This tutorial shows you how to get through the laser traps you'll encounter in Chapter 7 of Dead Space 2. The game in this walkthrough has been set to Normal difficulty, and also shows you where to find the logs on this level.

This tutorial shows you a few good tips on how you can manage your multiplayer Minecraft game. There's a special focus on how you can mine for diamonds and other rare commodities when you've logged on to a multiplayer server.
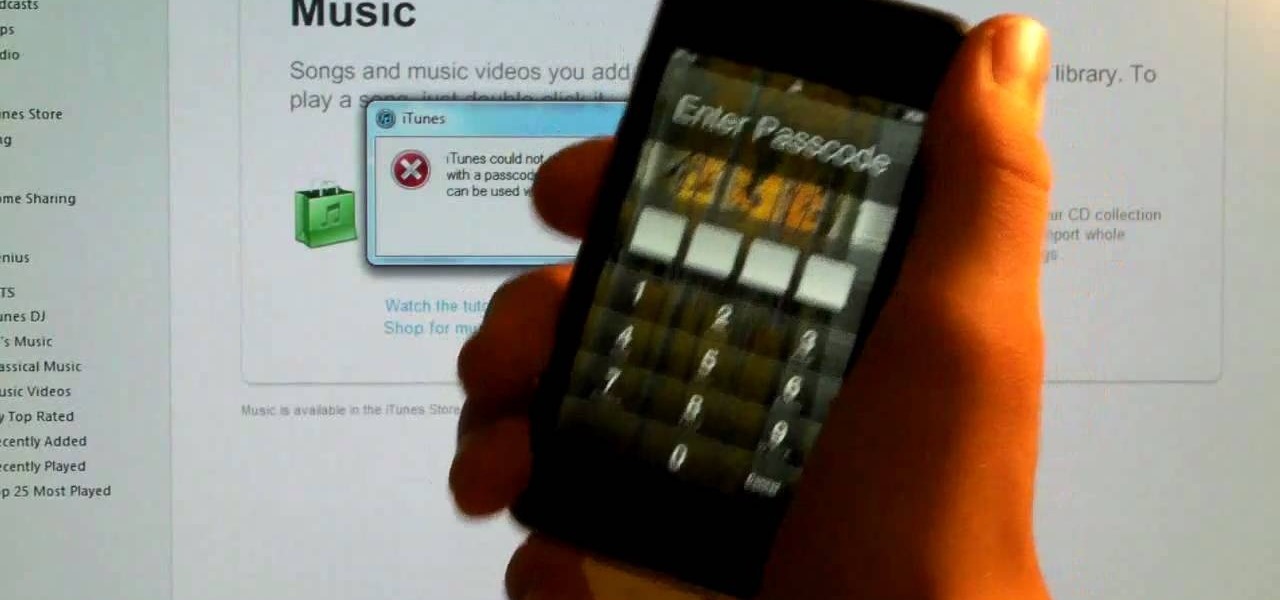
Remove the password on any iOS mobile device! This video will teach you everything you need to know to remove the log-in pass code from your iPhone, iPad or iPod Touch. For more information, including detailed, step-by-step instructions, and to try it out for yourself, watch this hacker's how-to.

Your first night in Minecraft is the most perilous one, and you don't have to build just a simple shelter. There's enough time to build a complete house out of twenty-three logs, twenty-three blocks of sand, four blocks of coal and eighty-one blocks of stone.

Add a small bit of content which appears whenever visitors to your website mouse over a specific area of your website - such as having your company's slogan appear in a small text box when users hover their mouse over the log.

The Sparkle app for your iPhone or iPod Touch is a client which allows you to message your friends in Second Life without having to log fully into Second Life. Great if all you want to do is send someone a quick chat message without playing the game.

Looking for the easiest method of customizing the login screen on a Microsoft Windows PC? This brief video tutorial from the folks at Butterscotch will teach you everything you need to know. For more information, and to get started personalizing your own log-on screen, take a look.

