Keeping track of your physical activities can be difficult, especially if you have a hectic lifestyle with responsibilities to constantly stay on top of. Thankfully, Samsung Health is there to help you log your workout routines, leaving you with one less thing to keep track of as you go about your busy day.

Getting new loot can be challenging in Fortnite Battle Royale. Whether you decide to pay for the Battle Pass or stick with the Free Pass, you still need to put in 50+ hours to unlock all the items. For those of us with Amazon Prime subscriptions, there's another way to unlock free items, and it won't cost you an extra dime.

The internet is constantly under siege by bots searching for vulnerabilities to attack and exploit. While conventional wisdom is to prevent these attacks, there are ways to deliberately lure hackers into a trap in order to spy on them, study their behavior, and capture samples of malware. In this tutorial, we'll be creating a Cowrie honeypot, an alluring target to attract and trap hackers.

After numerous scandals like the Equifax data breach and the 2016 US election, cybersecurity has become a significant issue for Americans. Unfortunately, anytime we use our devices, we're open to a cyber attack — especially when we browse the web. However, there are ways that we can make it harder for hackers and data miners.

Bluetooth Low Energy (BLE) is the de facto wireless protocol choice by many wearables developers, and much of the emerging internet of things (IoT) market. Thanks to it's near ubiquity in modern smartphones, tablets, and computers, BLE represents a large and frequently insecure attack surface. This surface can now be mapped with the use of Blue Hydra.

Hey everyone, this guide will show the process of stealing your victims Facebook credentials. This is a followup to my previous post.

Welcome back, my rookie hackers! The Golden Fleece of hackers is to develop a zero-day exploit, an exploit that has not been seen by antivirus (AV) software or and intrusion detection system (IDS). A zero-day exploit is capable of skating right past these defenses as they do not contain a signature or another way of detecting them.

At any moment, you can open up Meerkat and start live-streaming a video from your smartphone, available for anyone to watch. Thanks to its popularity at SXSW and the backing of several big Hollywood players, the app just announced that it's receiving $14 million in funding.

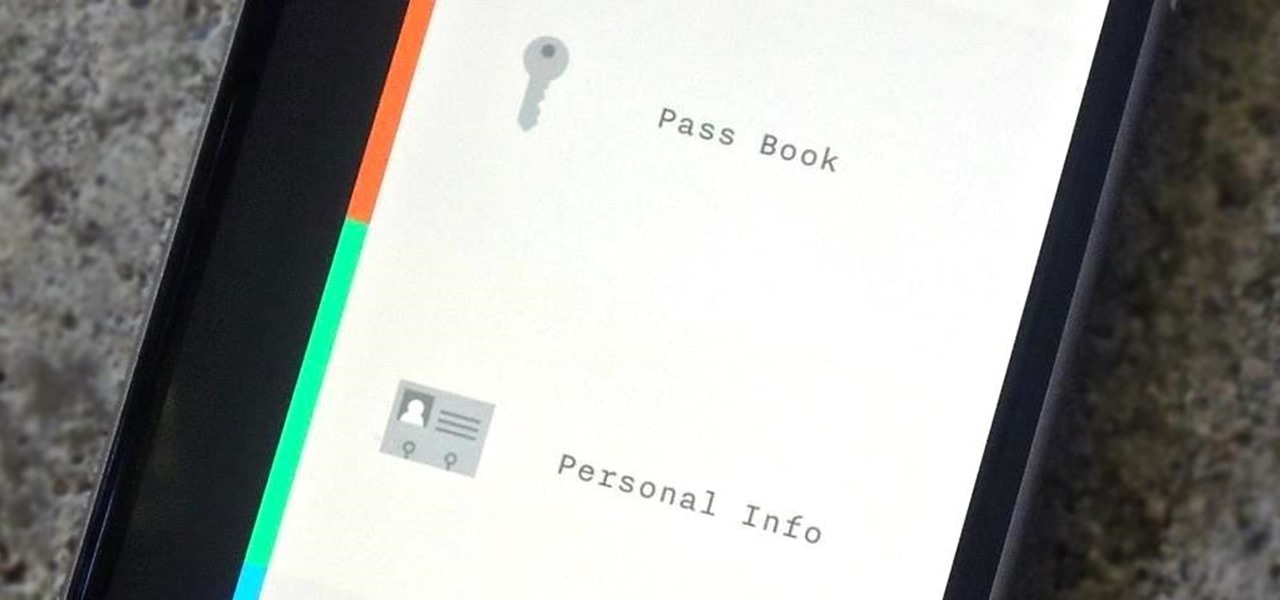
In the weeks before Apple officially released iOS 8, consumers were abuzz over rumors that a new feature would password-protect your photos and text messages from prying eyes. Unfortunately, this ended up being untrue, though we did cover some alternatives to protecting your important information using some built-in features and a third-party app. Now, there's a new iOS app that can do it all.

