In this video, we learn how to make your Facebook profile less public. First, log onto your Facebook account, then go to your privacy settings. Through there, go to search and choose who you want to allow to search for you on your site. After this, save your settings and move on to the other sections to change more privacy settings. If you do not want people that aren't your friends to see your information or to be able to search for you on Google, this is a great way to go. Making your infor...

In this video tutorial, viewers learn how to bypass the log on system. Begin by downloading the Kon-Boot file provided in the video description. Once downloaded, burn the file onto a disc or convert it into an ISO image file to burn it onto a disc. Now wait for the file to finish loading. This will take several minutes. Once finished, users will now automatically be able to log into the password protected computer by simply pressing any key on their keyboard. This video will benefit those vie...

In this tutorial, we learn how to find the hidden browser cache on Firefox. First, log onto a website that you use often and if you want to see how many times you have visited it, right click on an empty space on the page. Next, click on "view page info", then click on the "security" tab. When you click on this, you will be able to see how many times you have visited that website, and if they are storing cookies on your computer. You will also be able to see if you have stored passwords throu...
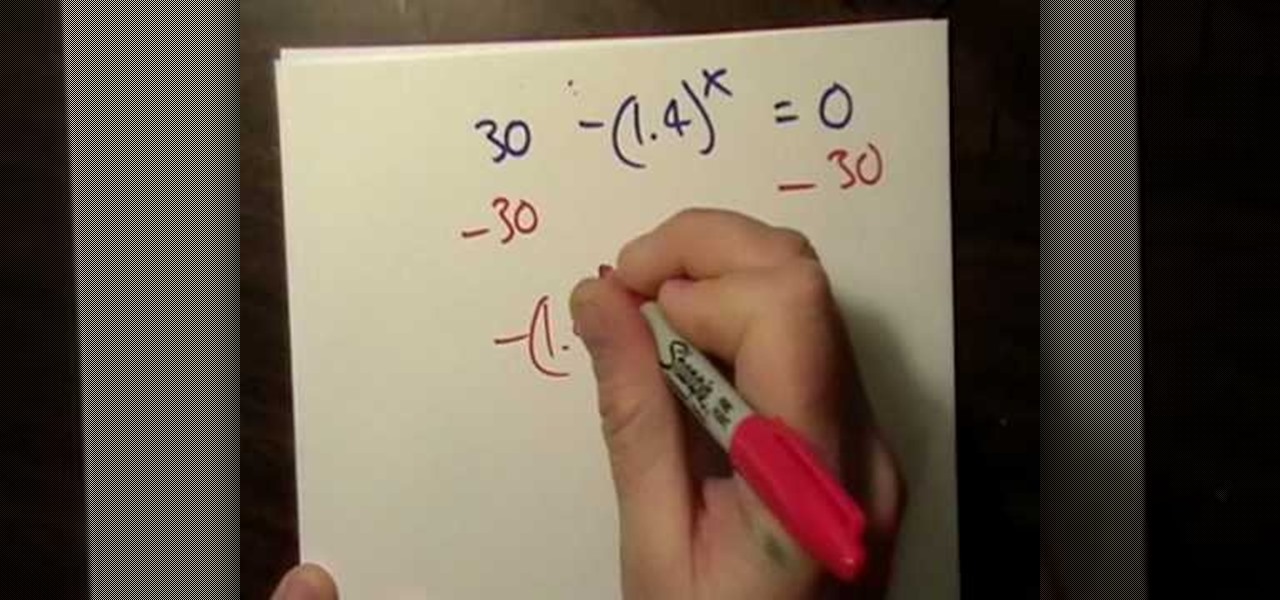
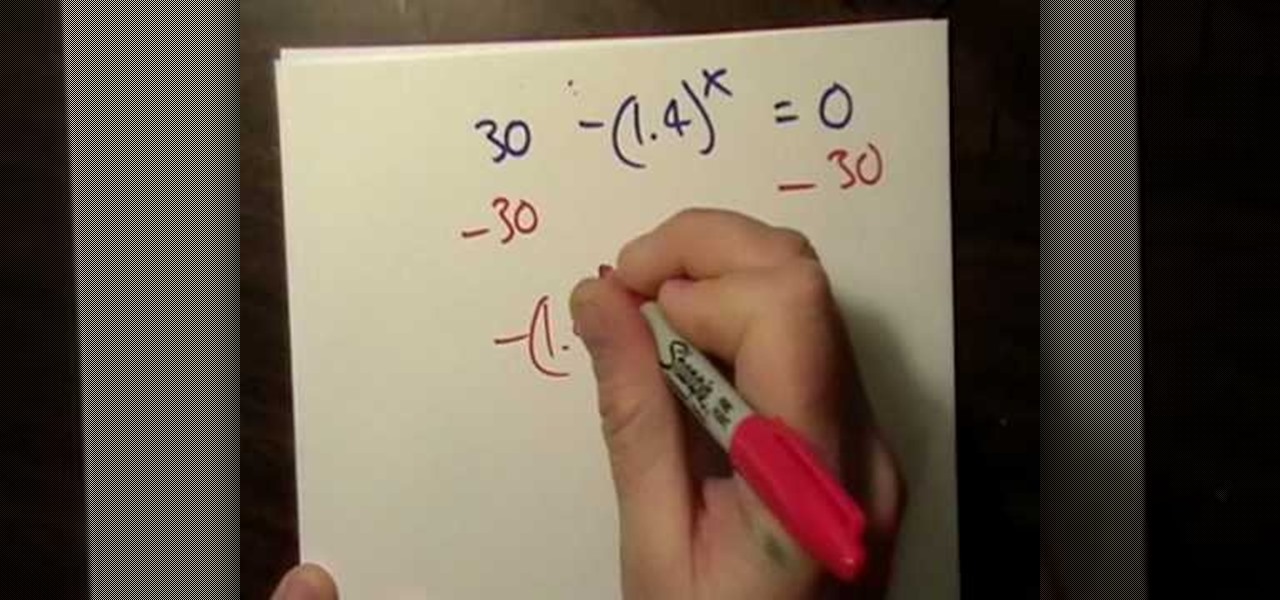
Looking for a primer on how to use the natural log, e, to solve an exponential function? Learn how with this free video lesson. From Ramanujan to calculus co-creator Gottfried Leibniz, many of the world's best and brightest mathematical minds have belonged to autodidacts. And, thanks to the Internet, it's easier than ever to follow in their footsteps (or just finish your homework or study for that next big test).