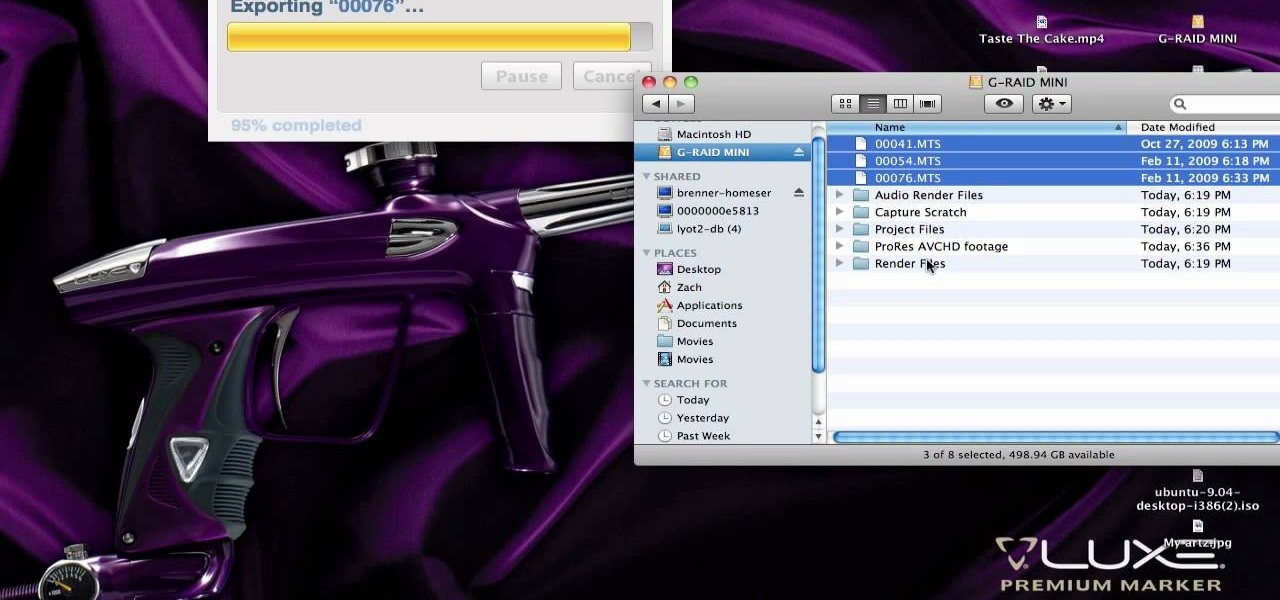
In this clip, you'll learn how to work with AVCHD files that can't be logged and transferred like MTS files. Whether you're new to Apple's Final Cut Pro non-linear video editor or just want to better acquaint yourself with the popular video editing program, you're sure to benefit from this video tutorial. For more information, including detailed, step-by-step instructions, watch this tutorial.

