An electric mandrel spinner is a tool that grips materials to be spun or machined. Watch this instructional lampworking video to see how molten glass may be shaped with a mandrel spinner. Mandrels are commonly used to shape beads of glass into a desired size and shape for jewelry manufacturing. This video shows you how to maintain an electric mandrel spinner.

An electric mandrel spinner is a tool that grips materials to be spun or machined. Watch this instructional lampworking video to see how molten glass may be shaped with a mandrel spinner. Mandrels are commonly used to shape beads of glass into a desired size and shape for jewelry manufacturing. This video shows you how burnish silver leaf using a lampwork torch and an electric mandrel spinner.

An electric mandrel spinner is a tool that grips materials to be spun or machined. Watch this instructional lampworking video to see how molten glass may be shaped with a mandrel spinner. Mandrels are commonly used to shape beads of glass into a desired size and shape for jewelry manufacturing. The rheostat dial on your power box will control your "set" spinning rate.

General Pipe Cleaners Easy Rooter Junior is the right machine to clear washtubs, small floor drains, roof vents and other medium-size drains. This video will give you a general overview of the operating instructions and safety procedures for the easy Rooter Junior. Take a look.

To calm our 8 week old baby Logan, the hair dryer is the foolproof white noise machine. Baby quiets down instantly. (But if he is hungry, then nothing works but milk.)

This video welding tutorial shows two arc or stick welding machines and explains how to connect the leads and hook it up ready for welding. Those interested in welding for metalwork will learn the proper machinery and equipment needed for welding and how to use the equipment correctly. Watch this instructional video and start welding.

This how to video tutorial demonstrates how to sew a straight stitch by hand, just in case you don't have a sewing machine. The straight stitch is excellent for simple hems, decorative stitching and gathering fabric.

Learn how to make a green, eco-friendly grocery bag. This is a great fashionable way to cut down on paper or plastic bags. All you need is some pretty fabric and a sewing machine. Remember this bag the next time you are going shopping.

In this how to video, Allyce King steps up to the sewing machine to make a quick, stylish bed for pets to coordinate with any decor. Then get some notion know-how. Check out this list of the supplies every creative chick should have in her sewing kit. Watch this how to video and you will be able to sew your pet a bed in no time.

Lawn mowers and lawn tractors are great machines and the latest models have some features worth checking out. New, fancy zero turn mowers, and four wheel steer mowers can make mowing your lawn quicker and easier. Tim Carter of Ask the Builder takes you through some of those new lawn mower features.

Learn Pat's tips for using the 1/4 inch foot on your sewing machine.

Your first bank account can be exciting and confusing at the same time. Check out this video and learn how to manage your money and accounts so you don't wind up in the red. You don't have to earn an MBA to make good financial decisions; this video offers plenty of suggestions to keep your accounts on track.

Tutus are not just for ballerinas anymore! Anyone who feels like twirling, dancing or just running around with a little extra poof can wear one! Follow this tutorial and make a tutu for yourself, your daughter or anyone else looking for a little fluff!

Using a Phillips head screwdriver remove the screw under the handle in the back of your iMac. Remove the screws outlined in the picture below. Remove screws 1 and 2 with a standard Phillips head screwdriver. Screws 3 and 4 use a standard flat head screwdriver. After removing the screws, gently pull out all of the plugs. Next holding the clear handle just below the bar code, pull out the section of the iMac.

What does it mean when a software company obsessively focused on innovating the way we use our mobile devices to see and communicate with the world adds virtual voice agents? Possibly e-commerce magic, with a powerful layer of augmented reality.

Cloud computing has come a long way since the days of simple online storage and server networking. Virtually every major company in the world now relies on complex cloud computing infrastructures to reach customers, innovate products, and streamline communications. Their reliance on advanced cloud computing platforms is only going to grow in the coming years.

Penetration-testing frameworks can be incredibly useful since they often streamline certain processes and save time by having a lot of tools available in one place. Of course, the most popular pentesting framework is undoubtedly Metasploit, but there are many others out there that cater to particular needs. For auditing web applications and servers, Tishna comes in handy.