Unless you're waiting in line for your iPhone 6 or iPhone 6 Plus, it's a sure bet that you'll be sitting by at home for your new device to get delivered today.

Welcome back, my greenhorn hackers! Although we have focused primarily on technical hacks here, social engineering can sometimes be especially effective. This one requires a bit of technical skill, but not too much. In addition, it's limited by how specific a target you can choose—but it will work.

This video shows you how to use the online file delivery service YouSenditIt.com to send a file to someone. There are two ways to do this. One is to register for an account and send a file, and the other is to do it directly from the interface that you'll find on the website. You don't have to register, but generally if your file is going to be larger than 20 MB the person on the receiving end will need to register. But in this video we're shown how to send a file from the interface you're pr...

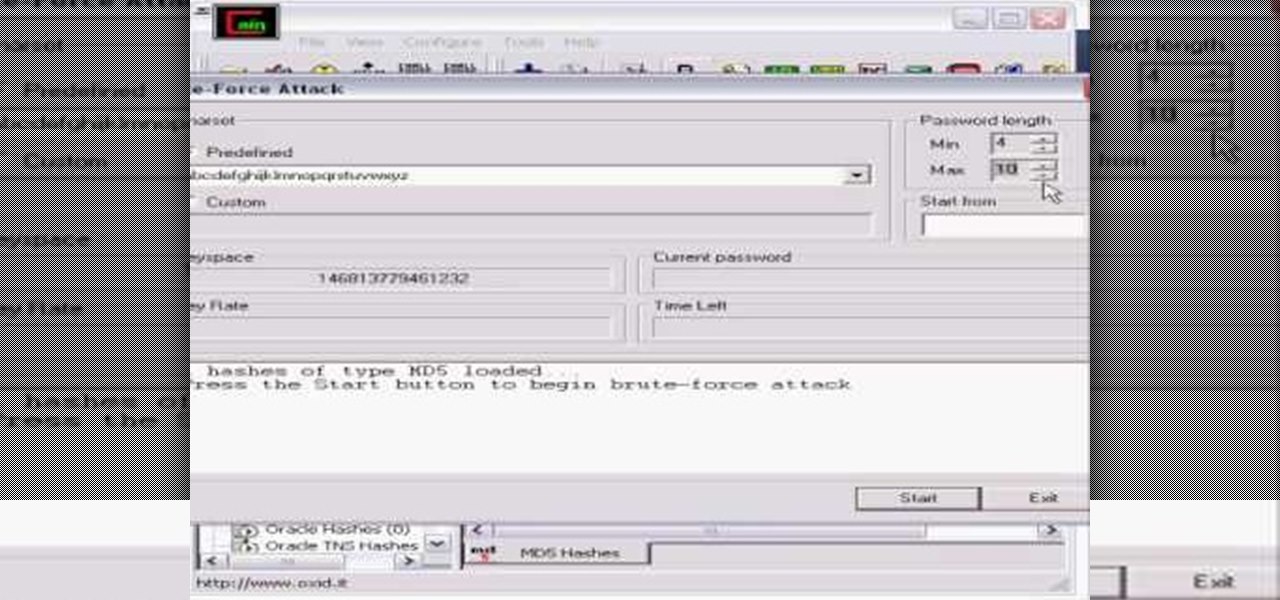
Whatever your reasons for doing it, if you are trying to hack passwords, it helps to have the right software for getting the job done. With the Cain and Abel program, you will be well on your way to hacking even the toughest personal passwords.