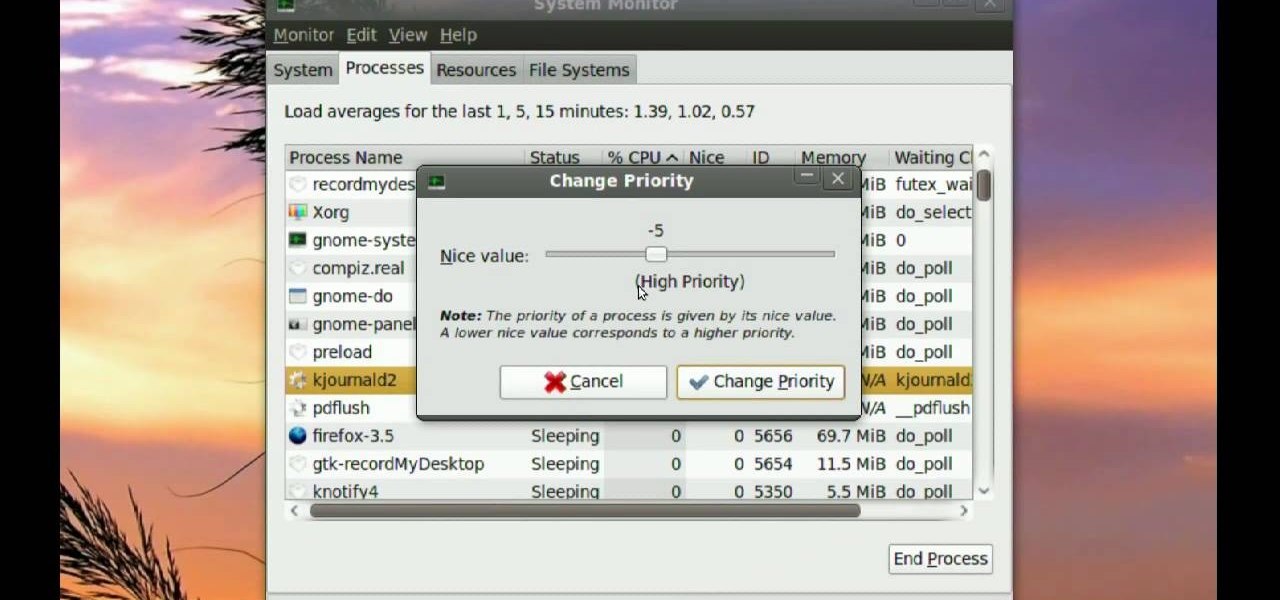
Ubuntu comes with pre-installed tools that can help solve problems you may encounter when using Ubuntu Linux. This video tutorial shows how to identify and address common problems in Ubuntu Linux. Such tools discussed include the system monitor, the log file viewer and the network tools.

In this video lesson of LEARN TO DRAW with Tom Gammill, where the creator of The Doozies discusses cartooning and the spirit of Christmas. Learn how to draw a cartoon santa claus using mostly circles and half circles. Towards the end of the video Tom teaches you how to make a holiday yule log too. Follow along and learn how to draw an easy cartoon Santa Claus.

Find lyrics to an unknown song by logging on to the Internet and typing in a few words from that song into a search engine. Locate lyrics to an unknown song with tips from a professional musician in this free video on music.

In this tutorial we show you where to download MySQL Query Browser and how to access and edit your databases. MySQL Query Browser is an easy way to access database information remotely from your desktop without having to log in to your server. Learn where to get MySQL Query Browser, and how to use it to access and edit your databases.

No need to spend money on fire starter logs and such items, with free lint from your dryer and some wax from a candle you can create a great item to start fires while camping, hiking and so on. Dryer lint and wax are both small and lightweight so they're easy to pack and carry around. Watch this video training tutorial and learn how to make flame fuel from dryer lint and wax.

Applications on the blink? In this tutorial, Gary Rosenzweig looks at various ways to force broken applications to quit. He also shows some handy keyboard shortcuts for logging out, restarting, shutting down and quitting instantly.

Epicurious Editor-in-Chief Tanya Wenman Steel demonstrates how to fill and roll up a genoise cake to make a jelly roll, a Yule log cake or bûche de Noël.

Learn how to log and capture movie footage in Apple iMovie so you can begin to transform your raw footage into a completed movie.

Don Schechter explains how to capture your footage from your camera to your computer and log it for easy access later on. You can use Adobe Premiere to capture your movie, but you can not forget to put your tape in your camera.

If left unattended, a hacker with a USB Rubber Ducky and physical access to the computer can infiltrate even the most secure computer. Such attacks often go undetected without the use of a tool like USBRip, which can provide you with assurance that your device hasn't been compromised.

