Former Google employee Tristan Harris claims there's an easy way to combat phone addiction without installing any new software. By enabling grayscale on your phone, checking your apps and notifications will be less appealing and thus stop you from obsessively checking your phone.

Stakeholders in the driverless industry are anxiously awaiting changes the US Department of Transportation (DOT) is making to self-driving vehicle guidelines.

Every Friday, Next Reality reviews the latest headlines from the financial side of augmented and mixed reality. This Market Reality column covers funding announcements, mergers and acquisitions, market analysis, and the like. This week's column is led by two companies cashing in on visual inputs.
Google, the company that rules the internet, is now testing a method to leverage its machine learning with its ubiquitous presence on mobile devices. The new model they're employing is called Federated Learning, and it hopes to apply artificial intelligence to Google's services on Android without compromising user privacy.

The Snapdragon 820 and 821 were met with praise last year, receiving almost no complaints compared to their overheating predecessor, the Snapdragon 810. But now, all eyes are on Qualcomm to see what goodies they have in store for us this year, as their new SoC, the Snapdragon 835, will be revealed this week at CES 2017.

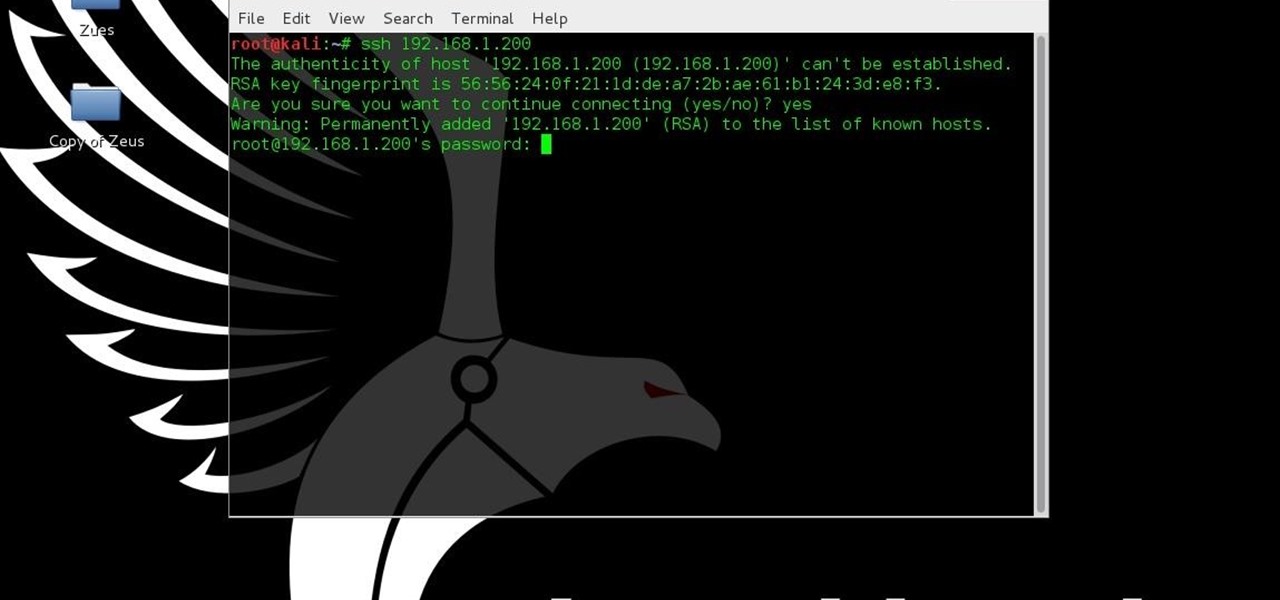
At this point in our series on creating a customized hacking container, you should be able to use Docker to save and retrieve customized instances of Ubuntu from your own machine. Make sure to revisit part one and part two if you need a refresher.

Mirror, mirror on the wall, who's the smartest of them all? Since Max Braun's Medium post went viral back in January of 2016, smart mirrors have been appearing on tech blogs in all shapes and sizes. Some are technically sound, some incredibly easy, but all are visually compelling. However, we've never seen one with a fully functional operating system and gesture support—until now.

We're almost there to completing the setup of your Mac for hacking! Now that we have Git and Homebrew under our belts, it's time to take on something fairly easy, but very important for our hacking needs.

Black Mirror, Netflix's technology-horror anthology, never fails to provide thought-provoking entertainment centered around emerging and futuristic technologies, and the third season's second episode, "Playtest," delves deep into the worlds of mixed, augmented, and virtual reality. While designed to leave you haunted by the end, offering a more "evil" narrative than we'll likely see in our actual future, the episode explores possibilities that aren't as far off as one might think.

On Wednesday, Microsoft launched a chatbot on social media that learns from conversation, and trolls quickly taught it how to be a shameless, Nazi-loving bigot. Oh Internet, an opportunity for a Hitler joke never slips past you, does it? This Is Why We Can't Have Nice Things

In this article I will show you how to obtain victim's credentials without cracking any hashes. There are a couple of ways to perform this task (for example dumping the SAM file and cracking the NTLM hashes), but here I will explain how to do it using PowerShell and a bit of social engineering. We are going to create a fake login popup.