It was bound to happen with all those numbers floating around in your brain – you've forgotten your Windows password. Here's how to recover it.

This video includes instructions on how to get your PlayStation Portable (PSP) onto the BGSU wireless network.

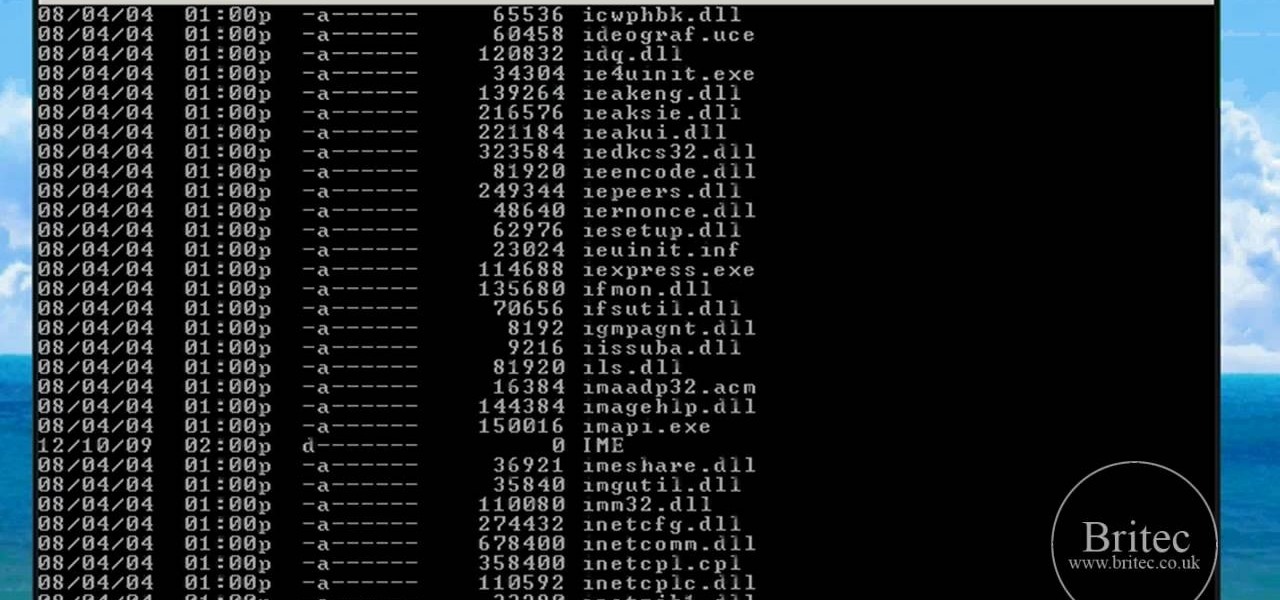
Faced with a missing log-on screen startup problem? This clip offers some advice for resolving it. It's easy! So easy, in fact, that this home-computing how-to from the folks at Britec can present a complete overview of the process in just over five minutes. For more information, including detailed, step-by-step instructions, take a look.

The fine folks at The Pathfinder School present what they call a spring tune-up for for you knife techniques, which have presumable deteriorated during the winter. The host is trying out a new knife he has been asked to test, and uses it to make a trap knotch and drill into a log, among other things.

K'NEX is one of the most popular construction toys on the market, right next to Lincoln Logs and LEGOs, but what makes K'NEX stand out is the fact that children can build mechanically derived toys. Instead of blocks or little logs, kids use interconnecting plastic rods and connectors, which give them tons of contraptions to build and play with. Today, K NEX has even more possibilities with wheels, pulleys, panels and flexi-rods to make amusement park roller coasters, airplanes, animals, bikes...

K'NEX is one of the most popular construction toys on the market, right next to Lincoln Logs and LEGOs, but what makes K'NEX stand out is the fact that children can build mechanically derived toys. Instead of blocks or little logs, kids use interconnecting plastic rods and connectors, which give them tons of contraptions to build and play with. Today, K NEX has even more possibilities with wheels, pulleys, panels and flexi-rods to make amusement park roller coasters, airplanes, animals, bikes...