Learn how to evaluate simple log expressions and how to use the log operation to solve exponential equations in intermediate algebra with this free video lesson. From Ramanujan to calculus co-creator Gottfried Leibniz, many of the world's best and brightest mathematical minds have belonged to autodidacts. And, thanks to the Internet, it's easier than ever to follow in their footsteps (or just finish your homework or study for that next big test).
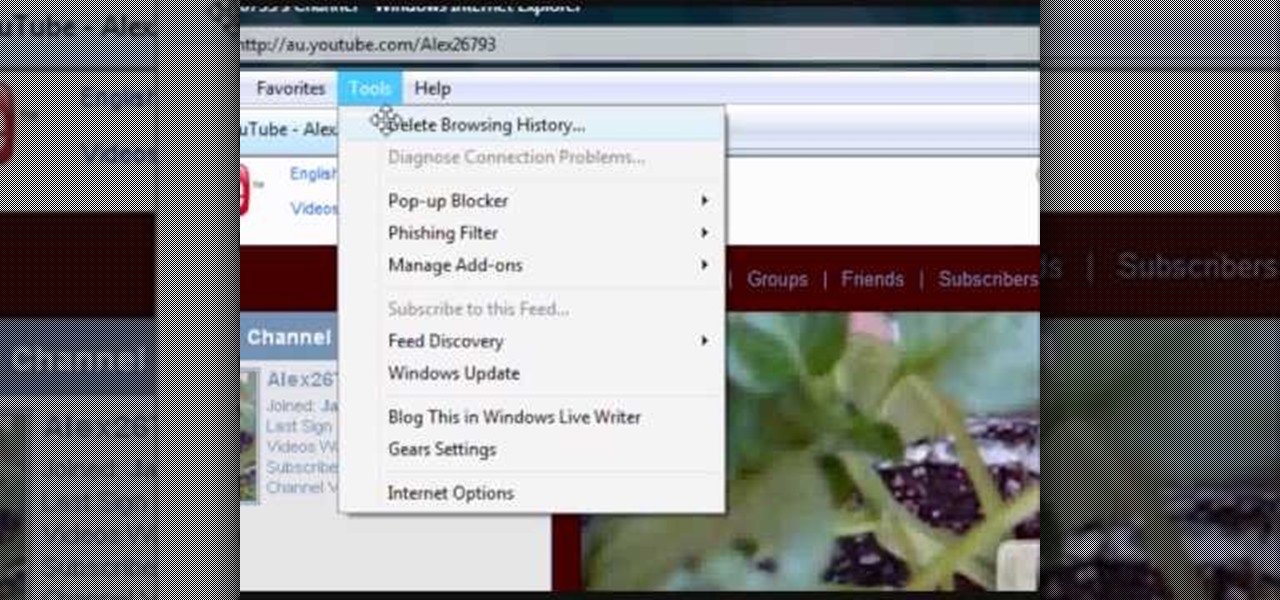
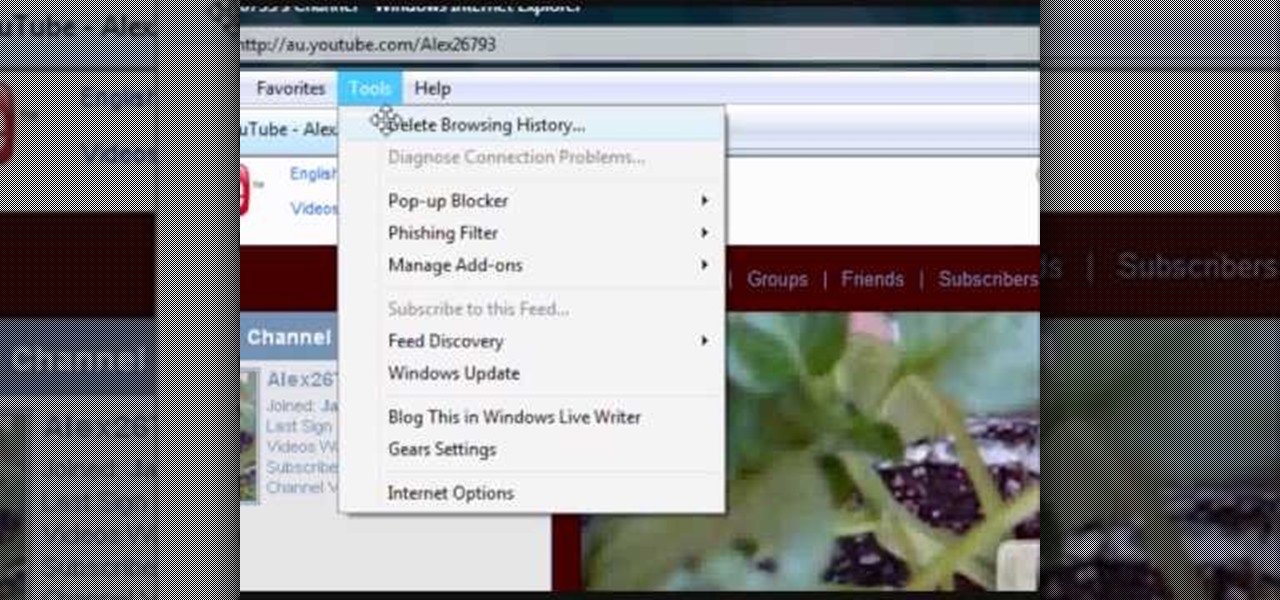
If your computer or web browser is running slowly, a good place to start clearing space is in your Temporary Internet Files. Temporary Internet files, as well as cookies, are collected every time you visit a site online. These files make it easier for your PC to remember your browsing history, and your log in information for various websites. However, sometimes all of these little files can add up into one big clog on your machine. If your computer isn't running up to par, follow along with t...

