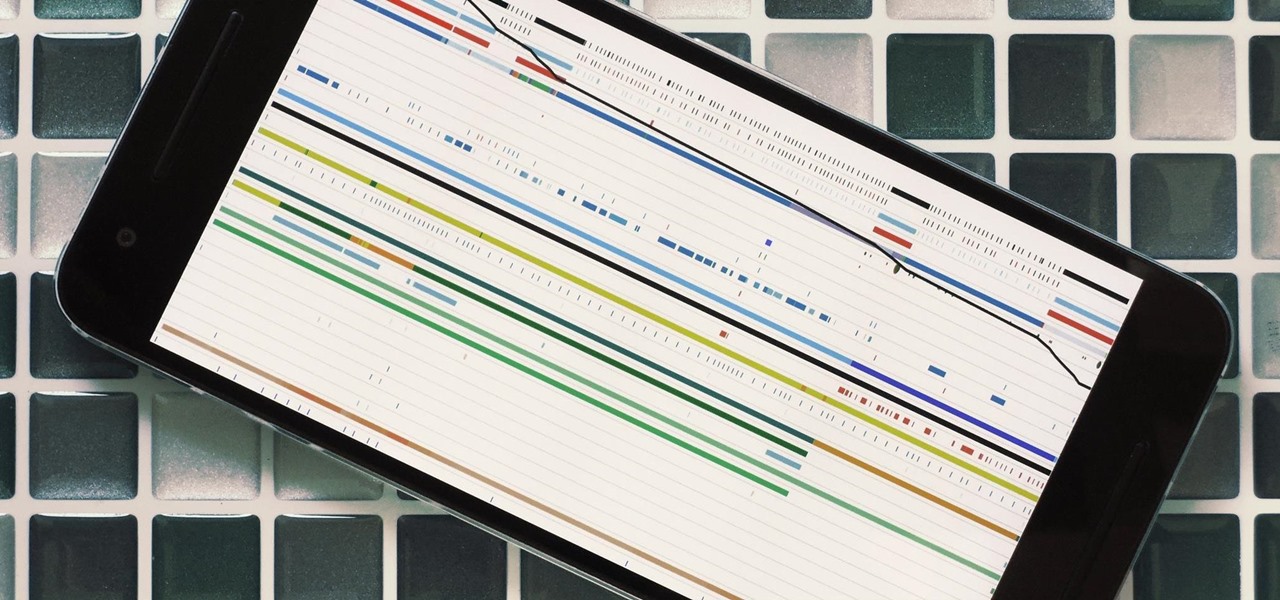
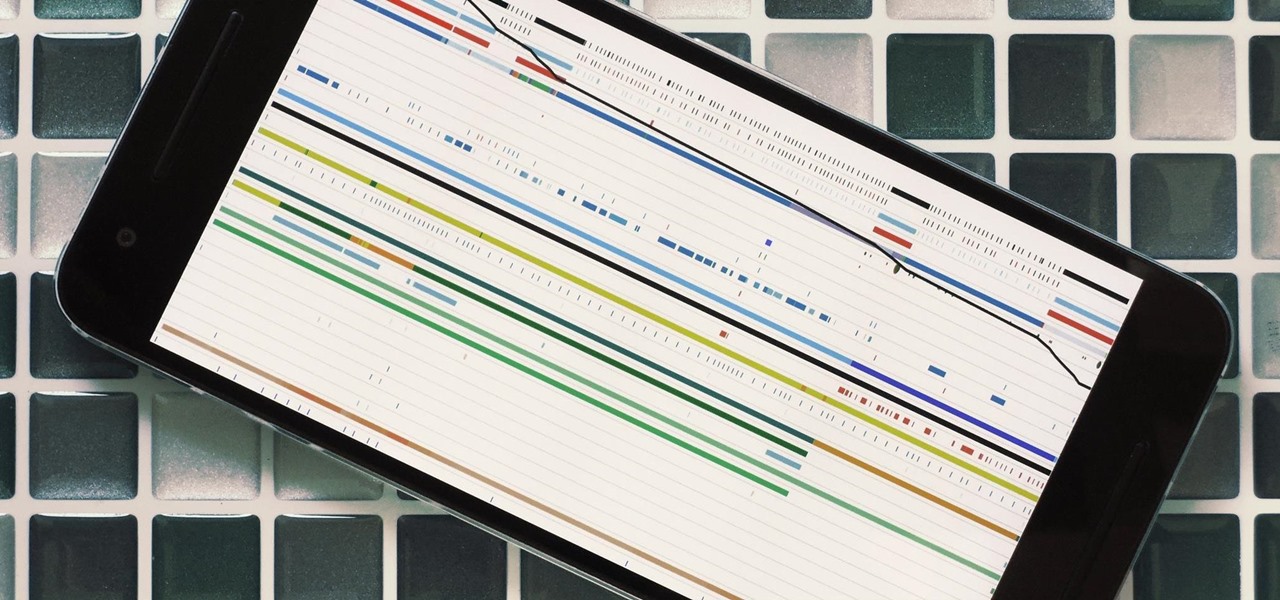
Android's stock battery menu is pretty decent. You can see which apps have been using the most power, and you can tell when your CPU was awake or asleep, among other things. But a lot of times, battery-sucking services will get lumped under the generic "Android System" header, and even though you can see when your CPU was awake, you can't exactly see why.

