If you love to take selfies and post them online for all the world to see, then it's important to ensure that you are always sharing your best side. It's pretty common for people to just open up their stock camera app and snap a quick photo, wherever they may be — but there's a bet

Open-source data scraping is an essential reconnaissance tool for government agencies and hackers alike, with big data turning our digital fingerprints into giant neon signs. The problem is no longer whether the right data exists, it's filtering it down to the exact answer you want. TheHarvester is a Python email scraper which does just that by searching open-source data for target email addresses.

Surveying a target's Wi-Fi infrastructure is the first step to understanding the wireless attack surface you have to work with.

On April 7, 2017, residents in Dallas, Texas, woke to the sound of emergency sirens blaring all over the city. No one could shut them off, and after repeated efforts to contain the situation, the city had to shut down the entire system. While the media reported a sophisticated computer hack was responsible, the truth was much less high-tech.

New releases of iOS are always pretty exciting. I remember the anticipation buildup of iOS 7 before it was announced at WWDC 2013, as it was expected to be a complete game changer compared to previous versions—and it was.

Welcome back, everybody. In the previous article, we covered the ideas and concepts of well-known ports and trust exploitation in order to evade a firewall. Today, we'll be building the shell, the part that receives commands, executes them, and sends the output back to the attacker.

Welcome finally, to a tutorial on buffer overflows! At last we have reached an exciting part of this series where I will dedicate the entire article on explaining and exploiting the notorious vulnerability. Grab some popcorn, sit back and enjoy the show.

Hello my anxious hackers, the week has started and here we begin a new series that I think will help many here and not only, for those that have the opportunity to follow our tutorials but they are not yet part of the community.

Heartbleed, move over. There's a new bug in town, and this time it's also affecting Mac and Linux computers. It's called Shellshock (its original official title is CVE-2014-6271), and it's currently got a 10 out of 10 severity rating over at the National Cyber Awareness System. While some updates have been issued to fix this bug, they were incomplete, and your system is probably still vulnerable, as it has been for the last probably 20 years.

Each day, we read about another security breach somewhere in our digital world. It has become so commonplace that we hardly react anymore. Target, J.P. Morgan, iCloud, Home Depot, and the list goes on and on.

It has been a long while since I last came here to write an article. Graduate school keeps you busy. After I looked over what I had written previously, I decided that I should introduce another fun topic from cryptography. In this case, steganography.

April Fool's Day, aka National Screw with Your Friends Day, is finally here. You can always pull a conventional prank, like strategically placing a whoopee cushion on your mom's chair, but that joke has been exhausted generations before smartphones were around. We live in a day and age where smack cam is the new level of pranking, so it's time to step your game up, novices.

Welcome back, my greenhorn hackers! Recently, I asked the Null Byte community what subject they would most like me to cover in future tutorials. Many of you cited scripting, and I decided it's best to cover this subject soon, so here goes.

Below are the official rules and guidelines for submitting content to WonderHowTo. Please look over them before publishing any articles. Ignoring the rules could result in deletion of your article or being flagged as a spammer. Most of these rules apply to comments as well.

Remote Desktop gives you access to your Windows 8 PC or device from wherever you are to run your applications and access your files remotely.

There's a new download available for Mafia II on the Xbox 360 (and PlayStation 3), and this walkthrough series will cover the entire gameplay for "Jimmy's Vendetta", which follows the first DLC for Mafia 2, "The Betrayal of Jimmy" (only available for the PS3). This is a lengthy add-on to Mafia II, so watch and learn to see everything involved with getting out alive, as both the Italians and Irish.

In this video series, survival skills expert Mike Myers explores how to survive in the desert. Learn basic desert survival tips such as: how to prepare for the wilderness, how to find a campsite, how to use a map and a compass, how to kill and eat a rattlesnake, how to treat a snake bite, what to do if your lost in the desert, how to filter water, and how much water is needed to survive in the desert.

You know your going to have to sleep outside and you don’t know how to stave off the chill of the night. With the right equipment, some layering techniques and a full belly you be sure to get a good nights sleep even if it’s cold out.

Theater acting is a fun and creative art form but it can be difficult to project your voice loud enough for the audience to hear if you are use to speaking softly. With a few exercises and practice anyone can have a booming voice.

You can learn to deal with the thing we all dread, a computer crash. Hopefully you diligently back up work but even if that's not case, stay calm. There is still hope and even if you're not a wiz at computers there are people out there who can help.

Always wanted to try skinny dipping but not sure quite how to get the ball rolling? There's not much to it but with a little bit of forward thinking you can make sure to get your friends on board while avoiding cops and an unwanted audience.

Use Cheat Engine to hack into the popular Bouncing Balls game. It's as easy as that. It's not too hard to use Cheat Engine if you've never before, then… flash game hacking everywhere!