K'NEX is one of the most popular construction toys on the market, right next to Lincoln Logs and LEGOs, but what makes K'NEX stand out is the fact that children can build mechanically derived toys. Instead of blocks or little logs, kids use interconnecting plastic rods and connectors, which give them tons of contraptions to build and play with. Today, K NEX has even more possibilities with wheels, pulleys, panels and flexi-rods to make amusement park roller coasters, airplanes, animals, bikes...

K'NEX is one of the most popular construction toys on the market, right next to Lincoln Logs and LEGOs, but what makes K'NEX stand out is the fact that children can build mechanically derived toys. Instead of blocks or little logs, kids use interconnecting plastic rods and connectors, which give them tons of contraptions to build and play with. Today, K NEX has even more possibilities with wheels, pulleys, panels and flexi-rods to make amusement park roller coasters, airplanes, animals, bikes...

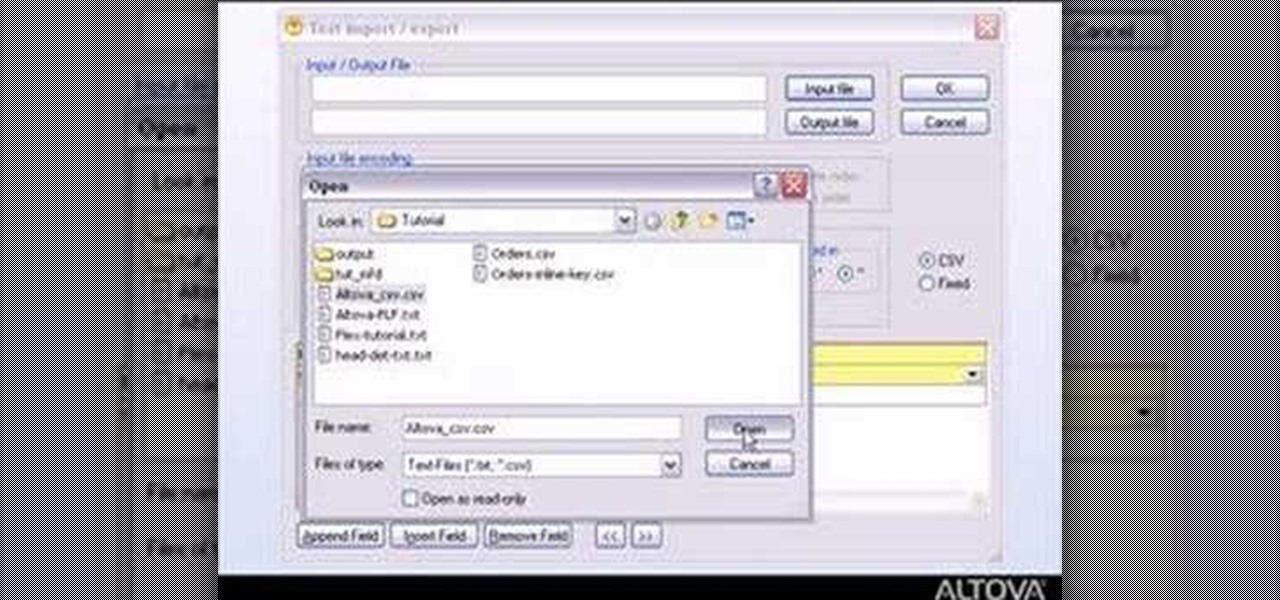
MapForce supports flat files as the source and/or target of any mapping involving XML, database, EDI, web services or other flat file data. In this how-to, you'll find instructions for mapping data from arbitrary text files (such as log files, CSV, fixed-width, and other legacy data sources) to databases and XML files.

Google has released a sync tool which provides an automated 2 way sync between your Google and your Outlook 2003 or 2007 calendar. It was easy to install and set up, plus it works! Just log into your Google calendar and you'll see it at the top.