Sometimes the best way to hide things is in plain sight. Whether you're trying to sneak some medication past security at a concert with a zero-tolerance policy, or you're just worried that maybe Omar comin', YouTuber MrGear has a clever way to put your mind at ease.

We all know them, and many of us despize them. And some might support them, regardless many have different opinions.

Welcome to an introduction on writing basic malware, an optional sub-series in which I expose you to malware and its technologies. This is written for those who wish to seek a beginning in malware analysis or enlightenment on the subject. We will be justifying the writing and covering types of malware.

This is my first How-To on Null-Byte, so I hope it's not too complicated written, because I am not a native english speaker. I don't use pictures, but this Tutorial is a good supplement for my updated Tutorial here.

Welcome finally, to a tutorial on buffer overflows! At last we have reached an exciting part of this series where I will dedicate the entire article on explaining and exploiting the notorious vulnerability. Grab some popcorn, sit back and enjoy the show.

With over 10,000 possible combinations, a four-digit passcode may seem secure, but it's fairly easy for someone to crack your code—no matter how clever you think it is. Luckily, there are many other options for securing your iPhone's lock screen—especially if your running iOS 9.

If you ever need to make calls and/or send texts to the U.S. or Canada from abroad, or even just receive them from those locations, there's an easy way to do so without breaking the bank. In fact, it's free, and all you need is a smartphone, computer, and some free tools.

As Android owners, we ultimately have to look at our device and ask the difficult question: "Where the hell did all these applications come from?"

Hi there again, aspiring hackers (and veterans as well)! I'm going to explain how to perform a dictionary attack on a WPA/WPA2 protected network with Wifite. Please note that this doesn't work with WPA Enterprise For that end, you'd have to use an Evil Twin to get the "Enterprise" auth attempt, and then crack it.

Welcome back, my tenderfoot hackers! Now that we have begun this trip down web app hacking lane, we need to first address target reconnaissance. Like any hack, reconnaissance is critical. (Are you tired of me saying that yet?)

Can you tell when your friends are serving up a bunch of BS, or are you constantly oblivious, unsure if they're spinning a valid story? With so many ways to lie and fake information floating around, it can be impossible to tell what's the truth from what's complete BS. Here's how to sort through what you hear and find the real truth.

iTunes 12 was released alongside Yosemite this year, but it didn't pack quite the punch that the operating system did. Instead, iTunes received a minor facelift, with few new features and somehow lacking the intuitive feel of its predecessor. If you're not thrilled with iTunes 12, we've got a few tips to help you feel like you've got iTunes 11 back on your computer!