Hack mybrute with this mybrute cheat. MyBrute hacks, cheats, tricks. Watch this video tutorial to learn how to hack your way to level 14 on MyBrute (08/18/09).

Lose weight and stay healthy by learning how to do aerobic exercises with the expert tips in this free fitness video series on doing aerobic exercises.

Weight loss is a very important factor in society today and everyone is looking for new ways to make it easier to lose weight. Learn what to expect when receiving acupuncture therapy and how it can help with hormone balance from a Chinese medicine expert in these free video clips.

Sue Fletcher, walks you through the ten basic steps of beginner tap dancing. Each step is explained from beginning to end in detail so you'll never feel lost or left behind. You'll learn moves like the brush step, the ball change and the flap, all of which are great for any level of expertise.

There’s a good chance that you’ll be alone in life one day, and no... I’m not talking about a couch-bound, dateless loser with a pocket pussy and a bag of potato chips. I’m talking about alone. In the wilderness. Hungry. Cold. Lost. You can’t stay in one place too long, so it would be nice to have something to carry your belongings in. Maybe it’s post-apocalyptic land where you’re the sole survivor, and all the backpacks and rucksacks in the world are but mere ash. Either way, knowing this si...

Your privacy is important, especially online. Almost anywhere you go on the internet, you leave a trail of data that companies can use without your permission. VPNs are the easiest way to keep your browsing private and your information safe. Ivacy VPN is one such service, and it's one of the best deals you can get on a VPN because it will cover 5 of your devices for a lifetime, and this is a two-account bundle, so you'll be able to cover 10 total devices for $49.99.

The draw of wireless earbuds is convenience, and many still offer the same sound performance as their wired counterparts. The difficult part is finding a pair that will stay in your ear reliably, work when you need them, and give you the best audio quality.

The memories on your devices are precious, even if you don't often get a chance to revisit them. The worst thing in the world is when something happens to your computer or phone, and you end up losing some of those memories because your files weren't backed up or your microSD wasn't fireproof.

When an iPhone is lost or stolen, it's imperative to start tracking it via Find My as soon as possible, whether that's from a computer, tablet, or someone else's phone. However, if it's stolen, there's a good chance the thief or robber turns on Airplane Mode, blocking all communication with the iPhone. If this is a scary thought, you can prevent thieves from accessing Airplane Mode altogether.

The pandemic has forced a number of public-facing businesses to either temporarily close or permanently cease operations, with one of the biggest victims of this trend being the movie theater business.

Between all the streaming services you have to contend with, it's hard to want to go through the trouble of plugging in an adapter and loading up a DVD when you could find another movie without needing to move.

What's worse than trying to hear your music over the sound of someone else panting at the gym? Or maybe you're getting really into a movie, and it's finally at the moment everything has been building up to when a car alarm in your parking lot suddenly goes off, and the moment is ruined.

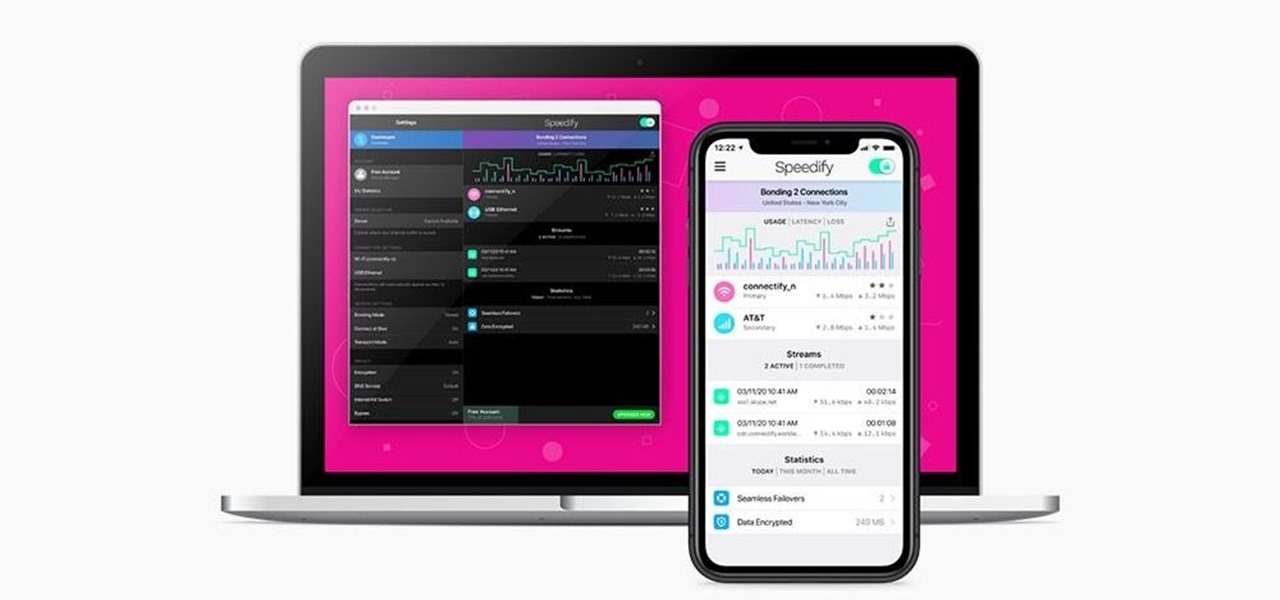
Using a virtual private network (VPN) is one of the safest ways to ensure your identity and data remain secure. Choosing one from the hundreds of services that now exist is another story. How do you tell which VPN truly provides the best protection at a great price?