Few things are more important than being well-versed in data analytics and interpretation when it comes to succeeding in today's increasingly data-driven world. As a data scientist, these skills are the key to a high-paying career. For hackers, there's no better way to defeat the enemy than to become the enemy.

Legendary drum-and-bass artist Squarepusher, the Warp records labelmate of fellow electronic music legend Aphex Twin, is back with his fifteenth album called Be Up a Hello, which is set to drop on Feb. 1.

Whenever a new Apple event invite arrives, the entire tech industry begins tearing the invite's graphics apart in a bid to decipher what the company may be planning on releasing in the coming weeks.

So you've managed to get a shell on the target, but you only have measly low-level privileges. Now what? Privilege escalation is a vast field and can be one of the most rewarding yet frustrating phases of an attack. We could go the manual route, but like always, Metasploit makes it easy to perform local privilege escalation and get root with its exploit suggester module.

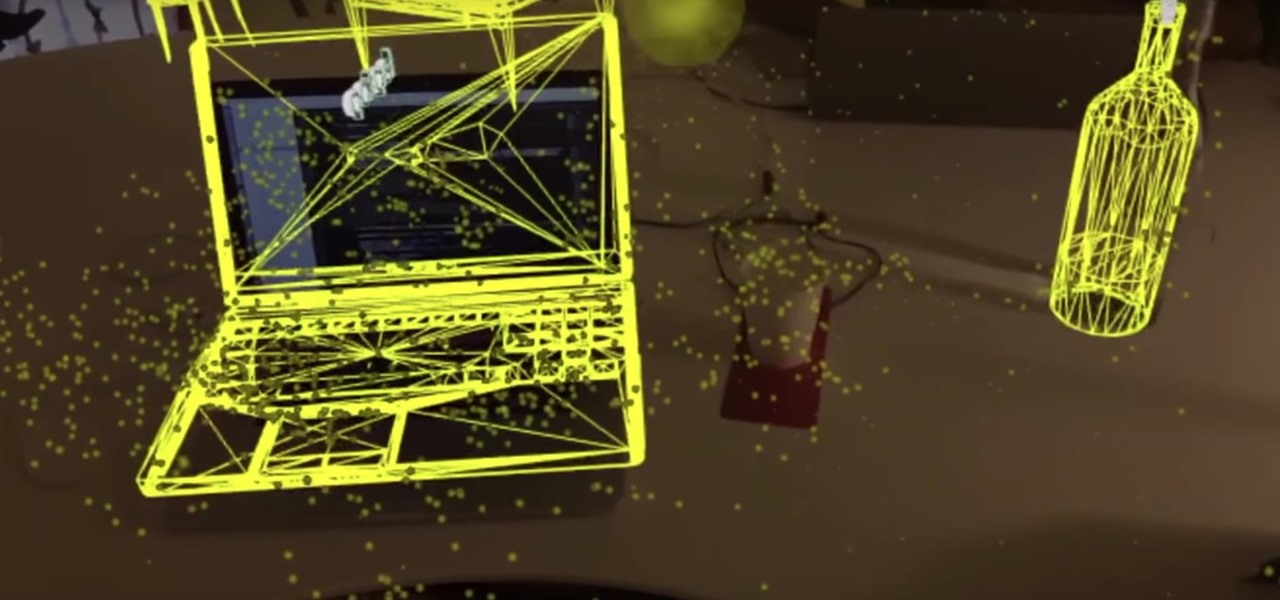
Higher-fidelity 3D content and next-generation AR experiences take more computing power than most modern AR headsets and mobile devices can handle. But Nvidia is introducing a new cloud-based solution to address that need that will stream AR content to modern devices.

Sure, Tony Stark was able to build the original Iron Man suit in a cave with a box of scraps, but can the average do-it-yourselfer replicate the EDITH smartglasses from Spider-Man: Far From Home in a similar fashion?

With Snapchat making the leap into the smartglasses realm, Facebook had to find a way to try and steal its competitor's augmented reality thunder.