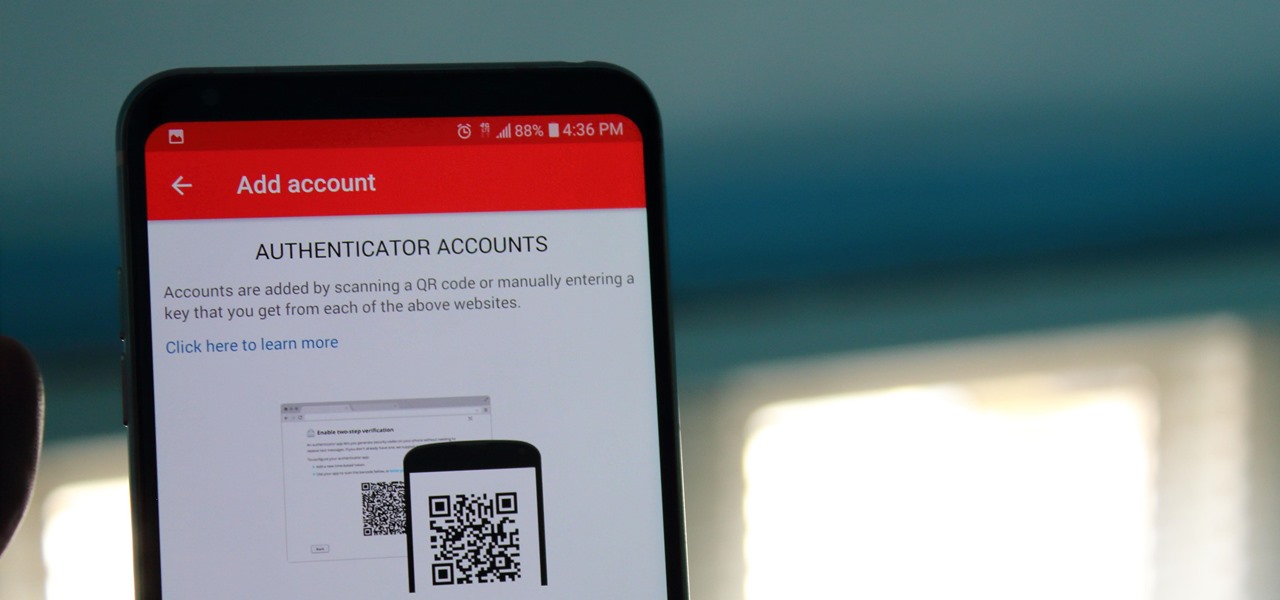
If you didn't get the memo, passwords aren't enough protection for your online accounts. Even a long and complex password offers only one line of defense which can falter. Two-factor authentication adds an additional layer, bolsters your defense, and decreases the risk of your account becoming compromised.

It always helps to be prepared for the worst. This applies to our phones now more than ever, as we depend on them to be our record keepers for text messages from friends, family, and coworkers. If you ever lose or severely damage your phone, having a backup of your precious texts gives you the peace of mind of knowing that you can always get them back.

Between the Cambridge Analytica scandal and the revelation that Facebook logs your calls and text history on Android, many are considering joining the #DeleteFacebook movement. But it can be difficult to leave the site, because so much of its content is only available to active users. If you want to keep in the loop without sacrificing your privacy, you'll want to follow the steps below.

During a penetration test, one of the most important aspects of engaging a target is information gathering. The more information you have coming into an attack, the more likely the attack is to succeed. In this article, I'll be looking at SpiderFoot, a modular cross-platform OSINT (open-source intelligence) gathering tool.

The peaceful, pastel and doily-filled world of Pinterest is my oasis. My account conveys who I want to be and what I want to accomplish, so the idea of someone hacking it and ruining my favorite escape for me is heartbreaking. Fortunately, Pinterest has updated its security, implementing three new features to hack-proof your account.

For the past three or four months, Microsoft has been pushing advertisements onto the lock screens of some Windows 10 users as part of its "Windows Spotlight" feature. This feature normally shows you scenic photographs and gives you the option to learn more about them by launching an Edge window once you log in. However, the aforementioned users have reported seeing the image below for the new Rise of the Tomb Raider game. Rather than taking you online in Edge to learn about it, you're given ...

Netflix is an enabler. It creates a joy around binge-watching and couch potato-ness, and the major contributor to this epidemic is its built-in "Post-Play" feature.