This is a very useful instructional video on how to use Skype to call anywhere in the world. You can go to Skype .com and click account and open a new account with Skype. Now log on Skype using your user name and pass word. now you can click the free calls button and you can call any one from any country across the world. You can also call mobile phones in the USA and Canada by paying a nominal fee. However you can talk with any one for unlimited time. It is very easy to use Skype. Your priva...

The holidays are here! This means that holiday desserts are just around the corner. This baking video will show you how to create a yummy chocolate yule log cake, a popular holiday tradition. It's also known as a Swiss roll. Learn the ins and outs of making this delicious cake. Your family will be convinced that you spent hours in the kitchen.

Getting splinters is no fun, but making them can be if you've got the right tools and the proper technique.

In this video you'll learn how to log in to Webmin, a web-based Unix administration interface, which will allow you to manage your serve with a web browser. Watch this video tutorial to learn how to control your server with a web browser and the Webmin interface.

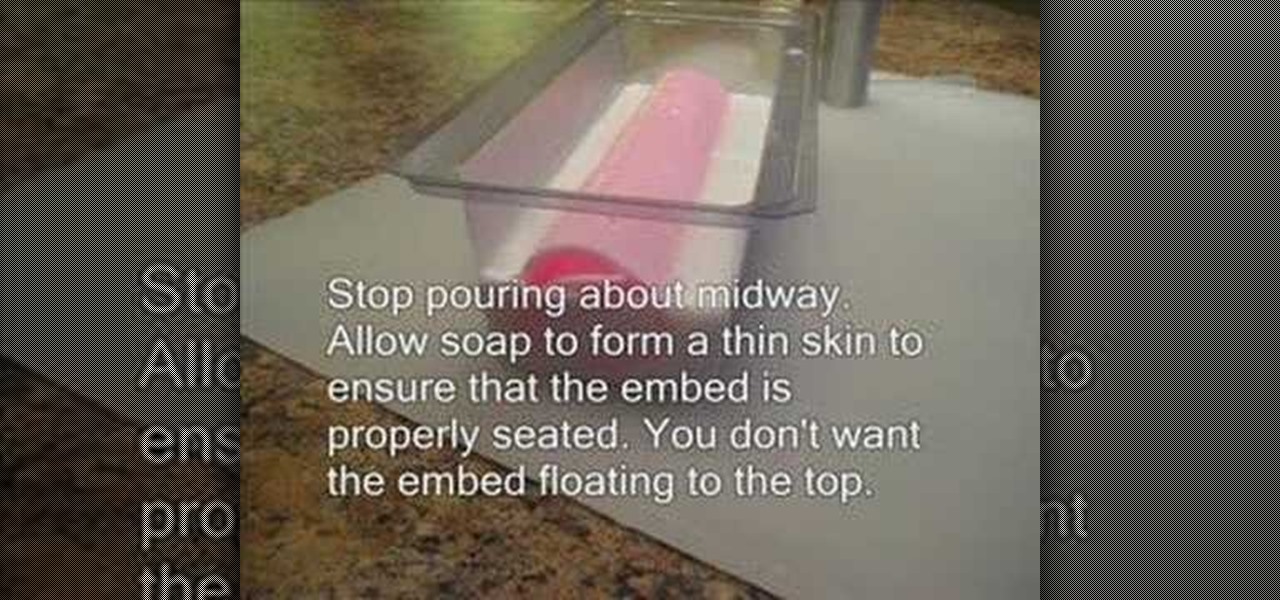
Learn to embed a soap log (soap curl) in a loaf mold. Create sliced soaps in no time at all!