There are a lot of songs out there, so it's tough to remember all of the words to every song you like. If you're like me and have a less-than-perfect memory, visual aids will ensure your Apple Music jams aren't interrupted with incorrect or forgotten lyrics. That's why Apple's update with time-synced lyrics is so cool, essentially turning your iPhone into a portable karaoke machine.

It is said that the best way to avoid detection when hacking is to leave no trace, and often that means not touching the filesystem at all. But realistically, in most cases, it's impossible not to interact with the filesystem in one way or another. The next best thing to do to throw off any investigators is to change the file attributes to hide activity. We can do this with Metasploit's Timestomp.

With the third season of Netflix's hit series Stranger Things set to debut July 4, it's time to crank up the hype machine, this time, in augmented reality.

It's no secret that the enterprise sector is hot for augmented reality, but the move into the enterprise AR software market by one of the biggest names in industrial engineering announces the technology's arrival loud and clear.

Many of us know that you can make a few bucks from Amazon by helping the company sell its wide array of products, but now there's a very different way to make a buck with the company, and it involves 3D technology.

There's no shortage of augmented reality platforms for remote video assistance, but startup Streem is looking to give its offering a leg up with an infusion of new technology.

As the tech world patiently waits for the advent of mainstream consumer smartglasses, Google is content to stick to the business world (for now).

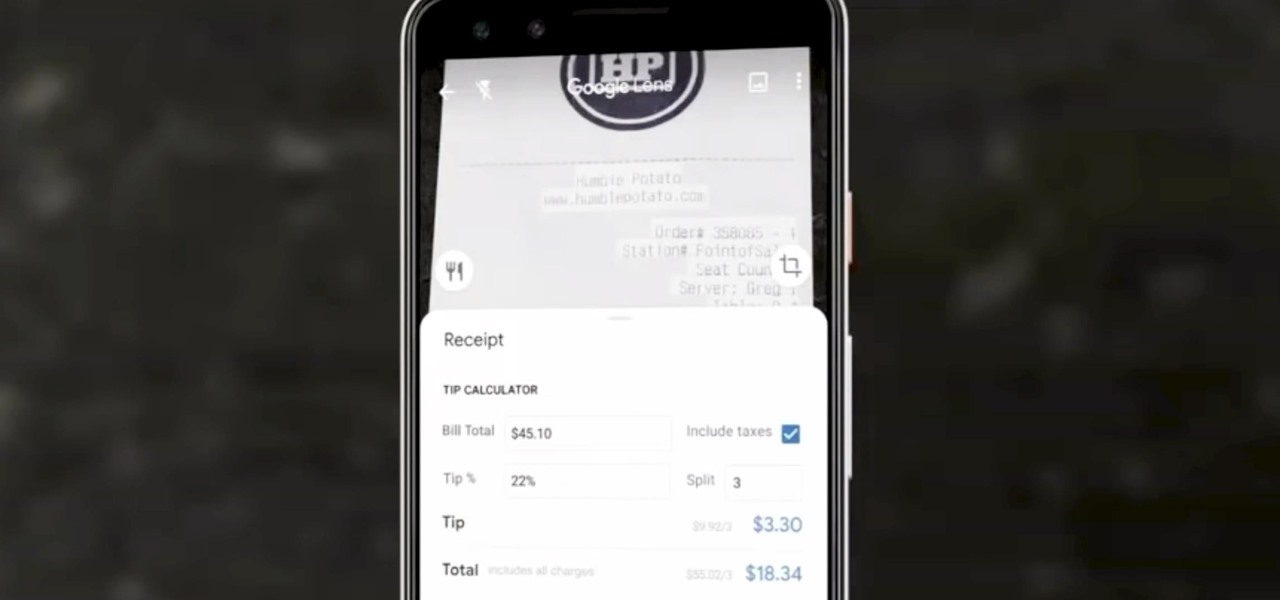
Google Lens can perform many different tasks with your smartphone's camera thanks to advanced machine learning, such as foreign text translations, landmark identification, and business cards to contacts conversion, to name a few. With this year's Google I/O conference, we have another cool Lens feature to look forward to — receipt calculations.