This time it's serious. Really. The largest web security vulnerability of all time went public on Monday, April 7th, 2014, resulting in widespread panic throughout the Internet as system administrators scrambled to secure their websites from the OpenSSL bug known as Heartbleed.

While you may suck at Instagram, it's likely that you manage multiple Instagram accounts, whether strictly for personal use or for managing blog and business pages.

If I'm in a hurry, sometimes I'll just turn my computer off and rush out of the house. Sometimes, I'm in the middle of a long YouTube video when I dash off, only to come back and find that my video position has been tragically lost. Hopefully I don't lose my place in that motorcycle accident compilation video when I get ba... damn it.

Apps are now very much integrated with social media, especially with your Facebook profile. Pretty much every app these days lets you log in using Facebook, while some actually force you to, giving you no other option. But, the most annoying part is that these apps leave notifications all over your Facebook timeline, cluttering the hell out of it. So, how can you completely banish all of these apps from being able to access your Facebook?

Dropbox announced Tuesday that a recent security breach compromised a list that included the email addresses of certain Dropbox users. To avoid future complications, the service announced that it would be implementing two-factor authentication, and even more useful, a security page that lets you monitor all activity on your account. In light of this and other recent web security threats, you might also want to know that services like Gmail, Facebook, and Yahoo! Mail have similar pages where y...

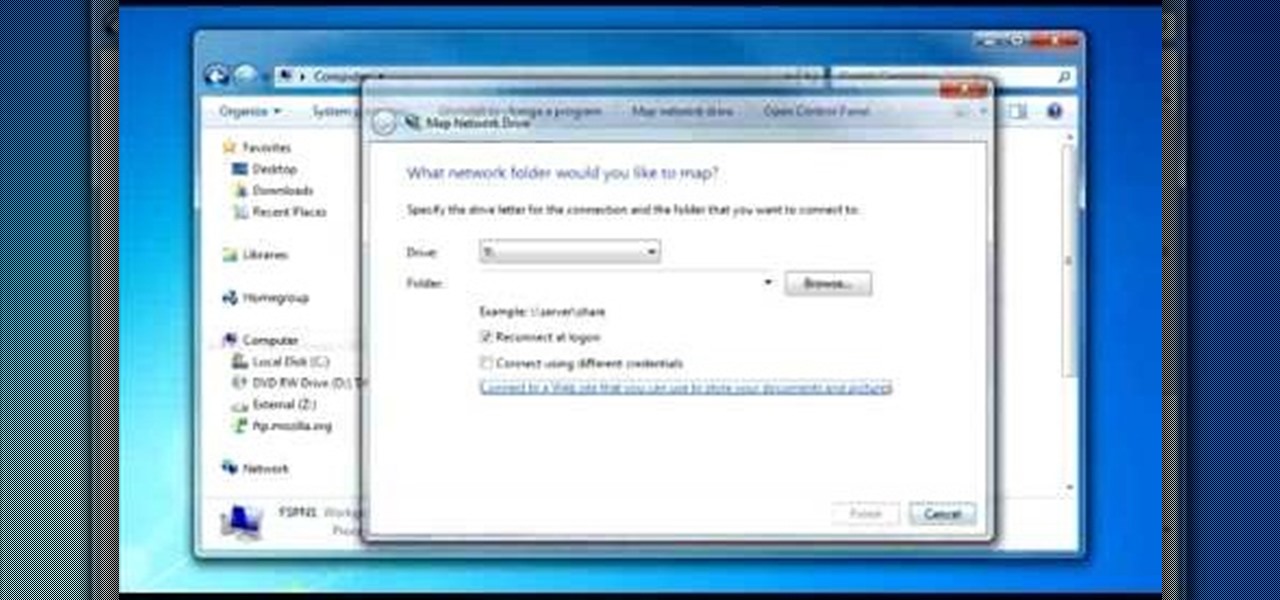
To do that click on tools in windows explorer and choose map network drive. Now click on "connect to a web site that you can use to store your documents and pictures" and then click on next and next. Now you have to type your internet or network address for example you type ftp://ftp.mozilla.org. This is a public server and it does not require a user name or password. Now click on next and there make sure you selected "log on anonymously" but if your server require a password then you have to...