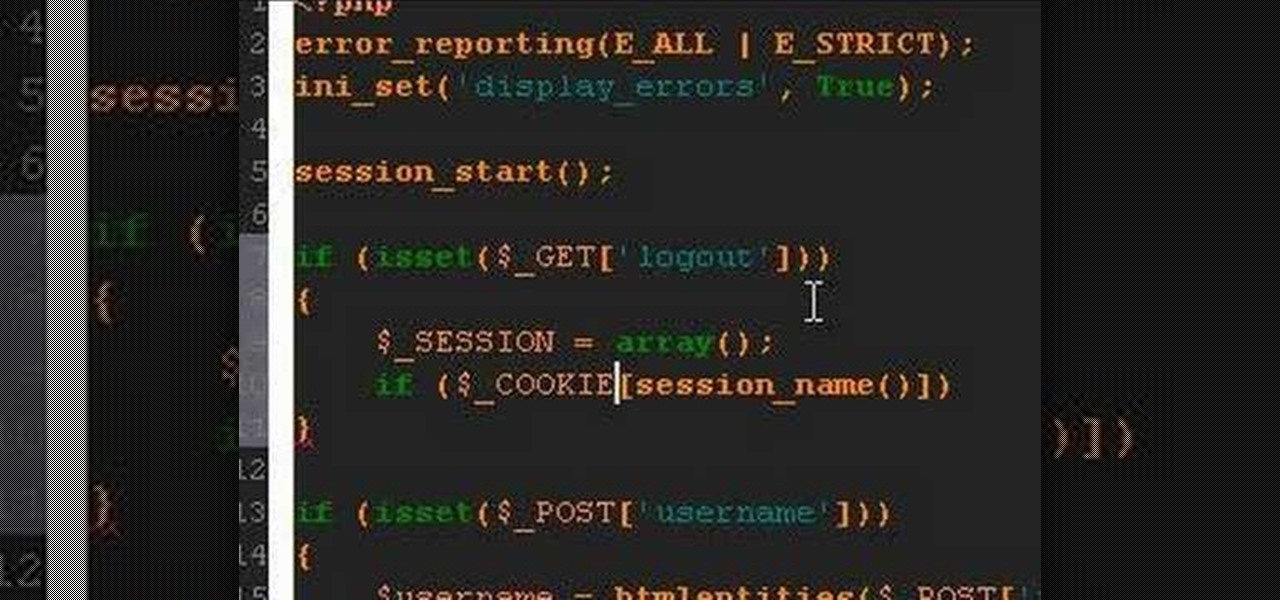
A PHP tutorial on how to log out a user and destroy a session.