As an avid coffee drinker, I used to be a big fan of single-serve coffee machines. One day, the machine decided to stop working—which does happen from time to time—so I decided to go old school and use my automatic drip. Then, I realized that all I had were pods of single-serve coffee grinds, and I was all out of regular coffee filters!

This tutorial is for people who want to try different types of hacks in an environment that is the same for everyone so it will help people to ask questions and learn. This series assumes you know how to run a VM and network them together. This series also assumes that the services running on the Metasploitable machine are needed to be running.

Summer's coming, and that means burger season. Okay, never mind... every season is burger season. Burgers are universally loved; they're the one meal you can find at numerous fast food shacks and haute cuisine spots.

As you're probably well aware by now, the Apple Watch isn't just for sending text messages and checking Instagram—you can also use it as your wallet. With Apple Pay compatibility, you can use your Watch to make purchases at any retailer that accepts the payment service.

Welcome back, my tenderfoot hackers! A short while ago, I started a new series called "How to Spy on Anyone." The idea behind this series is that computer hacking is increasingly being used in espionage and cyber warfare, as well as by private detectives and law enforcement to solve cases. I am trying to demonstrate, in this series, ways that hacking is being used in these professions. For those of you who are training for those careers, I dedicate this series.

Normally, office supplies and food don't mix, but you can use a paper shredder to make fresh pasta in your very own home (...or office). In other words, you don't have to buy a bulky and expensive piece of equipment to make fresh pasta. If you already have a paper shredder, you can simply feed pasta dough through it for perfect tagliatelle noodle strips that will taste far better than anything you can buy at the store. Step 1: Clean Your Machine

If you're like most people, you've stretched before a workout or playing sports. Doing so should help you get your muscles ready to work. While stretching is good for your muscles, you're wasting your time if it's the first thing you do. I talked to Dr. Brian Parr, professor at the Dept. of Exercise and Sports Science at the University of South Carolina Aiken, who explained this misconception and what you can do about it:

Need to add some spooky ambient fog to your super-scary Halloween party? Rather than shelling out money for a fog machine you'll probably only use once a year, make a trip to the nearest drug store and pick up a bottle of glycerin, a gallon of distilled water, a 2-liter bottle of cola, a disposable mini-pie tin, and a big candle in a jar.

Sometimes you just want to grill. It doesn't matter where you are, what you have, or whom you're with—you just want a delicious burger and you don't care what it takes.

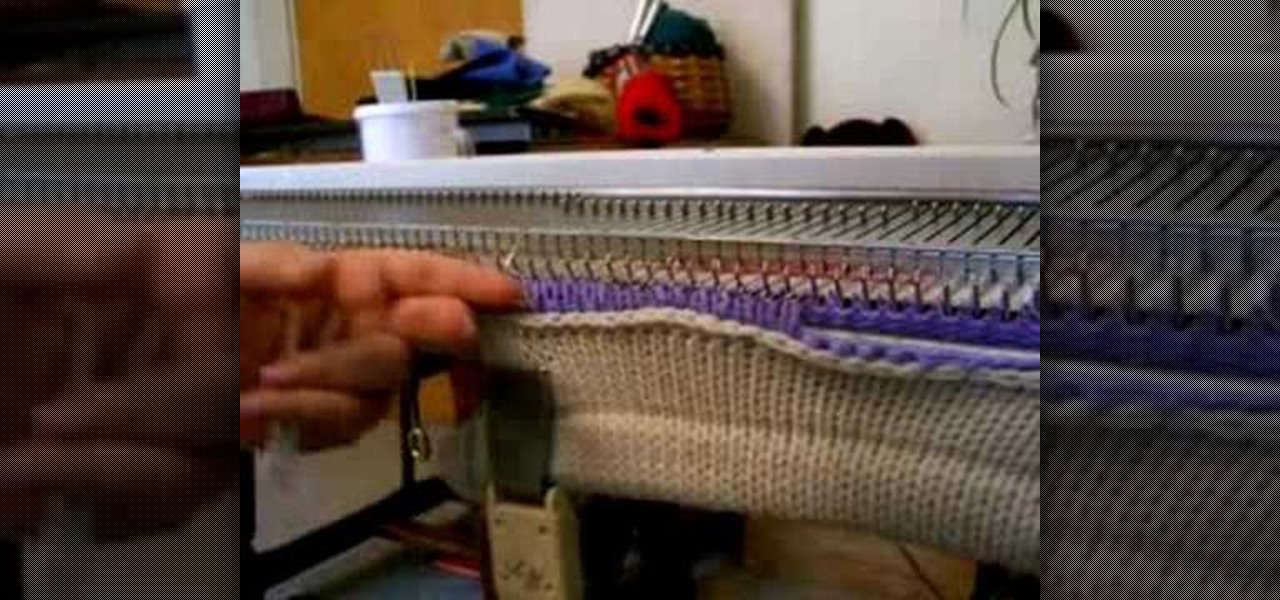
This instructional knitting video provides tips for making interesting patterns using a knitting machine. This is a demonstration of how to use a knitting machine to crochet cast on. This is one way to cleverly weave your yarn onto the knitting machine and begin the piece of knit work. You may want to reference written instructions in addition to watching this knitting video.