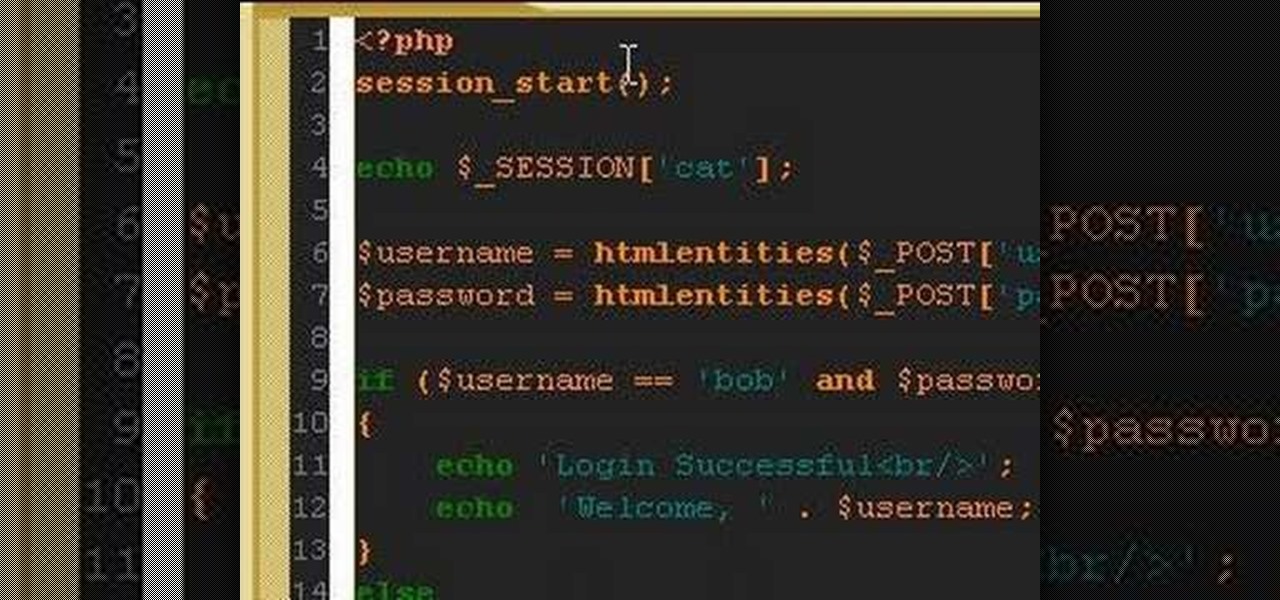
A PHP programming tutorial on creating login sessions to keep users logged in.

Most companies have services like employee login portals, internal-only subdomains, and test servers they would prefer to keep private. Red teams and white hat hackers can find these obscure and often vulnerable services using a tool designed to help protect users from fraudulent certificates.

Attention all Redditors: Between June 14 and June 18, Reddit experienced a data breach. The popular website claims it discovered the breach on June 19 and has since made the necessary moves to contain and eliminate the threat. Unfortunately, there isn't much they can do about the data was that accessed and stolen — your user data.

Welcome back, my tenderfoot hackers! As you should know from before, Snort is the most widely deployed intrusion detection system (IDS) in the world, and every hacker and IT security professional should be familiar with it. Hackers need to understand it for evasion, and IT security professionals to prevent intrusions. So a basic understanding of this ubiquitous IDS is crucial.

This two part Achievement Hunter guide will show you where to find all of the different skulls and collectibles necessary to unlock the 'Librarian of Macragge' achievement in Warhammer 40k: Space Marine. Keep an eye out for those skulls and audio logs so you can grab the achievement for yourself!

When you're surviving in the wild there's no running to 7-11 to grab some snacks. It's all up to you. This excellent instructional video teaches you how to build and set an Asian trail spring trap. Primarily, this trap would be used for medium sides animals as they make their way along a forest trail. The trap requires a heavy object near the trail (ideally a rock, or fallen log), a length of fine, strong cordage, a 4ft piece of sapling and several small branches for this device's triggering ...

In this tutorial, we learn how to redeem a code for Microsoft Points (Xbox 101). First, you will need to log onto your Xbox Live account on your console. From here, pick a game that you want to purchase. Make sure you research the information about the game and you really want it, because you cannot return it. After this, choose the option to redeem a code and then type in the code for your Microsoft Points. After you do this, you will be bale to purchase the game that you want and you will h...