Shortly after the official release of iOS 8, news outlets like BGR, Gizmodo, and Huffington Post were instructing iPhone 4S users to refrain from updating (which were practically regurgitations of an Ars Technica piece).

There are a ton of great new features in iOS 8, and one of the most interesting (and perplexing) ones is called "Family Sharing."

Android's permissions system is simple, transparent, and straightforward. When installing an app, you get a chance to review all of the permissions that the app has requested. These can range from accessing your location data to holding a "wakelock" in order to prevent your phone from entering sleep mode. But your only choice in this matter is to accept all requested permissions, or not install the app.

Transition animations are an essential element of any mobile operating system. They give the user a sense of what's happening on the screen, where the apps are coming from, and where they're going.

When the Nexus 5 debuted, one of its coolest features was the fact that you could say "OK Google" any time you were on the home screen to launch a Google Voice Search. This feature was ultimately made available for other devices by way of the Google Now Launcher.

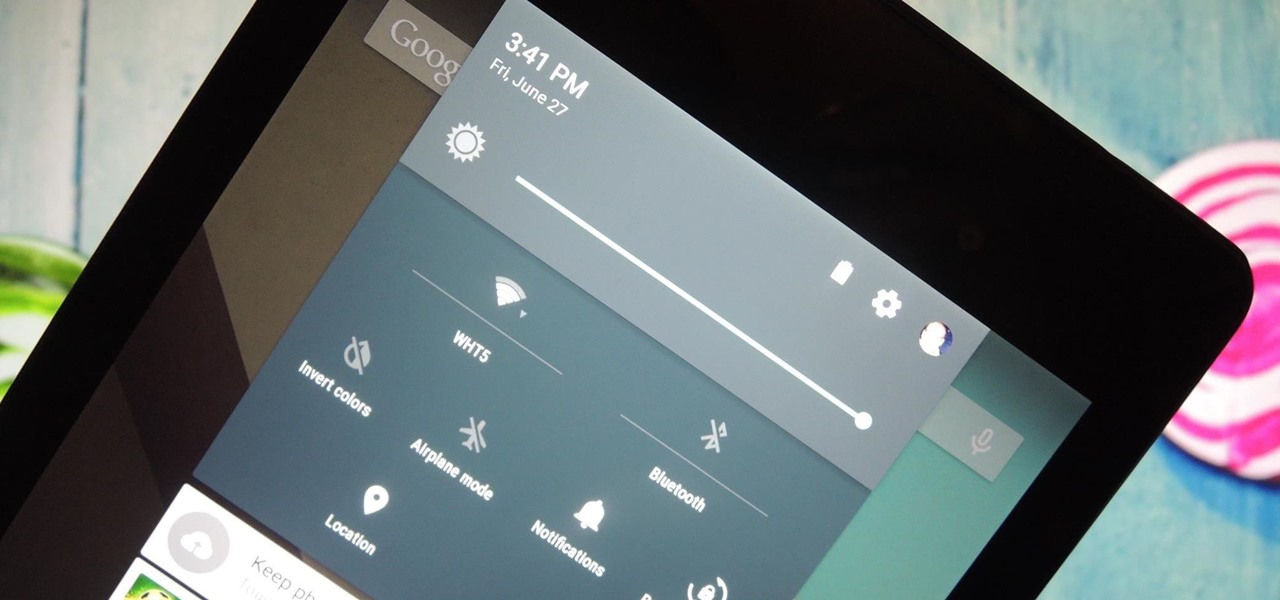
It was the star of the show, but now that Android L has been released for preview to Nexus 5 and Nexus 7 owners, there's a lot that Google didn't tell us about their latest mobile operating system, rumored to be called Lollipop.