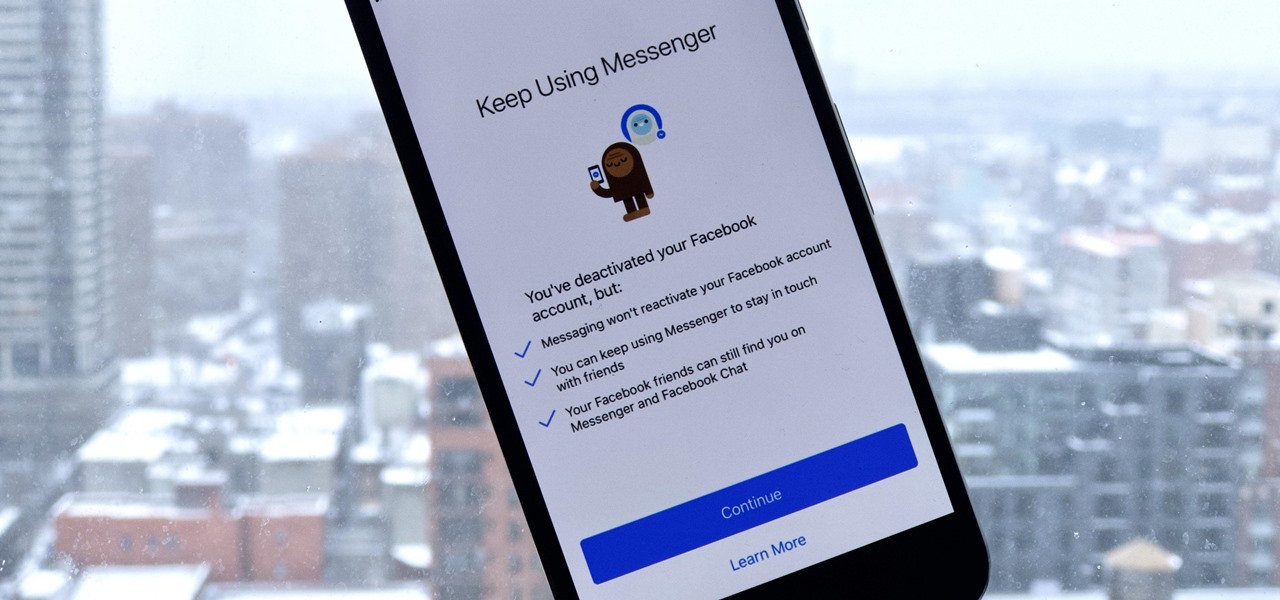
If you finally decide to take the plunge and delete your Facebook, you should know that your Messenger account may also go missing if that's how you log into it using your Facebook account. You can make a new Messenger profile without tying it to a Facebook account, but if you want to keep all of your old chats, you're going to want to deactivate rather than delete.

The threat of an evil access point has been around for a long time, and with the rise of open public Wi-Fi, that threat is often overshadowed by how comfortable we are using third-party Wi-Fi hotspots at coffee shops and public spaces. While we've shown an evil twin attack using the Aircrack-ng suite of tools, MitmAP is a Python tool to configure custom APs for many types of wireless attacks.

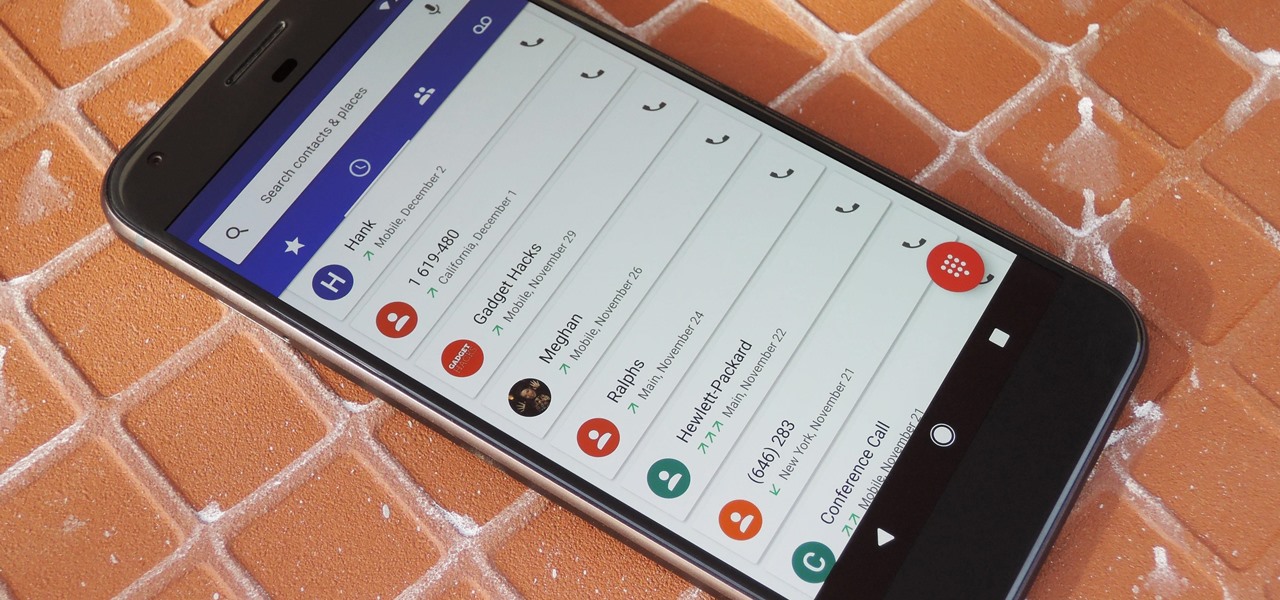
By default, Android limits your call history to the last 500 incoming, outgoing, or missed calls. When you reach this limit, older entries get trimmed off the bottom of the list and deleted forever. This isn't an issue with storage space, because even the biggest call logs only occupy mere kilobytes, so it's really just an artificial limit.

Welcome back, my aspiring hackers! Those of you who use Windows in a LAN environment understand that Windows machines can share directories, files, printers, etc. using "shares." This protocol dates back to the 1980s when the then dominant computer firm, IBM, developed a way for computers to communicate over the LAN by just using computer names rather than MAC or IP addresses.