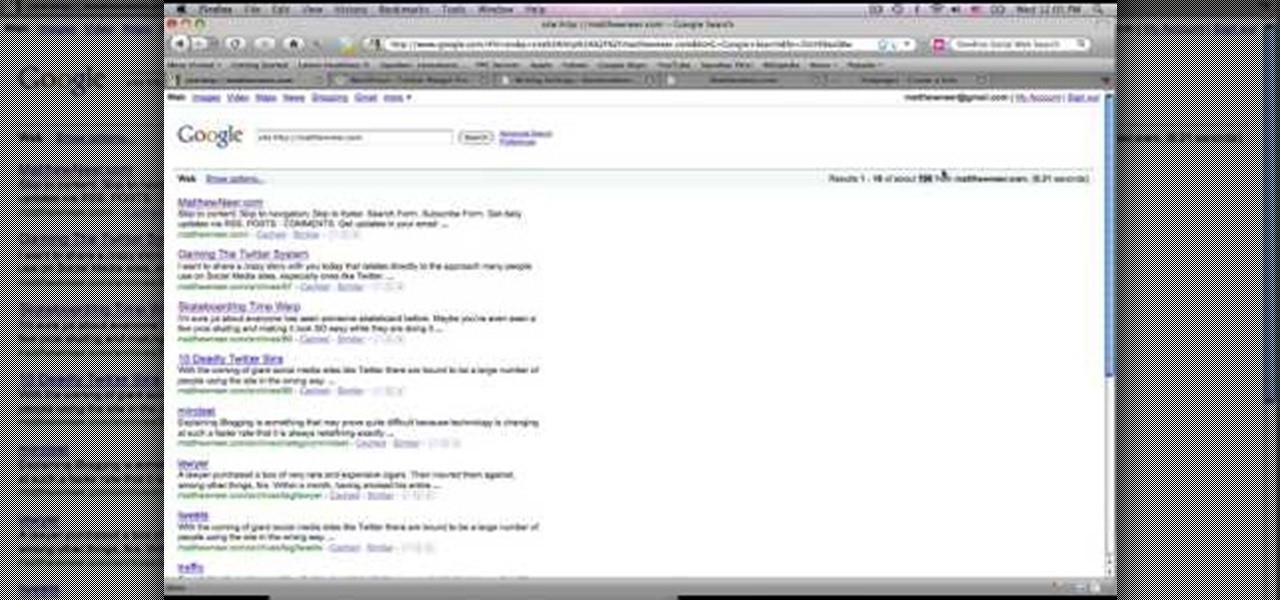
This video tutorial from MatthewNeer presents how to check your site's or blog's Google indexing.Type in Google word Site, press Space and then enter your site's or blog's URL address.Then press Enter or click Search button.Newly opened Google page will show all the pages from your site or blog which are already indexed in Google search engine.From search Results to the right you can see how many pages from your site are already indexed.According to the results you can reoptimize those pages ...

Your IP address is what identifies your personal computer while you are online. You may want to change your IP address for privacy, to bypass website settings, to download, or for various other reasons. This tutorial will take you through the steps you need to start surfing more anonymously.

There are a lot of things on your computer that can reveal information about you when you are surfing the Internet. If you are like me, then you will do anything to maintain your privacy and prevent those little leaks of information from happening. Here's a list of a few of the "threats" that can reveal information about you:

How to use Home Sharing in iTunes 9 to transfer music files to another computer. First make sure both computers have iTunes version 9 installed. To check this go to the iTunes 9 menu next to file in upper left and select the about item. On windows machines this will be in the help menu. In the computer with the music files we need to make sure the iTunes library is nicely organized. Again go to iTunes menu, this time open the preferences menu, and advanced icon. Check mark both sections "Keep...