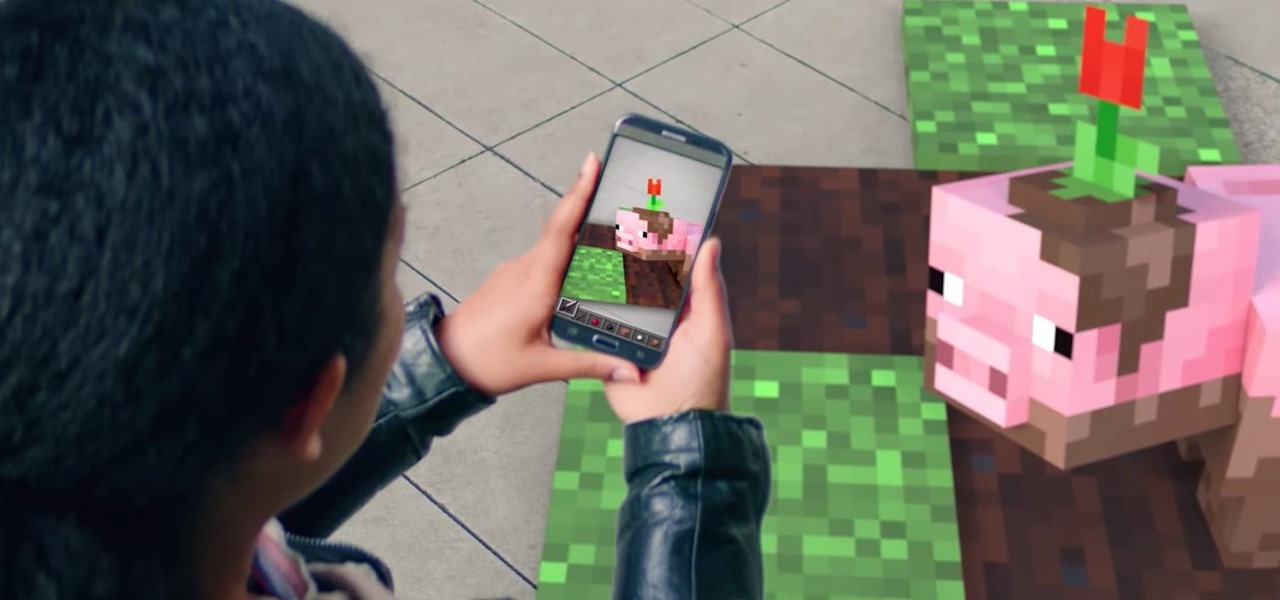
It looks like Microsoft will finally make good on its promise to bring Minecraft to augmented reality, as foreshadowed via a HoloLens demo in 2015.

The Avengers aren't the only shiny new toys available to Pixel handset owners, as the animated stars of the upcoming Pokémon Detective Pikachu movie have arrived in the Google Playground app.

The great thing about augmented reality is that so much is possible using the emerging tools and software, your only real limit is your imagination — that includes making real versions of imagined products.

Websites are often misconfigured in ways that allow an attacker to view directories that are not ordinarily meant to be seen. These directories can contain sensitive information such as private credentials or configuration files that can be used to devise an attack against the server. With a tool called Websploit, hackers can scan targets for these hidden directories without difficulty.

With the growing list of products Apple offers, the number of devices connected to your Apple ID can get quite extensive. Having all those devices connected to your Apple ID helps you keep track of them, but when it comes time to part ways with an Apple TV or Apple Watch, those devices can still be attached to your Apple ID. In some cases, this could affect the overall security of your account.

News junkies who own the Magic Leap One received some good news on Thursday, as CNN has published an app for the headset to display the network's news coverage in augmented reality.

It's confession time. Through a couple of sources, I managed to get an early look at the HoloLens 2. But I was sworn to secrecy, and I take my tech oaths seriously (shame on you, leakers).

It may sound like deja vu, but neural interface startup CTRL-labs has closed a $28 million funding round led by GV, Google's funding arm, for technology that reads user's nerve signals to interpret hand gestures.