With recent security breaches in the news, there is no better time than the present to make sure you know exactly what's happening on your device.

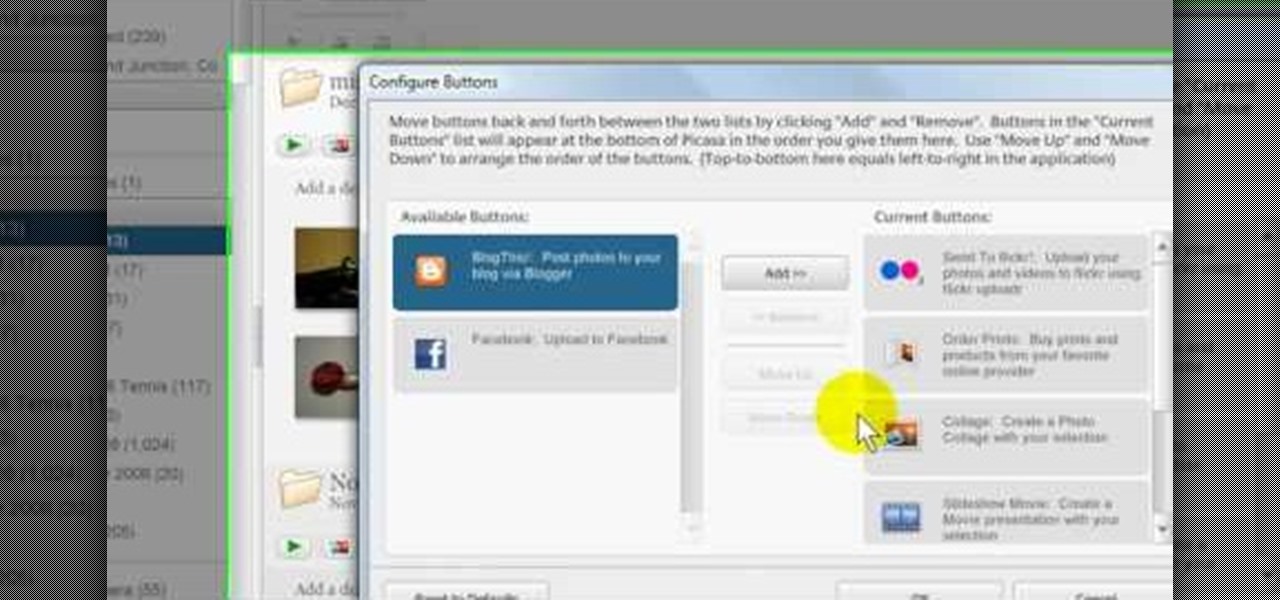
In this Computers & Programming video tutorial you will learn how to add photos to Facebook using Picasa. The video is from Help Me Rick. Log into Facebook, go down to the lower left corner and click ‘Applications’. Click ‘Find More’ and in the search applications box, type in ‘Picasa’. You will get a list of Picasa applications. Select the Picasa by Alan Lundeen. Here you click ‘go to applications’ -> install now -> OK -> Yes -> Facebook -> Add -> OK. Now you will get a Facebook icon on the ...

Jim Reppond of Coldwell Banker Bain demonstrates the way of getting postlets into Facebook. He says that by adding the postlets in your Facebook page, one can click on the link and directly go the postlets page if they are interested. He asks you to then go to the postlets page and log in using your username and password. Once inside, you can click on the 'My Postlets' tab to see your active postlets. Then chose the postlet you want to add to Facebook and click on the respective 'HOST' button...