Apple has released the 2nd beta of iOS 8, exactly fifteen days after the first version was unveiled at WWDC and subsequently released to developers. I've already shown you some of the new features of iOS 8, like location-based app alerts, randomized MAC addresses, hidden Safari tricks, and a slew of new things in the Messages app. But if you've had the chance the explore iOS 8, let's go through some of the changes that Apple has made to the latest iteration of its mobile operating system.

Welcome back, my aspiring hackers! In previous tutorials, I have shown you how to scan the globe for vulnerable servers and write simple scripts in BASH and Perl to perform other reconnaissance tasks. In a very recent guide, I taught how to scan vulnerable servers for Heartbleed.

Just because you have a Mac doesn't mean you can't root your Nexus 7 tablet. In fact, rooting Android 4.4 KitKat on both the 2013 and original 2012 N7 models is easy, if not easier than rooting it using a Windows PC.

Here's a routine that I'm sure all of us smartphone users go through at least several times a day. You notice your Samsung Galaxy S4's notification LED blinking, grab your phone to see what it is, and enter your PIN. Only instead of anything important, you find that it's just some online store enticing you with sales promotions, or some other email that you could have easily done without.

It's rare that a developer listens to the wishes of the masses, but that's exactly what CyanogenMod has done with their new CyanogenMod Installer, which automates the entire ROM installation process on your HTC One or other Android device. Previously, upgrading from the stock HTC One ROM to CyanogenMod required an unlocked bootloader, a custom recovery, the latest CM version, and Gapps. Let's be honest—unlocking the bootloader is a pain the ass, and probably the only reason stopping most peop...

Former Vice President Dick Cheney was so fearful of attacks, he had his heart defibrillator re-calibrated to block incoming wireless signals so that highly skilled hackers couldn't send him into cardiac arrest.

If you've seen our guide on the 18 coolest features in iOS 7, you know that there's a lot to like about Apple's new mobile OS, but there's also a laundry list of grievances to go with it. One that bugs me is the lack of Home screen customization, something that has always driven me to jailbreak in the past.

Netflix is more popular now than ever, but it still has a ways to go before satisfying everyone. Whether it's a lack of availability, buggy or unattractive apps, or just not being able to find anything to watch, lots of people have their complaints.

PRL, or Preferred Roaming List, basically tells your phone which towers to connect to first. Changing PRLs can improve reception and data speeds, and in some cases even give you access to corporate/test towers.

Living in Los Angeles has taught me one thing—parking is a luxury. If you are lucky enough to find street parking anywhere near your desired location, do not pass it up thinking you will get an even closer one. It does not exist. Looking for free parking? Get real. You can't even park at a busted meter in Los Angeles, despite state law saying otherwise. Now, finding a good parking spot is not just relevant for Los Angeles, but for other large cities and any other crowded areas, be it a shoppi...

In this video tutorial, viewers learn how to hide the call ID on an iPhone. The iPhone is a line of Internet- and multimedia-enabled smartphones designed and marketed by Apple Inc. This task is very simple and easy to do. Begin by gong to your main menu and select Settings. Scroll down and select Phone. Then select Show My Caller ID. Slide the bar to OFF. Now whenever the user makes a phone call, the receiver will not be able to see their ID. This video will benefit those viewers who have an ...

Check out the cool hidden game on Google and others. Help the easter bunny catch the eggs in order to spell out Google. It's a fun game to pass the time... just type in "Google Easter Egg" and press I'm Feeling Lucky. Bam... instant fun.

Using a sewing machine entails knowing how to the tension knob properly. This sewing how-to video demonstrates how to properly adjust the tension knob on a vintage Kenmore sewing machine. The tension knob is located near the front of the sewing machine. It has a dial numbered from 1 to 9. The larger the number, the tighter the tension.