Radford Education teaches you how to create a website using Google Sites. You need to have a Gmail account for this. Go to Google and click More - Sites. After the login, click Create new site in the upper left corner. Complete all the fields, starting with the name of your site. You can also select your site theme below. Hit the Create Site button at the bottom, when you're done. You will then be taken to your brand new site.

In this episode of Full Disclosure we are explaining the website attack known as Cross-Site Scripting (XSS). Cross-Site Scripting is a type of security vulnerability that affects web applications that do not sanitize user input properly. This kind of vulnerability allows an "attacker" to inject HTML or client side script like JavaScript into the website. Cross-Site Scripting is most commonly used to steal cookies. Cookies are used for authenticating, tracking, and maintaining specific informa...

Apple just released iOS 13.5 for public beta testers today, Monday, May 18. The GM (golden master) for iOS 13.5 arrives just three hours after Apple released it to iPhone developers, and 12 days after the release of iOS 13.5 dev beta 4.

Apple just released iOS 13.5 for iPhone developers today, Monday, May 18. This GM (golden master) update comes 12 days after the release of iOS 13.5 dev beta 4, which introduced updated COVID-19 exposure notification logging settings and the ability to share your Medical ID with first responders when placing an emergency call.

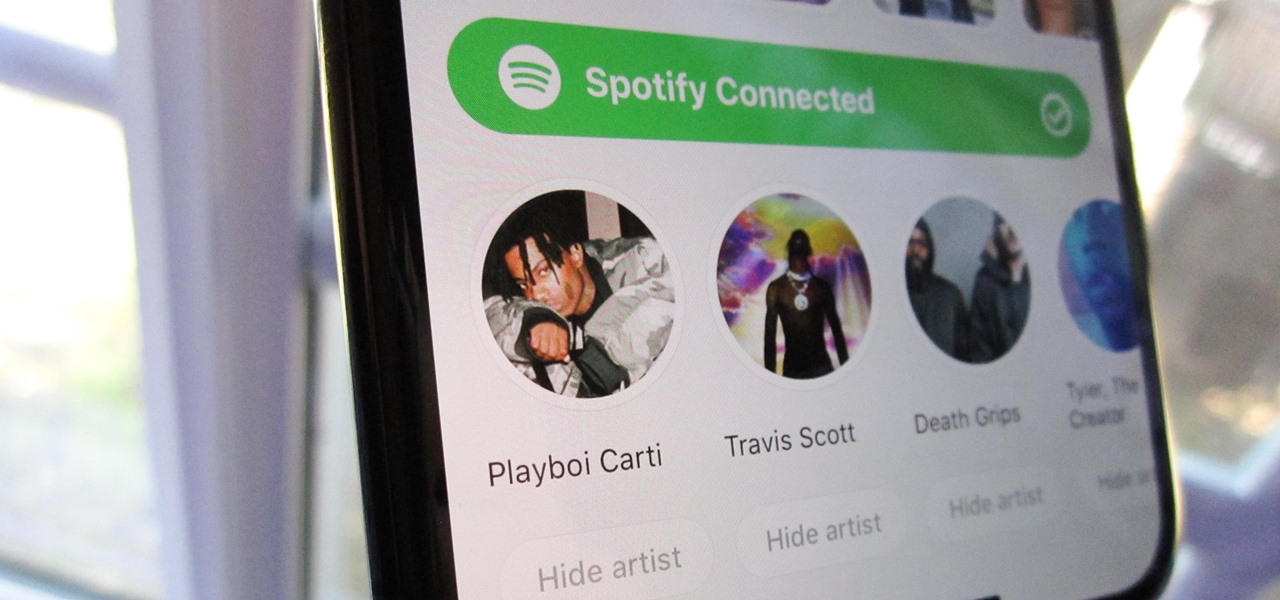
Spotify integration in Bumble has been around for a few years now, allowing prospective matches to view the artists you listen to the most on the popular music streaming service. It definitely helps people connect, but sadly, it doesn't work as well as it should because it rarely updates to show what you're listening to now.