In this tutorial, we learn how to make homemade valentine's hot chocolate stones. First, take 8 oz of a good dark chocolate and chop it up. Place this in a bowl, then add in 1/8 tsp of chipotle peppers. Also add in a pinch of salt, then add in 1/2 c of heavy cream to a skillet and bring to a boil. After it boils, pour it over the chocolate and let it sit for around 3 minutes. Then, give it a stir until it's completely smooth and beautiful. Pour this onto plastic wrap, then roll into a log sha...

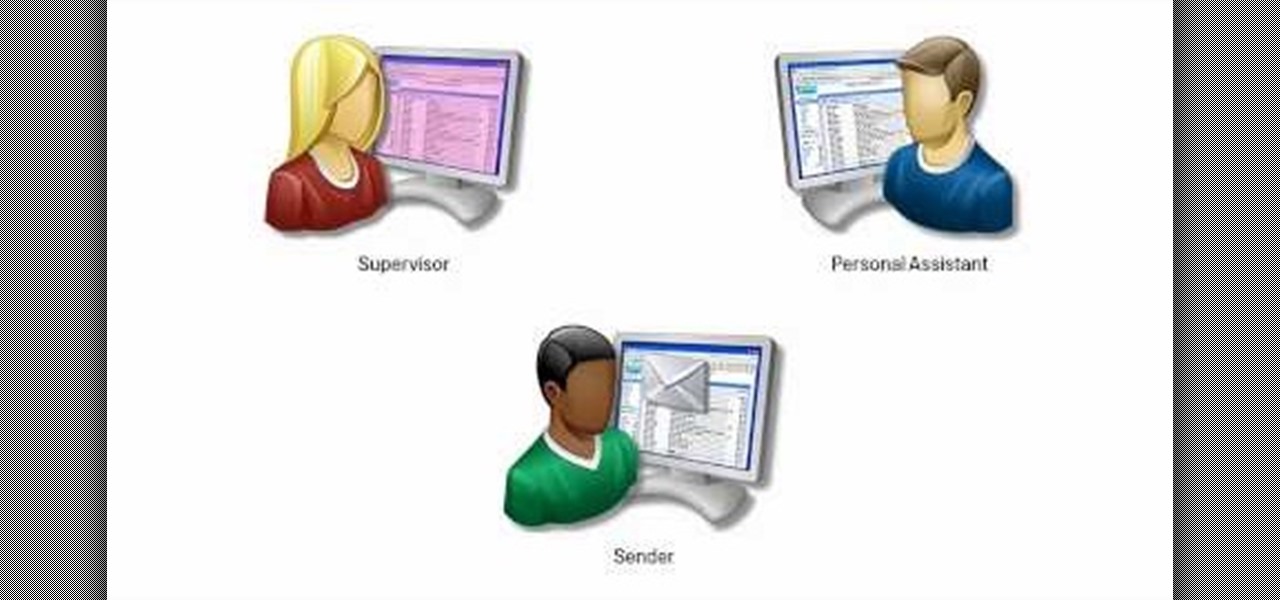
When you're personal assistant needs to handle your e-mails for you, it can be quite daunting having to give out your personal account information just so they can have access to your e-mail. And more importantly, having to battle for log in time might also be quite the hassle. With Gmail you can actually delegate your personal assistant so they have access to your inbox and can reply and send messages on your behalf, but they cannot change settings, passwords, or chat on your behalf. In this...

In this video tutorial, viewers learn how to read Google email offline. Begin by logging onto your Google account. Then click on Settings and select the Labs tab. In the Offline headline, click on Enable. To not grab all your emails, go to the Offline tab and select which messages will be synchronized with your computer, based on labels and time frame. This video will benefit those viewers who use Google mail, and would like to learn how to read their emails offline in case their internet con...

Adobe After Effects is powerful but difficult-to-use video editing tool. Youtube is a massive index of videos, most of which are low-quality and poorly edited. This video tutorial teaches you how to combine the two effectively by using After Effects CS4 to prepare HD videos for uploading to Youtube. It also includes other tricks like how to make a moving log as part of your video. Uploading HD quality videos will make your channel stand out and get more views.