This instructional knitting video provides tips for making interesting patterns using a knitting machine. This is a demonstration of how to use a knitting machine to crochet a cast off. This is one way to cleverly remove your work from the knitting machine and complete the piece of knit work. You may want to reference written instructions in addition to watching this knitting video.

This instructional knitting video provides tips for making interesting patterns using a knitting machine. This is a demonstration of how to pick up and hang stitches. Use a three prong tool to attach one piece of knitting work to the knitting machine. Once you set the set the machine up, you can knit a wearable piece with an altering pattern.

This is a cool technique for machine knitters to use. It's a hand technique that converts quite easily to machine. Sew a phony seam when with a small knitting tool to alter pieces on a knitting machine.

Take a look at this instructional video and learn how to build your own miniature computer numerical control (CNC) machine. A CNC machine acts as a controller that reads G Code instructions for machine tools such as drills and printers. To perform this task, you'll need some geared motors you can find in old analog camcorders with optical zoom.

Using a sewing machine entails knowing how to thread it properly. This sewing how-to video demonstrates how to insert thread into a sewing machine. Follow the users instruction to properly insert the thread into your sewing machine.

Using a sewing machine entails knowing how to the tension knob properly. This sewing how-to video demonstrates how to properly adjust the tension knob on a vintage Kenmore sewing machine. The tension knob is located near the front of the sewing machine. It has a dial numbered from 1 to 9. The larger the number, the tighter the tension.

Using a sewing machine entails knowing how to insert a bobbin properly. This sewing how-to video demonstrates how to insert the bobbin into the feed dog of a vintage Kenmore sewing machine. The bobbin in the feed dog part of the sewing machine makes up the bottom of the thread needed for sewing.

In this video series, let our expert show you how to use the confusing hip abduction and hip adduction machines for thigh exercises. With Sheila Lindsey's help, you can start learning how to work your inner and outer thighs. She illustrates the various parts of the machines, and she gives you some tips for achieving the results that you are looking for. With her simple gym instruction, you can begin your thigh workout with just the right amount of expertise. So, watch and learn today!

Need a little help with your magic card skills? Check out this video tutorial to learn how to perform the "time machine" card trick.

Watch this instructional knitting video to complete and open cast on with a knitting machine. Push your needles back into forward position and knit across one row. You will want to use clips and claw weights to keep your knit work straight. If you knit with a knitting machine, this is an essential trick for getting started with larger projects.

Watch this instructional knitting video to hang a rag hem on your knitting machine. Add weights to the inside of the knitted hem to keep your knit work straight. You will need a single pronged tool or a three pronged tool. If you knit with a knitting machine, this is an essential trick for getting started with larger projects.

If you knit with a knitting machine, a cone of yarn proves much more useful than a standard ball of yarn. This instructional knitting video demonstrates how an electric cone winder works. This little machine allows one to quickly wind a ball of yarn onto a cardboard cone.

There are a total of 242 stars in Super Mario Galaxy 2 on the Nintendo Wii — 120 normal stars, 120 green stars and 2 bonus stars. If you've already found all of the stars in Worlds 1, 2, 3 & 4, now it's time for World 5!

In my first installment in this series on professional hacking tools, we downloaded and installed Metasploit, the exploitation framework. Now, we will begin to explore the Metasploit Framework and initiate a tried and true hack.

Today's post is a small go-to guide for beginner programmers in Null Byte. With many of our community members picking up programming from our Community Bytes, it only makes sense to lay out a one-stop guide for your reference. Hopefully this guide will help you make an educated and thoughtful choice on what programming languages you want to learn, and how you want to learn said languages.

Wireless headphones are convenient, comfortable, and more common than ever before. With the massive proliferation of wireless earbuds, it's hard to identify which ones are good and which ones just want to look like they're worth the price. Avanca T1 Bluetooth Wireless Earbuds are high-quality wireless earbuds with excellent functionality and a low price of $29.95 now that they're 50% off.

Post-exploitation is often not quite as exciting as popping the initial shell, but it's a crucial phase for gathering data and further privilege escalation. Once a target is compromised, there's a lot of information to find and sift through. Luckily, there are tools available that can make the process easy. One such tool is Postenum.

One Instagram creator's augmented reality homage to Disney's deep bench of animated characters has earned him fifteen minutes of fame.

For anyone using open source information to conduct an investigation, a balance between powerful tools and privacy controls are a must. Buscador is a virtual machine packed full of useful OSINT tools and streamlined for online research. This program can easily be set up in VirtualBox, and once that's done, we'll walk you through some of the most useful tools included in it.