In order to make a wizard balloon hat, you will need 6 partially filled balloons. Twist two segments. Then, add another balloon. Continue in this way. Keep adding a balloon each time you make 2 twisted segments. Next, begin weaving them in a way. Twist each balloon and connecting it with other balloons. Once you work your way around, you should have sort of an octagonal shape with a lot of legs. Attach larger ones to the twists. It is important to be careful to fill the balloons with the appr...

Ash Davies teaches us how to Photoshop digital bokeh with this tutorial. First, open up Photoshop and create a new canvas with your width at 1920 and your height at 1200. Now, create a new layer and set your background layer as invisible. Now create a medium size circle and reduce the fill to 50%. Now enter blending options and add a stroke of 10 pixels to the inside with the color set to black. Now define the shape as a brush and then click "edit" and "define brush preset" name this, "bokeh"...

In this "how to" video, we learn how to draw a "chibi" form of an angel. Chibi is a Japanese term meaning "short person" or "small child". It has become a style of art in which Japanese Anime and Manga artists attempt to make all of their characters into "cute", childlike characters (with small bodies, large heads, and large eyes). The artist in this video shows his/her step by step process of drawing a small "chibi" angel holding tightly onto a heart. The artist starts with the eyes, then wo...

This video is an explanation of how to fix a leak in a backyard water feature with a pond and waterfall. If the waterfall is losing water and has to be refilled frequently, you can tell there is a leak somewhere. One place where a leak can happen is a place where the liner needs to be propped up with a rock so it won't flatten out and allow water to leak out. Another problem can occur when a rock is arranged so that water splashes over it. That problem can be fixed by rearranging the rocks to...