In this video, we learn how to tag people in pages in status updates. To do this, you need to open up your browser and log into www.facebook.com. Once you get to your profile, you will see a box that says "what's on your mind?". Type whatever you want to into this box, and to tag someone all you do is write "@" followed by their name, and their profile should pop up. Click on their picture and the text will now show a blue hyper-text when you post it. Now when people see your status, they can...

This video shows you how to make a fishing spear for catching fish or small wildlife in survival situation.To start, you need a sapling about 5 feet long and a knife. Make a raw sharpening of the stick. Then split the log at the tip for a length of 6-8 inches. To split, put the knife on the middle of the sapling, near the tip, and press hard against it. Once it is split, find a twig with the width of a pencil and push it inside the split, making the two halves of the stick form a gap between ...

As a kid, you always liked to be constructive, building with Legos and Lincoln Logs, and at one point you even got into playing the strategic, building block, video game Tetris. Why not go back to the gold old days and find a new game of today similar to those of your young years, like Rumis?

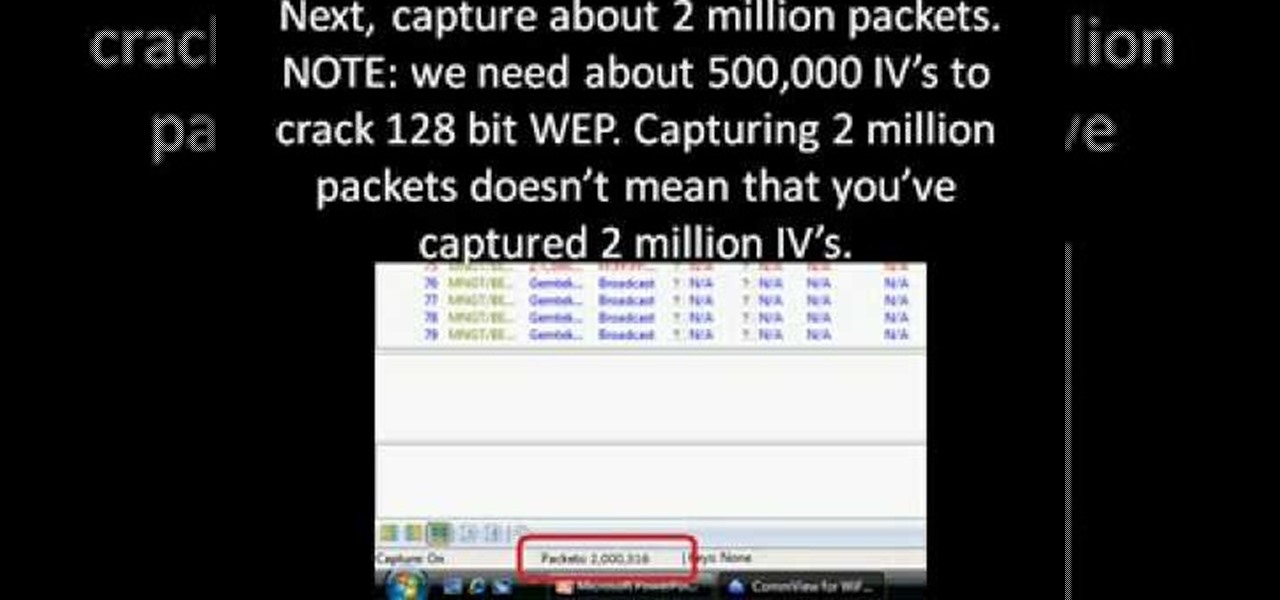
First you need to download Aircrack-ng and Second thing you need to download is CommView for Wi-Fi. Now you have to install CommView for Wi-Fi and then install the right driver.

In this video, we learn how to submit your site to the Yahoo search engine. First, go to site explorer. Once here, submit your website or web page in the appropriate box. After this, enter the full URL of the site feed you want to submit. After you do this, go to the side bar and verify your site, or add a META tag, then go to your site. Now, copy the code that Yahoo gave you and paste it into your website. After you do this, your site will be submitted and you can search for it through the Y...