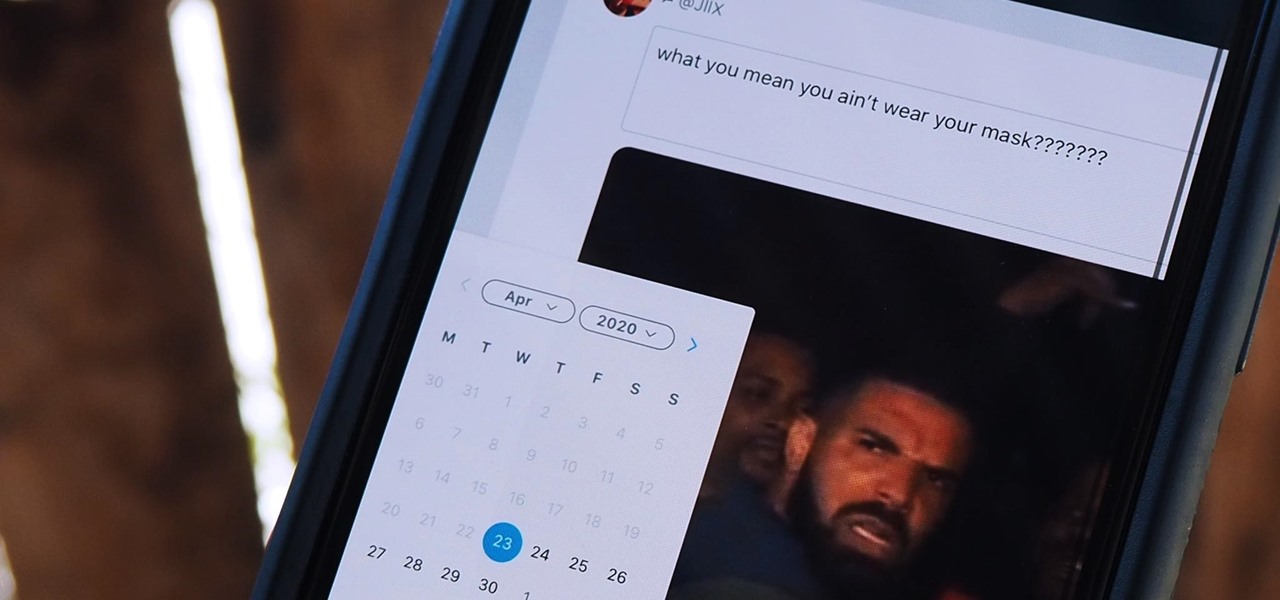
Twitter is a science. The smarter you post and engage with others, the better chance you have at building a bigger audience. Scheduling your tweets is one way to get there. Most engagement occurs at specific hours, but you may not be around then to post your tweet manually. While the official Twitter app on iOS and Android doesn't allow you to schedule, there is another way.

Apple released the third public beta for iOS 13.5 today, Wednesday, May 6. This latest public beta update comes exactly one week after Apple released iOS 13.5 public beta 2, which, among other things, introduced Apple and Google's joint COVID-19 exposure notification API. Public beta 3 updates that settings page to show a more detailed "Exposure Logging" option instead.

As a root user, you have a lot of responsibilities to make sure your phone stays secure. Expectedly, some things may slip through the cracks. Remembering to check which apps have been granted root access is extremely important. All it takes is one bad app, so it's good to learn how to avoid that at all cost.

Pandora has a simple rating system that works by hitting either the thumbs-up or thumbs-down icon on a track that's playing on your station. If you choose the former, the song you like along with others similar to it will play with more frequency, while selecting the latter will prevent that song and others like it from playing in your station moving forward.

If you've ever seen something called ThinkPoint Antivirus on your computer, you have gotten one ofhte most widespread and infectious fake antivirus malware programs out there. To get it off your PC, follow the instructions below, or watch this video for an alternate method if this one doesn't work.

As with most things on the Internet, browser cookies can be either helpful or harmful, depending on how they're used. On one hand, they make your experience more convenient by storing information about sites you use frequently. On the other, they can help companies track you across the web or cause your computer to be more vulnerable to attacks on public networks.

Facebook is an internet phenomenon which is quickly gaining popularity. For those who do not yet have a Facebook, this video will show you the basics of how to meet people and to connect with people online as well as how to set up your profile on the site. After creating an account using your email address and setting up your password, log on to the website. Set up your profile by clicking on the tab labeled "info" and entering information which you would like to share about yourself. You can...

In this tutorial, we learn how to delete a Facebook account. First, log onto the internet and log into your Facebook account. Once you are logged in, you will be presented with your home page. Now, click on the account settings on the right hand side and find the button that says you want to cancel your account. Once you have confirmed you want to cancel your account, Facebook will send you an e-mail that asks you to confirm it one last time. After you are done with this, your account will be...

In this video tutorial, viewers learn how to decorate a modern yule log cake. Begin by glazing the cakes with a chocolate glasage. This glaze is made with sugar, coco powder, chocolate and cold syrup. Pour the glazing all over the cake and shake to make sure that it is spread evenly. Make the glazing thin for maximum coverage. Using a knife, pick up the cake and place it on a decorative piece of cardboard or plate. The cake is then decorated with hardened and macaron. This video will benefit ...

This is a short video on how to make a corned beef flavored sausage log. Learn to make a single corned beef log from 80:20 ground chuck. The process excludes the addition of coarse ground venison to the recipe which works to improve the texture. This clip is concentrated on the mixing and cooking process in a residential environment. Stuffing, slicing and packing are touched on lightly using a 9" commercial slicer and residential vacuum sealer. The recipe is available at the end.

Don Schechter demonstrates how to capture your footage from your camera to your computer and log it for easy access later on for Final Cut Pro. Logging clips allows you to organize your footage without having to waste hard drive space.

For those of us living in any of the 49 states other than New York on Thanksgiving Day, checking out the famous Macy's Thanksgiving Day parade at New York is more a dream than reality. While the parade airs every Thanksgiving on television, it's also possible to catch the festivities online.