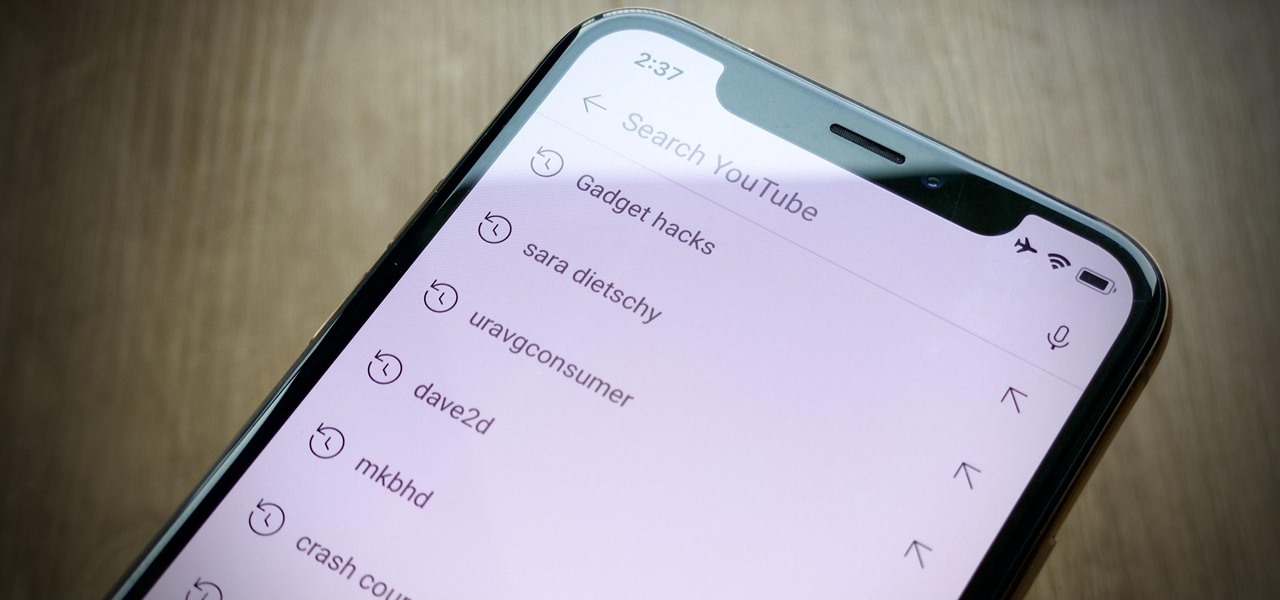
Sure, your search history can be useful, but more often than not, it's a paper trail of privacy infringement. It's perfectly reasonable not to want to see a complete list of your YouTube queries every single time you search for a new video. Luckily, blocking YouTube from saving your search history takes only a few taps.

Introduced in the Messages app back in iOS 8, audio messages are a fun way to spice up an iMessage thread when you're bored with text, emoji, and GIFs. However, it can be frustrating to lose an important, funny, or otherwise-interesting sound clip because iOS auto-deletes it two minutes after you send or listen to it. Thankfully, there is a way to stop this from happening.

Whether you miss the good old days of Telnet or you want to know what hacking was like when security was nothing but an afterthought, Telehack is the game for you. The text-based hacking game is a simulation of a stylized combination of ARPANET and Usenet, circa 1985 to 1990, with a full multi-user universe and player interactions, including 26,600 hosts.

If you're considering purchasing Apple's new 2020 iPhone SE, which brings many modern components into the compact body of an iPhone 8, you should know what its dust and water resistance rating means. Just how dirty and wet can the iPhone SE get without breaking any functionality?

Despite Android's flexibility in regards to customization, the options available in stock Android are pretty barebones. It is only with the help of third-party apps that we can entirely transform sections of the UI to our liking. And thanks to a new app, we can modify another part of the OS, the status bar.