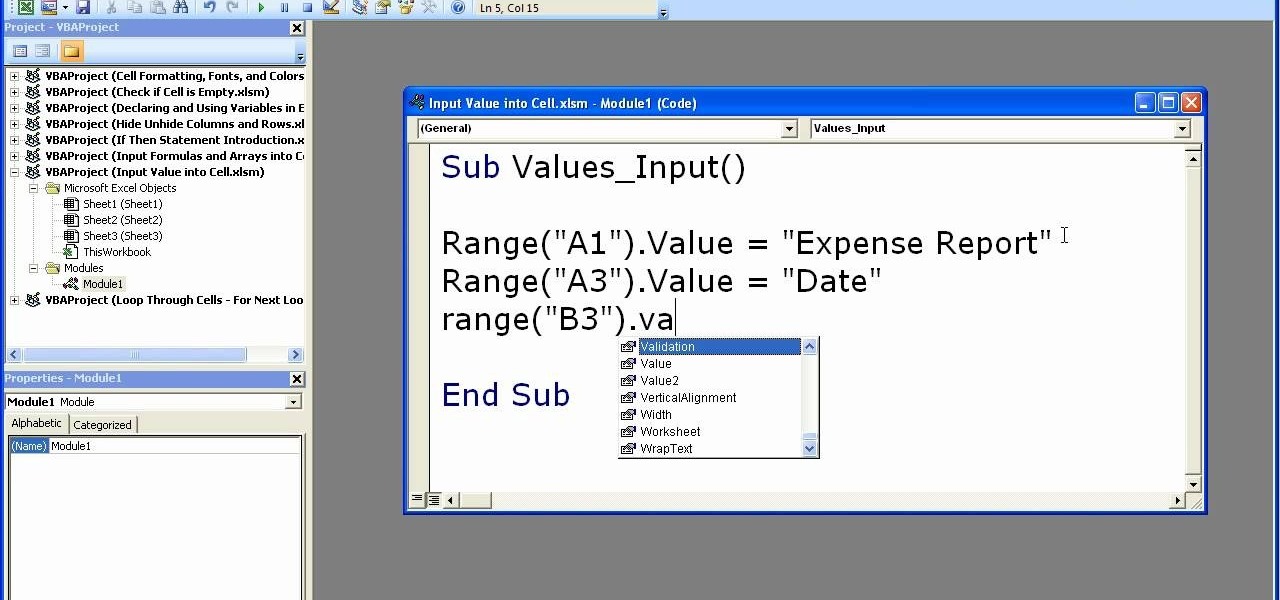
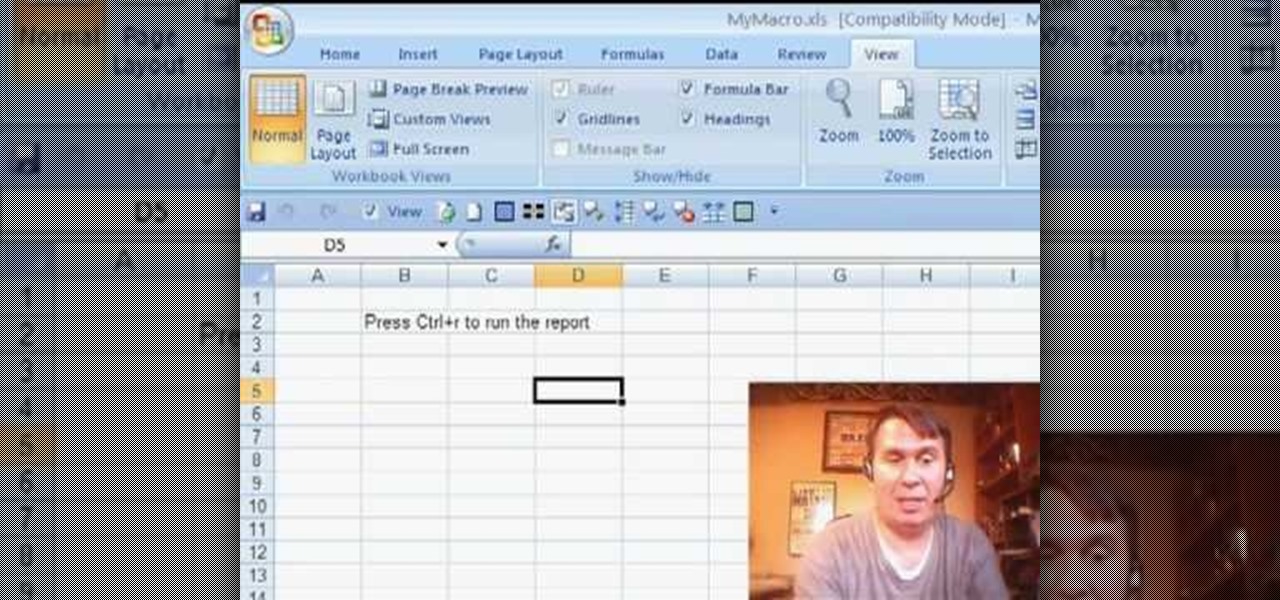
This video shows how to enter values into cells using Excel macros and Visual Basic. This includes a sample Expense Report that is used in this demonstration. In this demonstration, we will create the macro that inputs a title as "Expense Report", Three columns i.e. "Date", "Item" & "Amount", and the summery field as "Total Expenses", as well as the formulas located at the respective cells. Now, we're going to use two keyboard shortcuts i.e. "Alt + F11" to open-up the VBA window and "Alt + F8...

Install a pond skimmerThe most critical steps to installing a skimmer are the water level and attaching the liner to the face plate with a water tight seal. The pond should be rocked in. The skimmer needs to be level from front to back and side to side. That's critical. Optimum water level is approximately 3/4 inch down from the top of the steel face. Use the level (tool) to determine the water level on the face plate. It's important to have the weir door work effectively. Prepare the area fo...

Some times when you upgrade your Microsoft Excel software to Excel 2007 your old macros may stop working. Some times this may be due to the settings and by enabling the macros you can get your old macros to work. Macros are turn off by default in Excel 2007. You can turn this on from the macro security settings. But the settings option is it self completely hidden. You cannot find it in any of the tabs present on the top of the program. Even the macros option present in the view tab has no se...