In this video tutorial, viewers learn how to import, manage and export 16:9 footage in Adobe Final Cut Pro. Begin by opening the Log and Capture.Then configure the Logging, Clip Settings and Control Settings. For the Control Settings, set the Device Control as Fire Wire NTSC and the Capture/Input as DV NTSC 48 kHz Anamorphic. Then scroll through the sequence setting of the footage and check Anamorphic. To export, click on File and select Export. Click in Options set the the size to Compressor...

Compound butter is just flavoured butter. LegourmetTV shows you how to make garlic butter, which is a good companion to fresh bread. One clove of roasted garlic is added to half a cup of unsalted butter to make simple garlic compound butter. You can also add cinnamon and sugar to butter for toast. Alternatively, you can even add any of your favourite herbs to melt down a steak. You can also shape the butter into a log, wrap it up in baking paper and keep it in the refrigerator for storage. Th...

On this video from Bushcraft Machete, he explains the purpose of a scandi edge and how to use it. He uses the machete as a planer, stripping the bark from a log by holding the machete almost flat against the log and tapping the back of the blade with a stick. He explains that a scandi edge is sharpened all the way down to a point and has a very low angle. This type of edge makes the machete useful for carving off thin strips of wood. He has sharpened his machete with a scandi edge near the ha...

SSH, or the secure shell, is a way of controlling a computer remotely from a command-line interface. While the information exchanged in the SSH session is encrypted, it's easy to spy on an SSH session if you have access to the computer that's being logged in to. Using a tool called SSHPry, we can spy on and inject commands into the SSH sessions of any other user logged in to on the same machine.

The Facebook app only supports one account being logged in at a time — but what if you need one for work and one for your personal life? That would normally involve logging out and logging in every time you need to switch accounts, but your OnePlus device offers a much better solution.

Phishing is the easiest way to get your password stolen, as it only takes one mistake to log in to the wrong website. A convincing phishing site is key to a successful attempt, and tools to create them have become intuitive and more sophisticated. SocialFish allows a hacker to create a persuasive phishing page for nearly any website, offering a web interface with an Android app for remote control.

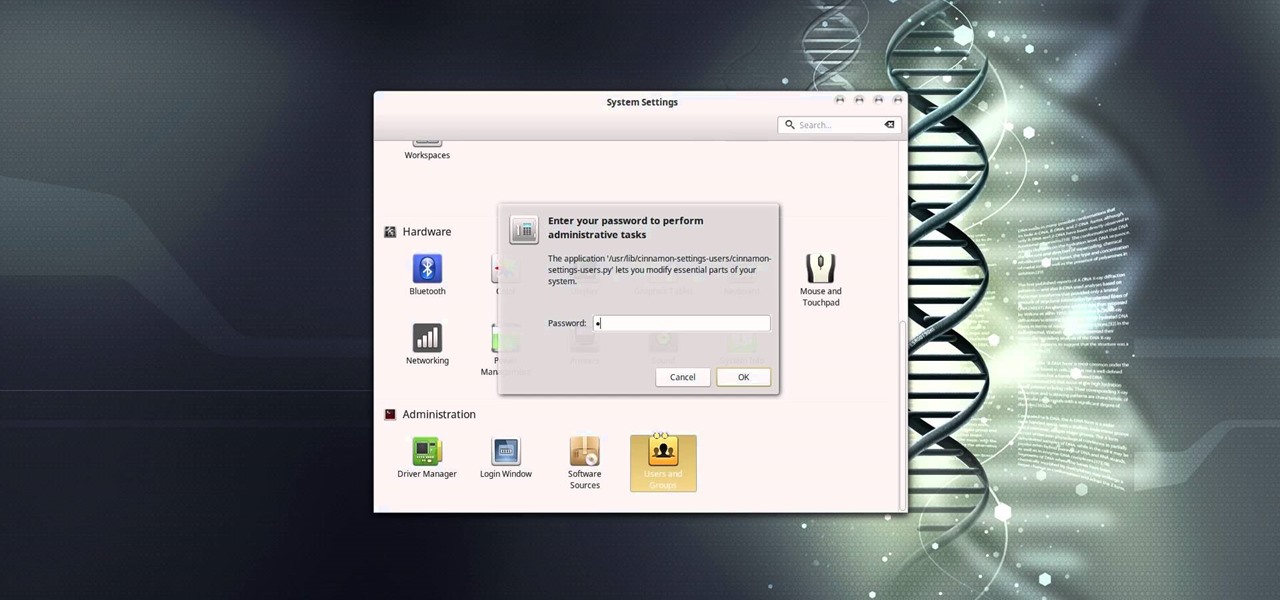
In this video tutorial, I'll show you how to remove the password from the log in screen on Linux Mint 17.2

Welcome back, my hacker noviates! In a recent post, I introduced you to Shodan, the world's most dangerous search engine. Shodan crawls the globe from IP to IP address, attempting to pull the banners of each web-enabled device and server it finds.

It's known that during the Thirty Years' War that took place in Europe between 1618 and 1648, soldiers used Swedish fire torches (also called Canadian candles) for heating, lighting, and cooking meals.